The Internet of Things (IoT) is an emerging technology and provides connectivity with the physical world using the support of 5G communication. In recent decades, there have been a lot of applications based on IoT technology for the sustainability of smart cities, such as farming, e-healthcare, education, smart homes, weather monitoring, etc. These applications communicate in a collaborative manner between embedded IoT devices and systematize daily routine tasks. However, it is observed that transmission system in constraint oriented network is still a burning research issue in smart cities. Also, there is an existence of a lot of malicious machines that can damage sustainable services of smart cities and compromised the connected devices. Thus, proposing an efficient solution using a 5G system is a demanding task for a smart environment that efficiently utilizes the communication resources and securing the data over insecure routes.
1. Introduction
IoT is a network of intelligent devices that exchange online data and support sustainable services. In all aspects of daily life, IoT plays a significant role with the integration of next-generation 5G networks
[1][2][3] to facilitate many areas such as healthcare, vehicles, entertainment, industrial equipment, sport, homes, social networking, etc. IoT is one of the most advanced developments in the last century and has been used in many applications, but still, privacy and authentication are among research challenges
[4][5][6] for sustainable computing. On the other hand, the number of connected devices is being increased consistently and their number has surpassed 50 billion, with the data produced by these devices also increasing exponentially. Indeed, the overall ubiquity of IoT facilitates day-to-day activities and enables people to interact with each other using 5G networks
[7][8]. However, this holistic view also raises security issues such as data preserving, botnet attacks, hijacking IoT devices, etc.
The main challenges faced in IoT applications are manufacturing standards, update management, physical hardening, user knowledge, and awareness
[9][10]. As a result, various IoT structures have been used to build and launch many IoT security applications. An IoT structure is a set of instructions, protocols, and specifications that simplifies the implementation of IoT. The accomplishment of these applications depends primarily on the characteristics of the IoT framework’s ecosystems, with a special focus on safety mechanisms where protection and privacy problems are of vital importance
[11][12][13]. Traditional IoT architecture is composed of three physical, network, and application layers. Devices are embedded in the physical layer that employ certain techniques to sense the environment and perform wireless communication to other devices
[14][15][16]. A lot of research work has reported on IoT protection and privacy issues. However, once the latest technology arrives, it will overcome the security dilemma in IoT as well.
IoT has various uses in real-time contexts and therefore has made a huge impact in almost every sector of life. It combines sensors, smart devices, and RFID technologies through the Internet to create intelligent coordination. The sensors are tiny energy-constrained devices employed to sense information and deliver it over the network for intelligent decisions. These networks in an IoT environment come in a different structure, such as distributed, ubiquitous, grid, and vehicular. However, due to rapid development, extensive use, and their ubiquitous nature, IoT networks face various protection, privacy, and vulnerability issues in their applications and infrastructure. A few works on these security issues reported in the literature mainly employed machine learning and blockchain approaches. Different researchers have worked on different security aspects of IoT networks, including privacy preservation
[17][18][19], authentications
[20][21][22], access control
[23][24][25], scalability
[26][27][28], information sharing
[29][30][31], and trust management
[32][33][34]. However, proposing a decentralized communication platform for facilitating connected users over the insecure Internet and mobile network is a demanding task. In addition, the gathered data should be transmitted without compromising the identification of nodes and sensitive information.
Figure 1 illustrates the components of the proposed architecture. The proposed architecture presents a sustainable development for public health applications, which is a significant factor in optimizing the system management and flow of information to assist society. It utilizes the technology of IoT, sensors, and 5G to share the resources and communication bandwidth efficiently. In addition, the cooperation of mobile sink highly distributes a load of IoT technology using the 5G network and increases mobility support and resource management.
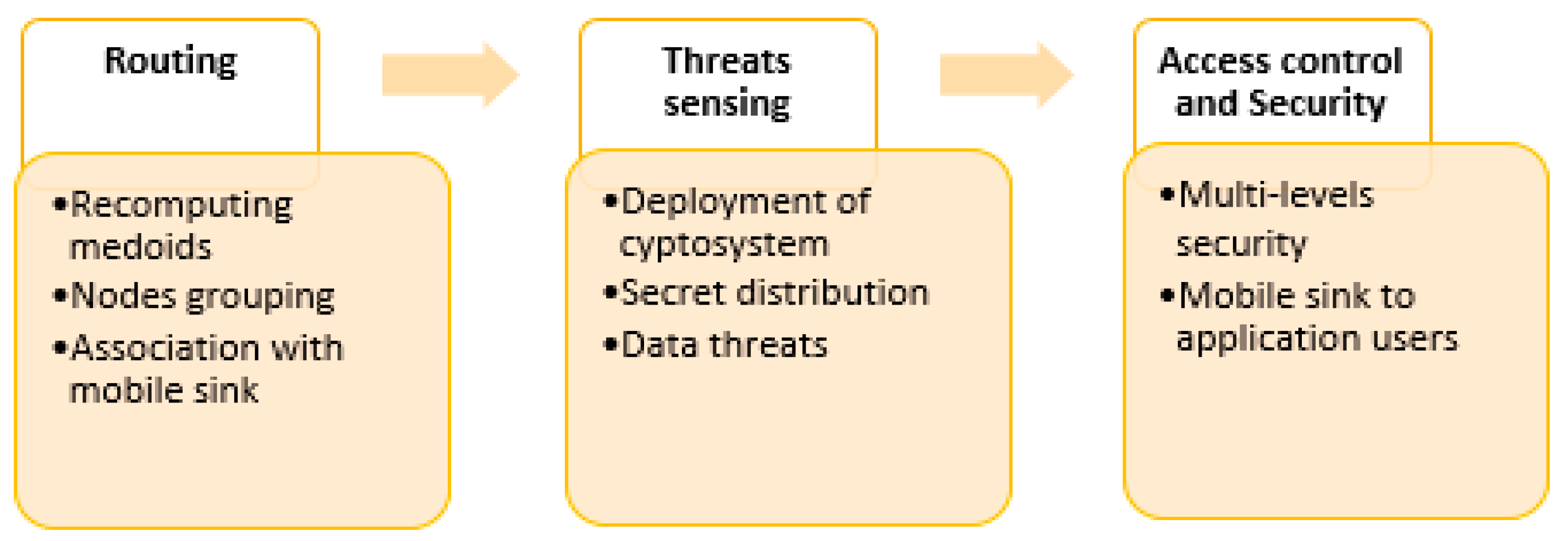 Figure 1.
