Video Upload Options
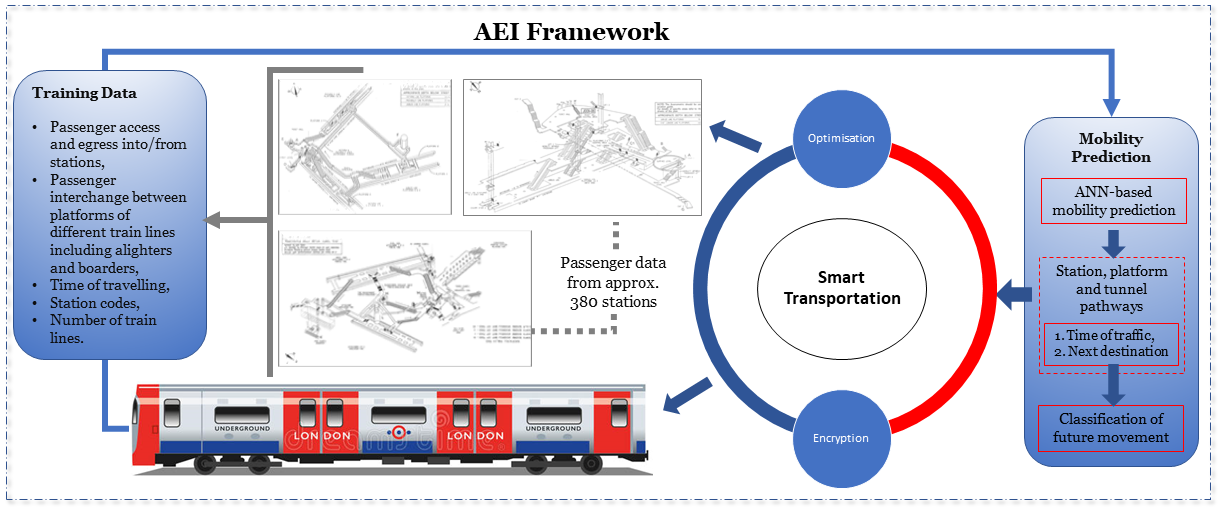
Information and Communication Technology (ICT) enabled optimisation of train's passenger traffic flows is a key consideration of transportation under Smart City planning (SCP). Traditional mobility prediction based optimisation and encryption approaches are reactive in nature; however, Artificial Intelligence (AI) driven proactive solutions are required for near real-time optimisation. Leveraging the historical passenger data recorded via Radio Frequency Identification (RFID) sensors installed at the train stations, mobility prediction models can be developed to support and improve the railway operational performance vis-a-vis 5G and beyond. In this paper we have analysed the passenger traffic flows based on an Access, Egress and Interchange (AEI) framework to support train infrastructure against congestion, accidents, overloading carriages and maintenance. This paper predominantly focuses on developing passenger flow predictions using Machine Learning (ML) along with a novel encryption model that is capable of handling the heavy passenger traffic flow in real-time. We have compared and reported the performance of various ML driven flow prediction models using real-world passenger flow data obtained from London Underground and Overground (LUO). Extensive spatio-temporal simulations leveraging realistic mobility prediction models show that an AEI framework can achieve 91.17% prediction accuracy along with secure and light-weight encryption capabilities. Security parameters such as correlation coefficient (<0.01), entropy (>7.70), number of pixel change rate (>99%), unified average change intensity (>33), contrast (>10), homogeneity (<0.3) and energy (<0.01) prove the efficacy of the proposed encryption scheme.
1. Introduction
The current exponential passenger traffic flow is a precursor towards an imminent traffic flux, encryption, and capacity crunch. In this backdrop, effective management of traffic through optimisation, preserving confidential data streams and effective utilisation of resources through deployment of a large number of 5G Heterogeneous cells (HetNets) in the train underground environment have emerged as the most conceding solution to achieve the prediction accuracies, encryption, and manifold capacity gain goal [1]. However, traffic flows and encryption of the passengers’ data are on a direct collision path with complicated passengers traffic movement, which needs AI for optimisation, encryption, and an energy-efficient vision of 5G HetNets deployment in the train underground environment. This is due to the complexity in high accumulated traffic flows with relevant information, i.e., traffic patterns within the LUO environment, to be optimised [1][2], and encrypted [3]. It is difficult to understand the LUO ecology from a business point of view when cellular services are limited [4]. Furthermore, traffic variations are unknown, which is one of the dominant factors that affect the environment. With the limited information, optimisation and encryption would become significantly challenging, which eventually leads to ineffective resource management and a high number of unnecessary deployments that have CO2 emissions [3][5] and costs [6].
