Your browser does not fully support modern features. Please upgrade for a smoother experience.

Submitted Successfully!
Thank you for your contribution! You can also upload a video entry or images related to this topic.
For video creation, please contact our Academic Video Service.
| Version | Summary | Created by | Modification | Content Size | Created at | Operation |
|---|---|---|---|---|---|---|
| 1 | Javier Bermejo Higuera | -- | 2481 | 2024-03-07 19:44:02 | | | |
| 2 | Jessie Wu | + 5 word(s) | 2486 | 2024-03-08 03:15:17 | | | | |
| 3 | Jessie Wu | + 2 word(s) | 2488 | 2024-03-08 03:16:22 | | |
Video Upload Options
We provide professional Academic Video Service to translate complex research into visually appealing presentations. Would you like to try it?
Cite
If you have any further questions, please contact Encyclopedia Editorial Office.
Ortiz-Ruiz, E.; Bermejo, J.R.; Sicilia, J.A.; Bermejo, J. Advanced Persistent Thread and Common Systems Behavioral Sources. Encyclopedia. Available online: https://encyclopedia.pub/entry/55988 (accessed on 01 May 2026).
Ortiz-Ruiz E, Bermejo JR, Sicilia JA, Bermejo J. Advanced Persistent Thread and Common Systems Behavioral Sources. Encyclopedia. Available at: https://encyclopedia.pub/entry/55988. Accessed May 01, 2026.
Ortiz-Ruiz, Emanuel, Juan Ramón Bermejo, Juan Antonio Sicilia, Javier Bermejo. "Advanced Persistent Thread and Common Systems Behavioral Sources" Encyclopedia, https://encyclopedia.pub/entry/55988 (accessed May 01, 2026).
Ortiz-Ruiz, E., Bermejo, J.R., Sicilia, J.A., & Bermejo, J. (2024, March 07). Advanced Persistent Thread and Common Systems Behavioral Sources. In Encyclopedia. https://encyclopedia.pub/entry/55988
Ortiz-Ruiz, Emanuel, et al. "Advanced Persistent Thread and Common Systems Behavioral Sources." Encyclopedia. Web. 07 March, 2024.
Copy Citation
The rapid proliferation of Internet of Things (IoT) networks in Colombia and various global regions has unquestionably resulted in a significant increase in cyberattacks. This rapid expansion of interconnected devices carries significant implications for individuals, organizations, and governing entities.
machine learning techniques
cyberattack prevention
Internet of Things (IoT)
1. Introduction
As a result, deficiencies in security updates and transparency regarding Internet of Thing (IoT) device security, coupled with unsafe internet deployment practices, leave these devices vulnerable to cybercriminal activities. Periodic assessments conducted by cybersecurity firms highlight the suboptimal security landscape of IoT infrastructure. Given the widespread deployment of IoT devices not only in private environments [1], but also in a variety of settings, including critical infrastructure installations [2], it is imperative to protect these devices and their associated infrastructures. Numerous techniques are currently available to identify cyberattacks targeting IoT infrastructures. Machine-based methodologies offer distinct advantages over signature-based analysis, such as enhanced detection precision and reduced false positives [3] (p. 5), while also facilitating the identification of both anomalies and novel attack characteristics. Nevertheless, these approaches are not devoid of drawbacks [4], such as the demand for supplementary hardware resources and diminished data-processing velocities.
A viable countermeasure to this burgeoning menace involves the employment of machine learning methodologies. By harnessing intelligent algorithms, detection and prevention of cyber-intrusions upon IoT infrastructures become feasible. Nevertheless, it is essential to recognize these techniques’ limitations and necessitate scrupulous supervision and perpetual modification to outpace the everchanging tactics employed by cyber-malefactors [2].
-
Colombia’s vulnerability to cyber-intrusions underscores the immediacy for more robust cybersecurity provisions [2]. As the nation’s IoT network experiences continue growth, the likelihood of more severe breaches intensifies, jeopardizing personal privacy and national security.
-
To effectively attenuate these hazards, it is imperative for individuals, organizations, and governing authorities to engage in close cooperation towards devising comprehensive cybersecurity protocols tailored explicitly for IoT systems [2]. Unswerving vigilance and anticipatory endeavors are crucial in maintaining a strategic advantage over nefarious actors seeking to capitalize on susceptibilities within Colombia’s rapidly developing digital terrain [2].
