
| Version | Summary | Created by | Modification | Content Size | Created at | Operation |
|---|---|---|---|---|---|---|
| 1 | Dean Liu | -- | 1215 | 2022-10-31 01:31:04 |
Video Upload Options
The IT Baseline Protection Catalogs, or IT-Grundschutz-Kataloge, ("IT Baseline Protection Manual" before 2005) are a collection of documents from the Germany Federal Office for Security in Information Technology (BSI) that provide useful information for detecting weaknesses and combating attacks in the information technology (IT) environment (IT cluster). The collection encompasses over 3000 pages, including the introduction and catalogs. It serves as the basis for the IT baseline protection certification of an enterprise.
1. Basic Protection
IT baseline protection (protection) encompasses standard security measures for typical IT systems, with normal protection needs.[1]
The detection and assessment of weak points in IT systems often occurs by way of a risk assessment, wherein a threat potential is assessed, and the costs of damage to the system (or group of similar systems) are investigated individually. This approach is very time-intensive and very expensive.
Protection may rather proceed from a typical threat, which applies to 80% of cases, and recommend adequate countermeasures against it. In this way, a security level can be achieved, viewed as adequate in most cases, and, consequently, replace the more expensive risk assessment. In cases in which security needs are greater, such protection can be used as a basis for further action.
2. The IT Baseline Protection Catalogs Layout

To familiarize the user with the manual itself, it contains an introduction with explanations, the approach to IT baseline protection, a series of concept and role definitions, and a glossary. The component catalogs, threat catalogs, and the measures catalogs follow these introductory sections. Forms and cross-reference tables supplement the collection available on the Federal Office for Security in Information Technology's (BSI) Internet platform. Here you can also find the Baseline Protection Guide, containing support functions for implementing IT baseline protection in procedural detail.
Each catalog element is identified by an individual mnemonic laid out according to the following scheme (the catalog groups are named first). C stands for component, M for measure, and T for threat. This is followed by the layer number affected by the element. Finally, a serial number within the layer identifies the element.
2.1. Component Catalog
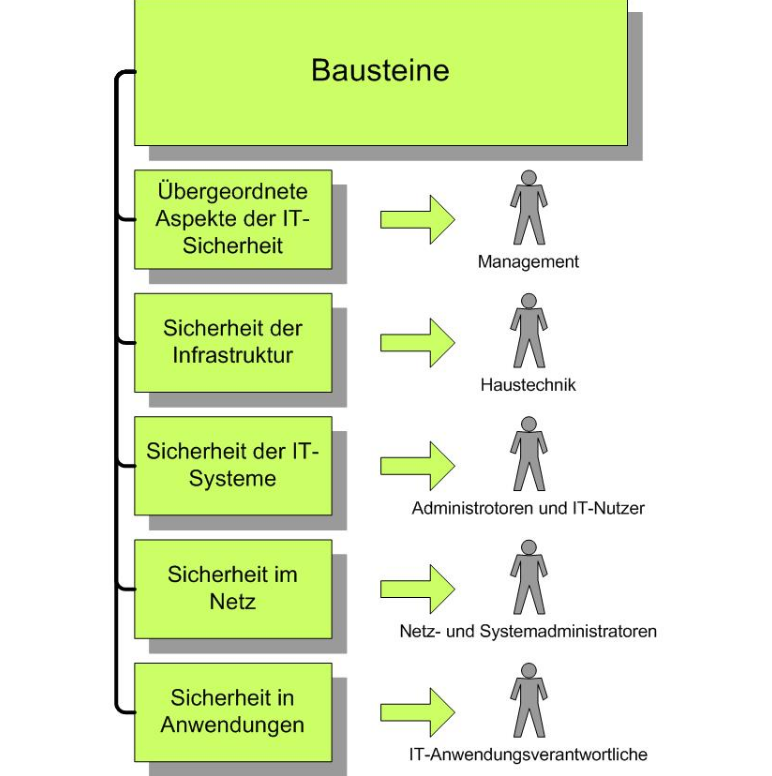
The component catalog is the central element, and contains the following five layers: overall aspects, infrastructure, IT systems, networks and IT applications.
Partitioning into layers clearly isolates personnel groups impacted by a given layer from the layer in question. The first layer is addressed to management, including personnel and outsourcing. The second is addressed to in-house technicians, regarding structural aspects in the infrastructure layer. System administrators cover the third layer, looking at the characteristics of IT systems, including clients, servers and private branch exchanges or fax machines. The fourth layer falls within the network administrators task area. The fifth within that of the applications administrator and the IT user, concerning software like database management systems, e-mail and web servers.
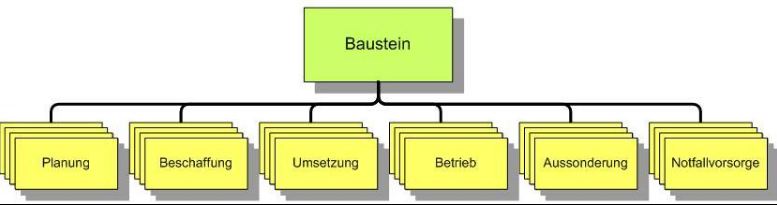
Each individual component follows the same layout. The component number is composed of the layer number in which the component is located and a unique number within the layer. The given threat situation is depicted after a short description of the component examining the facts. An itemization of individual threat sources ultimately follows. These present supplementary information. It is not necessary to work through them to establish baseline protection.