2. Related Work
Mobile operators capitalises on large scale mobility traces obtained via mobile phones to optimize their network operational behaviour. In addition, movement patterns aid to develop a scenario where mobile users play a significant role in their movement behaviours through most visited places. Embracing the world in the 5G era, challenges in understanding traffic patterns and human mobility predictions is limited, which has been experienced by urbanised cellular towers [4][7][8]. Extra diligent intelligence is required to fully automate the network that would be a hypothetical remedy against current complexities involved in predicting the traffic flows in the underground train environment [9][10]. Traffic flow patterns can be predicted by the ML models by using historical data, as shown in Figure 1. This would aid in developing solutions for optimisation and encryption, which makes it easier to proactively monitor and predict passengers movements [9][11].
Several studies on real-time datasets despite randomness in the path of traffic flow, show user movement predictions [12][13]. The movements are user trajectories from source to destination with regular intervals, expected or unexpected. Several comprehensive surveys for mobility prediction are available in [14][15][16] that exploit various methods of predicting user mobility patterns where Markov chain-based is a popular predictor due to being less complex in nature [12][15][17]. However, with the limitations of real-time datasets that have complexity involved, ML predictors can be a viable alternative in order to study traffic flow and provide encryption to it. Hence, there is a need to explore the performance of ML predictors for the mobility prediction by using a meaningful and novel AEI framework that, with the best of our knowledge, has never been considered before. Several mobility prediction schemes probabilistic approaches for predicting the likelihood of the next destination were discussed in [16][18][19][20]. In the context of cellular network optimisation, various machine learning algorithms including decision tree [21], k-means algorithm [22][23], and artificial neural networks [24] have been employed for predicting user mobility patterns in order to perform network resource optimisation patterns. In the context of road networks, NN algorithms [25][26] have been used for short-term traffic flow prediction, as well for reduce road congestion by analysing traffic information and further relaying the message back to the vehicles [27]. A smartphone based software to recognise traffic flows with high accuracy was proposed by using the Random Forests (RF) classification model and positioning technology in [26][28].
London Underground Limited (LUL) is one of the oldest and largest tubes in the world, which is renowned for carrying a large number of passengers in all cardinal directions of the metropolitan city, London. Due to the nature of the trains, they are heavily loaded, and it is of utmost importance that user-friendly traffic information within train carriages to prevent superfluous congestion and confusion is provided. It is evident from the fact of the horde of passengers travelling at different times of the day must be facilitated with comfort and safety [2][29][30]. A similar contribution was made in the field of train adaptive control when identifying the rolling stock parameters [29] of moving trains. Furthermore, an article was proposed that focused on the paradigm of localisation of rolling stocks and its movements, dispatching control, and rail traffic in [30]. A system-theoretic standpoint for establishing transformation and reduction of the parallel paths; reducing overhead was developed in [31]. A similar study was contingent upon robustness into the operational system by analysing the problems of rail transformation of the network to some parallel lists where a taxonomy of the time-optimality criterion is proposed for an ordinary differential [32]; however, the transformation of the railway does not take passenger traffic flows into account through which robustness can be injected into the operation of the rail system. Another illustration in regard to correlations of rail transit traffic flow, which impacts the train control system on rail transit service quality [33].
Some works are found in the context of passenger traffic flows, network complexity, and energy efficiency [34]. Real-time traffic information that drives interstation running time monitored by train supervision systems in [35]. In the same context, another work that further classifies the traffic into weights and temperatures is found where the structure of the classification training model was proposed with an ML algorithm, such as KNN in [36]. The cellular coverage inside the underground stations are often patchy or in some cases non-existent whereas the traffic flows are quite complex. This makes it quite challenging to control and predict the passenger flow variations and also real-time operational optimisation for smart city planning (Mayor of London Transport Strategy can be found online at: https://www.london.gov.uk/sites/default/files/mayorstransport-strategy-2018.pdf).
