
Video Upload Options
As the Global Navigation Satellite System (GNSS) is widely used in all walks of life, the signal structure of satellite navigation is open, and the vulnerability to spoofing attacks is also becoming increasingly prominent, which will seriously affect the credibility of navigation, positioning, and timing (PNT) services. Satellite navigation signal authentication technology is an emerging technical means of improving civil signal anti-spoofing on the satellite navigation system side, and it is also an important development direction and research focus of the GNSS.
1. Introduction
2. Principles and Technical Architecture of the Satellite Navigation Signal Authentication
2.1. Principles
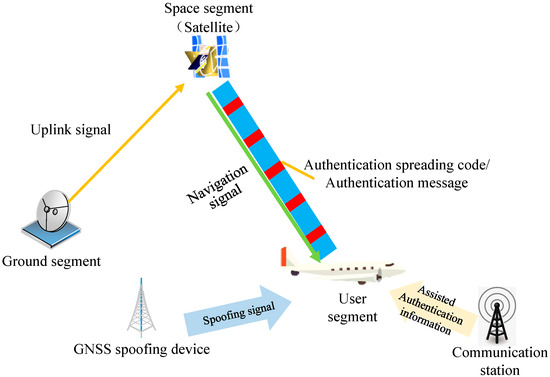
Satellite navigation signal authentication technology aims to add encrypted authentication marks to satellite navigation signals to prevent satellite navigation signals from GNSS spoofing attacks. It is a new GNSS anti-spoofing technology that combines information security and navigation signal design. The sender (navigation