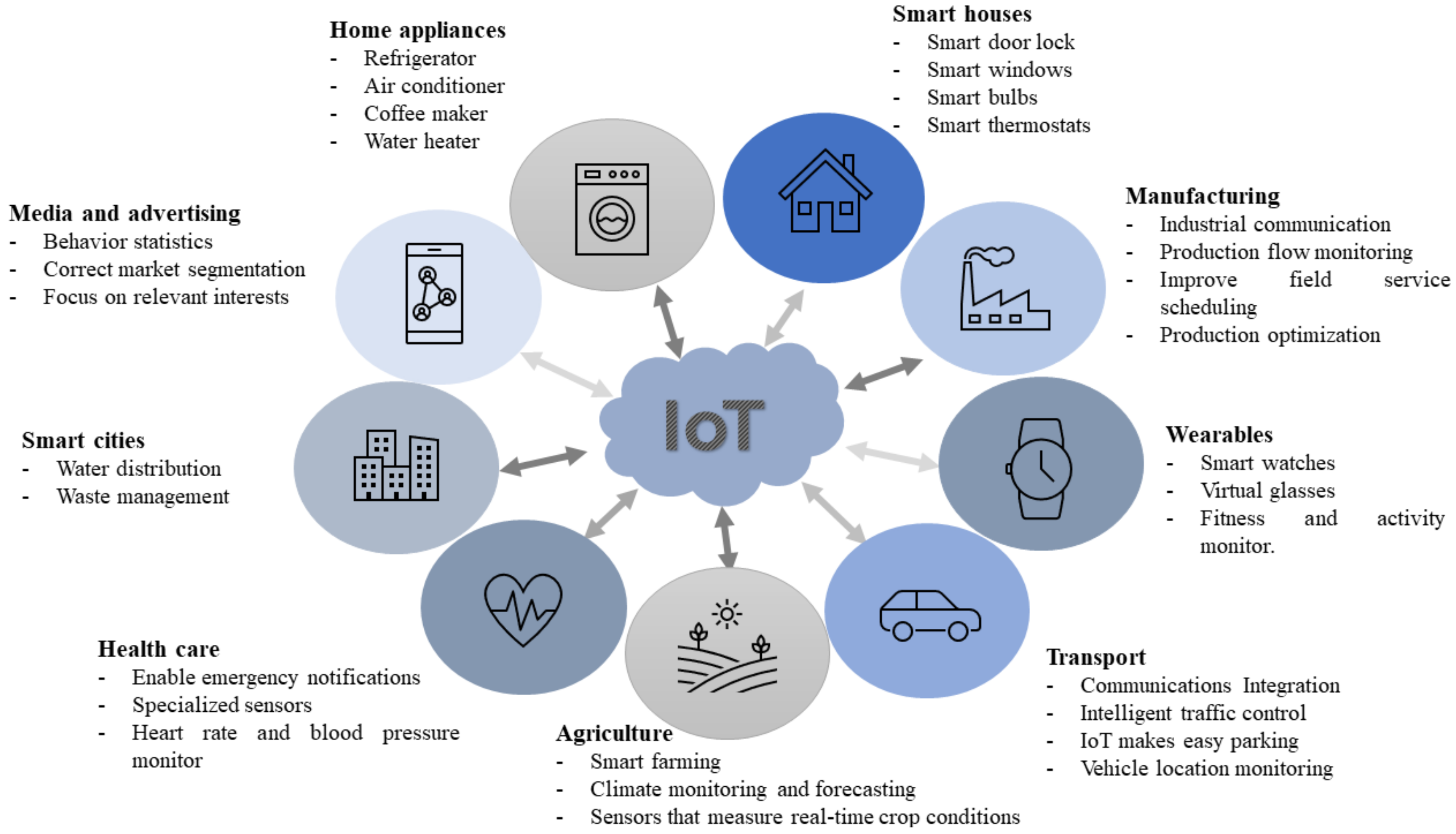
IoT reaches different scopes; they can be medicine, education, industry, entertainment, sports, clothes, smart cities, agriculture, and many others. See Figure 1. Technology recollects a big amount of data, including personal information, routines, and health records, to simplify the diverse tasks that we accomplish daily. However, having that great collection of records could be counterproductive, if someone else uses it to gain something. This opens the door for cybercriminals, who understand the value of these types of sensitive data.