Figure 1. Main components of the proposed architecture.
2. Related work
In
[35], the authors defined the required infrastructure and the protocol for the secure implementation of the IoT framework. They identified several new methods that could be used to address IoT security problems using machine learning and blockchain-based approaches. Advance 5G wireless sensor technologies
[36][37] facilitate mobile communication for complex and highly dynamic environments. These technologies acquiring the information by sensing the data from a real-world environment and transmit to a sink node to fulfill the demands of the application users. To collaborate with mobile IoT networks, the solution should be robust and more reliable to support the requests of application users. In
[38], the authors investigated the outage probability (OP) and predicted wireless communication. It was based on the improved grey wolf optimization algorithm and an Elman neural network was proposed. The simulation-based results illustrate that the prediction accuracy was higher than other solutions and managed the wireless transmission system more accurately for mobile IoT networks. The authors in
[39] proposed an Internet of Things-based WBAN for disaster cases. It ensures life savings and smooth communication using technologies of the wireless network. In addition, a gateway selection algorithm using fuzzy logic was developed that aims to select a suitable wireless communication technology.
The authors in
[40] maximized the task throughput for the IoT-enabled 5G network in the presence of heterogeneous task demands and constraint resources. They utilized multi-graph coloring and proposed an efficient two-stage process. The computational complexity and correctness of the proposed algorithm were analyzed. The simulation-based results demonstrate its efficacy against existing work. The authors in
[41] suggested a rigorous prediction model using a rule-based machine learning classification method, i.e., the decision tree, on the noise-free accuracy dataset for real-life cell phone data of individual users. The Naive Bayes classifier and Laplace estimator were used to increase the model’s prediction accuracy by minimizing noisy instances in the results. In
[42], for Industrial Internet of Things (IIoT) devices, a machine learning-based anomaly detection system was proposed to detect cyber threats such as backdoor, order injection, and Structured Query Language (SQL) injection attacks. A distributed ledger-based blockchain (DLBC) technology was recommended in
[43] to fix IoT protection and privacy problems such as spoofing and false authentication. In
[44], a distributed intelligence system was proposed to reduce unnecessary data transfer to the cloud through immediate decision-making. They also resolved several security issues in the IoT environment using blockchain technology.
In
[45], classified devices with an ML approach were used to boost IoT environment security by identifying malicious data in the blockchain network. Similarly, a trust protection mechanism was introduced in
[46] to provide stable and effective access control to identify and remove intrusions in a distributed IoT system. The authors in
[47] presented a Safe Private Blockchain (SPB) that allows energy prosumers to negotiate energy rates and share energy with an IoT smart grid deployment. It consists of a three-layered trust management system in which trust is tracked based on the interactions between supply chain members, and trust. Finally, credibility is dynamically allocated based on these interaction scores
[48]. In
[49], a blockchain-based, privacy-preserving update protocol was suggested that allows users to update apps but also preserve their privacy. It increases the security level as compared to an existing solution with improved network performance. The authors in
[50] proposed a clustering perturbation algorithm to preserve privacy for social networks that aim to introduce a strategy of exchanging attributes among vertices of the same degree randomly. It makes the network attackers pursue fake targets and accordingly maintains the stable structure of the observing field. In
[51], the authors proposed a deep-reinforcement-learning-based quality-of-service (QoS)-aware secure routing protocol (DQSP). It ensures the QoS along with the extraction of knowledge from traffic history. In addition, it optimizes the routing policy and improves the data delivery performance against other solutions. The authors in
[52] proposed a telemedicine system based on MEC and artificial intelligence for remote health monitoring and automatic disease diagnosis. The concept of mobile edge computing (MEC) among users and cloud systems reduces the problem of 5G scenarios in terms of latency and processing. Different computing technologies are also utilized in the proposed solution to significantly improve the efficacy of the patient treatment by decreasing the computing cost using an intelligent paradigm.
