
| Version | Summary | Created by | Modification | Content Size | Created at | Operation |
|---|---|---|---|---|---|---|
| 1 | Adnan Tahir | -- | 2113 | 2023-05-12 19:27:36 | | | |
| 2 | Camila Xu | Meta information modification | 2113 | 2023-05-15 05:37:16 | | | | |
| 3 | Camila Xu | Meta information modification | 2113 | 2023-05-15 05:38:11 | | | | |
| 4 | Camila Xu | Meta information modification | 2113 | 2023-05-15 05:38:58 | | |
Video Upload Options
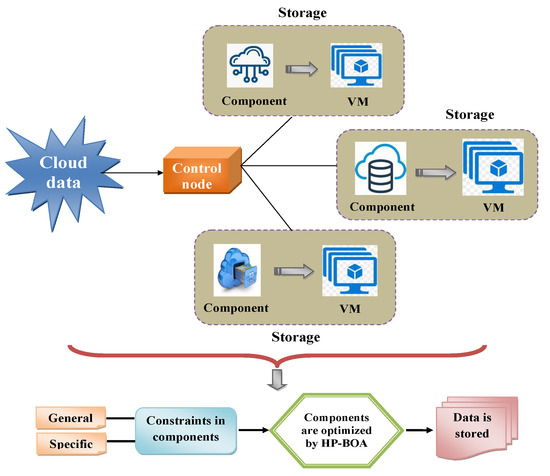
The prime objective of the cloud data storage process is to make the service, irrespective of being infinitely extensible, a more reliable storage and low-cost model that also encourages different data storage types. Owing to the storage process, it must satisfy the cloud users’ prerequisites. Nevertheless, storing massive amounts of data becomes critical as this affects the data quality or integrity. Hence, this poses various challenges for existing methodologies. An efficient, reliable cloud storage model is proposed using a hybrid heuristic approach to overcome the challenges. The prime intention of the proposed system is to store the data effectively in the cloud environment by resolving two constraints, which are general and specific (structural). The cloud data were initially gathered and used to analyze the storage performance. Since the data were extensive, different datasets and storage devices were considered. Every piece of data as specified by its corresponding features, whereas the devices were characterized by the hardware or software components. Subsequently, the objective function was formulated using the network’s structural and general constraints. The structural constraints were determined by the interactions between the devices and data instances in the cloud. Then, the general constraints regarding the data allocation rules and device capacity were defined. To mitigate the constraints, the components were optimized using the Hybrid Pelican–Billiards Optimization Algorithm (HP-BOA) to store the cloud data. Finally, the performance was validated, and the results were analyzed and compared against existing approaches. Thus, the proposed model exhibited the desired results for storing cloud data appropriately.
1. Introduction
| Author [Citation] | Methodology | Features | Challenges |
|---|---|---|---|
| Fan et al. [12] | CMPSO | • It provides highly secure and reliable resource allocation over wireless networks. | • It does not provide a fine-tuned strategy for accommodating connectivity. |
| • It has a low computational cost. | • The power consumption of the entire system is very high. | ||
| Li et al. [13] | ANC | • It is easy to implement with high network performance in terms of robustness and fidelity. | • This strategy is not flexible because of the changing channel qualities in wireless networks. |
| • The communication throughput is very high. | • It decreases the total response time of a user when the workload is high. | ||
| Assi et al. [14] | Tabu meta-heuristic |
• It meets the wireless requirements such as heterogeneity, reliability, and lowlatency. | • If an unexpected power outage occurs, the valuable data stored in the data center could be lost and unrecoverable. |
| • It provides high synchronization and updating of the data over wireless networks. | • It has a high cost for protectingthe cloud storage system. | ||
| Zaharie et al. [15] | OMT | • It provides automatic services when the customer requires more services over the network channel. | • It has a higher offloading failure probability; therefore, the transmission reliability is decreased. |
| • It can easily interface with the applications and data sources. | • It has less scalability in the search space. | ||
| Suba et al. [16] | EMSA algorithm |
• It is highly elastic, has a lower cost, and is trustworthy. | • It does not meet the bandwidth requirements and has a low maturity level. |
| • The information is quickly accessible by the users, and it is more reliable. | • It does not have any loop-back connectivity and access control. | ||
| • It has high, virtually limitless storage capacity. | |||
| Shao et al. [17] | PKI-based signature scheme |
• It provides greater hardware redundancy. | • The packet loss ratio is very high. |
| • It has the ability of automatic storage failover. | • The signal-to-noise ratio is very high during packet transmission. | ||
| Akash et al. [18] | ACO | • It achieves better performance by balancing the network load. | • It may result in large network delays, and it has a high overhead. |
| • It provides high security and integrity of the information over the network channel. | • The quality of service is low in terms of cost, security, and latency. | ||
| Sangeetha et al. [19] | Fibonacci cryptographic |
• It can handle the network traffic. | • It has a high consumption of network resources. |
| • It provides lowcomputational complexity. | • It has poornode authentication and a high transmission time. | ||
| • The caching ability is less. |
2. Reliable Cloud Data Storage: System Model and Problem Formulation
2.1. System Model
- 1
-
File storage: The files are hierarchically placed in this type. The information is stored in the metadata format of every file. Hence, the files are managed in higher-level abstraction types. Thus, it aids in improving performance.
- 2
-
Block storage: Here, the data or files are segmented into different chunks and represented with block addresses. This process does not contain the server for authorization.
- 3
-
Object storage: The encapsulation is performed with the object and metadata. Since the data belong to any type, they are distributed over the cloud. This also ensures the scalability and reliability of the system.