-
This document provides an explanation of the utilization of machine learning algorithms within the Internet of Things (IoT) security landscape [5]. The transparency and traceability afforded by blockchain facilitate secure and verifiable data transactions, enabling ML algorithms to operate on trustworthy datasets [6]. This synergy not only fortifies the reliability of AI-driven decisions in IoT applications but also establishes a resilient defense against potential security breaches, providing a meticulous overview of fundamental principles and key attributes technology, elucidating how these features can be strategically harnessed to augment the capabilities of AI in application issues.
-
In general, each cyber-attack has a solution that improves the impact on the economy [7] and the introduction of good practices for globalization change:
-
Symbiotic integration for decentralized economies: Delving into the synergistic potential of integrating AI and blockchain [8], elucidating how this union could cultivate a novel ecosystem characterized by decentralized economic structures. Additionally, outlining the inherent benefits derived from this transformative integration.
-
Comprehensive taxonomy of IoT ecosystem: Offering a meticulous taxonomy encompassing diverse dimensions, including blockchain platforms, architectural frameworks, infrastructure typologies, and consensus protocols. This taxonomy is complemented by an exploration of existing applications of decentralized AI within this comprehensive framework.
-
Examination of practical applications: Presenting a thorough examination and discussion of multiple practical use cases wherein AI applications leverage blockchain technology across various vertical domains.
-
The ongoing research on Internet of Things (IoT) anomaly detection [9][10] is a rapidly expanding field. This growth necessitates an analysis of application trends and current gaps. The vast majority of publications focus on areas such as network and infrastructure security, sensor monitoring [11], and applications for smart homes and smart cities, and are extending into even more sectors. Recent advancements in the field have increased the need to study the numerous applications of anomaly detection [3][6][12] in IoT. This resesarch commences with a summary of detection methods based in ML and applications into the Colombia ecosystem, followed by a discussion of categorizing anomaly detection algorithms in IoT. Subsequently, researchers scrutinize current publications to identify distinct application domains, examining selected documents based on researchers' search criteria. Different surveys encompass 64 documents among recent publications released between January 2019 and July 2021. In these recent publications, researchers observe a shortage of anomaly detection methodologies in IoT [13], for instance, when confronting the integration of systems with various sensors obtained with distributive data analytics, changes in data and conceptual shifts, and data augmentation where there is a scarcity of ground truth data.
2. Advanced Persistent Thread Comparison and Actual Perspective
Currently, advanced persistent threats (APTs) known to be associated with cyberattacks around the world have an imminent vision related with an actual perspective [14]. ENISA establishes a point of reference for all threats applying to assets related to information and communication technology (ICT) [15] and different scenarios such as IoT and Industrial Internet of Things (IIoT), where collaborative efforts among governments, industry leaders, and organizations are imperative to formulate comprehensive strategies that effectively tackle the expanding threat landscape surrounding IoT networks. Through strategic investments in cutting-edge security solutions and the adoption of proactive measures, including robust encryption protocols and advanced intrusion detection systems, researchers can successfully mitigate the risks associated with cyberattacks on critical infrastructures. Ref. [15] (p. 11) indicates an attacks incidents taxonomy related with a combination of cybercrime subject (motive), action (method), object (outcome). EUROPOL’s European Cybercrime Centre has categorized incidents based on their type and event, which is a crucial aspect of incident management along two vectors where organizations can effectively analyze and respond to various types of events in a structured manner [16]. With regard to APT events in a critical cyber infrastructure (CCI) in a digital ecosystem, APT types are defined by NIST (US National Institute of Standards and Technology) [17]. TTPS enabled at the IoT layers (MI-TRE ATT&CK methodology) and consequently areas of interest [18] such as industry, smart grids, transport and medical services involve the implementation of restricted requirements based on security, privacy and trust.
The cyber-physical perspective with detection and prevention systems has some paradigms in IoT systems related to perimeters. I. Stellios et al. [19] describe edge nodes as (i) edge nodes (e.g., RFIDs, sensors), (ii) edge computing (fog), and (iii) communications. Other paradigms to consider are the OT/IoT reference security architecture NIST SP 800-82r3 [20] or scenarios, such as Mirai, and DDOS cyber-attacks [21] when there are undefined parameters and constant changes, high heterogeneity, autonomous entities, inclusion of non-traditional devices, and limited permission granularity. Along these lines, the expansion of DDOS cyber-attacks is significant among hyper-connected devices as follows [17]:
-
Computers in general;
-
Network nodes;
-
Mobile devices;
-
Wearable items;
-
Video games;
-
Home automation items;
-
Storage devices;
-
Surveillance items;
-
Work devices;
-
Domestic virtual assistants;
-
Cars;
-
Media and TV items;
-
Appliances examples;
-
Other generic items.