satellite) uses cryptography technology to generate an "authentication symbol", which is embedded in the existing satellite navigation signal and broadcast to users. The receiver (GNSS user terminal) verifies the "authentication symbol" to confirm whether the received navigation signal is from a real satellite in orbit, and whether the navigation message has been forged or tampered with [17]. Satellite navigation signal authentication technology has the following characteristics:
1) One-way broadcast.
The satellite navigation signal uses the navigation satellite broadcast signal to provide PNT services for terrestrial users, and its signal characteristics have the characteristics of one-way broadcast. Therefore, satellite navigation signal authentication technology should be based on the broadcast system authentication framework.
2) Signal disclosure transmission.
Satellite navigation signals use the public signal structure to broadcast signals, and their signal authentication needs to have the characteristics of public signal transmission.
3) Compatible with existing signal structure.
The authentication of satellite navigation signals will not affect existing GNSS services, so its authentication signal design should be compatible with existing signal structure.
2.1.1. Satellite Navigation Signal Authentication Type
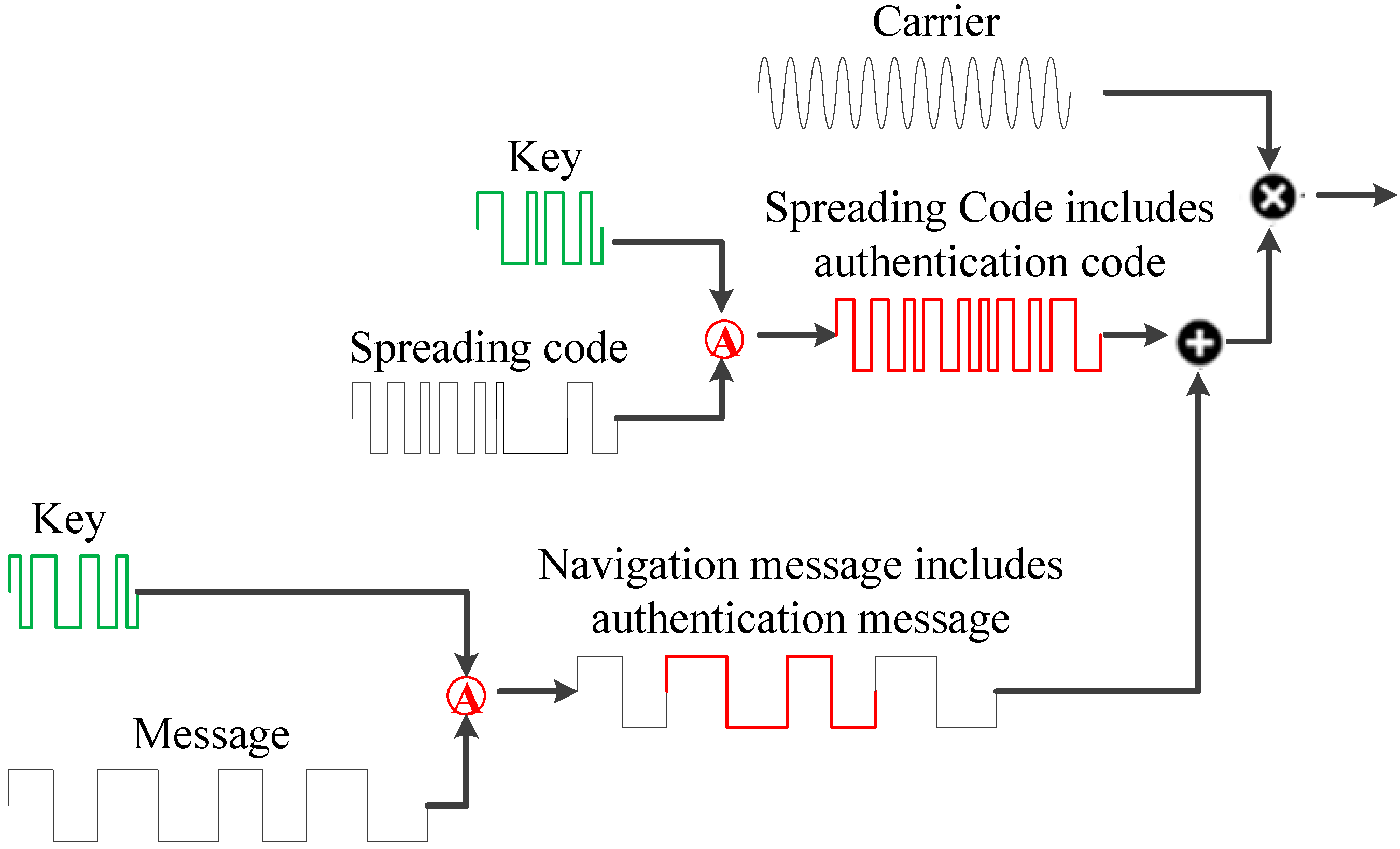
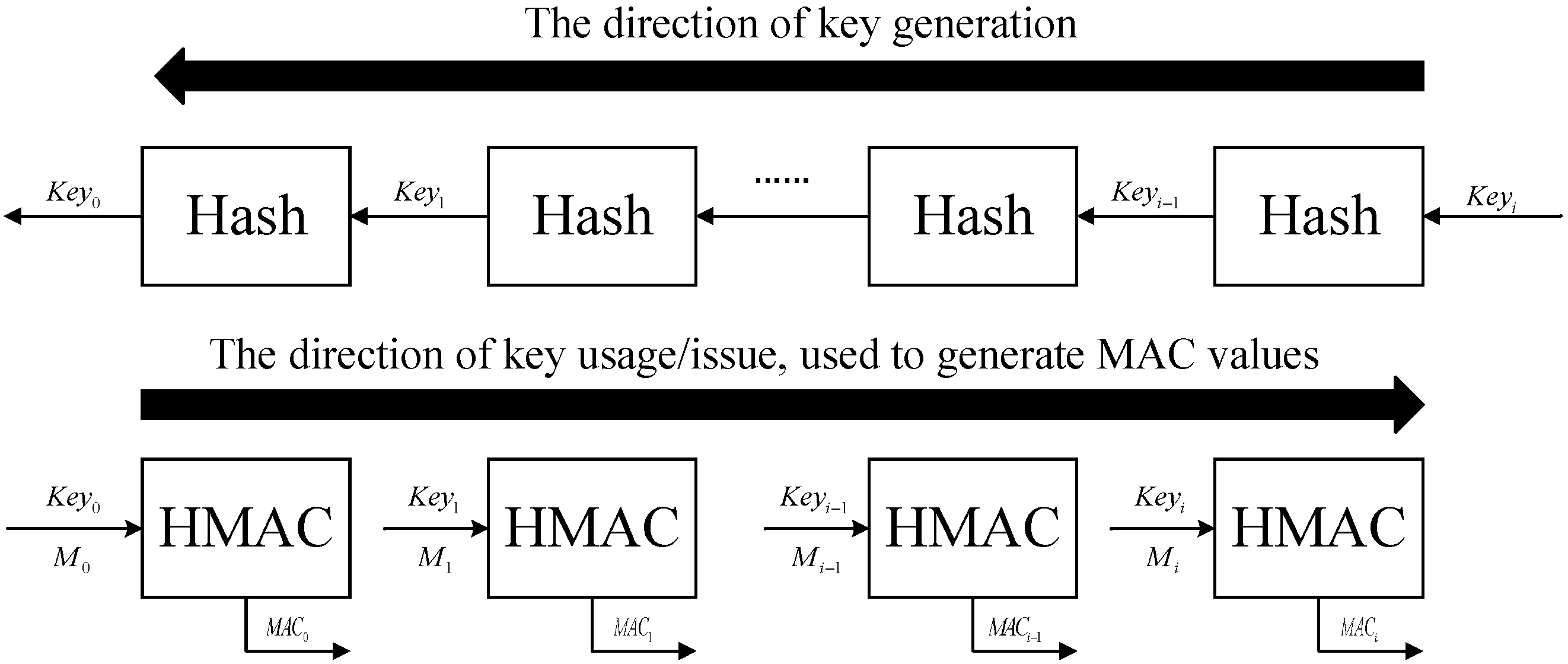
Satellite navigation signals include the carrier, pseudocodes, and message. The newly added authentication mark can be added to the navigation message [18] and spreading spectrum codes [19]. Figure 1 shows the generation of the navigation message including authentication message and the spreading spectrum code including authentication code. Therefore, the satellite navigation signal authentication type is divided into Navigation Message Authentication (NMA) and Spreading Code Authentication (SCA) [20].
1) NMA
NMA uses message bit-level authentication to realize navigation source authentication. Its advantage is that the modification of the existing signal system is small and the signal modulation method is not changed. It’s just to upgrade the software of the