IoT technology has gained prominent attention for the development of sustainable smart cities with the support of a 5G network. Table 1 describes the research findings along with limitations based on the discussed work.
Table 1. Summary of discussed work.
| |
Contributions and Limitations |
| Existing solutions |
-
Many solutions offer quality-aware services and lead to higher bandwidth and improved data delivery performance.
-
However, most of the solutions face connectivity problems when the load on IoT nodes increases especially in 5G mobile networks.
-
Due to frequent network disconnectivity issues, it was also observed that most of the proposed solutions have a high data latency for real-time applications.
-
It was also noticed that 5G communication offers attention to many real-world network technologies for the growth of promising solutions with the collaboration of cloud and mobile infrastructure.
-
However, most of the network technologies with the collaboration of the 5G network lack security and communication trust.
|
| Proposed architecture |
A solution was developed using a 5G network for real-time public health application that increases the sustainability of complex operations in the presence of unpredictable events. It also facilitates application users with high communication bandwidth and optimal performance. |
3. Conclusions
We proposed a mobility support 5G architecture with real-time routing for sustainable smart cities. Its main factors are highlighted as follows:
- i. It supports the delivery of online data with a high level of security and network continuity for mobile networks. Unlike other traditional approaches, it leads to few data delays and decreases the processing cost with the availability of higher bandwidth.
- ii. It also secures the 5G ecosystem with a nominal risk rate and supports trustworthy communication. The mobile sink collaborates with both gateway nodes and medical storage centers to gather the IoT data, which explicitly increases the success rate of sensitive data with optimum delay.
- iii. Moreover, instead of only securing the boundary points for data routing, the proposed architecture performs risk analysis for the IoT nodes and links. The proposed architecture was tested and evaluated against existing work in terms of various experiments and it was seen to have significantly better performance. The multi-level security secures the routing for next-generation networks without imposing additional resource usage.
However, it was observed that the proposed architecture still lacks intelligence in distributing the IoT data on established routes and leads to communication complexity when network nodes increase. Therefore, its aim is to introduce some machine learning schemes to train the proposed architecture with nominal latency and support emergency communications.

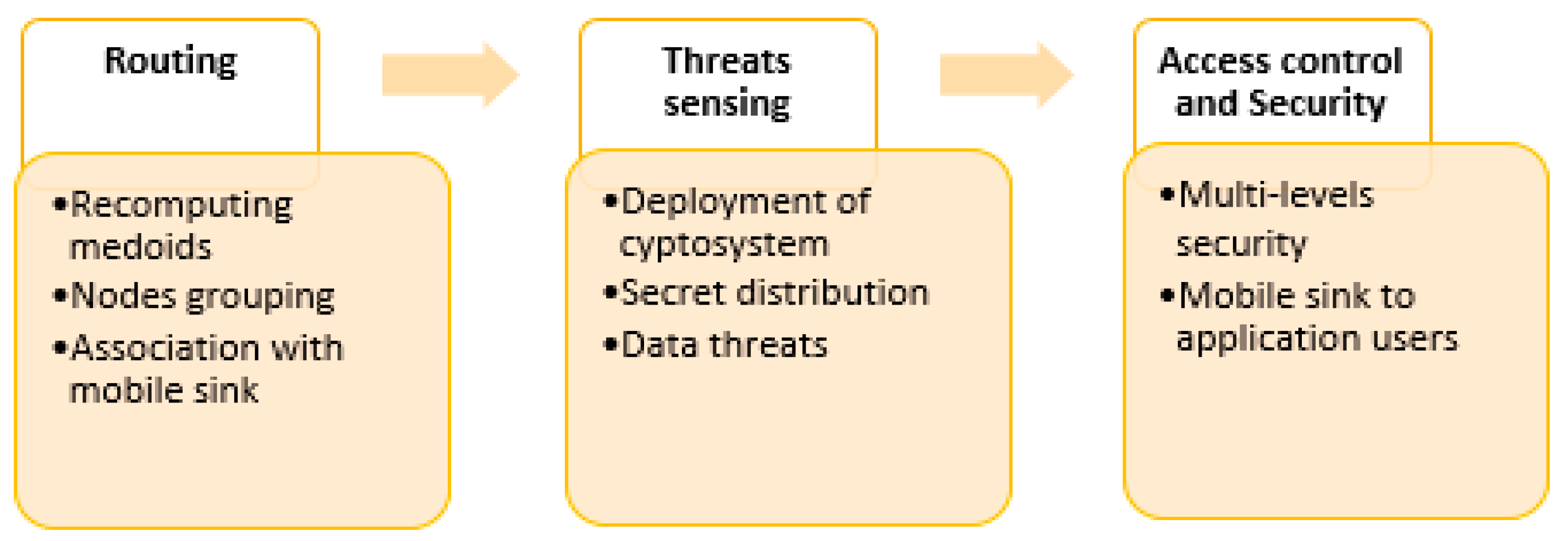 Figure 1. Main components of the proposed architecture.
Figure 1. Main components of the proposed architecture.