2. IoT Vulnerabilities and Challenges
The literature shows multiple concerns already found in different IoT devices
[5]. Now, to understand how big these concerns are, vulnerabilities must be covered due to the increasing use of this kind of technology and the sensitive information they gather. A key is to maintain confidentiality, integrity, and availability, also known as the CIA triad; this represents a fundamental concept in cybersecurity. There has been a lot of research, and the most common types of attacks that have been made on IoT devices can be seen in the systematic review in
Table 1.
Table 1. Systematic Review: IoT Attacks.
The large number of attacks that exist on IoT devices gives us an idea of the importance of establishing security countermeasures against these threats
[8]. The consequences that they can have on a person’s lifestyle and health could be devastating. Devices’ sensitive data could be at risk with a technique in which data is being sent through devices and because they have poor authentication methods for devices that handle such an important type of data, raising question marks about confidentiality.
Other types of attacks have the objective of changing data information, making the users’ data that was recollected hard to trust. This way, it damages the integrity part of the IoT device. Several IoT devices are now used for medical purposes, recollecting real-time information. If they are not available at every moment of the day, not only are they not fulfilling their purpose, but they could be putting a user’s life in danger by not registering, what might be, for some users, life and death cases.
As can be seen, the biggest fundamentals in cybersecurity have been exposed by these types of technologies. Correcting these problems would be the following step to take to guarantee confidentiality, integrity, and availability. However, numerous other issues appear when trying to apply new forms of security to IoT devices, as shown in Table 2.
Table 2. Systematic Review: Security Challenges.
Smartwatches: Bluetooth Communication Attacks
Bluetooth is everywhere: in speakers, headphones, refrigerators, cars, wearables, medical devices, and more. IoT is about small devices and multiple sensors. Bluetooth is a suitable technology that provides IoT features that can be applied to a wide range of potential IoT applications. Manufacturers need to understand how to implement secure architectures to protect users’ sensitive information while considering the challenges and limitations of the IoT.
However, Bluetooth communication has been the target of multiple types of attacks for years as cybercriminals exploit the vulnerabilities this technology has had in earlier versions. These communication protocols have been updated to protect devices against eavesdropping and man-in-the-middle attacks.
The literature shows multiple researchers finding weaknesses in wearable devices
[13][14][15][16]. They talk about different attacks on several IoT devices that communicate via Bluetooth, as well as they give countermeasures and recommendations to users for safer use of this technology. Furthermore, other research includes studies that found vulnerabilities in some devices
[17]. One of them is an attack on a smartwatch, where the PIN that secures its communication with a smartphone was exploited while performing a brute-force attack. In the pairing process, this smartwatch had one of the least secure mechanisms, which shows that smartwatches are prone to attacks
[18]. With respect to threats, one article divides them into two categories: passive adversary and active adversary, where the first, the attacker eavedrops on the connection and tries to find LTK or other information, but he can not manipulate the message, and in the second, the attacker can inject, modify, and block the message transmitted, enabling the ability to create his own messages and send them to the victim’s device
[19].
Other research focuses on wearable devices, such as a Fitbit smartwatch, and how they can be targets of man-in-the-middle attacks. The attack consists of using two fake devices, one that disguises itself as a smart device and another one as a mobile app that connects to the Fitbit device; it also adds that Fitbit collects a lot of sensitive data, and it proposes to educate the users to be aware of what happens when doing an incorrect use of the device
[20]. Another research project highlights a couple of vulnerabilities in some wearable devices, such as the smartwatch Fitbit Inspire, which has a serious threat known as the Link Layer Length Overflow. It means that an attacker acting as a central device can make the peripheral devices suffer instabilities until they finally crash
[21].
More studies have concluded that it is important to teach users about the correct use of this technology because most of the recommendations always go to the manufacturers. They propose some guidelines to instruct about wearable devices
[22] and state the need for standards in the wearable industry
[20].
