
| Version | Summary | Created by | Modification | Content Size | Created at | Operation |
|---|---|---|---|---|---|---|
| 1 | Zeinab Teimoori | -- | 3463 | 2022-11-18 22:56:15 | | | |
| 2 | Jason Zhu | Meta information modification | 3463 | 2022-11-21 02:50:16 | | |
Video Upload Options
Electric Vehicles (EVs) have been gaining interest as a result of their ability to reduce vehicle emissions. Developing an intelligent system to manage EVs charging demands is one of the fundamental aspects of this technology to better adapt for all-purpose transportation utilization. It is necessary for EVs to be connected to the Smart Grid (SG) to communicate with charging stations and other energy resources in order to control charging schedules, while Artificial Intelligent (AI) techniques can be beneficial for improving the system, they can also raise security and privacy threats. Privacy preservation methodologies have been introduced to ensure data security. Federated Learning (FL) and blockchain technology are two emerging strategies to address information protection concerns.
1. Charging Stations Distribution
2. Charging Scheduling and Charging Station Selection
2.1. Personal Electric Vehicles
2.2. Electric Taxis
2.3. Electric Buses
3. Electric Vehicles Data Security
3.1. Federated Learning
3.2. Blockchain
-
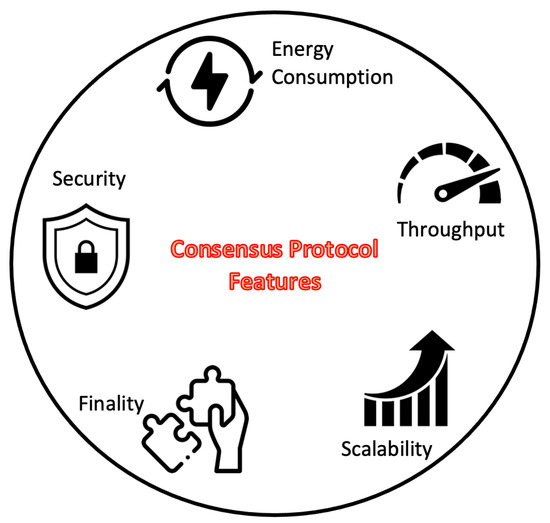
Scalability: Denotes to the capability of a consensus protocol to sustain the overall performance with the addition of nodes, transactions, and data [66].
-
Energy Consumption: This metric is the key issue of blockchain limited widespread applicability. As an example, PoW consensus protocol has high energy consumption as the block miner selection requires massive computational power [67].
-
Security: Indicates a consensus protocol resistance to various attacks. For instance, PoW-based models can crash by two major attacks, namely Denial of Service (DoS) and Sybil [70], therefore such a system should present feasible solutions to prevent malicious intrusion.
-
Finality: Defines the determinism of the blockchain by ensuring that blocks cannot be reversed or changed purposefully once they are added to the chain [71].
4. Electric Vehicles Energy Trading
References
- Al-Hanahi, B.; Ahmad, I.; Habibi, D.; Masoum, M.A. Charging infrastructure for commercial electric vehicles: Challenges and future works. IEEE Access 2021, 9, 121476–121492.
- Ma, T.Y.; Xie, S. Optimal fast charging station locations for electric ridesharing with vehicle-charging station assignment. Transp. Res. Part Transp. Environ. 2021, 90, 102682.
- Huang, Y.; Kockelman, K.M. Electric vehicle charging station locations: Elastic demand, station congestion, and network equilibrium. Transp. Res. Part Transp. Environ. 2020, 78, 102179.
- Pevec, D.; Babic, J.; Carvalho, A.; Ghiassi-Farrokhfal, Y.; Ketter, W.; Podobnik, V. Electric Vehicle Range Anxiety: An Obstacle for the Personal Transportation (R)evolution? In Proceedings of the 4th International Conference on Smart and Sustainable Technologies (SpliTech), Split, Croatia, 18–21 June 2019; pp. 1–8.
- Kavianipour, M.; Fakhrmoosavi, F.; Singh, H.; Ghamami, M.; Zockaie, A.; Ouyang, Y.; Jackson, R. Electric vehicle fast charging infrastructure planning in urban networks considering daily travel and charging behavior. Transp. Res. Part Transp. Environ. 2021, 93, 102769.
