Deep packet inspection (DPI) is a type of data processing that inspects in detail the data being sent over a computer network, and may take actions such as alerting, blocking, re-routing, or logging it accordingly. Deep packet inspection is often used to baseline application behavior, analyze network usage, troubleshoot network performance, ensure that data is in the correct format, check for malicious code, eavesdropping, and internet censorship, among other purposes. There are multiple headers for IP packets; network equipment only needs to use the first of these (the IP header) for normal operation, but use of the second header (such as TCP or UDP) is normally considered to be shallow packet inspection (usually called stateful packet inspection) despite this definition. There are multiple ways to acquire packets for deep packet inspection. Using port mirroring (sometimes called Span Port) is a very common way, as well physically inserting a network tap which duplicates and sends the data stream to an analyzer tool for inspection. Deep Packet Inspection (and filtering) enables advanced network management, user service, and security functions as well as internet data mining, eavesdropping, and internet censorship. Although DPI has been used for Internet management for many years, some advocates of net neutrality fear that the technique may be used anticompetitively or to reduce the openness of the Internet. DPI is used in a wide range of applications, at the so-called "enterprise" level (corporations and larger institutions), in telecommunications service providers, and in governments.
- net neutrality
- packet inspection
- security
1. Background
DPI technology boasts a long and technologically advanced history, starting in the 1990s, before the technology entered what is seen today as common, mainstream deployments. The technology traces its roots back over 30 years, when many of the pioneers contributed their inventions for use among industry participants, such as through common standards and early innovation, such as the following:
- RMON
- Sniffer
- Wireshark
Essential DPI functionality includes analysis of packet headers and protocol fields. For example, Wireshark offers essential DPI functionality through its numerous dissectors that display field names and content and, in some cases, offer interpretation of field values.
Some security solutions that offer DPI combine the functionality of an intrusion detection system (IDS) and an Intrusion prevention system (IPS) with a traditional stateful firewall.[1] This combination makes it possible to detect certain attacks that neither the IDS/IPS nor the stateful firewall can catch on their own. Stateful firewalls, while able to see the beginning and end of a packet flow, cannot catch events on their own that would be out of bounds for a particular application. While IDSs are able to detect intrusions, they have very little capability in blocking such an attack. DPIs are used to prevent attacks from viruses and worms at wire speeds. More specifically, DPI can be effective against buffer overflow attacks, denial-of-service attacks (DoS), sophisticated intrusions, and a small percentage of worms that fit within a single packet.[2]
DPI-enabled devices have the ability to look at Layer 2 and beyond Layer 3 of the OSI model. In some cases, DPI can be invoked to look through Layer 2-7 of the OSI model. This includes headers and data protocol structures as well as the payload of the message. DPI functionality is invoked when a device looks or takes other action based on information beyond Layer 3 of the OSI model. DPI can identify and classify traffic based on a signature database that includes information extracted from the data part of a packet, allowing finer control than classification based only on header information. End points can utilize encryption and obfuscation techniques to evade DPI actions in many cases.
A classified packet may be redirected, marked/tagged (see quality of service), blocked, rate limited, and of course, reported to a reporting agent in the network. In this way, HTTP errors of different classifications may be identified and forwarded for analysis. Many DPI devices can identify packet flows (rather than packet-by-packet analysis), allowing control actions based on accumulated flow information.[3]
2. At the Enterprise Level
Initially security at the enterprise level was just a perimeter discipline, with a dominant philosophy of keeping unauthorized users out, and shielding authorized users from the outside world. The most frequently used tool for accomplishing this has been a stateful firewall. It can permit fine-grained control of access from the outside world to pre-defined destinations on the internal network, as well as permitting access back to other hosts only if a request to the outside world has been made previously.[4]
Vulnerabilities exist at network layers, however, that are not visible to a stateful firewall. Also, an increase in the use of laptops in enterprise makes it more difficult to prevent threats such as viruses, worms, and spyware from penetrating the corporate network, as many users will connect the laptop to less-secure networks such as home broadband connections or wireless networks in public locations. Firewalls also do not distinguish between permitted and forbidden uses of legitimately-accessed applications. DPI enables IT administrators and security officials to set policies and enforce them at all layers, including the application and user layer to help combat those threats.[5][6]
Deep Packet Inspection is able to detect a few kinds of buffer overflow attacks.
DPI may be used by enterprise for Data Leak Prevention (DLP). When an e-mail user tries to send a protected file, the user may be given information on how to get the proper clearance to send the file.[7][clarification needed]
3. At Network/Internet Service Providers
In addition to using DPI to secure their internal networks, Internet service providers also apply it on the public networks provided to customers. Common uses of DPI by ISPs are lawful intercept, policy definition and enforcement, targeted advertising, quality of service, offering tiered services, and copyright enforcement.