Another piece of research worries about the data these devices obtain; for example, the users’ location, which exposes them to different types of attacks. Furthermore, it proposes the constant change of the MAC address to avoid any type of targeting
[23]. A group of researchers also mentions the vulnerabilities of the MAC address in Fitbit devices, as they recollect the MAC addresses of nearby Fitbit devices, and while Fitbit offers a reasonable level of security, they also gather extraneous data about users
[24].
In one paper, they make passive attacks on wearable devices using Bluetooth sniffers and HCI snoop logs and capture an encryption key in plain text
[25]. While another article shows the use of Bluetooth and describes an attack where it forces a key renegotiation using eavesdropping techniques
[26]. Other works show the potential risks the devices are exposed to when manufacturers do not follow the recommendations of the Bluetooth Special Interest Group, as it happens more often than it should
[27][28]. While various research projects include tests on different devices, the literature does not show a way to compare the security levels of these devices. There is no existence of measurement to identify when an IoT device is secure or what characteristics can be considered to categorize if an IoT device is safe or not.
3. Background: Bluetooth Technologies and Evolution
Bluetooth is used for short-range radio-frequency communication. As mentioned before, vulnerabilities can be found in IoT devices, and this could be discovered through the Bluetooth protocol. The most common attacks are man-in-the-middle (MITM), where an attacker can obtain the keys that are exchanged between devices and, once obtained, eavesdrop on communications
[29].
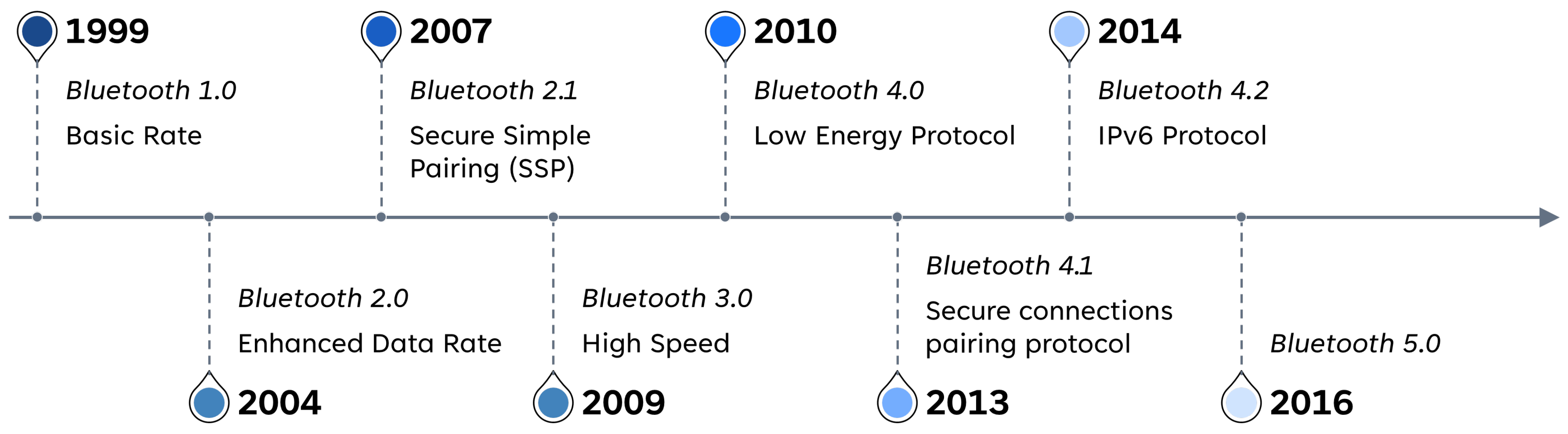
The earliest days of Bluetooth introduced Bluetooth Basic Rate (BR), Enhanced Data Rate (EDR), and High Speed (HS) models. Bluetooth 1.1 and 1.2 versions could only work with BR because they are only capable of supporting up to 1 megabit per second (Mbps). EDR improves in Bluetooth version 2.0, where it gets data rates up to 3.0 Mbps. HS arrives during Bluetooth 3.0, supporting faster data rates up to 24 Mbps. However, devices that support higher data rates are also able to support lower data rates from earlier Bluetooth specifications. When referring to these versions of Bluetooth, they are commonly known as Bluetooth Classic. See Figure 2.