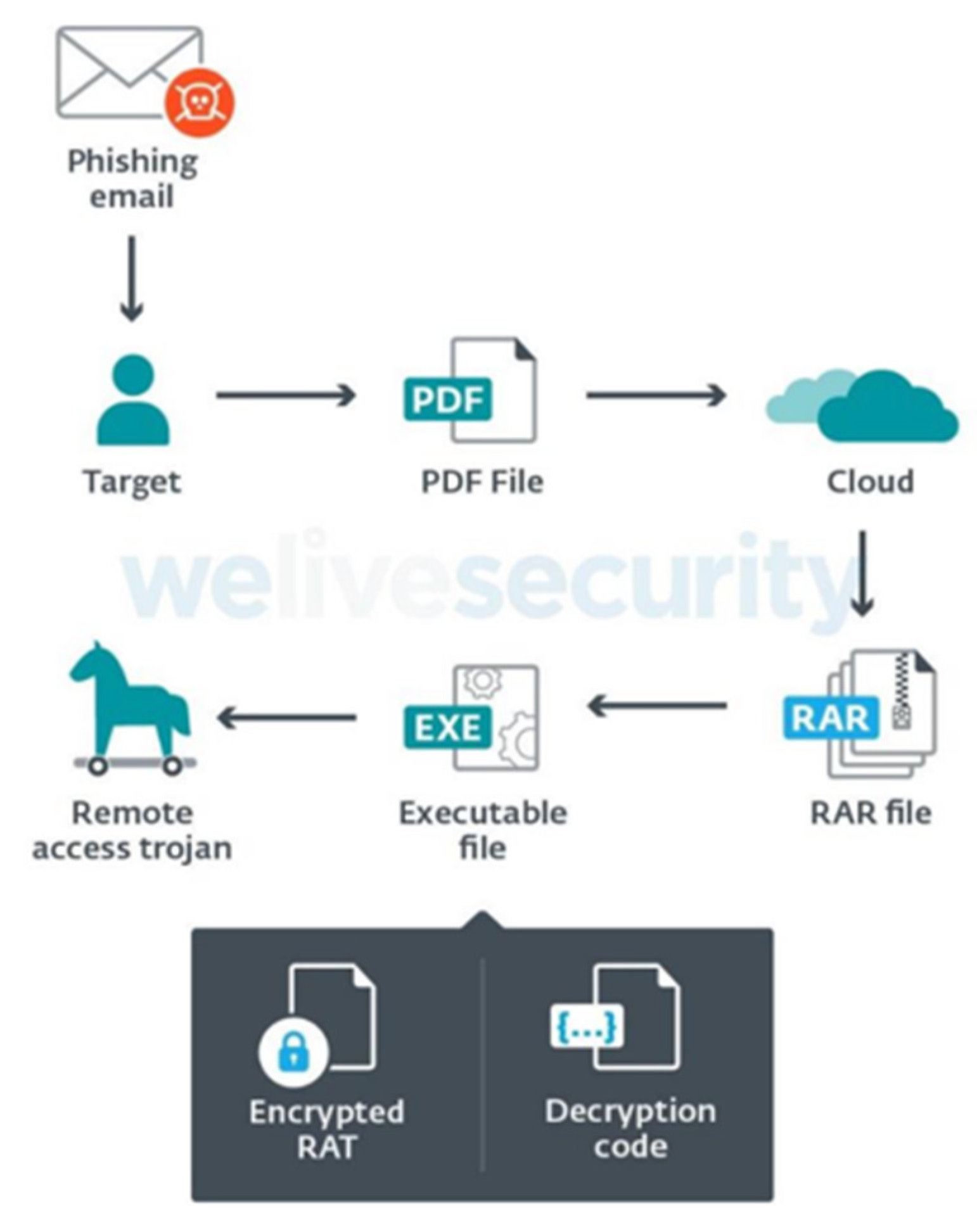
The cyberspace context change of cyberattacks detection [22] related to scenarios and taxonomy involve APT features