3.1. Lawful Interception
Service providers are required by almost all governments worldwide to enable lawful intercept capabilities. Decades ago in a legacy telephone environment, this was met by creating a traffic access point (TAP) using an intercepting proxy server that connects to the government's surveillance equipment. The acquisition component of this functionality may be provided in many ways, including DPI, DPI-enabled products that are "LI or CALEA-compliant" can be used – when directed by a court order – to access a user's datastream.[8]
3.2. Policy Definition and Enforcement
Service providers obligated by the service-level agreement with their customers to provide a certain level of service and at the same time, enforce an acceptable use policy, may make use of DPI to implement certain policies that cover copyright infringements, illegal materials, and unfair use of bandwidth. In some countries the ISPs are required to perform filtering, depending on the country's laws. DPI allows service providers to "readily know the packets of information you are receiving online—from e-mail, to websites, to sharing of music, video and software downloads".[9] Policies can be defined that allow or disallow connection to or from an IP address, certain protocols, or even heuristics that identify a certain application or behavior.
3.3. Targeted Advertising
Because ISPs route the traffic of all of their customers, they are able to monitor web-browsing habits in a very detailed way allowing them to gain information about their customers' interests, which can be used by companies specializing in targeted advertising. At least 100,000 United States customers are tracked this way, and as many as 10% of U.S. customers have been tracked in this way.[10] Technology providers include NebuAd, Front Porch, and Phorm. U.S. ISPs monitoring their customers include Knology[11] and Wide Open West. In addition, the United Kingdom ISP British Telecom has admitted testing solutions from Phorm without their customers' knowledge or consent.[10]
3.4. Quality of Service
DPI can be used against net neutrality.
Applications such as peer-to-peer (P2P) traffic present increasing problems for broadband service providers. Typically, P2P traffic is used by applications that do file sharing. These may be any kind of files (i.e. documents, music, videos, or applications). Due to the frequently large size of media files being transferred, P2P drives increasing traffic loads, requiring additional network capacity. Service providers say a minority of users generate large quantities of P2P traffic and degrade performance for the majority of broadband subscribers using applications such as e-mail or Web browsing which use less bandwidth.[12] Poor network performance increases customer dissatisfaction and leads to a decline in service revenues.
DPI allows the operators to oversell their available bandwidth while ensuring equitable bandwidth distribution to all users by preventing network congestion. Additionally, a higher priority can be allocated to a VoIP or video conferencing call which requires low latency versus web browsing which does not.[13] This is the approach that service providers use to dynamically allocate bandwidth according to traffic that is passing through their networks.
3.5. Tiered Services
Mobile and broadband service providers use DPI as a means to implement tiered service plans, to differentiate "walled garden" services from "value added", "all-you-can-eat" and "one-size-fits-all" data services.[14] By being able to charge for a "walled garden", per application, per service, or "all-you-can-eat" rather than a "one-size-fits-all" package, the operator can tailor his offering to the individual subscriber and increase their average revenue per user (ARPU). A policy is created per user or user group, and the DPI system in turn enforces that policy, allowing the user access to different services and applications.
3.6. Copyright Enforcement
ISPs are sometimes requested by copyright owners or required by courts or official policy to help enforce copyrights. In 2006, one of Denmark's largest ISPs, Tele2, was given a court injunction and told it must block its customers from accessing The Pirate Bay, a launching point for BitTorrent.[15]
Instead of prosecuting file sharers one at a time,[16] the International Federation of the Phonographic Industry (IFPI) and the big four record labels EMI, Sony BMG, Universal Music, and Warner Music have sued ISPs such as Eircom for not doing enough about protecting their copyrights.[17] The IFPI wants ISPs to filter traffic to remove illicitly uploaded and downloaded copyrighted material from their network, despite European directive 2000/31/EC clearly stating that ISPs may not be put under a general obligation to monitor the information they transmit, and directive 2002/58/EC granting European citizens a right to privacy of communications.