Figure 2. Bluetooth Technologies and Evolution.
Bluetooth Low-Energy (BLE) was established in the Bluetooth 4.0 specification; later, an update was made in versions 4.1 and 4.2. It is useful for wearable medical devices and sensors because it was primarily made for devices that use a coin-cell battery. It reduces power consumption and memory requirements. Basically, it is designed to operate in sleep mode and wake up only when the connection is initiated. This improves efficiency when discovering devices and during connection procedures and results in packets with shorter lengths, while services and protocols are simpler.
Since Bluetooth 4.0 devices can support both Bluetooth Classic and BLE, this is known as the dual mode. Cellphones work as a perfect example, where they might use Bluetooth Classic when connected to earphones and have the necessity to have constant data streaming while also using BLE when connected to a smart wristband that tracks your activity while doing exercises, and you only need the data exchange when you synchronize your devices to check your results.
Bluetooth has five basic security services:
- (a)
-
Authentication, using the Bluetooth address to verify the identity of each device during the communication stage.
- (b)
-
Confidentiality, guaranteeing that only authorized devices have access to data, avoiding any type of eavesdropping.
- (c)
-
Authorization, verifying that a device is authorized to use the service before allowing it to do it, guaranteeing that only this device can use the service and no other device can.
- (d)
-
Message integrity, when information is exchanged between two Bluetooth devices, it has to be secure and nothing can be modified.
- (e)
-
Pairing/bonding, the generated keys are shared and stored for future use, to create trust between two Bluetooth devices.
3.1. Bluetooth Classic
Bluetooth includes four security modes; mode 1 has no security, mode 2 has authentication and encryption in the controller, and mode 3 has it in the physical link. These three modes only existed in the prior Bluetooth 2.1 version.
Security Mode 4 is a service-level enforced security mode; it uses secure simple pairing (SSP) and it uses Elliptic-curve Diffie–Hellman (ECDH) key agreement for link key generation. This helps protect against eavesdropping and man-in-the-middle attacks. The ECDH that is used could be the elliptic curve 192 or 256. For authentication and encryption, a secret symmetric key is necessary, and it is known as the link key. Security mode 4 includes five security levels. Starting from security level 0 and ending at security level 4: (i) Level 0 has no security and is only allowed for service discovery protocols; (ii) Level 1, also does not require security; (iii) Level 2 requires an unauthenticated link key; (iv) Level 3 requires an authenticated link key, and; (v) Level 4 requires authenticating the link key using secure connections. The secure connections pairing protocol was introduced in Bluetooth 4.1 and it uses the ECDH 256, improving from the ECDH 192 that was used prior.
3.2. Bluetooth Low Energy
This section meticulously explains BLE, to understand how it is possible to protect against the most common attacks on this technology.
Bluetooth 4.0, 4.1, and 4.2 count cryptographic keys to improve security in the devices, these keys are named Identity Resolving Key (IRK), to support low-energy private device addresses, and Connections Signature Resolving Key (CSRK), to assist data signing. When pairing BLE devices, a Long-Term Key (LTK) is generated, which is important for authentication and encryption (known as the link key in Bluetooth Classic). This could result in two different methods. During the first method, one device generates the LTK and sends it to the other device in a secure manner; this is known as low-energy Legacy Pairing. Furthermore, it is important to notice that for this method, all the keys are distributed in a secure process during the pairing stage. In the second method, both devices create the key without the need to share it through the link. This method is called low-energy Secure Connections. Meanwhile, the LTK is generated, while the IRK and the CSRK are created and distributed securely. An important difference between these methods is that low-energy Legacy Pairing does not include Elliptic-curve Diffie–Hellman (ECDH) encryption, which makes it vulnerable to eavesdropping attacks and allows attackers to potentially find the LTK. In contrast, Low-energy Secure Connections can countermeasure this threat.
Low-energy Security includes two modes. Security Mode 1 has four levels related to encryption. Level 1 does not require encryption and authentication. Level 2 asks for unauthenticated pairing with encryption. Level 3 needs authenticated pairing with encryption. Level 4 uses the Secure Connections method previously discussed in this section, as it asks for an authenticated link key using low-energy Secure Connections pairing with encryption. Security Mode 2 requires data signing in both of its levels, with the sole difference that level 1 only needs unauthenticated pairing while level 2 asks for authenticated pairing. Because encryption is a great security asset, using Security Mode 1 Level 3 or 4 is strongly recommended over other options.