considered in the attack cycle (see Figure 1):
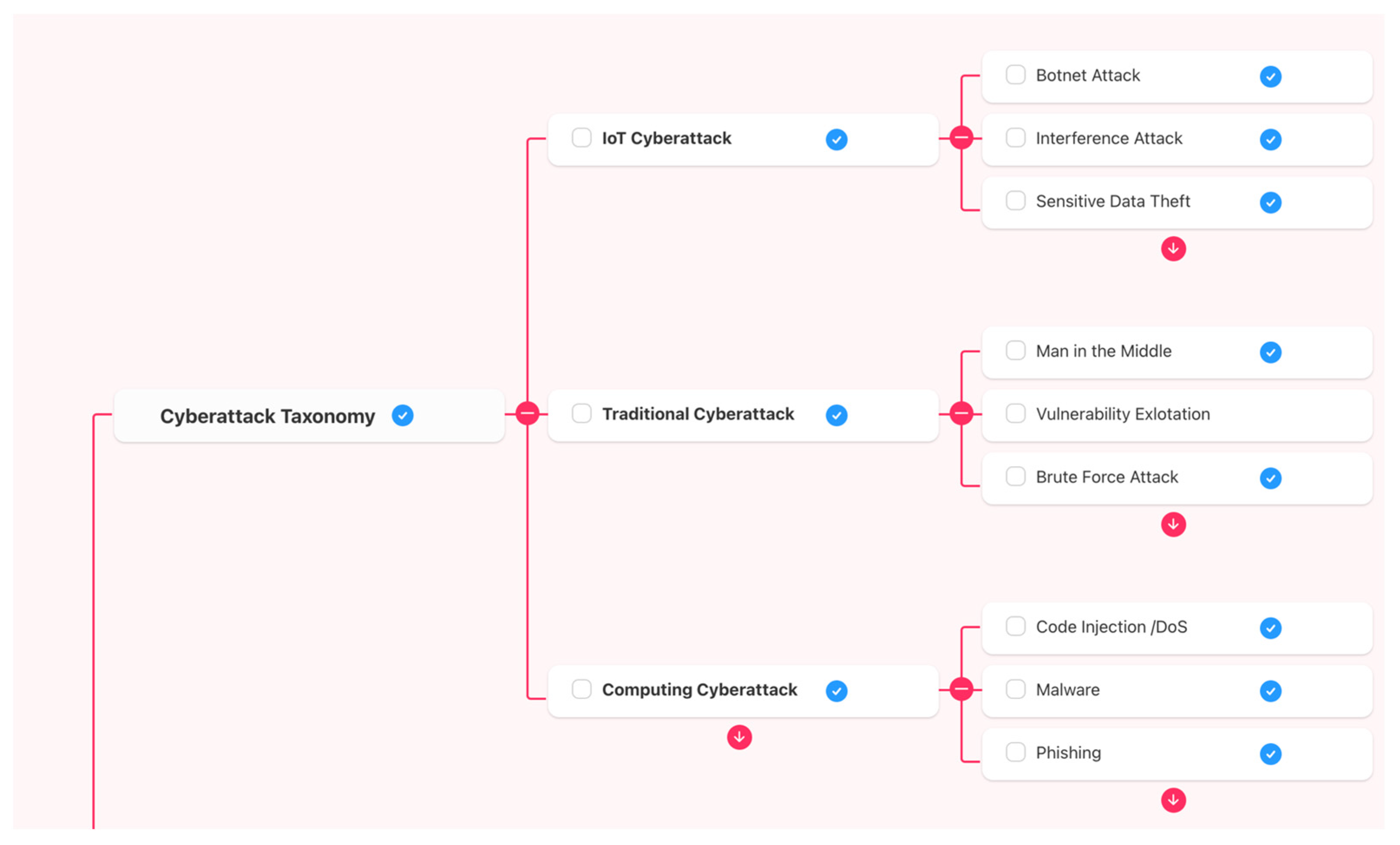
Figure 1. Cyberattack taxonomy based in [23] the APT lifecycle.