- Guler, D.; Yomralioglu, T. Suitable location selection for the electric vehicle fast charging station with AHP and fuzzy AHP methods using GIS. Ann. GIS 2020, 26, 169–189.
- Yassine, A.; Hossain, M.S. COVID-19 Networking Demand: An Auction-Based Mechanism for Automated Selection of Edge Computing Services. IEEE Trans. Netw. Sci. Eng. 2022, 9, 308–318.
- Chen, Y.; Qin, Z.; Gan, X. Optimal EV Charging Network Design: When Users Have Choices. In Proceedings of the 11th International Conference on Wireless Communications and Signal Processing (WCSP), Xi’an, China, 23–25 October 2019; pp. 1–6.
- Vaidya, B.; Mouftah, H.T. Smart electric vehicle charging management for smart cities. IET Smart Cities 2020, 2, 4–13.
- Huang, D.; Chen, Y.; Pan, X. Optimal model of locating charging stations with massive urban trajectories. IOP Conf. Ser. Mater. Sci. Eng. 2020, 715, 012009.
- Liu, G.; Kang, L.; Luan, Z.; Qiu, J.; Zheng, F. Charging Station and Power Network Planning for Integrated Electric Vehicles (EVs). Energies 2019, 12, 2595.
- Ramachandran, A.; Balakrishna, A.; Kundzicz, P.; Neti, A. Predicting electric vehicle charging station usage: Using machine learning to estimate individual station statistics from physical configurations of charging station networks. arXiv 2018, arXiv:1804.00714.
- Zeb, M.Z.; Imran, K.; Khattak, A.; Janjua, A.K.; Pal, A.; Nadeem, M.; Zhang, J.; Khan, S. Optimal Placement of Electric Vehicle Charging Stations in the Active Distribution Network. IEEE Access 2020, 8, 68124–68134.
- Cui, S.; Zhao, H.; Wen, H.; Zhang, C. Locating Multiple Size and Multiple Type of Charging Station for Battery Electricity Vehicles. Sustainability 2018, 10, 3267.
- Deb, S.; Gao, X.Z.; Tammi, K.; Kalita, K.; Mahanta, P. A novel chicken swarm and teaching learning based algorithm for electric vehicle charging station placement problem. Energy 2021, 220, 229645.
- Zhang, J.; Li, T.; Pan, A.; Long, X.; Jiang, L.; Liu, Z.; Zhang, Y. Charging Time and Location Recommendation Strategy Considering Taxi User Satisfaction. In Proceedings of the Asia Energy and Electrical Engineering Symposium (AEEES), Chengdu, China, 28–31 May 2020; pp. 257–264.
- Guo, Z.; Ou, D.; Xie, W.; Tan, Z. Analysis and Optimization to the Final Network of Charging Stations. In Proceedings of the IEEE 3rd Optoelectronics Global Conference (OGC), Shenzhen, China, 4–7 September 2018; pp. 209–213.
- Dong, G.; Ma, J.; Wei, R.; Haycox, J. Electric vehicle charging point placement optimisation by exploiting spatial statistics and maximal coverage location models. Transp. Res. Part Transp. Environ. 2019, 67, 77–88.
- Cui, Q.; Weng, Y.; Tan, C.W. Electric Vehicle Charging Station Placement Method for Urban Areas. IEEE Trans. Smart Grid 2019, 10, 6552–6565.
- Tayyab, M.; Helm, S.; Hauer, I.; Brinken, J.; Schmidtke, N. Infrastructure linking for placement of Charging stations using Monte Carlo simulation. In Proceedings of the 6th IEEE Congress on Information Science and Technology (CiSt), Agadir, Morocco, 5–12 June 2020; pp. 436–441.
- Hu, X.; Xu, L.; Lin, X.; Pecht, M. Battery Lifetime Prognostics. Joule 2020, 4, 310–346.
- Sanguesa, J.A.; Torres-Sanz, V.; Garrido, P.; Martinez, F.J.; Marquez-Barja, J.M. A Review on Electric Vehicles: Technologies and Challenges. Smart Cities 2021, 4, 372–404.