The Motion Picture Association of America (MPAA) which enforces movie copyrights, has taken the position with the Federal Communications Commission (FCC) that network neutrality could hurt anti-piracy techniques such as deep packet inspection and other forms of filtering.[18]
3.7. Statistics
DPI allows ISPs to gather statistical information about use patterns by user group. For instance, it might be of interest whether users with a 2Mbit connection use the network in a dissimilar manner to users with a 5Mbit connection. Access to trend data also helps network planning.[clarification needed]
4. By Governments
In addition to using DPI for the security of their own networks, governments in North America, Europe, and Asia use DPI for various purposes such as surveillance and censorship. Many of these programs are classified.[19]
4.1. China
The Chinese government uses deep packet inspection to monitor and censor network traffic and content that it claims is harmful to Chinese citizens or state interests. This material includes pornography, information on religion, and political dissent.[20] Chinese network ISPs use DPI to see if there is any sensitive keyword going through their network. If so, the connection will be cut. People within China often find themselves blocked while accessing Web sites containing content related to Taiwanese and Tibetan independence, Falun Gong, the Dalai Lama, the Tiananmen Square protests and massacre of 1989, political parties that oppose that of the ruling Communist party, or a variety of anti-Communist movements[21] as those materials were signed as DPI sensitive keywords already. China previously blocked all VoIP traffic in and out of their country[22] but many available VoIP applications now function in China. Voice traffic in Skype is unaffected, although text messages are subject to filtering, and messages containing sensitive material, such as curse-words, are simply not delivered, with no notification provided to either participant in the conversation. China also blocks visual media sites such as YouTube.com and various photography and blogging sites.[23]
| Alexa rank | Website | Domain | URL | Category | Primary language |
|---|---|---|---|---|---|
| 6 | Wikipedia | wikipedia.org | www.wikipedia.org | Censorship-free encyclopedia | English |
| 1 | google.com | www.google.com | Worldwide Internet search engine | English | |
| 1 | Google Encrypted | google.com | encrypted.google.com | Search | English |
| 2 | facebook.com | www.facebook.com | Social network | English | |
| 3 | YouTube | youtube.com | www.youtube.com | Video | English |
| 557 | Jehovah's Witnesses | jw.org | www.jw.org | Spiritual, Christianity | Multilingual |
| 24693 | OpenVPN | openvpn.net | www.openvpn.net | Avoidance of political internet censorship | English |
| 33553 | StrongVPN | strongvpn.com | www.strongvpn.com | Avoidance of political internet censorship | English |
| 78873 | Falun Dafa | falundafa.org | www.falundafa.org | Spiritual | English |
| 1413995 | VPN Coupons | vpncoupons.com | www.vpncoupons.com | Avoidance of political internet censorship | English |
| 2761652 | ElephantVPN | elephantvpn.com | www.elephantvpn.com | Avoidance of political internet censorship | English |
4.2. Egypt
Since 2015, Egypt reportedly started to join the list which was constantly being denied by the Egyptian National Telecom Regulatory Authority (NTRA) officials. However, it came to news when the country decided to block the encrypted messaging app Signal as announced by the application's developer.[24]
In April 2017, all VoIP applications including FaceTime, Facebook Messenger, Viber, WhatsApp calls and Skype have been all blocked in the country.[25]
As of 2022, FaceTime, Facebook Messenger are unblocked.
4.3. Indonesia
The Indonesian Government via Telkom Indonesia,[26] supported by Cisco Meraki DPI technology, do country wide surveillance, and map it into SSN/NIK(Nomor Induk Kependudukan) of its citizens that registered to the ISP. They use this for filtering porn, hates speech, and reducing tension in West Papua.[27] In most of the case, these data always released to dark web by sub contractor that works for the gov. Indonesian Gov plan to scale up the surveillance to next level until 2030.[28]
4.4. Iran
The Iranian government purchased a system, reportedly for deep packet inspection, in 2008 from Nokia Siemens Networks (NSN) (a joint venture Siemens AG, the German conglomerate, and Nokia Corp., the Finnish cell telephone company), now NSN is Nokia Solutions and Networks, according to a report in the Wall Street Journal in June, 2009, quoting NSN spokesperson Ben Roome.[29] According to unnamed experts cited in the article, the system "enables authorities to not only block communication but to monitor it to gather information about individuals, as well as alter it for disinformation purposes".
The system was purchased by the Telecommunication Infrastructure Co., part of the Iranian government's telecom monopoly. According to the Journal, NSN "provided equipment to Iran last year under the internationally recognized concept of 'lawful intercept,' said Mr. Roome. That relates to intercepting data for the purposes of combating terrorism, child pornography, drug trafficking, and other criminal activities carried out online, a capability that most if not all telecom companies have, he said.... The monitoring center that Nokia Siemens Networks sold to Iran was described in a company brochure as allowing 'the monitoring and interception of all types of voice and data communication on all networks.' The joint venture exited the business that included the monitoring equipment, what it called 'intelligence solution,' at the end of March, by selling it to Perusa[30] Partners Fund 1 LP, a Munich-based investment firm, Mr. Roome said. He said the company determined it was no longer part of its core business.
The NSN system followed on purchases by Iran from Secure Computing Corp. earlier in the decade.[31]
Questions have been raised about the reporting reliability of the Journal report by David Isenberg, an independent Washington, D.C.-based analyst and Cato Institute Adjunct Scholar, specifically saying that Mr. Roome is denying the quotes attributed to him and that he, Isenberg, also had similar complaints with one of the same Journal reporters in an earlier story.[32] NSN has issued the following denial: NSN "has not provided any deep packet inspection, web censorship or Internet filtering capability to Iran".[33] A concurrent article in The New York Times stated the NSN sale had been covered in a "spate of news reports in April [2009], including The Washington Times," and reviewed censorship of the Internet and other media in the country, but did not mention DPI.[34]
According to Walid Al-Saqaf, the developer of the internet censorship circumventor Alkasir, Iran was using deep packet inspection in February 2012, bringing internet speeds in the entire country to a near standstill. This briefly eliminated access to tools such as Tor and Alkasir.[35]
4.5. Malaysia
The incumbent Malaysian government, headed by Barisan Nasional, was said to be using DPI against a political opponent during the run-up to the 13th general elections held on 5 May 2013.
