As the Global Navigation Satellite System (GNSS) is widely used in all walks of life, the signal structure of satellite navigation is open, and the vulnerability to spoofing attacks is also becoming increasingly prominent, which will seriously affect the credibility of navigation, positioning, and timing (PNT) services. Satellite navigation signal authentication technology is an emerging technical means of improving civil signal anti-spoofing on the satellite navigation system side, and it is also an important development direction and research focus of the GNSS.
- satellite navigation
- Beidou navigation satellite system
- credible navigation
1. Introduction
2. 、Principles and Technical Architecture of the Satellite Navigation Signal Authentication
Satellite navigation signal authentication uses cryptographic methods to improve the anti-spoofing of civil GNSS signals and provides users with more credible PNT services. First of all, this section introduces the principle of satellite navigation signal authentication. Then, it describes the technical architecture of navigation signal authentication based on space segment, ground section and user segment, Finally, it analyzes the new capabilities brought by satellite navigation signal authentication, as well as the advantages and limitations in anti-spoofing.2.1. Principles
Satellite navigation signal authentication technology aims to add encrypted authentication marks to satellite navigation signals to prevent satellite navigation signals from GNSS spoofing attacks. It is a new GNSS anti-spoofing technology that combines information security and navigation signal design. The sender (navigation satellite) uses cryptography technology to generate an "authentication symbol", which is embedded in the existing satellite navigation signal and broadcast to users. The receiver (GNSS user terminal) verifies the "authentication symbol" to confirm whether the received navigation signal is from a real satellite in orbit, and whether the navigation message has been forged or tampered with [17][21]. Satellite navigation signal authentication technology has the following characteristics:
1) One-way broadcast.
The satellite navigation signal uses the navigation satellite broadcast signal to provide PNT services for terrestrial users, and its signal characteristics have the characteristics of one-way broadcast. Therefore, satellite navigation signal authentication technology should be based on the broadcast system authentication framework.
2) Signal disclosure transmission.
Satellite navigation signals use the public signal structure to broadcast signals, and their signal authentication needs to have the characteristics of public signal transmission.
3) Compatible with existing signal structure.
The authentication of satellite navigation signals will not affect existing GNSS services, so its authentication signal design should be compatible with existing signal structure.
2.1.1. Satellite Navigation Signal Authentication Type
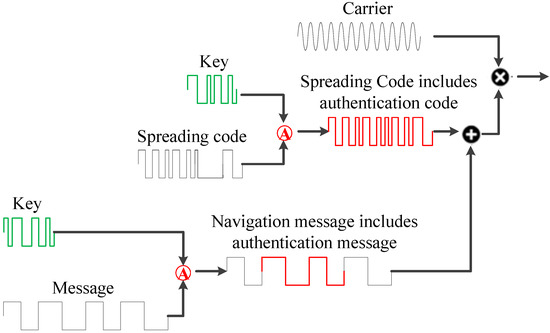
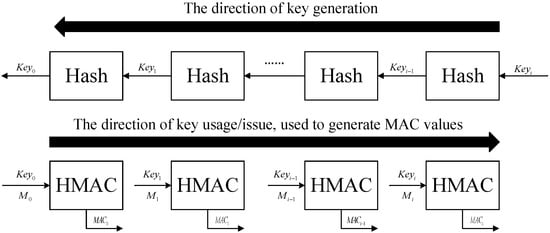
Satellite navigation signals include the carrier, pseudocodes, and message. The newly added authentication mark can be added to the navigation message [18][22] and spreading spectrum codes [19][23]. Figure 1 shows the generation of the navigation message including authentication message and the spreading spectrum code including authentication code. Therefore, the satellite navigation signal authentication type is divided into Navigation Message Authentication (NMA) and Spreading Code Authentication (SCA) [20][24].
1) NMA
NMA uses message bit-level authentication to realize navigation source authentication. Its advantage is that the modification of the existing signal system is small and the signal modulation method is not changed. It’s just to upgrade the software of the user receiver. The engineering realization cost is small. The Galileo E1 OSNMA structure is shown as Figure 2. Galileo reserved a 40-bit message in the early ICD, and the ICD announced in 2021 clarified that the 40-bit message is the navigation authentication message [21][25].