user receiver. The engineering realization cost is small. The Galileo E1 OSNMA structure is shown as Figure 2. Galileo reserved a 40-bit message in the early ICD, and the ICD announced in 2021 clarified that the 40-bit message is the navigation authentication message [21].
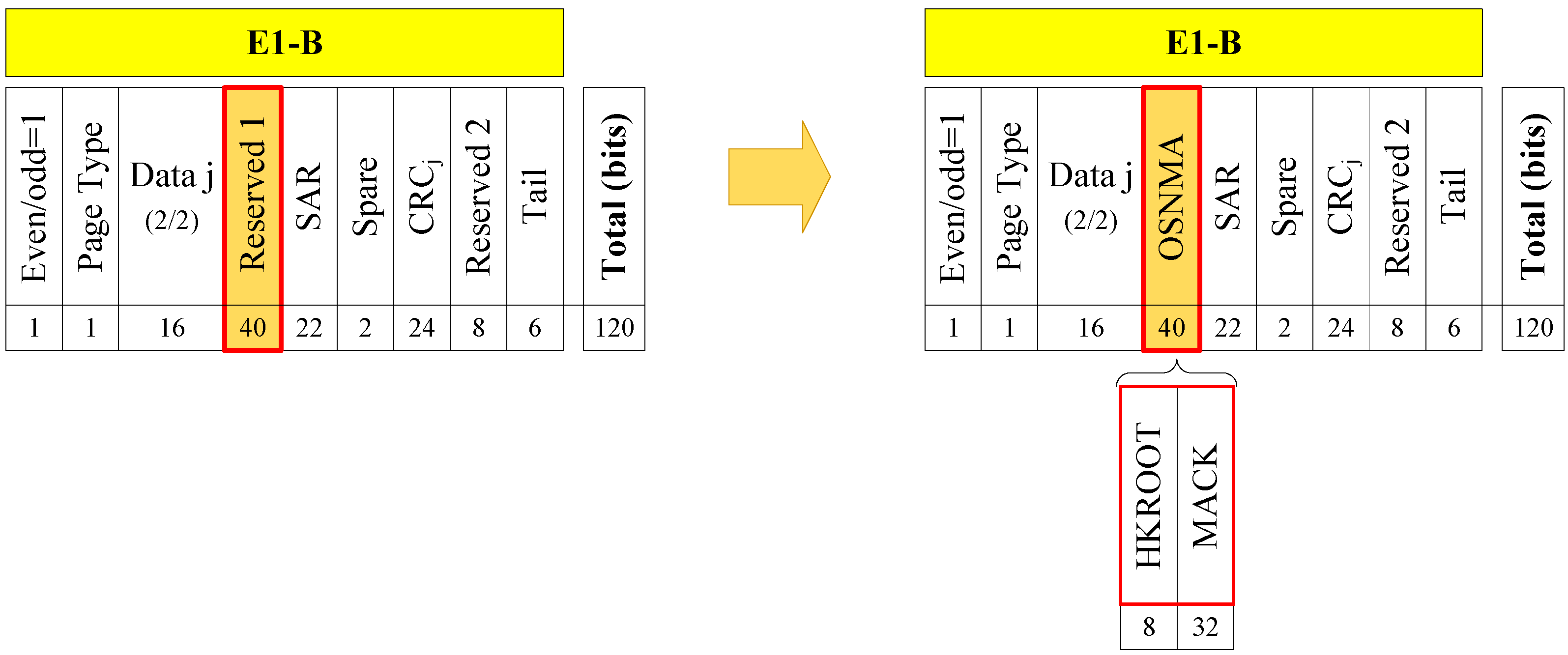
Figure 2. GALILEO NMA message structure [21].
2) SCA
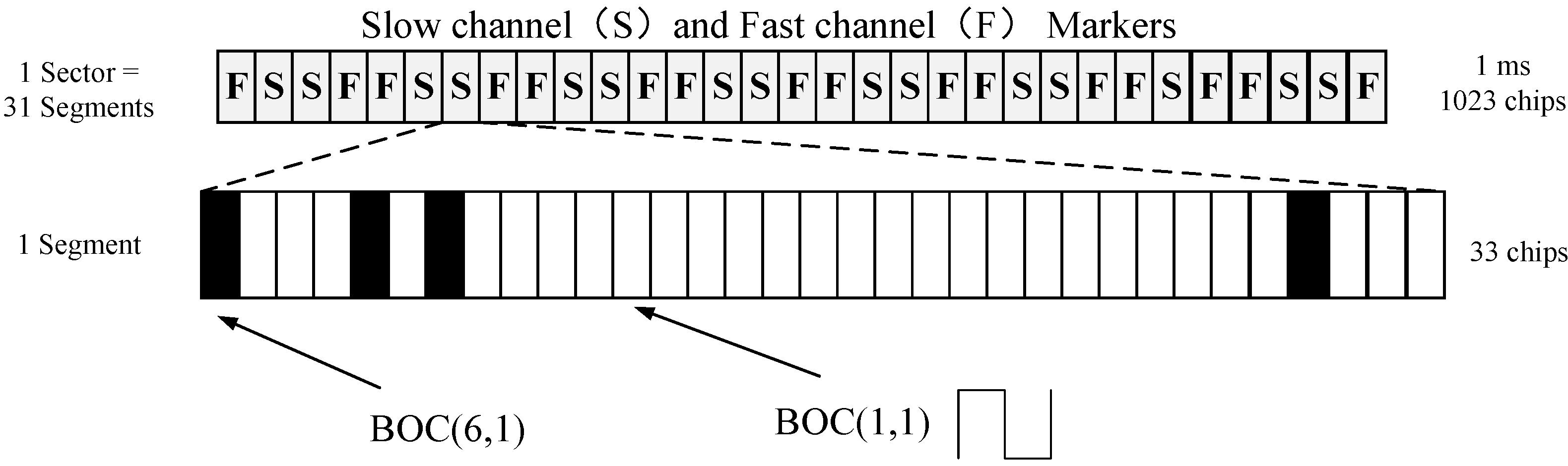
SCA adopts the characteristics of unpredictable authentication spreading chips, and implements authentication processing in the power domain, which can provide spoofing protection in the pseudorange domain. The typical SCA is the CHIMERA signal, as shown in the Figure 3. Based on the TMBOC (Time-Multiplexed Binary Offset Carrier) signal, the 1 ms sector is divided into 31 segments via a combination of time division and time hopping, and different authentication channel (fast channel and slow channel) are assigned for each segment. The authentication codes are randomly replaced for 29 BOC(1,1) in each segment of 33 chips, and the four BOC(6,1) chips are never modified [22].