- Saner, C.B.; Trivedi, A.; Srinivasan, D. A Cooperative Hierarchical Multi-Agent System for EV Charging Scheduling in Presence of Multiple Charging Stations. IEEE Trans. Smart Grid 2022, 13, 2218–2233.
- Wang, H.J.; Wang, B.; Fang, C.; Li, W.; Huang, H.W. Charging Load Forecasting of Electric Vehicle Based on Charging Frequency. IOP Conf. Ser. Earth Environ. Sci. 2019, 237, 062008.
- Wu, Z.; Chen, B. Distributed Electric Vehicle Charging Scheduling with Transactive Energy Management. Energies 2022, 15, 163.
- Long, T.; Jia, Q.S.; Wang, G.; Yang, Y. Efficient real-time EV charging scheduling via ordinal optimization. IEEE Trans. Smart Grid 2021, 12, 4029–4038.
- Liu, L.; Zhou, K. Electric vehicle charging scheduling considering urgent demand under different charging modes. Energy 2022, 249, 123714.
- Song, J.; Han, Z.; Wang, W.; Chen, J.; Liu, Y. A new secure arrangement for privacy-preserving data collection. Comput. Stand. Interfaces 2022, 80, 103582.
- Li, F.; Xu, L.; Zhang, M.; Tian, Y.; Wu, Y.; Guo, N. Charging Load Feature Extraction and Charging Optimization Recommendations Based on Shanghai Public Charging Station Operation Data. In Proceedings of the 10th International Conference on Power and Energy Systems (ICPES), Chengdu, China, 25–27 December 2020; pp. 338–344.
- Setiawan, A.D.; Hidayatno, A.; Putra, B.D.; Rahman, I. Selection of Charging Station Technology to Support the Adoption of Electric Vehicles in Indonesia with the AHP-TOPSIS Method. In Proceedings of the 3rd International Conference on Power and Energy Applications (ICPEA), Busan, Korea, 24–26 April 2020; pp. 85–88.
- Savari, G.F.; Krishnasamy, V.; Sathik, J.; Ali, Z.M.; Aleem, S.H.A. Internet of Things based real-time electric vehicle load forecasting and charging station recommendation. ISA Trans. 2020, 97, 431–447.
- Tu, W.; Mai, K.; Zhang, Y.; Xu, Y.; Huang, J.; Deng, M.; Chen, L.; Li, Q. Real-Time Route Recommendations for E-Taxies Leveraging GPS Trajectories. IEEE Trans. Ind. Inform. 2021, 17, 3133–3142.
- Wang, G.; Zhang, Y.; Fang, Z.; Wang, S.; Zhang, F.; Zhang, D. FairCharge: A Data-Driven Fairness-Aware Charging Recommendation System for Large-Scale Electric Taxi Fleets. Proc. ACM Interact. Mob. Wearable Ubiquitous Technol. 2020, 4, 1–25.
- Tian, Z.; Jung, T.; Wang, Y.; Zhang, F.; Tu, L.; Xu, C.; Tian, C.; Li, X.Y. Real-Time Charging Station Recommendation System for Electric-Vehicle Taxis. IEEE Trans. Intell. Transp. Syst. 2016, 17, 3098–3109.
- Wang, E.; Ding, R.; Yang, Z.; Jin, H.; Miao, C.; Su, L.; Zhang, F.; Qiao, C.; Wang, X. Joint Charging and Relocation Recommendation for E-Taxi Drivers via Multi-Agent Mean Field Hierarchical Reinforcement Learning. IEEE Trans. Mob. Comput. 2020, 21, 1274–1290.
- Zhang, L.; Wang, S.; Qu, X. Optimal electric bus fleet scheduling considering battery degradation and non-linear charging profile. Transp. Res. Part Logist. Transp. Rev. 2021, 154, 102445.
- Wang, G.; Fang, Z.; Xie, X.; Wang, S.; Sun, H.; Zhang, F.; Liu, Y.; Zhang, D. Pricing-aware Real-time Charging Scheduling and Charging Station Expansion for Large-scale Electric Buses. ACM Trans. Intell. Syst. Technol. 2021, 12, 1–26.
- Bie, Y.; Ji, J.; Wang, X.; Qu, X. Optimization of electric bus scheduling considering stochastic volatilities in trip travel time and energy consumption. Comput.-Aided Civ. Infrastruct. Eng. 2021, 36, 1530–1548.