Every day, thousands of passengers use RFID cards to tap in and tap out of the train stations providing an estimate of passenger flows. The use of passive RFID technology requires an RFID card and a reader that is cost-effective and secure based on Radio Frequency (RF) electromagnetic fields. RFID operates in the range of frequencies such as; Low-Frequency (LF) runs at 125 to 134 kHz, High-Frequency (HF) at 13.56 MHz, and Ultra-High-Frequency (UHF) runs at 433 and 860–960 MHz. The database linked to RFID devices stores the passenger data in the form of unique identification numbers through an electronic microchip. In the context of encryption, some works have been conducted to alter the data in such a way that it appears random and irregular [37]. Two types of encryption, known as symmetric key and asymmetric key in [37] are used to highlight the importance of current trends in encryption. In the symmetric key algorithm, keys at encryption and decryption are the same level, while they are different in asymmetric keys. In both types of algorithms, the main aim of encryption is to protect the valuable data from attackers. Chaotic systems can produce random data that can be employed in a cryptosystem [38]. In [38][39][40][41], researches have reported a number of encryption schemes that used chaotic maps, which are well suited for light weight encryption and offer ergodicity, sensitivity, and randomness. [38][39][40][41]. In our work, we have also used the aforementioned properties of chaos and proposed a scheme for protection data from attackers. Two chaotic maps, nonlinear chaos map [42] and Logistic map [43], are used in the encryption process, which is discussed in more detail in the latter part of the paper.
3. Conclusion
The novel spatio-temporal mobility prediction based optimisation and encryption algorithm proposed in this paper can solve numerous future 5G network pathways and traffic movement problems. The proposed AEI framework employs the ingenious concept of future passenger location estimations and accuracies through which advantages of futuristic optimisation can be maximised. It then devises classification of mobility prediction and preserving important passengers data with encryption for the estimated future network scenario. Most of the conventional approaches deal with reactive instead of predictive mode of operations expected to perform necessary optimisation in response to dynamic environment changes, which leaves behind a gap for the availability of computational resources. On the contrary, the proposed approach provides state-of-the-art heuristic techniques for traffic movement predictions, network pathway implementation, implementation of encrypted traffic flows, and practical solutions to address optimisation problems ahead of time in the underground train network. With this outset, 5G ambitions regarding address latency and QoS issues can be met. Therefore, it comprehensively discusses the proactive ML based classification of mobility prediction algorithms, mapping of optimal classification algorithms and an encryption algorithm with a single map for faster processing. Extensive simulations based on real-time traffic employing realistic classification of mobility predictions using AEI framework can achieve 91.17% with an ANN algorithm as compared to other ML algorithms mentioned in this paper. Comparative performance analysis with movement precision of train traffic flows indicate adequate stability and robustness of the proposed AEI framework towards predicting accuracies, and hence, it provides advanced encryption to the sensitive information to preserve from threats. Moreover, the AEI framework provides an opportunity to discuss cell load, coverage and capacity, and energy efficiency coupled with carbon emissions in the underground train network due to the overlap among their primary parameters of optimisation, which would be presented in our upcoming researches. For future works, we would provide metrics to implement optimisation with the incorporation of underground specific tap-in tap-out individual offsets and energy efficiency coupled with carbon emissions. Furthermore, we aim to work along the lines of user specific behaviours to maintain QoS requirements, provide reliable encryption and cellular cell constraints to effectively serve underground traffic flow. Another promising area of the research would incorporate several direction bounds of train traffic in conjunction to address energy efficiency and network pathway design problems.
References
- Oh, E.; Krishnamachari, B.; Liu, X.; Niu, Z. Toward dynamic energy-efficient operation of cellular network infrastructure. IEEE Commun. Mag. 2011, 49, 56–61.
- Patel, D.; Neil, G. Passenger information systems on London Underground Limited rolling stock. In Proceedings of the IEEE Colloquium on Passenger Information (Trains and Trackside) (Digest No.030), London, UK, 5 February 1991.
- Malmodin, J.; Lunden, D.; Moberg, Å.; Andersson, G.; Nilsson, M. Life Cycle Assessment of ICT: Carbon footprint and operational electricity use from the operator, national, and subscriber perspective in Sweden. IEEE J. Ind. Ecol. 2014, 18, 829–845.
- Wang, H.; Xu, F.; Li, Y.; Zhang, P.; Jin, D. Understanding Mobile Traffic Patterns of Large Scale Cellular Towers in Urban Environment. IEEE/ACM Trans. Netw. 2017, 25, 1147–1161.
- Asad, S.M.; Ozturk, M.; Rais, R.N.B.; Zoha, A.; Hussain, S.; Abbasi, Q.H.; Imran, M.A. Reinforcement Learning driven Energy Efficient Mobile Communication and Applications. In Proceedings of the IEEE International Symposium on Signal Processing and Information Technology (ISSPIT), Ajman, UAE, 10–12 December 2019.
- Chen, C.; Berry, R.A.; Honig, M.L.; Subramanian, V.G. Competitive Resource Allocation in HetNets: The Impact of Small-Cell Spectrum Constraints and Investment Costs. IEEE Trans. Cogn. Commun. Netw. 2017, 3, 478–490.