| Type | Indicators | Receiver Processing | Feature |
|---|---|---|---|
| NMA [21] | Galileo-OSNMA Time Between Authentication: 10 s |
Message bit authentication using Message Authentication Code (MAC) | The project implementation is less difficult, the security level is not as good as SCA, and it can be processed in real time at the terminal. |
| SCA [22] | NTS3-CHIMERA Time Between Authentication for slow channel: 180 s Time Between Authentication for fast channel: 1.5 s or 6 s |
Power Domain Authentication Using Sampled Data for Spreading Code Correlation Processing | The pseudorange can be authenticated. The authentication requires data caching, and the project implementation is costly. |
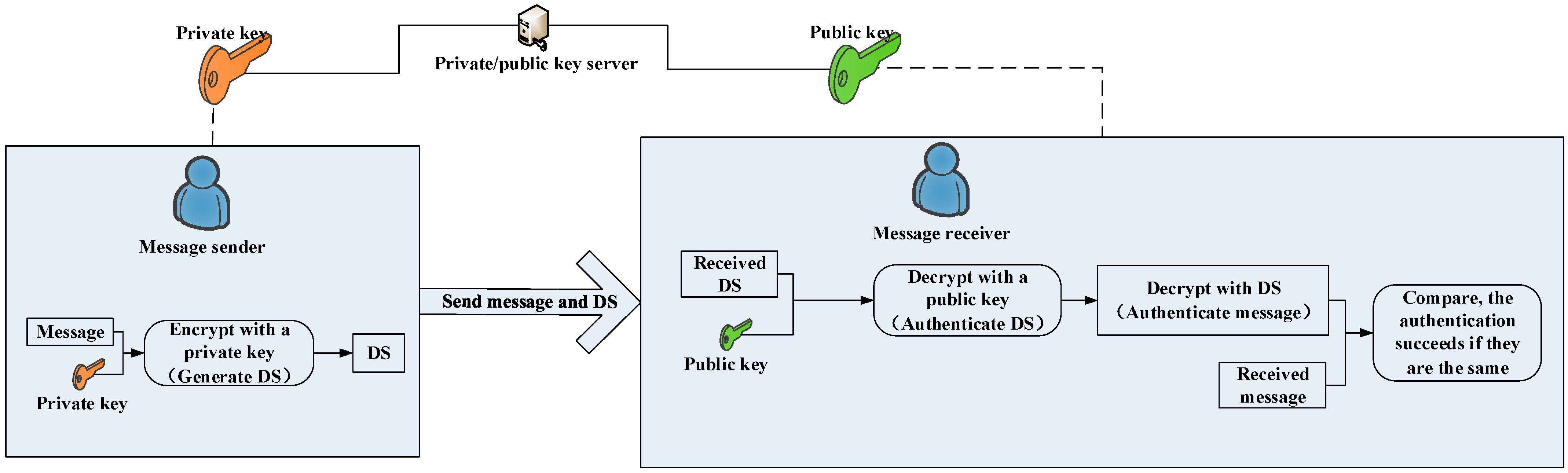
2.1.2. Satellite Navigation Message Authentication Type
2.2. Technical Architecture
2.3. Incremental Capability
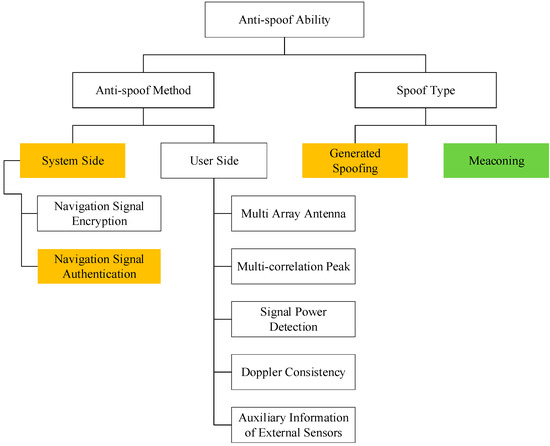
- (1)
-
Anti-spoofing method
| Anti-Spoofing Method | Description | Effect |
|---|---|---|
| Navigation signal encryption [29] | Encrypted signals serve authorized users, making it difficult for attackers to predict signals | High |
| Navigation signal authentication [30] | It is difficult for spoofed attackers to predict the authentication message/spreading code | High |
| DOA detection based on multi-array antennas [7][8] | The spoofing signal is generally emitted from a single transmitting antenna, and its satellites come from the same direction, while the real satellites of the signal come from different directions | High |
| Multiple correlation peaks [31][32] | The superposition of the spoofed signal and the real signal will bring multiple correlation peaks, and it will also cause distortion of the correlation peaks | Medium |
| Signal power [33][34] | The spoofing signal has more power, and the signal power changes during the spoofing implementation | Medium |
| Doppler consistency [35][36] | It is difficult for spoofing signals to keep the carrier Doppler shift consistent with the pseudocode Doppler shift | Medium |
| Auxiliary information of external sensors [4][5] | Spoofing signals cannot deceive sensors such as inertial navigation, chip-scale atomic clocks, and lidar | High |
- (2)
-
Anti-spoofing capability
| Spoofing | NMA | SCA | |
|---|---|---|---|
| Generated spoofing | Primary generated spoofing (low-cost software radio or commercial signal simulator) | High | High |