- Yıldırım, Ş.; Yıldız, B. Electric bus fleet composition and scheduling. Transp. Res. Part Emerg. Technol. 2021, 129, 103197.
- Bie, Y.; Hao, M.; Guo, M. Optimal electric bus scheduling based on the combination of all-stop and short-turning strategies. Sustainability 2021, 13, 1827.
- Basma, H.; Mansour, C.; Haddad, M.; Nemer, M.; Stabat, P. Energy consumption and battery sizing for different types of electric bus service. Energy 2022, 239, 122454.
- Geyer, R.C.; Klein, T.; Nabi, M. Differentially Private Federated Learning: A Client Level Perspective. arXiv 2018, arXiv:1712.07557.
- Mohassel, P.; Rindal, P. ABY3: A Mixed Protocol Framework for Machine Learning. In Proceedings of the 2018 ACM SIGSACConference on Computer and Communications Security, Toronto, ON, Canada, 15–19 October 2018; pp. 35–52.
- Yang, Q.; Liu, Y.; Chen, T.; Tong, Y. Federated Machine Learning: Concept and Applications. arXiv 2019, arXiv:1902.04885.
- Abdulrahman, S.; Tout, H.; Ould-Slimane, H.; Mourad, A.; Talhi, C.; Guizani, M. A Survey on Federated Learning: The Journey From Centralized to Distributed On-Site Learning and Beyond. IEEE Internet Things J. 2021, 8, 5476–5497.
- Du, Z.; Wu, C.; Yoshinaga, T.; Yau, K.L.A.; Ji, Y.; Li, J. Federated Learning for Vehicular Internet of Things: Recent Advances and Open Issues. IEEE Open J. Comput. Soc. 2020, 1, 45–61.
- Zhao, J.; Zhu, X.; Wang, J.; Xiao, J. Efficient client contribution evaluation for horizontal federated learning. In Proceedings of the ICASSP 2021—2021 IEEE International Conference on Acoustics, Speech and Signal Processing (ICASSP), Virtual, 6–11 June 2021; pp. 3060–3064.
- Teimoori, Z.; Yassine, A.; Hossain, M.S. A Secure Cloudlet-based Charging Station Recommendation for Electric Vehicles Empowered by Federated Learning. IEEE Trans. Ind. Inform. 2022, 18, 6464–6473.
- Wu, Z.; Li, Q.; He, B. Exploiting Record Similarity for Practical Vertical Federated Learning. arXiv 2021, arXiv:2106.06312.
- Zhang, Z.; He, N.; Li, D.; Gao, H.; Gao, T.; Zhou, C. Federated transfer learning for disaster classification in social computing networks. J. Saf. Sci. Resil. 2022, 3, 15–23.
- Zheng, Z.; Zhou, Y.; Sun, Y.; Wang, Z.; Liu, B.; Li, K. Applications of federated learning in smart cities: Recent advances, taxonomy, and open challenges. Connect. Sci. 2022, 34, 1–28.
- Pandey, S.R.; Tran, N.H.; Bennis, M.; Tun, Y.K.; Manzoor, A.; Hong, C.S. A Crowdsourcing Framework for On-Device Federated Learning. IEEE Trans. Wirel. Commun. 2020, 19, 3241–3256.
- Saputra, Y.M.; Hoang, D.T.; Nguyen, D.N.; Dutkiewicz, E.; Mueck, M.D.; Srikanteswara, S. Energy Demand Prediction with Federated Learning for Electric Vehicle Networks. arXiv 2019, arXiv:1909.00907.
- Zhang, H.; Bosch, J.; Olsson, H.H. Real-time End-to-End Federated Learning: An Automotive Case Study. In Proceedings of the IEEE 45th Annual Computers, Software, and Applications Conference (COMPSAC), Madrid, Spain, 12–16 July 2021; pp. 459–468.
- Nakamoto, S. Bitcoin: A Peer-to-Peer Electronic Cash System. Decentralized Business Review. 2008. Available online: https://bitcoin.org/bitcoin.pdf (accessed on 18 September 2022).