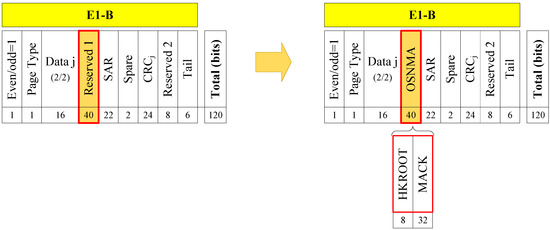
Figure 2. GALILEO NMA message structure [21].
GALILEO NMA message structure [25].
2) SCA
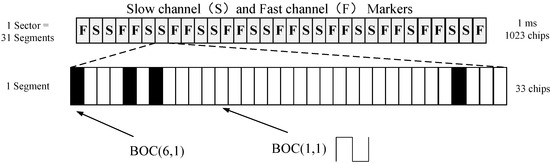
SCA adopts the characteristics of unpredictable authentication spreading chips, and implements authentication processing in the power domain, which can provide spoofing protection in the pseudorange domain. The typical SCA is the CHIMERA signal, as shown in the Figure 3. Based on the TMBOC (Time-Multiplexed Binary Offset Carrier) signal, the 1 ms sector is divided into 31 segments via a combination of time division and time hopping, and different authentication channel (fast channel and slow channel) are assigned for each segment. The authentication codes are randomly replaced for 29 BOC(1,1) in each segment of 33 chips, and the four BOC(6,1) chips are never modified [22][26].
| Type | Indicators | Receiver Processing | Feature |
|---|---|---|---|
| NMA [21][25] | Galileo-OSNMA Time Between Authentication: 10 s |
Message bit authentication using Message Authentication Code (MAC) | The project implementation is less difficult, the security level is not as good as SCA, and it can be processed in real time at the terminal. |
| SCA [22][26] | NTS3-CHIMERA Time Between Authentication for slow channel: 180 s Time Between Authentication for fast channel: 1.5 s or 6 s |
Power Domain Authentication Using Sampled Data for Spreading Code Correlation Processing | The pseudorange can be authenticated. The authentication requires data caching, and the project implementation is costly. |
2.1.2. Satellite Navigation Message Authentication Type
The navigation message authentication protocol includes Digital Signatures (DS) and the Timed Efficient Stream Loss-Tolerant Authentication (TESLA). Digital signatures are implemented based on asymmetric cryptography (also known as public key cryptography). The sender uses the private key to sign the message, and the receiver uses the public key to verify the signature of the message [23][27]. Digital signatures commonly use the Elliptic Curve Digital Signature Algorithm (ECDSA), which has the characteristics of high security and complex algorithm strength. In addition, European scholars proposed EC Schnorr’s digital signature algorithm [24][18]. The digital signature schematic is shown in Figure 4 below.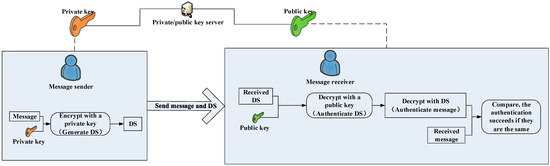
2.2. Technical Architecture
The satellite navigation system consists of the space segment, ground segment, and user segment. Based on the existing satellite navigation system, the satellite navigation signal authentication will be extended to the space segment, the ground segment, the user terminal, and the network auxiliary segment. The space segment adds the authentication spreading code/authentication messages to the broadcast downlink satellite navigation signal, the user segment authenticates the received satellite navigation signal, and the network auxiliary segment uses the communication base station (terrestrial communication/satellite communication) to provide network auxiliary authentication information. If there is a GNSS spoofing signal in the actual environment, the user segment can identify whether the current signal is a spoofing signal through the authentication of the message/spreading spectrum code. The architecture of the satellite navigation signal authentication is shown in Figure 6.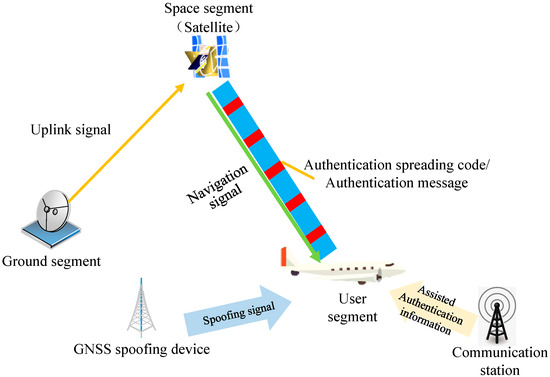
2.3. Incremental Capability