During a given campaign about advanced persistent process, Kim, Gihoom et al. [24] refer to the APT attack process related with preparation, intrusion, inside activity, and achievement. In the preparation phase, the adversary acts by analyzing and collecting the information of the victim and gaining control with the command and control server (C and C) with a malicious code. In the inside phase, the insider collects IT infrastructure information of the targeted object to achieve its final goal of the system becoming infected in the intrusion phase. In the example explained in [23], an APT using malicious software tailored to a specific target establishes a communication network and facilitates the injection of malicious code by attackers. Employing a covert approach, this specialized malware traverses laterally within the system, meticulously scanning for security vulnerabilities and leveraging them to infect additional systems within the network. The phases related to TTPs conducted over a long time in infiltration and exploitation and include (1) initial access, (2) defense, evasion, (3) credential access, (4) discovery, (5) collection, (6) and exfiltration. The taxonomy used in the APT lifecycle context [22][23] is different to common analysis and actual perspectives; according to [23], by 2025, 64 billion IoT devices will be connected to various cutting-edge environments, including smart cities, Industry 4.0, and crowdsensing. Military and governments in the world, except Latin-American, indicate [25] growth of connections to 5G, and there is a problematic focus for Colombia to advance in IoT [26] implementation of a 5G plan. In harmony with world trends, the MinICT (Ministry of Information Communications and Technology) proposes possible uses in each of the 5G spectrum areas. Frequencies below 1 GHz will preferably be used for high-speed mobile broadband in urban, suburban, and rural areas; in this context, many potentialities of IoT framed in 5G are analyzed for the advancement of the regions such as agro-industrial, manufacturing, tourism, E-health, and environment.
3. Common Systems Behavioral (CSB) Sources Used for Attack Detection
The consequence related with taxonomy use, according to [23], is that the lifecycle of APT and IoT (implementation 5G in Colombia) must contribute an Annual Cybersecurity Survey 2022–2023 [27]. Consequently, a methodology applicable and adaptable in Colombia is created to identify the root cause of approximately 157,000 daily cyberattacks [28] suffered by the country, a large percentage of which are aimed at IoT technologies, which can be implemented with the emergence and implementation of the 5G network. The consequence related to taxonomy use, according to [24], including the lifecycle of APT and description of some main factors on IoT (5G implementation in Colombia) is attributed in part to the increase of cybercrime in Colombia, according to Annual Cybersecurity Survey 2022–2023 [28], with the balance in 2021–2022 of 62% of cybercrime infractions in Colombia. The context in this order of ideas indicates that the cost could exceed USD 90 million by 2025. In [27] (page 19) the same report, it indicates that AI for early detection and anticipation of such actions is one of the major challenges in the development of innovative solutions against cyberattacks.
Indeed, Colombia has been facing an adversarial context since 2019 [29], particularly in relation to behavioral patterns associated with identified advanced persistent threats (APTs) such as APT-related Cyberattacks in Colombia:
-
(APT-C-36) [30] “Attackers coming from South America carried out continuous targeted attacks against Colombian government institutions as well as important corporations in financial sector, petroleum industry, professional manufacturing”, as per the Spalax Operation in 2021 with a RAT (remote-access Trojan) scuh as: Remcos, njRAT, AsyncRAT, and others (see Figure 2).
In relation to CSB, the common system behavioral is a set of TTPs related with APT actions on objectives [24], but in IoT–I–IoT [32] ecosystems, there are different behavioral sources (external and in-device behavior) [23]. Other methods use detection systems which are related to malicious domain names, such as extracting the readability of domain names, time to live (TTL) [33], features to establish classifiers for detection or methods [32] related to recognition of phases, e.g., reconnaissance, weaponization, delivery, exploitation, installation, com-mand and control, and action [14][32][34]. With respect to an attack modeling, a large cyberphysical system (CPS) is characterized by integration, across technologies, industrial domains, and the lifecycle, and by “smartness as IoT”. CPSs can be described using a set of characteristics: technical emphasis, cross-cutting aspects, level of automation and lifecycle integration. But in relation with common system behavioral detection, there are different components regarding comprehension for IoT systems. In Ref. [22] (page 4), the characteristics have three instances for detection: (1) IoT terminal devices are deployed, especially scattered; (2) the majority of IoT terminal devices have limited hardware resources which are unsuitable for installing large-scale attack detection software; (3) it is impossible to deploy security detection hardware directly on the resource-constrained IoT terminal devices.
In this sense, the layers for detection and prevention have has different elements (data sources of data and construct of ontology) like a comparison and structure [22], e.g.,
-
Alerts instances correlation:
- -
-
Alert instances filters.
- -
-
Alert instances clustering.
- -
-
APT attack scenario.
-
Victim–host IP
- -
-
Preliminary correlation.
- -
-
Log instances community detection.
4. Advanced Persistent Thread and Cyberattacks Detection (ML) and (CPS) Approaches
The first step for detection and identification of an APT behavior [23][35] is to connect sources by origin and destiny. Depending on the design stage, the TTP fingerprint was specifically developed and configured to detect advanced persistent threat (APT) attacks. This fingerprint leverages the correlation between the attack tree and MITRE framework, which serves as a comprehensive reference for mobile tactics and techniques associated with APT attacks. According to reference [35], the attack tree implemented in the fingerprint encompasses all relevant mobile tactics and techniques outlined by the MITRE framework. This ensures that a wide array of potential APT attack vectors can be accurately identified and mitigated through this sophisticated detection system.