-
Data reliability and availability: By storing the data with more machines or servers, the data user can obtain the encoded data to be deciphered further as the original data. When any of the servers has a fault, they are then used by the other effective servers, thereby enhancing the data integrity and reliability of the cloud network.
-
Security: The better system enhances the security level. It also verifies the data integrity and confidentiality, which protects the network from any corrupted services.
-
Offline data owner: Once the data are outsourced to a server or machine, there is no need to check the integrity of the stored data in the system.
-
Efficiency: Due to this objective, the system’s efficacy is reached in terms of less storage space, resolving the overhead problem in communication and computation, and so on.
References
- Tang, B.; Fedak, G. WukaStore: Scalable, Configurable and Reliable Data Storage on Hybrid Volunteered Cloud and Desktop Systems. IEEE Trans. Big Data 2017, 8, 85–98.
- Sookhak, M.; Richard Yu, F.; Zomaya, A.Y. Auditing Big Data Storage in Cloud Computing Using Divide and Conquer Tables. IEEE Trans. Parallel Distrib. Syst. 2018, 29, 999–1012.
- Ghaffar, Z.; Ahmed, S.; Mahmood, K.; Islam, S.H.; Hassan, M.M.; Fortino, G. An improved authentication scheme for remote data access and sharing over cloud storage in cyber-physical-social-systems. IEEE Access 2020, 8, 47144–47160.
- Yuan, Y.; Zhang, J.; Xu, W. Dynamic Multiple-Replica Provable Data Possession in Cloud Storage System. IEEE Access 2020, 8, 120778–120784.
- Mendes, R.; Oliveira, T.; Cogo, V.; Neves, N.; Bessani, A. Charon: A Secure Cloud-of-Clouds System for Storing and Sharing Big Data. IEEE Trans. Cloud Comput. 2021, 9, 1349–1361.
- Li, Y.; Yu, Y.; Min, G.; Susilo, W.; Ni, J.; Choo, K.K.R. Fuzzy identity-based data integrity auditing for reliable cloud storage systems. IEEE Trans. Dependable Secur. Comput. 2019, 16, 72–83.
- Yang, S.; Wieder, P.; Aziz, M.; Yahyapour, R.; Fu, X.; Chen, X. Latency-sensitive data allocation and workload consolidation for cloud storage. IEEE Access 2018, 6, 76098–76110.
- Wen, Z.; Cala, J.; Watson, P.; Romanovsky, A. Cost Effective, Reliable, and Secure Workflow Deployment over Federated Clouds. In Proceedings of the 2015 IEEE 8th International Conference on Cloud Computing, CLOUD 2015, New York, NY, USA, 27 June–2 July 2015; pp. 604–612.
- Lu, S.; Xia, Q.; Tang, X.; Zhang, X.; Lu, Y.; She, J. A reliable data compression scheme in sensor-cloud systems based on edge computing. IEEE Access 2021, 9, 49007–49015.
- Lu, H.; Foh, C.H.; Wen, Y.; Cai, J. Delay-Optimized File Retrieval under LT-Based Cloud Storage. IEEE Trans. Cloud Comput. 2015, 5, 656–666.
- Zhao, X.; Lucani, D.E.; Shen, X.; Wang, H. Reliable IoT storage: Minimizing bandwidth use in storage without newcomer nodes. IEEE Commun. Lett. 2018, 22, 1462–1465.
- Liu, X.; Fan, L.; Wang, L.; Meng, S. Multiobjective Reliable Cloud Storage with Its Particle Swarm Optimization Algorithm. Math. Probl. Eng. 2016, 2016.
- Li, J.; Liu, Y.; Zhang, Z.; Ren, J.; Zhao, N. Towards Green IoT Networking: Performance Optimization of Network Coding Based Communication and Reliable Storage. IEEE Access 2017, 5, 8780–8791.
- Kherraf, N.; Sharafeddine, S.; Assi, C.M.; Ghrayeb, A. Latency and Reliability-Aware Workload Assignment in IoT Networks with Mobile Edge Clouds. IEEE Trans. Netw. Serv. Manag. 2019, 16, 1435–1449.
- Eraşcu, M.; Micota, F.; Zaharie, D. Scalable optimal deployment in the cloud of component-based applications using optimization modulo theory, mathematical programming and symmetry breaking. J. Log. Algebr. Methods Program. 2021, 121, 100664.
- Sathya, A.; Raja, S.K.S. Privacy Preservation-Based Access Control Intelligence for Cloud Data Storage in Smart Healthcare Infrastructure. Wirel. Pers. Commun. 2021, 118, 3595–3614.
- Ji, Y.; Shao, B.; Chang, J.; Bian, G. Flexible identity-based remote data integrity checking for cloud storage with privacy preserving property. Clust. Comput. 2022, 25, 337–349.
- Lee, O.T.; Akash, G.J.; Kumar, S.D.; Chandran, P. Storage Node Allocation Methods for Erasure Code-based Cloud Storage Systems. Arab. J. Sci. Eng. 2019, 44, 9127–9142.
- Sumathi, M.; Sangeetha, S. A group-key-based sensitive attribute protection in cloud storage using modified random Fibonacci cryptography. Complex Intell. Syst. 2021, 7, 1733–1747.
- Wen, M.; Ota, K.; Li, H.; Lei, J.; Gu, C.; Su, Z. Secure data deduplication with reliable key management for dynamic updates in CPSS. IEEE Trans. Comput. Soc. Syst. 2015, 2, 137–147.