The purpose of DPI, in this instance, was to block and/or hinder access to selected websites, e.g. Facebook accounts, blogs and news portals.[36][37]
4.6. Russian Federation
DPI is not yet mandated in Russia. Federal Law No.139 enforces blocking websites on the Russian Internet blacklist using IP filtering, but does not force ISPs into analyzing the data part of packets. Yet some ISPs still use different DPI solutions to implement blacklisting. For 2019, the governmental agency Roskomnadzor is planning a nationwide rollout of DPI after the pilot project in one of the country's regions, at an estimated cost of 20 billion roubles (US$300M).[38]
Some human rights activists consider Deep Packet inspection contrary to Article 23 of the Constitution of the Russian Federation, though a legal process to prove or refute that has never taken place.[39]
4.7. Singapore
The city state reportedly employs deep packet inspection of Internet traffic.[40]
4.8. Syria
The state reportedly employs deep packet inspection of Internet traffic, to analyze and block forbidden transit.
4.9. United States
FCC adopts Internet CALEA requirements: The FCC, pursuant to its mandate from the U.S. Congress, and in line with the policies of most countries worldwide, has required that all telecommunication providers, including Internet services, be capable of supporting the execution of a court order to provide real-time communication forensics of specified users. In 2006, the FCC adopted new Title 47, Subpart Z, rules requiring Internet Access Providers to meet these requirements. DPI was one of the platforms essential to meeting this requirement and has been deployed for this purpose throughout the U.S.
The National Security Agency (NSA), with cooperation from AT&T Inc., has used Deep Packet Inspection to make internet traffic surveillance, sorting, and forwarding more intelligent. The DPI is used to find which packets are carrying e-mail or a Voice over Internet Protocol (VoIP) telephone call.[41] Traffic associated with AT&T's Common Backbone was "split" between two fibers, dividing the signal so that 50 percent of the signal strength went to each output fiber. One of the output fibers was diverted to a secure room; the other carried communications on to AT&T's switching equipment. The secure room contained Narus traffic analyzers and logic servers; Narus states that such devices are capable of real-time data collection (recording data for consideration) and capture at 10 gigabits per second. Certain traffic was selected and sent over a dedicated line to a "central location" for analysis. According to an affidavit by expert witness J. Scott Marcus, a former senior advisor for Internet Technology at the US Federal Communications Commission, the diverted traffic "represented all, or substantially all, of AT&T’s peering traffic in the San Francisco Bay area", and thus, "the designers of the…configuration made no attempt, in terms of location or position of the fiber split, to exclude data sources comprised primarily of domestic data".[42] Narus's Semantic Traffic Analyzer software, which runs on IBM or Dell Linux servers using DPI, sorts through IP traffic at 10Gbit/s to pick out specific messages based on a targeted e-mail address, IP address or, in the case of VoIP, telephone number.[43] President George W. Bush and Attorney General Alberto R. Gonzales have asserted that they believe the president has the authority to order secret intercepts of telephone and e-mail exchanges between people inside the United States and their contacts abroad without obtaining a FISA warrant.[44]
The Defense Information Systems Agency has developed a sensor platform that uses Deep Packet Inspection.[45]
4.10. Vietnam
Vietnam launched its network security center and required ISPs to upgrade their hardware systems to use deep packet inspection to block Internet traffic.[46][47]
5. Net Neutrality
People and organizations concerned about privacy or network neutrality find inspection of the content layers of the Internet protocol to be offensive,[8] saying for example, "the 'Net was built on open access and non-discrimination of packets!"[48] Critics of network neutrality rules, meanwhile, call them "a solution in search of a problem" and say that net neutrality rules would reduce incentives to upgrade networks and launch next-generation network services.[49]
Deep packet inspection is considered by many to undermine the infrastructure of the internet.[50]
6. Encryption and Tunneling Subverting DPI
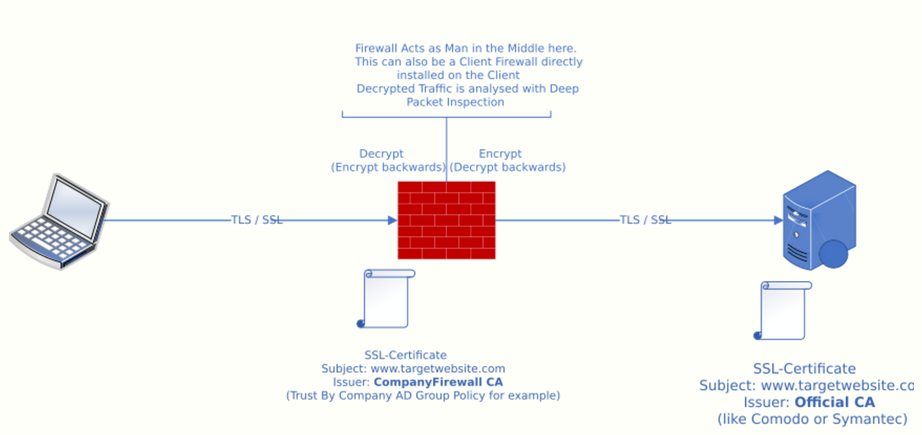
With increased use of HTTPS and privacy tunneling using VPNs, the effectiveness of DPI is coming into question.[51] In response, many web application firewalls now offer HTTPS inspection, where they decrypt HTTPS traffic to analyse it.[52] The WAF can either terminate the encryption, so the connection between WAF and client browser uses plain HTTP, or re-encrypt the data using its own HTTPS certificate, which must be distributed to clients beforehand.[53] The techniques used in HTTPS/SSL Inspection (also known as HTTPS/SSL Interception) are the same used by man-in-the-middle (MiTM) attacks[54]
It works like this:
- Client wants to connect to https://www.targetwebsite.com
- Traffic goes through Firewall or Security Product
- Firewall works as transparent Proxy
- Firewall Creates SSL Certificate signed by its own "CompanyFirewall CA"
- Firewall presents this "CompanyFirewall CA" Signed Certificate to Client (not the targetwebsite.com Certificate)
- At the same time the Firewall on its own connects to https://www.targetwebsite.com
- targetwebsite.com Presents its Officially Signed Certificate (Signed by a Trusted CA)
- Firewall checks Certificate Trust chain on its own
- Firewall now works as Man-in-the-middle.