- Baumann, P.; Koehler, C.; Dey, A.K.; Santini, S. Selecting Individual and Population Models for Predicting Human Mobility. Trans. Mob. Comput. 2018, 17, 2408–2422.
- Lee, K.; Hong, S.; Kim, S.J.; Rhee, I.; Chong, S. SLAW: Self-Similar Least-Action Human Walk. IEEE/ACM Trans. Netw. 2012, 20, 515–529.
- Klaine, P.V.; Imran, M.A.; Onireti, O.; Souza, R.D. A Survey of Machine Learning Techniques Applied to Self-Organizing Cellular Networks. IEEE Commun. Surv. Tutor. 2017, 19, 2392–2431.
- Liu, L.; Shah, S.A.; Zhao, G.; Yang, X. Respiration symptoms monitoring in body area networks. Appl. Sci. 2018, 8, 568.
- Fazio, P.; Tropea, M.; De Rango, F.; Voznak, M. Pattern Prediction and Passive Bandwidth Management for Hand-over Optimization in QoS Cellular Networks with Vehicular Mobility. IEEE Trans. Mob. Comput. 2016, 15, 2809–2824.
- Farooq, H.; Imran, A. Spatiotemporal Mobility Prediction in Proactive Self-Organizing Cellular Networks. IEEE Commun. Lett. 2017, 21, 370–373.
- Song, C.; Qu, Z.; Blumm, N.; Barabási, A.L. Limits of Predictability in Human Mobility. IEEE Trans. Mob. Comput. 2010, 327, 1018–1021.
- Zhang, H.; Dai, L. Mobility prediction: A survey on state-of-the-art schemes and future applications. IEEE Access 2019, 7, 802–822.
- Park, H.; Lim, Y. A markov-based prediction algorithm for user mobility at heterogeneous cloud radio access network. In Proceedings of the IEEE International Conference on Big Data and Smart Computing (BigComp), Kyoto, Japan, 27 February–2 March 2019; pp. 1–5.
- Aliu, O.G.; Imran, A.; Imran, M.A.; Evans, B. A Survey of Self Organisation in Future Cellular Networks. IEEE Commun. Surv. Tutor. 2013, 15, 336–361.
- Lv, Q.; Qiao, Y.; Ansari, N.; Liu, J.; Yang, J. Big Data Driven Hidden Markov Model Based Individual Mobility Prediction at Points of Interest. IEEE Trans. Veh. Technol. 2017, 66, 5204–5216.
- Hasan Farooq, A.A.; Imran, A. Mobility Prediction-Based Autonomous Proactive Energy Saving (AURORA) Framework for Emerging Ultra-Dense Networks. IEEE Trans. Green Commun. Netw. 2018, 2, 958–971.
- Cong, Y.; Zhou, X.; Kennedy, R.A. Interference Prediction in Mobile Ad Hoc Networks With a General Mobility Model. IEEE Trans. Wirel. Commun. 2015, 14, 4277–4290.
- Apollinaire Nadembega, A.H.; Taleb, T. A Destination and Mobility Path Prediction Scheme for Mobile Networks. IEEE Trans. Veh. Technol. 2015, 64, 2577–2590.
- Yu, Z.; Wang, H.; Guo, B.; Gu, T.; Mei, T. Supporting Serendipitous Social Interaction Using Human Mobility Prediction. IEEE Trans. Hum.-Mach. Syst. 2015, 45, 811–818.
- Mondal, M.A.; Rehena, Z. Identifying Traffic Congestion Pattern using K-means Clustering Technique. In Proceedings of the International Conference on Internet of Things: Smart Innovation and Usages (IoT-SIU), Ghaziabad, India, 18–19 April 2019.
- Asif, M.T.; Dauwels, J.; Goh, C.Y.; Oran, A.; Fathi, E.; Xu, M.; Dhanya, M.M.; Mitrovic, N.; Jaillet, P. Spatiotemporal Patterns in Large-Scale Traffic Speed Prediction. IEEE Trans. Intell. Transp. Syst. 2014, 15, 794–804.
- Chen, M.; Challita, U.; Saad, W.; Yin, C.; Debbah, M. Artificial Neural Networks-Based Machine Learning for Wireless Networks: A Tutorial. IEEE Commun. Surv. Tutor. 2019, 21, 3039–3071.
- Chan, K.Y.; Dillon, T.S.; Singh, J.; Chang, E. Neural-Network-Based Models for Short-Term Traffic Flow Forecasting Using a Hybrid Exponential Smoothing and Levenberg–Marquardt Algorithm. IEEE Trans. Intell. Transp. Syst. 2012, 13, 644–654.