Related with APT-C 36, there are components for evaluating [29][31] a CSB where detection systems can identify [22] anomalies according to [1] behavioral needs:
- -
-
Anomaly detection: [6][12]: Construct a taxonomy [19] or ontology [24] based [14] correlation (Table 1) and convert a BE (behavioral execution) in an input coordinated with a CSB detected. The inclusion analyzes the interrelationships of machine learning use in cybersecurity and CPS [12], e.g., virtual MAC spoofing detection [36].Table 1. The attributes of advanced persistent threat (APT) [22] with CSB detected and associated.
Number Attributes Description 1 Timestamp The time the alert occurs. 2 Alert_Type The type of alert. 3 Src_Ip The source IP of the attack step. 4 Dest_Ip The destination IP of the attack step. 5 Src_Port The source port number of the attack step. 6 Dest_Port The destination port number of the attack step. 7 Victim_HostIp The IP of the host victimized by the attack step. 8 APT type (associate) The CSB detected (1). Classic attack 9 TTP associate The CSB detected (2). 10 Vector associate The CSB detected (3). 11 Actor associate The CSB detected (4). 12 Purpose associate The CSB detected (5). 13 APT attribution - -
-
Misuse detection: The second dataset is the distance from the data to the nearest neighbor within the cluster or CPS (correlated). Furthermore, the approach rebuilds the data features by using the distances, and formats the data features as logistic regression, naïve Bayes, perceptron, and k-nearest neighbor (k-NN) classifier.
Expanding upon the current context of the work and correlating it with each approach to the primary anomaly detection models in real time [37], there is a compelling interest in thoroughly optimizing the study’s results, compensating for the volume of transformed data and effectively applying the methods mentioned in [38], particularly in convolutional neural networks (CNNs) with recurring features; several strategies can be employed as continuous review of these features also allows them to effectively complement real-time intrusion detection systems, thereby enhancing intrusion detection [39] accuracy and performance.
The purpose of this methodology is to conduct a systematic revision of the state of cybersecurity in Colombia [27] and evaluate the potential impact of AI in preventing future IoT cyberattacks [40]. Currently, there is a lack of technical expectation regarding the effectiveness of AI in this field [41]. By analyzing the existing literature and relevant data sources [7], this research aims to provide insights into the implementation and potential benefits of AI technologies for enhancing cybersecurity measures in Colombia. Through a structured approach to reviewing available information and identifying key findings, this research seeks to contribute to the development of strategies and practices that can effectively mitigate cyberthreats in the country.
References
- Pokhrel, S.; Abbas, R.; Aryal, B. IoT Security: Botnet detection in IoT using Machine learning. arXiv 2021, arXiv:2104.02231.
- Parra, D.T.; Talero-Sarmiento, L.H.; Ortiz, J.D.; Guerrero, C.D. Technology readiness for IoT adoption in Colombian SMEs. In Proceedings of the 2021 16th Iberian Conference on Information Systems and Technologies (CISTI), Chaves, Portugal, 23–26 June 2021; pp. 1–6.
- Seifousadati, A.; Ghasemshirazi, S.; Fathian, M. A Machine Learning Approach for DDoS Detection on IoT Devices. arXiv 2021, arXiv:2110.14911.
- Hassija, V.; Chamola, V.; Saxena, V.; Jain, D.; Goyal, P.; Sikdar, B. A Survey on IoT Security: Application Areas, Security Threats, and Solution Architectures. IEEE Access 2019, 7, 82721–82743.
- Jain, V.K.; Gajrani, J. IoT Security: A Survey of Issues, Attacks and Defences. In Proceedings of the Intelligent Learning for Computer Vision: Proceedings of Congress on Intelligent Systems, New Delhi, India, 5–6 September 2020; pp. 219–236.
- Xiao, L.; Wan, X.; Lu, X.; Zhang, Y.; Wu, D. IoT Security Techniques Based on Machine Learning: How do IoT devices use AI to enhance security? IEEE Signal Process. Mag. 2018, 35, 41–49.
- Dodda, R.; Gaddam, V.; Prasad, J.R.; Rao, B.V. The Evolution of Internet Of Things (IOT) And Its Impact on Existing Technology. Int. J. Sci. Technol. Eng. 2016, 2, 96–103.