3.3. Bluetooth: Pairing Methods
In this section, the researchers give a more detailed explanation of the low-energy pairing methods and describe the phases that occurred during the pairing methods. Starting with low-energy Legacy Pairing. Phases:
- (i)
-
Phase 1, once explore the input/output capabilities and security requirements in the devices, they will establish an agreement on a Temporary Key (TK).
- (ii)
-
Phase 2, they proceed to create a Short Term Key (STK) using random values that are being exchanged and the TK. This STK establishes an encrypted link between devices.
- (iii)
-
Phase 3, it assures a safe key transport for all the keys mentioned earlier in this article (LTK, IRK, CSRK).
Low-energy Secure Connections work in a different manner. Even though phase 1 works the same way as legacy pairing, in phase 2, the LTK is generated without the need for the STK. This LTK is useful in phase 3, and the LTK encrypts the links, and a key agreement is made to distribute the IRK and CSRK securely instead of using a key transport.
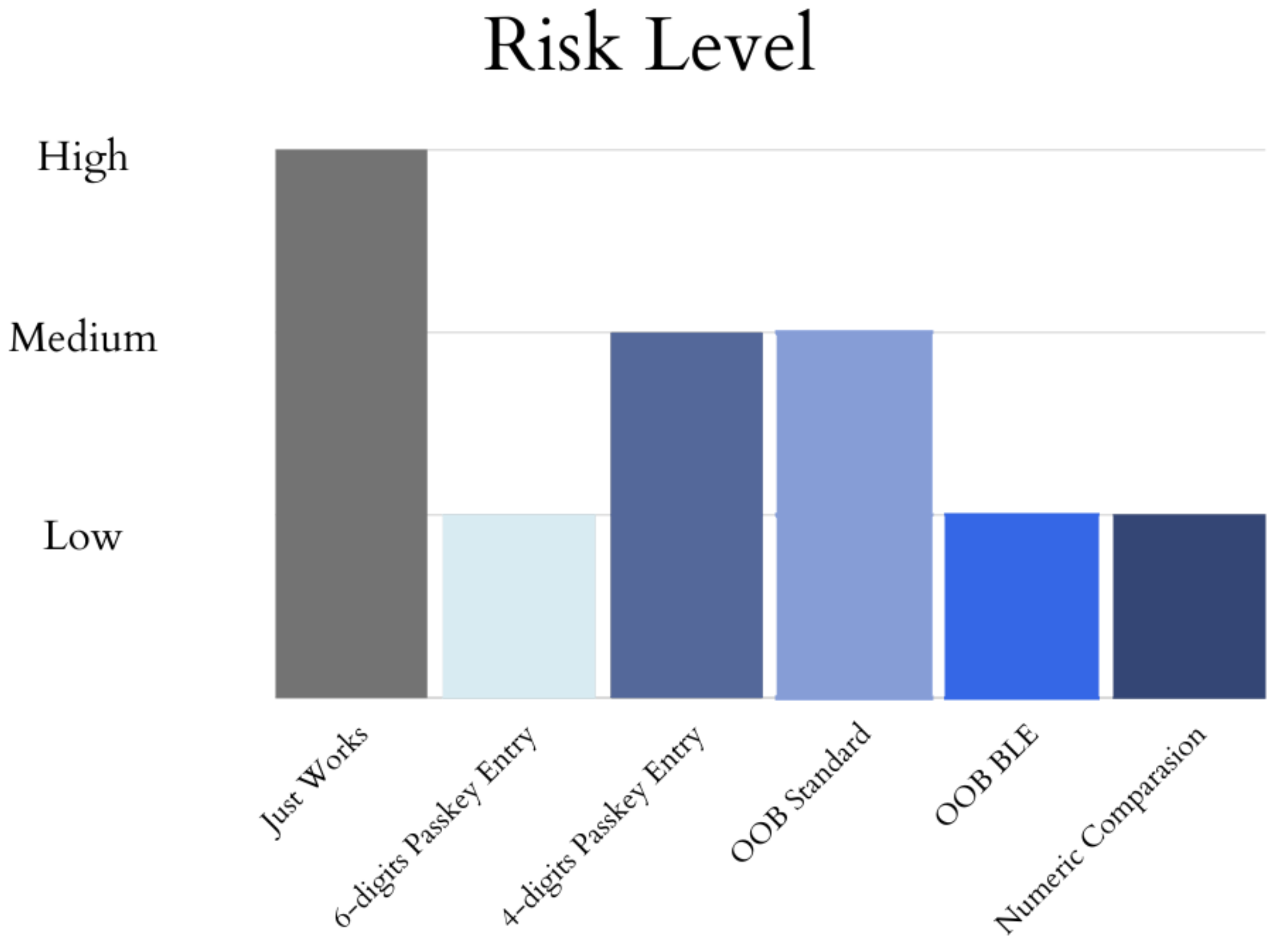
During the pairing process between two devices, one of four different pairing processes can be applied. These pairing processes are: (a) Out of Band for Bluetooth Standard or BLE; (b) Numeric Comparison; (c) Passkey Entry 4 or 6 digits; and (d) Just Works. The input/output capabilities of devices play an important role in determining what processes can be utilized.
The out-of-band (OOB) process requires two devices that have OOB technology, such as near-field communication (NFC). One device sends the other a 128-bit number, which is the TK, using OOB technology. Using low-energy Legacy Pairing provides one-in-a-million protection against MITM attacks to guess the TK. However, this protection comes from the OOB technology that the device uses, because if someone is capable of eavesdropping on the OOB, they will obtain the TK values. For low-energy Secure Connections, the device address is sent through the OOB. Even if an eavesdropper can obtain it, this does not give them any value in decrypting the data.
Numeric comparison is an option available only for low-energy Secure Connections. This method is not available for low-energy Legacy Pairing. The process involves two devices displaying a 6-digit number on their respective screens, and the user enters one of two options: (i) YES, if both displays show the same 6-digit number; (ii) NO, if the numbers are different. The previous 6-digit number is not used to generate the link key to avoid eavesdropping. Even if an unauthorized person captures this 6-digit number, it will not be useful for any further pairing process. Additionally, it has protection against MITM attacks, as the user must confirm if the 6-digit number is or is not the same on both devices before proceeding. This guarantees that no other device can initiate the pairing process.