- Ning, Y. Traffic Pattern Recognition System Design and Development Based on Smart Phones. In Proceedings of the 7th International Conference on Intelligent Computation Technology and Automation, Changsha, China, 25–26 October 2014.
- Ki, Y.K.; Heo, N.W.; Choi, J.W.; Ahn, G.H.; Park, K.S. An incident detection algorithm using artificial neural networks and traffic information. In Proceedings of the Cybernetics and Informatics (K&I), Lazy pod Makytou, Slovakia, 31 January–3 February 2018.
- Zhany, Y.; Luo, B.-S. Development and Implementation of Traffic Pattern Recognition Software Based on iOS Framework. In Proceedings of the 7th International Conference on Intelligent Computation Technology and Automation, Changsha, China, 25–26 October 2014; pp. 182–185.
- Gorbachev, R.; Moroz, N.; Semenikhin, K.; Starostenko, A. Identification of Rolling Stock Parameters for Adaptive Train Control. In Proceedings of the 2016 International Conference on Engineering and Telecommunication (EnT), Moscow, Russia, 29–30 November 2016; pp. 99–103.
- Fikejz, J. Localization Of Rolling Stock Within The Railway Network Model. In Proceedings of the International Conference on Multimedia Computing and Systems (ICMCS), Marrakech, Morocco, 14–16 April 2014; pp. 734–739.
- Meng, X.; Jia, L.; Xie, J.; Qin, Y.; Xu, J. Complex characteristic analysis of passenger train flow network. In Proceedings of the 2010 Chinese Control and Decision Conference, Xuzhou, China, 26–28 May 2010; pp. 2533–2536.
- Bavafa-Toosi, Y.; Blendinger, C.; Mehrmann, V.; Steinbrecher, A.; Unger, R. A New Methodology for Modeling, Analysis, Synthesis, and Simulation of Time-Optimal Train Traffic in Large Networks. IEEE Trans. Autom. Sci. Eng. 2008, 5, 43–52.
- Wang, G.; Zeng, X.; Yuan, T. Study on the influence of train control system on service quality of rail transit. In Proceedings of the 2017 International Conference on Service Systems and Service Management, Dalian, China, 16–18 June 2017; pp. 1–4.
- Gu, Q.; Tang, T.; Cao, F.; Song, Y.D. Energy-Efficient Train Operation in Urban Rail Transit Using Real-Time Traffic Information. IEEE Trans. Intell. Transp. Syst. 2014, 15, 1216–1233.
- Tong, G.; Fan, C.; Cui, F.; Meng, X. Fuzzy Neural Network Model Applied in the Traffic Flow Prediction. In Proceedings of the 2006 IEEE International Conference on Information Acquisition, Weihai, China, 20–23 August 2006; pp. 1229–1233.
- Zhao, E.; Zhang, Y.; Yao, D.; Li, L.; Tan, J.; Li, Z. A New Training Structure for Multiple-to-Multiple Traffic Flow Prediction. In Proceedings of the 2018 Chinese Automation Congress (CAC), Xi’an, China, 30 November–2 December 2018.
- Ahmad, J.; Ahmed, F. Efficiency analysis and security evaluation of image encryption schemes. Computing 2010, 23, 25.
- Major, W.; Buchanan, W.J.; Ahmad, J. An authentication protocol based on chaos and zero knowledge proof. Nonlinear Dyn. 2020, 3068–3087.
- Adeel, A.; Ahmad, J.; Larijani, H.; Hussain, A. A Novel Real-Time, Lightweight Chaotic-Encryption Scheme for Next-Generation Audio-Visual Hearing Aids. Cognit. Comput. 2019.
- Masood, F.; Ahmad, J.; Shah, S.A.; Jamal, S.S.; Hussain, I. A Novel Hybrid Secure Image Encryption Based on Julia Set of Fractals and 3D Lorenz Chaotic Map. Entropy 2020, 22, 274.
- Jawad, A.; Masood, F.; Shah, S.A.; Jamal, S.S.; Hussain, I. A Novel Secure Occupancy Monitoring Scheme Based on Multi-Chaos Mapping. Symmetry 2020, 12, 350.
- Ahmad, J.; Khan, M.A.; Hwang, S.O.; Khan, J.S. A compression sensing and noise-tolerant image encryption scheme based on chaotic maps and orthogonal matrices. Neural Comput. Appl. 2017, 28, 953–967.
- Zhang, G.; Ding, W.; Li, L. Image Encryption Algorithm Based on Tent Delay-Sine Cascade with Logistic Map. Symmetry 2020, 12, 355.