- Frauenthaler, P.; Sigwart, M.; Spanring, C.; Sober, M.; Schulte, S. ETH Relay: A Cost-efficient Relay for Ethereum-based Blockchains. In Proceedings of the IEEE International Conference on Blockchain (Blockchain), Rhodes, Greece, 2–6 November 2020; pp. 204–213.
- Jain, S.; Ahuja, N.J.; Srikanth, P.; Bhadane, K.V.; Nagaiah, B.; Kumar, A.; Konstantinou, C. Blockchain and Autonomous Vehicles: Recent Advances and Future Directions. IEEE Access 2021, 9, 130264–130328.
- Oyinloye, D.P.; Teh, J.S.; Jamil, N.; Alawida, M. Blockchain Consensus: An Overview of Alternative Protocols. Symmetry 2021, 13, 1363.
- Moniruzzaman, M.; Khezr, S.; Yassine, A.; Benlamri, R. Blockchain for smart homes: Review of current trends and research challenges. Comput. Electr. Eng. 2020, 83, 106585.
- Kim, H.; Park, J.; Bennis, M.; Kim, S.L. Blockchained On-Device Federated Learning. IEEE Commun. Lett. 2020, 24, 1279–1283.
- Huang, Z.; Li, Z.; Lai, C.S.; Zhao, Z.; Wu, X.; Li, X.; Tong, N.; Lai, L.L. A Novel Power Market Mechanism Based on Blockchain for Electric Vehicle Charging Stations. Electronics 2021, 10, 307.
- Lu, Y.; Huang, X.; Zhang, K.; Maharjan, S.; Zhang, Y. Blockchain Empowered Asynchronous Federated Learning for Secure Data Sharing in Internet of Vehicles. IEEE Trans. Veh. Technol. 2020, 69, 4298–4311.
- Khoumsi, A. An Efficient Blockchain-based Electric Vehicle Charging Management System. In Proceedings of the IEEE Symposium on Computers and Communications (ISCC), Athens, Greece, 5–8 September 2021; pp. 1–7.
- Thukral, M.K. Emergence of blockchain-technology application in peer-to-peer electrical-energy trading: A review. Clean Energy 2021, 5, 104–123.
- Gamage, H.T.M.; Weerasinghe, H.D.; Dias, N.G.J. A Survey on Blockchain Technology Concepts, Applications, and Issues. SN Comput. Sci. 2020, 1, 114.
- Bao, J.; He, D.; Luo, M.; Choo, K.K.R. A Survey of Blockchain Applications in the Energy Sector. IEEE Syst. J. 2021, 15, 3370–3381.
- Lepore, C.; Ceria, M.; Visconti, A.; Rao, U.P.; Shah, K.A.; Zanolini, L. A Survey on Blockchain Consensus with a Performance Comparison of PoW, PoS and Pure PoS. Mathematics 2020, 8, 1782.
- Feng, L.; Zhang, H.; Tsai, W.T.; Sun, S. System architecture for high-performance permissioned blockchains. Front. Comput. Sci. 2019, 13, 1151–1165.
- Blockchain.com. Transaction Rate Per Second. Available online: https://www.blockchain.com/charts/transactions-persecond (accessed on 12 June 2022).
- Baza, M.; Nabil, M.; Mahmoud, M.M.E.A.; Bewermeier, N.; Fidan, K.; Alasmary, W.; Abdallah, M. Detecting sybil attacks using proofs of work and location in vanets. IEEE Trans. Dependable Secur. Comput. 2020, 19, 39–53.
- Zhang, S.; Lee, J.H. Analysis of the main consensus protocols of blockchain. ICT Express 2020, 6, 93–97.
- Agung, A.A.G.; Handayani, R. Blockchain for smart grid. J. King Saud Univ. Comput. Inf. Sci. 2022, 34, 666–675.
- Liu, Z.; Wang, D.; Wang, J.; Wang, X.; Li, H. A Blockchain-Enabled Secure Power Trading Mechanism for Smart Grid Employing Wireless Networks. IEEE Access 2020, 8, 177745–177756.
- Toyoda, K.; Zhao, J.; Zhang, A.N.S.; Mathiopoulos, P.T. Blockchain-Enabled Federated Learning With Mechanism Design. IEEE Access 2020, 8, 219744–219756.