Another method is passkey entry, which requires that both devices have a keyboard input or at least one of them has a display output. This method works with low-energy Legacy Pairing. A passkey is given on one device and entered on the other, and then a TK is generated using the passkey. The passkey is required to have six numeric digits, which would give an entropy of twenty bits that ensures the complexity of deciphering the given key. Low-energy Secure Connections pairing works differently. After the devices exchange public keys, the six numeric digits passkey is generated, and once it is entered into the device, it starts sending a hash of each bit of the passkey. This procedure is repeated twenty times to complete the twenty bits of the passkey. Furthermore, the public keys were sent during the previous step. This method offers protection against MITM attacks. When using a passkey of six digits, it gives an attacker a one-in-a-million chance to guess the correct passkey.
The last method is the least secure one, and it is used due to the limitations in the input/output capabilities of the devices. For low-energy Legacy Pairing the key is always the same and is set to all zeros, leaving the pairing exposed to eavesdropping and MITM attacks. In the low-energy Secure Connections method, the pairing process follows the same steps as in the numeric comparison process, but the user is unable to see the 6-digit number. This is because the devices involved in this procedure cannot display the number, which in turn makes it impossible to perform the final commitment checks.
These four pairing methods are not exclusive to Bluetooth Low-Energy; they can also be found in Bluetooth Classic, working slightly differently due to the IRK and CSRK being exclusive to BLE. Only the LTK is set to be created, but it is known as the link key. The association models (out of band, numeric comparison, and passkey entry) provide authenticated link keys; meanwhile, the link key is unauthenticated during the Just Works pairing model for Bluetooth Classic. The risk of an attack is determined by the version of Bluetooth and the pairing method used. See Figure 3.
Figure 3. Risk Level on Pairing Methods.