Navigation signal authentication technology will bring a new service to the GNSS, which neither improves the accuracy nor augments the integrity and continuity, just focuses on improving the anti-spoofing capability of GNSS civil signals to provide users with more credible PNT services. Signal authentication is a system-side anti-spoof technology which can resist generative spoofing. The orange part in Figure 7 represents the incremental capability.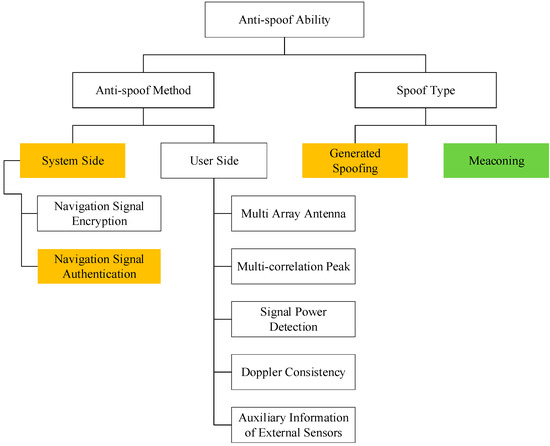
- (1)
-
Anti-spoofing methodTable 3.Comparison of common anti-spoofing algorithms.
Effect Navigation signal encryption [ Spoofing NMA SCA 29][32] Encrypted signals serve authorized users, making it difficult for attackers to predict signals High Generated spoofing Primary generated spoofing (low-cost software radio or commercial signal simulator) High High Navigation signal authentication [30][17] It is difficult for spoofed attackers to predict the authentication message/spreading code High Intermediate generated spoofing (receive GNSS signal first and then generate spoofing signal) High High DOA detection based on multi-array antennas [7][8][7,8] The spoofing signal is generally emitted from a single transmitting antenna, and its satellites come from the same direction, while the real satellites of the signal come from different directions High Multiple correlation peaks [ SCER Low High/Medium 31][32][33,34] The superposition of the spoofed signal and the real signal will bring multiple correlation peaks, and it will also cause distortion of the correlation peaks Medium Advanced generated spoofing (multiple intermediate generative spoofing) High/Medium High Signal power [33][34][35,36] The spoofing signal has more power, and the signal power changes during the spoofing implementation Medium Meaconing Simple meaconing (same delay for each satellite channel) Low Low Doppler consistency [35][36][37,38] It is difficult for spoofing signals to keep the carrier Doppler shift consistent with the pseudocode Doppler shift Medium Multichannel meaconing (the delay of each satellite channel is inconsistent) Low Low Auxiliary information of external sensors [4][5][4,5] Spoofing signals cannot deceive sensors such as inertial navigation, chip-scale atomic clocks, and lidar High - (2)
-
Anti-spoofing capabilityGenerated spoofing means that the attacker generates a spoofing signal with the exact same structure as the real GNSS signal [37][39], which utilizes the known vulnerabilities of the civilian signal ICD to generate a false GNSS spoofing signal and broadcast it to the target receiver. The prerequisite for satellite navigation signal authentication is that the spoofing attacker cannot break the cryptographic algorithm, so that the authentication message/spreading code cannot be forged. Therefore, satellite navigation signal authentication can solve the generative spoofing attack to civilian users. Meaconing means that the attacker receives the navigation signal [38][40], performing proper delay and power amplification on the real GNSS signal, and then broadcasts the meaconing signal to the target receiver. The meaconing does not change the message and spreading code, so the satellite navigation signal authentication effect is not good for this method. In addition to the above two common spoofing methods, Security Code Estimation and Replay (SCER) [39][41] has also been proposed in recent years. This method is to receive the real signal and estimate the encrypted or authenticated message in real time as much as possible. Then, the encrypted or authenticated message in the signal is reassembled and sent. SCER predicts the authentication message based on the security code estimation method, which is effective for security codes with a low symbol rate (navigation message), but less effective for security codes with a high symbol rate (spreading code).Table 4. Signal authentication anti-spoofing effect