| Intermediate generated spoofing (receive GNSS signal first and then generate spoofing signal) | High | High | |
| SCER | Low | High/Medium | |
| Advanced generated spoofing (multiple intermediate generative spoofing) | High/Medium | High | |
| Meaconing | Simple meaconing (same delay for each satellite channel) | Low | Low |
| Multichannel meaconing (the delay of each satellite channel is inconsistent) | Low | Low | |
References
- EUSPA EO and GNSS Market Report 2022. Available online: https://www.euspa.europa.eu/euspa-market-report-2022-0 (accessed on 1 December 2022).
- Humphreys, T.E.; Ledvina, B.M.; Psiaki, M.L.; O’Hanlon, B.W.; Kintner, P.M., Jr. Assessing the spoofing threat: Development of a portable GPS civilian spoofer. In Proceedings of the 21st International Technical Meeting of the Satellite Division of the Institute of Navigation (ION GNSS 2008), Savannah, GA, USA, 16–19 September 2008; pp. 2314–2325.
- Bhatti, J.; Humphreys, T.E. Hostile Control of Ships via False GPS Signals: Demonstration and Detection. Navigation 2017, 64, 51–66.
- Wang, K.; Chen, S.; Pan, A. Time and Position Spoofing with Open Source Projects. In Proceedings of the Black Hat Europe 2015, Amsterdam, The Netherlands, 10–13 November 2015.
- Moafipoor, S.; Bock, L.; Fayman, J.A. Resilient Sensor Management for Dismounted Assured-PNT. In Proceedings of the 2020 International Technical Meeting of the Institute of Navigation, San Diego, CA, USA, 21–24 January 2020; pp. 1135–1147.
- Khanafseh, S.; Roshan, N.; Langel, S.; Chan, F.-C.; Joerger, M.; Pervan, B. GPS spoofing detection using RAIM with INS coupling. In Proceedings of the Position, Location and Navigation Symposium-PLANS, Monterey, CA, USA, 5–8 May 2014; pp. 1232–1239.
- Yang, Q.; Zhang, Y.; Tang, C.K. A combined antijamming and antispoofing algorithm for GPS Arrays. Int. J. Antennas Propag. 2019, 2019, 8012569.
- Lee, Y.S.; Yeom, J.S.; Noh, J.H.; Lee, S.J.; Jung, B.C. A novel GNSS spoofing detection technique with array antenna-based multi-PRN diversity. J. Position. Navig. Timing 2021, 10, 169–177.
- de Castro, H.V.; van der Maarel, G.; Safipour, E. The possibility and added-value of authentication in future Galileo open signal. In Proceedings of the 23th International Technical Meeting of the Satellite Division of the Institute of Navigation (ION 2010), Portland, OR, USA, 21–24 September 2010.