- Traffic from Client will be decrypted (with Key Exchange Information from Client), analysed (for harmful traffic, policy violation or viruses), encrypted (with Key Exchange Information from targetwebsite.com) and sent to targetwebsite.com
- Traffic from targetwebsite.com will also be decrypted (with Key Exchange Information from targetwebsite.com), analysed (like above), encrypted (with Key Exchange Information from Client) and sent to Client.
- The Firewall Product can read all information exchanged between SSL-Client and SSL-Server (targetwebsite.com)
This can be done with any TLS-Terminated connection (not only HTTPS) as long as the firewall product can modify the TrustStore of the SSL-Client
7. Infrastructure Security
Traditionally the mantra which has served ISP well has been to only operate at layer 4 and below of the OSI model. This is because simply deciding where packets go and routing them is comparably very easy to handle securely. This traditional model still allows ISPs to accomplish required tasks safely such as restricting bandwidth depending on the amount of bandwidth that is used (layer 4 and below) rather than per protocol or application type (layer 7). There is a very strong and often ignored argument that ISP action above layer 4 of the OSI model provides what are known in the security community as 'stepping stones' or platforms to conduct man in the middle attacks from. This problem is exacerbated by ISP's often choosing cheaper hardware with poor security track records for the very difficult and arguably impossible to secure task of Deep Packet Inspection.
OpenBSD's packet filter specifically avoids DPI for the very reason that it cannot be done securely with confidence.
This means that DPI dependent security services such as TalkTalk's former HomeSafe implementation are actually trading the security of a few (protectable and often already protectable in many more effective ways) at a cost of decreased security for all where users also have a far less possibility of mitigating the risk. The HomeSafe service in particular is opt in for blocking but its DPI cannot be opted out of, even for business users.[55]
8. Software
nDPI (a fork from OpenDPI[56] which is EoL by the developers of ntop)[57][58] is the open source version for non-obfuscated protocols. PACE, another such engine, includes obfuscated and encrypted protocols, which are the types associated with Skype or encrypted BitTorrent.[59] As OpenDPI is no longer maintained, an OpenDPI-fork named nDPI[60] has been created, actively maintained and extended with new protocols including Skype, Webex, Citrix and many others.
L7-Filter is a classifier for Linux's Netfilter that identifies packets based on application layer data.[61] It can classify packets such as Kazaa, HTTP, Jabber, Citrix, Bittorrent, FTP, Gnucleus, eDonkey2000, and others. It classifies streaming, mailing, P2P, VoIP, protocols, and gaming applications. The software has been retired and replaced by the open source Netify DPI Engine.[62]
Hippie (Hi-Performance Protocol Identification Engine) is an open source project which was developed as Linux kernel module.[63] It was developed by Josh Ballard. It supports both DPI as well as firewall functionality.[64]
SPID (Statistical Protocol IDentification) project is based on statistical analysis of network flows to identify application traffic.[65] The SPID algorithm can detect the application layer protocol (layer 7) by signatures (a sequence of bytes at a particular offset in the handshake), by analyzing flow information (packet sizes, etc.) and payload statistics (how frequently the byte value occurs in order to measure entropy) from pcap files. It is just a proof of concept application and currently supports approximately 15 application/protocols such as eDonkey Obfuscation traffic, Skype UDP and TCP, BitTorrent, IMAP, IRC, MSN, and others.