- Pennino, D.; Pizzonia, M.; Vitaletti, A.; Zecchini, M. Blockchain as IoT Economy Enabler: A Review of Architectural Aspects. J. Sens. Actuator Netw. 2022, 11, 20.
- An, Y.; Yu, F.R.; Li, J.; Chen, J.; Leung, V.C. Edge Intelligence (EI)-Enabled HTTP Anomaly Detection Framework for the Internet of Things (IoT). IEEE Internet Things J. 2020, 8, 3554–3566.
- Chatterjee, A.; Ahmed, B.S. IoT Anomaly Detection Methods and Applications: A Survey. Internet Things 2022, 19, 100568.
- Liang, F.; Hatcher, W.G.; Liao, W.; Gao, W.; Yu, W. Machine Learning for Security and the Internet of Things: The Good, the Bad, and the Ugly. IEEE Access 2019, 7, 158126–158147.
- Bharati, S.; Podder, P. Machine and Deep Learning for IoT Security and Privacy: Applications, Challenges, and Future Directions. arXiv 2022, arXiv:2210.13547.
- Rashid, M.M.; Kamruzzaman, J.; Imam, T.; Kaisar, S.; Alam, M.J. Cyber Attacks Detection from Smart City Applications Using Artificial Neural Network. In Proceedings of the Asia-Pacific Conference on Computer Science and Data Engineering (CSDE), Gold Coast, Australia, 16–18 December 2020; pp. 1–6.
- Kharchenko, V.; Sklyar, V. ENISA Documents in Cybersecurity Assurance for Industry 4.0: IIoT Threats and Attacks Scenarios. In Proceedings of the 2019 10th IEEE International Conference on Intelligent Data Acquisition and Advanced Computing Systems, Metz, France, 18–21 September 2019; Volume 2, pp. 1046–1049.
- Tsakalidis, G.; Vergidis, K.; Madas, M. Decision and Information Technologies (CoDIT)—Cybercrime Offences: Identification, Classification and Adaptive Response. In Proceedings of the 2018 5th International Conference on Control, Decision and Information Technologies (CoDIT), Thessaloniki, Greece, 10–13 April 2018; pp. 470–475.
- da Rocha, B.C.; de Melo, L.P.; de Sousa, R.T., Jr. A Study on APT in IoT Networks. In Proceedings of the 18th International Conference on e-Business (ICE-B 2021), Nanjing, China, 3–7 December 2021.
- Stellios, I.; Kotzanikolaou, P.; Psarakis, M.; Alcaraz, C.; López, J. A Survey of IoT-Enabled Cyberattacks: Assessing Attack Paths to Critical Infrastructures and Services. IEEE Commun. Surv. Tutor. 2018, 20, 3453–3495.
- NIST. Guide to Operational Technology (OT) Security; NIST: Gaithersburg, MD, USA, 2023.
- Available online: https://nvlpubs.nist.gov/nistpubs/SpecialPublications/NIST.SP.800-82r3.pdf (accessed on 1 January 2024).
- Bertino, E.; Islam, N. Botnets and Internet of Things Security. Computer 2017, 50, 76–79.
- Cheng, X.; Zhang, J.; Chen, B. Cyber Situation Comprehension for IoT Systems Based on APT Alerts and Logs Correlation. Sensors 2019, 19, 4045.
- Singh, T.; Jabar, M.M. Exploration of Mobile Device Behavior for Mitigating Advanced Persistent Threats (APT): A Systematic Literature Review and Conceptual Framework. Sensors 2022, 22, 4662.
- Kim, G.; Choi, C.; Choi, J. Ontology modeling for APT attack detection in an IoT-based power system. In Proceedings of the 2018 Conference on Research in Adaptive and Convergent Systems—RACS ’18, Adaptive and Convergent Systems (RACS), Honolulu, HI, USA, 9–12 October 2018; pp. 160–164.
- OMDIA. 01 de Diciembre de 2023. 5G Forecast 2023–2028. 2023. Available online: https://www.5gamericas.org/resources/charts-statistics/latin-america/ (accessed on 1 January 2024).
- Barrios, A.; Cama, D.; Mardini, J.; Díaz, J. Projections of IoT Applications in Colombia Using 5G Wireless Networks. Sensors 2021, 21, 7167.