- Fernandez-Hernandez, I.; Rijmen, V.; Seco-Granados, G.; Simón, J.; Rodríguez, I. Design Drivers, Solutions and Robustness Assessment of Navigation Message Authentication for the Galileo Open Service. In Proceedings of the 27th International Technical Meeting of the Satellite Division of the Institute of Navigation (ION GNSS + 2014), Tampa, FL, USA, 8–12 September 2014; pp. 2810–2827.
- Walker, P.; Rijmen, V.; Fernandez-Hernandez, I.; Bogaardt, L.; Seco-Granados, G.; Simón, J.; Calle, D.; Pozzobon, O. Galileo Open Service Authentication: A Complete Service Design and Provision Analysis. In Proceedings of the 28th International Technical Meeting of the Satellite Division of the Institute of Navigation (ION GNSS + 2015), Tampa, FL, USA, 14–18 September 2015; pp. 3383–3396.
- Fernandez-Hernandez, I.; Rijmen, V.; Seco-Granados, G.; Simon, J.; Rodríguez, I.; David Calle, J. A Navigation Message Authentication Proposal for the Galileo Open Service. Navig. J. Inst. Navig. 2016, 63, 85–102.
- Nicola, M.; Motella, B.; Pini, M.; Falletti, E. Galileo OSNMA Public Observation Phase: Signal Testing and Validation. IEEE Access 2022, 10, 27960–27969.
- Manandhar, D.; Shibasaki, R. Authenticating GALILEO Open Signal using QZSS Signal. In Proceedings of the 31st International Technical Meeting of the Satellite Division of the Institute of Navigation (ION GNSS + 2018), Miami, FL, USA, 24–28 September 2018; pp. 3995–4003.
- Pravin, P. Navigation Message Authentication (NMA) for NavIC SPS; ICG-16: Abu Dhabi, United Arab Emirates, 2022.
- Anderson, J.M.; Carroll, K.L.; DeVilbiss, N.P.; Gillis, J.T.; Hinks, J.C.; O’Hanlon, B.W.; Rushanan, J.J.; Scott, L.; Yazdi, R.A. Chips-Message Robust Authentication (CHIMERA) for GPS Civilian Signals. In Proceedings of the 31th International Technical Meeting of the Satellite Division of the Institute of Navigation, ION GNSS + 2018, Portland, OR, USA, 25–29 September 2018.
- Fernandez-Hernandez, I. Snapshot and Authentication Techniques for Satellite Navigation; Aalborg University: Aalborg, Denmark, 2015.
- Curran, J.T.; Paonni, M. Securing GNSS: An End-to-end Feasibility Analysis for the Galileo Open-service. In Proceedings of the 27th International Technical Meeting of the Satellite Division of the Institute of Navigation (ION GNSS + 2014), Tampa, FL, USA, 8–12 September 2014; pp. 2828–2842.
- Gkougkas, E.; Pany, T.; Eissfeller, B. Sensitivity Analysis of Potential Future Authentication Components for Open Service GNSS Signals. In Proceedings of the 31st International Technical Meeting of The Satellite Division of the Institute of Navigation (ION GNSS + 2018), Miami, FL, USA, 24–28 September 2018.
- Shen, C.; Guo, C. Study and Evaluation of GNSS Signal Cryptographic Authentication Defenses. GNSS World China 2018, 43, 7–12.
- European Union. GALILEO Open Service Navigation Message Authentication (OSNMA) Receiver Guidelines for the Test Phase; European Union Issue 1.0; European Union: Luxembourg, 2021.
- Air Force Research Laboratory Space Vehicles Directorate Advanced GPS Technology. Chips Message Robust Authentication (Chimera) Enhancement for the L1C Signal: Space Segment/User Segment Interface. 16 April 2019. CHAPMAN D C. Chips Message Robust Authentication (Chimera) Enhancement for the L1C Signal: Space Seg-ment/User Segment Interface (IS-AGT-100): Advanced GPS Technologies Program. 2019.