Tstat (TCP STatistic and Analysis Tool) provides insight into traffic patterns and gives details and statistics for numerous applications and protocols.[66]
Libprotoident introduces Lightweight Packet Inspection (LPI), which examines only the first four bytes of payload in each direction. That allows to minimize privacy concerns, while decreasing the disk space needed to store the packet traces necessary for the classification. Libprotoident supports over 200 different protocols and the classification is based on a combined approach using payload pattern matching, payload size, port numbers, and IP matching.[67]
A France company called Amesys, designed and sold an intrusive and massive internet monitoring system Eagle to Muammar Gaddafi.[68]
8.1. Comparison
A comprehensive comparison of various network traffic classifiers, which depend on Deep Packet Inspection (PACE, OpenDPI, 4 different configurations of L7-filter, NDPI, Libprotoident, and Cisco NBAR), is shown in the Independent Comparison of Popular DPI Tools for Traffic Classification.[69]
9. Hardware
There is a greater emphasis being placed on deep packet inspection - this comes in light[clarification needed] after the rejection of both the SOPA and PIPA bills. Many current DPI methods are slow and costly, especially for high bandwidth applications. More efficient methods of DPI are being developed. Specialized routers are now able to perform DPI; routers armed with a dictionary of programs will help identify the purposes behind the LAN and internet traffic they are routing. Cisco Systems is now on their second iteration of DPI enabled routers, with their announcement of the CISCO ISR G2 router.[70]
The content is sourced from: https://handwiki.org/wiki/Social:Deep_packet_inspection
References
- Ido Dubrawsky (2003-07-29). "Firewall Evolution - Deep Packet Inspection". http://www.securityfocus.com/infocus/1716.
- Khachatryan, Artavazd (2020-02-01). "100Gbps Network DPI, Content Extraction on Xilinx's FPGA" (in en). https://medium.com/grovf/100gbps-network-dpi-content-extraction-on-xilinxs-fpga-2996d661042a.
- Moscola, James, et al. "Implementation of a content-scanning module for an internet firewall." Field-Programmable Custom Computing Machines, 2003. FCCM 2003. 11th Annual IEEE Symposium on. IEEE, 2003.
- Elan Amir (2007-10-29). "The Case for Deep Packet Inspection". http://www.itbusinessedge.com/item/?ci=35275.
- Noferesti, Morteza; Jalili, Rasool (2020-01-15). "ACoPE: An adaptive semi-supervised learning approach for complex-policy enforcement in high-bandwidth networks" (in en). Computer Networks 166: 106943. doi:10.1016/j.comnet.2019.106943. ISSN 1389-1286. https://www.sciencedirect.com/science/article/abs/pii/S1389128619304074.
- "firewall". https://searchsecurity.techtarget.com/definition/firewall.
- Tahboub, Radwan; Saleh, Yousef (January 2014). "Data Leakage/Loss Prevention Systems (DLP)". 2014 World Congress on Computer Applications and Information Systems (WCCAIS): 1–6. doi:10.1109/WCCAIS.2014.6916624. https://ieeexplore.ieee.org/document/6916624.
- Nate Anderson (2007-07-25). "Deep Packet Inspection meets 'Net neutrality, CALEA". https://arstechnica.com/articles/culture/Deep-packet-inspection-meets-net-neutrality.ars.
- Jeff Chester (2006-02-01). "The End of the Internet?". http://www.thenation.com/doc/20060213/chester.
- Peter Whoriskey (2008-04-04). "Every Click You Make: Internet Providers Quietly Test Expanded Tracking of Web Use to Target Advertising". The Washington Post. https://www.washingtonpost.com/wp-dyn/content/article/2008/04/03/AR2008040304052.html.
- "Charter Communications: Enhanced Online Experience". http://connect.charter.com/landing/op1.html.
- "Deep Packet Inspection: Taming the P2P Traffic Beast". http://www.lightreading.com/insider/details.asp?sku_id=1221&skuitem_itemid=957.
- Matt Hamblen (2007-09-17). "Ball State uses Deep Packet Inspection to ensure videoconferencing performance". http://www.computerworld.com/article/2541004/networking/ball-state-uses-deep-packet-inspection-to-ensure-videoconferencing-performance.html.
- "Allot Deploys DPI Solution at Two Tier 1 Mobile Operators to Deliver Value- Added and Tiered Service Packages". 2008-02-05. http://news.moneycentral.msn.com/ticker/article.aspx?Feed=PR&Date=20080205&ID=8139811&Symbol=ALLT.
- Jeremy Kirk (2008-02-13). "Danish ISP prepares to fight Pirate Bay injunction". http://www.infoworld.com/article/08/02/13/Danish-ISP-prepares-to-fight-Pirate-Bay-injunction_1.html.
- Matthew Clark (2005-07-05). "Eircom and BT won't oppose music firms". http://www.enn.ie/frontpage/news-9617239.html.
- Eric Bangeman (2008-03-11). ""Year of filters" turning into year of lawsuits against ISPs". https://arstechnica.com/news.ars/post/20080311-year-of-filters-turning-into-year-of-lawsuits-against-isps.html.
- Anne Broach (2007-07-19). "MPAA: Net neutrality could hurt antipiracy tech". http://www.news.com/8301-10784_3-9746938-7.html.
- Carolyn Duffy Marsan (2007-06-27). "OEM provider Bivio targets government market". http://www.networkworld.com/newsletters/isp/2007/0625isp1.html.
- "The Great Firewall of China". 2006-01-12. http://www.businessweek.com/technology/content/jan2006/tc20060112_434051.htm.