- ur Rehman, M.H.; Salah, K.; Khaled, E.; Svetinovic, D. Towards Blockchain-Based Reputation-Aware Federated Learning. In Proceedings of the IEEE INFOCOM 2020—IEEE Conference on Computer Communications Workshops (INFOCOM WKSHPS), Toronto, ON, Canada, 6–9 July 2020; pp. 183–188.
- García, J.S.; Morcillo, J.D.; Redondo, J.M.; Becerra-Fernandez, M. Automobile Technological Transition Scenarios Based on Environmental Drivers. Appl. Sci. 2022, 12, 4593.
- Rajasekaran, A.S.; Azees, M.; Al-Turjman, F. A comprehensive survey on security issues in vehicle-to-grid networks. J. Control Decis. 2022, 1–10.
- Elkasrawy, A.; Venkatesh, B. Demand Response Cooperative and Demand Charge. IEEE Trans. Smart Grid 2020, 11, 4167–4175.
- El-Sayed, I.; Khan, K.; Dominguez, X.; Arboleya, P. A Real Pilot-Platform Implementation for Blockchain-Based Peer-to-Peer Energy Trading. In Proceedings of the IEEE Power & Energy Society General Meeting (PESGM), Virtual, 2–6 August 2020; pp. 1–5.
- Bulut, E.; Kisacikoglu, M.C.; Akkaya, K. Spatio-Temporal Non-Intrusive Direct V2V Charge Sharing Coordination. IEEE Trans. Veh. Technol. 2019, 68, 9385–9398.
- Li, G.; Gong, C.; Zhao, L.; Wu, J.; Boukhatem, L. An Efficient Reinforcement Learning based Charging Data Delivery Scheme in VANET-Enhanced Smart Grid. In Proceedings of the IEEE International Conference on Big Data and Smart Computing (BigComp), Busan, Korea, 19–22 February 2020; pp. 263–270.
- Shurrab, M.; Singh, S.; Otrok, H.; Mizouni, R.; Khadkikar, V.; Zeineldin, H. RAn Efficient Vehicle-to-Vehicle (V2V) Energy Sharing Framework. IEEE Internet Things J. 2022, 9, 5315–5328.
- Pankiraj, J.S.; Yassine, A.; Choudhury, S. Double-Sided Auction Mechanism for Peer-to-Peer Energy Trading Markets. In Proceedings of the IEEE International Conference on Progress in Informatics and Computing (PIC), Shanghai, China, 17–19 December 2021; pp. 443–452.
- Said, D. A Decentralized Electricity Trading Framework (DETF) for Connected EVs: A Blockchain and Machine Learning for Profit Margin Optimization. IEEE Trans. Ind. Inform. 2021, 17, 6594–6602.
- Bansal, G.; Bhatia, A. A Fast, Secure and Distributed Consensus Mechanism for Energy Trading Among Vehicles using Hashgraph. In Proceedings of the International Conference on Information Networking (ICOIN), Barcelona, Spain, 7–10 January 2020; pp. 772–777.
- Otoum, S.; Ridhawi, I.A.; Mouftah, H. A Federated Learning and Blockchain-enabled Sustainable Energy-Trade at the Edge: A Framework for Industry 4.0. IEEE Internet Things J. 2022.
- Wang, J. A novel electric vehicle charging chain design based on blockchain technology. Energy Rep. 2022, 8, 785–793.
- Kaur, K.; Kaddoum, G.; Zeadally, S. Blockchain-Based Cyber-Physical Security for Electrical Vehicle Aided Smart Grid Ecosystem. IEEE Trans. Intell. Transp. Syst. 2021, 22, 5178–5189.
- El Houda, Z.A.; Hafid, A.S.; Khoukhi, L. Blockchain-based Reverse Auction for V2V charging in smart grid environment. In Proceedings of the ICC 2021—IEEE International Conference on Communications, Montreal, QC, Canada, 14–23 June 2021; pp. 1–6.
- Sun, G.; Dai, M.; Zhang, F.; Yu, H.; Du, X.; Guizani, M. Blockchain-Enhanced High-Confidence Energy Sharing in Internet of Electric Vehicles. IEEE Internet Things J. 2020, 7, 7868–7882.