- Hiroshi, Y. Angō Gijutsu Nyūmon, 3rd ed.; Post & Telecom Press: Beijing, China, 2016. (In Chinese)
- Fernández-Hernández, I.; Walter, T.; Neish, A.M.; Anderson, J.; Mabilleau, M.; Vecchione, G.; Châtre, E. SBAS message authentication: A review of protocols, figures of merit and standardization plans. In Proceedings of the 2021 International Technical Meeting of the Institute of Navigation, Auditorium UPC, Barcelona, Spain, 25–28 January 2021; pp. 111–124.
- Neish, A.; Walter, T.; Powell, J.D. SBAS data authentication: A concept of operations. In Proceedings of the 32nd International Technical Meeting of the Satellite Division of the Institute of Navigation (ION GNSS + 2019), Miami, FL, USA, 16–20 September 2019; pp. 1812–1823.
- Neish, A.; Walter, T.; Enge, P. Parameter selection for the TESLA keychain. In Proceedings of the 31st International Technical Meeting of the Satellite Division of the Institute of Navigation (ION GNSS + 2018), Miami, FL, USA, 24–28 September 2018; pp. 2155–2171.
- Perrig, A.; Canetti, R.; Tygar, J.D. Efficient authentication and signing of multicast streams over lossy channels. In Proceedings of the 2000 IEEE Symposium on Security and Privacy, Berkeley, CA, USA, 14–17 May 2000; pp. 56–73.
- Caparra, G.; Sturaro, S.; Laurenti, N.; Wullems, C. Evaluating the Security of One-Way Key Chains in TESLA-Based GNSS Navigation Message Authentication Schemes. In Proceedings of the 2016 International Conference on Localization and GNSS (ICL-GNSS), Barcelona, Spain, 28–30 June 2016; pp. 1–6.
- Zhao, X.; Liu, C. GPS Military Signal Security Protection and Password Management. Mod. Navig. 2020, 11, 14–19.
- Margaria, D.; Motella, B.; Anghileri, M.; Floch, J.-J.; FernandezHernandez, I.; Paonni, M. Signal structure-based authentication for civil GNSSs: Recent solutions and perspectives. IEEE Signal Process. Mag. 2017, 34, 27–37.
- Li, J.Z.; Zhu, X.W.; Ouyang, M.J.; Li, W.Q.; Chen, Z.K.; Dai, Z.Q. Research on multi-peak detection of small delay spoofing signal. IEEE Access 2020, 8, 151777–151787.
- Khan, A.M.; Ahmad, A. Global navigation satellite systems spoofing detection through measured autocorrelation function shape distortion. Int. J. Satell. Commun. Netw. 2022, 40, 148–156.
- Dehghanian, V.; Nielsen, J.; Lachapelle, G. GNSS spoofing detection based on receiver C/N0 estimates. In Proceedings of the International Technical Meeting of the Satellite Division of the Institute of Navigation, Nashville, TN, USA, 17–21 September 2012; pp. 2875–2884.
- Elezi, E.; Cankaya, G.; Boyaci, A.; Yarkan, S. A detection and identification method based on signal power for different types of electronic jamming attacks on GPS signals. In Proceedings of the 2019 IEEE 30th Annual International Symposium on Personal, Indoor and Mobile Radio Communications (PIMRC), Istanbul, Turkey, 8–11 September 2019; pp. 1–5.
- He, L.; Li, H.; Lu, M.Q. Global navigation satellite system spoofing detection technique based on the doppler ripple caused by vertical reciprocating motion. IET Radar Sonar Navig. 2019, 13, 1655–1664.
- He, L.; Li, H.; Lu, M.Q. Dual-antenna GNSS spoofing detection method based on doppler frequency difference of arrival. GPS Solut. 2019, 23, 1–14.
- Bian, S.; Hu, Y.; Ji, B. Research status and prospect of GNSS anti-spoofing technology. Sci. Sin. Inf. 2017, 47, 275–287.
- Zhao, X.; Chen, X.; Guo, X. A Repeater Spoofing Method for GNSS Clock of receiver. Telecommun. Eng. 2020, 60, 1415–1419.
- Arizabaleta, M.; Gkougkas, E.; Pany, T. A Feasibility Study and Risk Assessment of Security Code Estimation and Replay (SCER) Attacks. In Proceedings of the 32nd International Technical Meeting of the Satellite Division of the Institute of Navigation (ION GNSS + 2019), Miami, FL, USA, 16–20 September 2019.