- "Internet Filtering in China in 2004-2005: A Country Study". http://www.opennetinitiative.net/studies/china.
- Guy Kewney, China blocks Skype, VoIP, The Register, 2005 https://www.theregister.co.uk/2005/09/12/china_blocks_skype/
- "China Blocks YouTube, Restores Flickr and Blogspot". 2007-10-18. http://www.pcworld.com/article/id,138599-c,sites/article.html.
- "Egypt has blocked encrypted messaging app Signal". https://www.engadget.com/2016/12/20/egypt-blocks-signal.
- "تعاني من مشكلة توقُّف خدمات الاتصال عبر الإنترنت في مصر…هذه هي أسباب الأزمة". http://www.huffpostarabi.com/2017/04/21/story_n_16149218.html.
- Thompson, Nik; McGill, Tanya; Khristianto, Daniel Vero (1 January 2021). "Public Acceptance of Internet Censorship in Indonesia". ACIS 2021 Proceedings. https://aisel.aisnet.org/acis2021/22. Retrieved 21 August 2022.
- Wildana, Faiq (30 October 2021). "An Explorative Study on Social Media Blocking in Indonesia" (in en). The Journal of Society and Media 5 (2): 456–484. doi:10.26740/jsm.v5n2.p456-484. ISSN 2580-1341. https://doi.org/10.26740/jsm.v5n2.p456-484. Retrieved 21 August 2022.
- Paterson, Thomas (4 May 2019). "Indonesian cyberspace expansion: a double-edged sword". Journal of Cyber Policy 4 (2): 216–234. doi:10.1080/23738871.2019.1627476. ISSN 2373-8871. https://doi.org/10.1080/23738871.2019.1627476. Retrieved 21 August 2022.
- Christensen, Christian. "Iran: Networked dissent". Le Monde Diplomatique 1.
- "Perusa :: Who we are". perusa-partners.de. http://www.perusa-partners.de/english/who_we_are.php.
- "Iran's Web Spying Aided By Western Technology" by Christopher Rhoads in New York and Loretta Chao in Beijing, The Wall Street Journal, June 22, 2009. Retrieved 6/22/09. https://www.wsj.com/articles/SB124562668777335653
- "Questions about WSJ story on Net Management in Iran" by David S. Isenberg, isen.blog, June 23, 2009. Retrieved 6/22/09. http://www.isen.com/blog/2009/06/questions-about-wsj-story-on-net.html
- "Provision of Lawful Intercept capability in Iran" Company press release. June 22, 2009. Retrieved 6/22/09. http://www.nokiasiemensnetworks.com/global/Press/Press+releases/news-archive/Provision+of+Lawful+Intercept+capability+in+Iran.htm
- "Web Pries Lid of Iranian Censorship" by Brian Stelter and Brad Stone, The New York Times, June 22, 2009. Retrieved June 23, 2009. https://www.nytimes.com/2009/06/23/world/middleeast/23censor.html?_r=1&hp
- February 14, 2012 "Breaking and Bending Censorship with Walid Al-Saqaf" , an Interview with Arseh Sevom. Last viewed February 23, 2012. http://www.arsehsevom.net/2012/02/breaking-and-bending-censorship-with-walid-al-saqaf/
- Goh Kheng Teong (2013-05-20). "DAP complains to MCMC over blockade on its websites, videos, FB, social media networks". http://www.malaysia-chronicle.com/index.php?option=com_k2&view=item&id=102522:dap-complains-to-mcmc-over-blockade-on-its-websites-videos-fb-social-media-networks&Itemid=2.
- "In Malaysia, online election battles take a nasty turn". 2013-05-04. http://www.themalaysianinsider.com/malaysia/article/in-malaysia-online-election-battles-take-a-nasty-turn.
- "Roskomnadzor to deploy new blocking technology (in Russian)". BBC News Русская Служба. 18 December 2018. https://www.bbc.com/russian/features-46596673.
- Constitution of the Russian Federation (English translation) http://www.government.ru/eng/gov/base/54.html
- "Deep packet inspection rears it ugly head". https://majid.info/blog/telco-snooping.
- J. I. Nelson (2006-09-26). "How the NSA warrantless wiretap system works". http://www.nerdylorrin.net/jerry/politics/Warrantless/WarrantlessFACTS.html.
- Bellovin, Steven M.; Matt Blaze; Whitfield Diffie; Susan Landau; Peter G. Neumann; Jennifer Rexford (January–February 2008). "Risking Communications Security: Potential Hazards of the Protect America Act". IEEE Security and Privacy (IEEE Computer Society) 6 (1): 24–33. doi:10.1109/MSP.2008.17. http://www.crypto.com/papers/paa-ieee.pdf. Retrieved 2008-03-03.
- Robert Poe (2006-05-17). "The Ultimate Net Monitoring Tool". Wired. https://www.wired.com/science/discoveries/news/2006/05/70914. Retrieved 2008-03-03.