- (TicTac), ICT Analysis and Creativity Tank. AI for Protection and Threat Prevention. 2023. Available online: https://www.ccit.org.co/estudios/estudio-anual-de-ciberseguridad-2022-2023/ (accessed on 1 January 2024).
- Kaspersky, «Impacto TIC» 25 01 2024. . Available online: https://impactotic.co/tecnologia/157-000-ciberataques-diarios-en-colombia-en-el-2023/ (accessed on 30 January 2024).
- QiAnXin Threat Intelligence Center 2023. Available online: https://ti.qianxin.com/blog/articles/apt-c-36-continuous-attacks-targeting-colombian-government-institutions-and-corporations-en/ (accessed on 1 January 2024).
- Malpedia. 2023. Available online: https://malpedia.caad.fkie.fraunhofer.de/actor/apt-c-36 (accessed on 1 January 2024).
- ESET WeliveSecurity. 2021. Available online: https://www.welivesecurity.com (accessed on 1 January 2024).
- Available online: https://www.welivesecurity.com/2021/01/12/operation-spalax-targeted-malware-attacks-colombia/ (accessed on 1 January 2024).
- Javed, S.H.; Ahmad, M.B.; Asif, M.; Almotiri, S.H.; Masood, K.; Ghamdi, M.A.A. An Intelligent System to Detect Advanced Persistent Threats in Industrial Internet of Things (I-IoT). Electronics 2022, 11, 742.
- Ma, Z.; Li, Q.; Meng, X. Discovering Suspicious APT Families Through a Large-Scale Domain Graph in Information-Centric IoT. IEEE Access 2019, 7, 13917–13926.
- Kolias, C.; Kambourakis, G.; Stavrou, A.; Voas, J.M. DDoS in the IoT: Mirai and Other Botnets. Computer 2017, 50, 80–84.
- Al-Kadhimi, A.A.; Singh, M.M.; Jabar, T. Fingerprint for Mobile-Sensor APT Detection Framework (FORMAP) Based on Tactics Techniques and Procedures (TTP) and Mitre. In Proceedings of the 8th International Conference on Computational Science and Technology: ICCST 2021, Labuan, Malaysia, 28–29 August 2022; Springer: Singapore, 2022; pp. 515–533.
- Jiang, P.; Wu, H.; Wang, C. Virtual MAC Spoofing Detection Through Deep Learning. In Proceedings of the 2018 IEEE International Conference on Communications (ICC), Kansas City, MO, USA, 20–24 May 2018; pp. 1–6.
- Pelletier, C.; Webb, G.I.; Petitjean, F. Deep learning for the classification of Sentinel-2 image time series. In Proceedings of the IGARSS 2019-2019 IEEE International Geoscience and Remote Sensing Symposium, Yokohama, Japan, 28 July–2 August 2019.
- Dong, S.; Xia, Y.; Peng, T. Network abnormal traffic detection model based on semi-supervised deep reinforcement learning. IEEE Trans. Netw. Serv. Manag. 2021, 18, 4197–4212.
- Di Mauro, M.; Galatro, G.; Liotta, A. Experimental review of neural-based approaches for network intrusion management. IEEE Trans. Netw. Serv. Manag. 2020, 17, 2480–2495.
- Ahanger, T.A. Defense Scheme to Protect IoT from Cyber Attacks Using AI Principles. Int. J. Comput. Commun. Control 2018, 13, 915–926.
- Kuzlu, M.; Fair, C.; Guler, O. Role of Artificial Intelligence in the Internet of Things (IoT) Cybersecurity. Discov. Internet Things 2021, 1, 7.
More
Information
Subjects:
Computer Science, Cybernetics
Contributors
MDPI registered users' name will be linked to their SciProfiles pages. To register with us, please refer to https://encyclopedia.pub/register
:
View Times:
903
Revisions:
3 times
(View History)
Update Date:
08 Mar 2024
Notice
You are not a member of the advisory board for this topic. If you want to update advisory board member profile, please contact office@encyclopedia.pub.
OK
Confirm
Only members of the Encyclopedia advisory board for this topic are allowed to note entries. Would you like to become an advisory board member of the Encyclopedia?
Yes
No
${ textCharacter }/${ maxCharacter }
Submit
Cancel
Back
Comments
${ item }
|
More
No more~
There is no comment~
${ textCharacter }/${ maxCharacter }
Submit
Cancel
${ selectedItem.replyTextCharacter }/${ selectedItem.replyMaxCharacter }
Submit
Cancel
Confirm
Are you sure to Delete?
Yes
No