The necessary measures are presented in a text with short illustrations. The text follows the facts of the life cycle in question and includes planning and design, acquisition (if necessary), realization, operation, selection (if necessary), and preventive measures. After a complete depiction, individual measures are once again collected into a list, which is arranged according to the measures catalog's structure, rather than that of the life cycle. In the process, classification of measures into the categories A, B, C, and Z is undertaken. Category A measures for the entry point into the subject, B measures expand this, and category C is ultimately necessary for baseline protection certification. Category Z measures any additional measures that have proven themselves in practice.
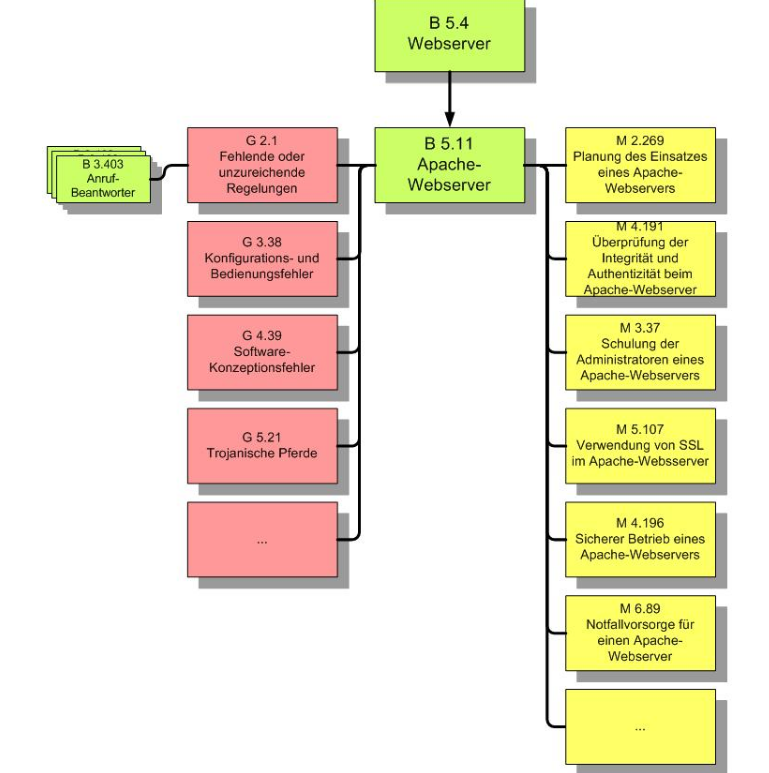
To keep each component as compact as possible, global aspects are collected in one component, while more specific information is collected into a second. In the example of an Apache web server, the general B 5.4 Web server component, in which measures and threats for each web server are depicted, would apply to it, as well as the B5.11 component, which deals specifically with the Apache web server. Both components must be successfully implemented to guarantee the system's security.
The respective measures or threats, which are introduced in the component, can also be relevant for other components. In this way, a network of individual components arises in the baseline protection catalogs.
2.2. Threat Catalogs
The threat catalogs, in connection with the component catalogs, offer more detail about potential threats to IT systems. These threat catalogs follow the general layout in layers. "Force majeure", "organizational deficiencies", "spurious human action", "technical failure", and "premeditated acts" are distinguished. According to the BSI, the knowledge collected in these catalogs is not necessary to establish baseline protection. Baseline protection does, however, demand an understanding of the measures, as well as the vigilance of management. Individual threat sources are described briefly. Finally, examples of damages that can be triggered by these threat sources are given.
2.3. Measures Catalogs
The measures catalogs summarize the actions necessary to achieve baseline protection; measures appropriate for several system components are described centrally. In the process, layers are used for structuring individual measures groups. The following layers are formed: infrastructure, organization, personnel, hardware and software, communication, and preventive measures.
Managers are initially named to initiate and realize the measures in the respective measures description. A detailed description of the measures follows. Finally, control questions regarding correct realization are given. During realization of measures, personnel should verify whether adaptation to the operation in question is necessary; any deviations from the initial measures should be documented for future reference.
2.4. Supplementary Material
Besides the information summarized in the IT Baseline Protection Manual, the Federal Office for Data Security provides further material in the Internet.[2]
The forms provided serve to remedy protection needs for certain IT system components. A table summarizes the measures to be applied for individual components in this regard. Each measure is named and its degree of realization determined. Degrees of realization, "considerable", "yes", "partial", and "no", are distinguished. Finally, the realization is terminated and a manager is named. If the measures' realization is not possible, reasons for this are entered in the adjacent field for later traceability. The conclusion consists of a cost assessment.
Besides the forms, the cross-reference tables another useful supplement. They summarize the measures and most important threats for individual components. Measures, as well as threats, are cited with mnemonics. Measures are cited with a priority and a classification. The table contains correlations between measures and the threats they address. However, the cross-reference tables only cite the most important threats. If the measure cited for a given threat is not applicable for the individual IT system, it is not superfluous. Baseline protection can only be ensured if all measures are realized.
References
- IT Basic Protection Manual, sec. 1.1
- "BSI Download". http://www.bsi.de/gshb/deutsch/download/index.htm.