- Carol D. Leonnig (2007-01-07). "Report Rebuts Bush on Spying - Domestic Action's Legality Challenged". The Washington Post. https://www.washingtonpost.com/wp-dyn/content/article/2006/01/06/AR2006010601772.html.
- Cheryl Gerber (2008-09-18). "Deep Security: DISA Beefs Up Security with Deep Packet Inspection of IP Transmissions". https://www.dpacket.org/articles/deep-security-disa-beefs-security-deep-packet-inpection-ip-transmissions.
- "Ra mắt Nền tảng cung cấp dịch vụ Trung tâm điều hành an toàn, an ninh mạng đáp ứng yêu cầu kết nối, chia sẻ thông tin". https://www.mic.gov.vn/Pages/TinTuc/143083/Ra-mat-Nen-tang-cung-cap-dich-vu-Trung-tam-dieu-hanh-an-toan--an-ninh-mang-dap-ung-yeu-cau-ket-noi--chia-se-thong-tin.html.
- https://khonggianmang.vn/
- Genny Pershing. "Network Neutrality: Historic Neutrality". http://www.cybertelecom.org/ci/neutral.htm#his.
- Genny Pershing. "Network Neutrality: Insufficient Harm". http://www.cybertelecom.org/ci/neutral.htm#ins.
- Fuchs, Christian. "Implications of Deep Packet Inspection (DPI) Internet Surveillance for Society". http://www.projectpact.eu/documents-1/%231_Privacy_and_Security_Research_Paper_Series.pdf.
- Sherry Justine, Chang Lan, Raluca Ada Popa, and Sylvia Ratnasamy, Blindbox: Deep packet inspection over encrypted traffic, ACM SIGCOMM Computer Communication Review, 2015 http://dl.acm.org/citation.cfm?id=2787502
- "Best Practices - HTTPS Inspection". 2017-07-21. https://supportcenter.checkpoint.com/supportcenter/portal?eventSubmit_doGoviewsolutiondetails=&solutionid=sk108202. "With HTTPS Inspection, the Security Gateway can inspect the traffic that is encrypted by HTTPS. The Security Gateway uses certificates and becomes an intermediary between the client computer and the secure web site. All data is kept private in HTTPS Inspection logs. Only administrators with HTTPS Inspection permissions can see all the fields in a log."
- "SecureSphere WAF Specifications". https://www.imperva.com/Products/WebApplicationFirewall-WAF. "SecureSphere WAF Specifications […] HTTPS/SSL Inspection: Passive decryption or termination"
- "What is SSL Inspection? How does it work? - The SSL Store™" (in en-US). 2018-08-03. https://www.thesslstore.com/blog/ssl-inspection.
- Raney, Steve (2004). "Suburban silver bullet: Personal rapid transit shuttle and wireless commuting assistant with cellular location tracking". Transportation Research Record 1872: 62–70. doi:10.3141/1872-08. https://dx.doi.org/10.3141%2F1872-08
- "OpenDPI.org". http://www.opendpi.org.
- ntop (2 February 2012). "nDPI - Open and Extensible LGPLv3 Deep Packet Inspection Library". http://www.ntop.org/products/ndpi.
- Fichtner, Franco. "Bye bye OpenDPI". http://lastsummer.de/bye-bye-opendpi.
- "Deep packet inspection engine goes open source". Ars Technica. 9 September 2009. https://arstechnica.com/open-source/news/2009/09/deep-packet-inspection-engine-goes-open-source.ars.
- "nDPI". ntop. 2 February 2012. http://www.ntop.org/products/ndpi.
- "Application Layer Packet Classifier for Linux". sourceforge.net. http://l7-filter.sourceforge.net.
- "A fond farewell to l7-filter". https://l7-filter.clearfoundation.com.
- "SourceForge.net Repository - [hippie Index of"]. sourceforge.net. http://hippie.cvs.sourceforge.net/viewvc/hippie.
- "HiPPIE - Free download". linux112.com. http://www.linux112.com/hippie-p313520.html.
- hjelmvik. "SPID Statistical Protocol IDentification". SourceForge. http://sourceforge.net/projects/spid.
- Tstat project home http://tstat.tlc.polito.it/index.shtml
- "WAND Network Research Group: libprotoident". wand.net.nz. http://research.wand.net.nz/software/libprotoident.php.
- Spy-Gear Business to Be Sold - Amesys to Sell Business That Provided Surveillance Technology Used by Gadhafi, the Wall Street Journal, German edition, March 9, 2012. http://www.wallstreetjournal.de/article/SB10001424052970203961204577269391401776590.html
- Tomasz Bujlow; Valentín Carela-Español; Pere Barlet-Ros (2015). "Independent Comparison of Popular DPI Tools for Traffic Classification". Computer Networks (In press (Computer Networks)) 76: 75–89. doi:10.1016/j.comnet.2014.11.001. http://tomasz.bujlow.com/publications/2014_journal_elsevier_comnet_independent_comparison.htm. Retrieved 2014-11-10.
- Application Visibility and Control. (n.d.). In Cisco Systems http://www.cisco.com/en/US/prod/routers/application_visibility_control.html
