Chaos is the characteristic of a system whose current state is guaranteed to be highly sensitive to the previous state (spatial chaos), the initial conditions (temporal chaos), or both (spatio-temporal chaos). Such a sensitivity makes the output or the behavior of a chaotic system difficult to predict. Chaos theory justifies and formulates the apparent disorder of chaotic systems on the basis of orderly patterns, structured feedback loops, iterative repetitions, self-organization, self-similarity, fractals, etc. Chaotic maps, attractors, and sequences all refer to the mathematical structures used for this formulation. Chaotic systems, maps, attractors, and sequences have been of great interest to the research community in recent years [12,13]. They have been used for security purposes in a broad variety of applications ranging from smart grids [14] to communication systems [15]. Especially, chaotic encryption has been used for encrypting a variety of content types in addition to images [1,2].
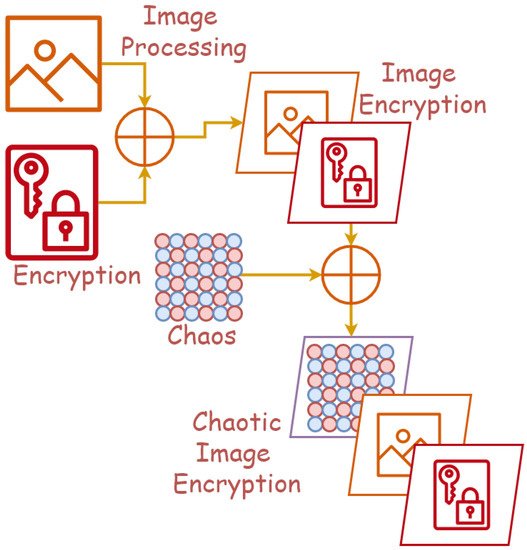
- image encryption
- chaos
- chaotic encryption
- chaotic image encryption
1. Introduction
2. State-of-the-Art
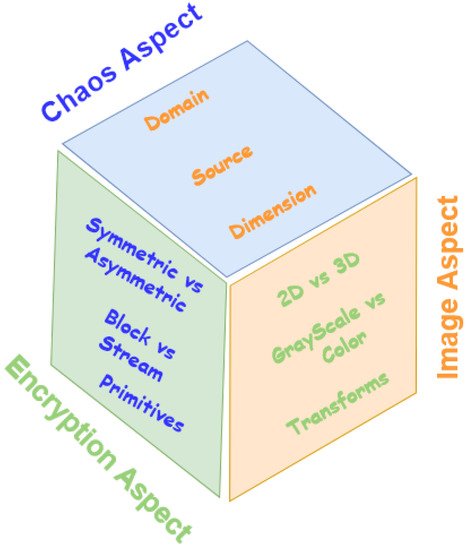
2.1. State-of-the-Art in Chaos Aspect
2.1.1. Chaos Domains
Spatial Chaos
Temporal Chaos
Spatiotemporal Chaos
2.1.2. Chaos Sources
Mathematical Sources
-
Chaotic systems and mapsThese are functions originally designed for creating chaos. Chaotic systems and maps play a critical role in chaotic image encryption. To mention a few, one may refer to the following:
- –
-
Fractional-order chaotic systemFractional calculus goes back more than 300 years, with modern studies focusing on systems such as the fractional-order Chen, Lorenz, and Liu systems [42]. A novel switching fractional-order chaos system was proposed by Hou [42] and utilizes controlling switches to switch between its sub-systems and achieve a strong chaos source for applying the exclusive Or (XOR) operation against the plaintext image.Another algorithm utilizing fractional-order systems was proposed by Wei [43], which opts to use a more standard third-order fractional system, as well as a novel Josephus scrambling algorithm and circular diffusion to achieve desirable encryption properties and resilience against common attacks.
- –
-
Arnold cat mapArnold mapping is a well-know transposition chaotic map that, in the context of cryptography, was used by Ranimol and Gopakumar [44], as well as Zhang et al. [45] to provide a method of permutating and de-correlating adjacent pixels in their proposed encryption algorithms. Both algorithms were proven to exhibit a large keyspace with high key sensitivity and be capable of resisting common attacks such as brute force, entropy, CPT, and KPT.
- –
-
Coupled map latticeA Coupled Map Lattice (CML) is a form of spatiotemporal chaos map efficient for random number stream generation. In one use case, Wu [46] proposed a novel implementation of the CML to create encryption streams dependent not only on initial values, but also on intermediate cipher images by using said ciphertexts to modify the CML parameters. This adds a layer of plaintext dependency, which aids in the defense against several attacks.
- –
-
Lorenz mapA Lorenz system is a type of differential equation that is highly susceptible to initial conditions. Jiang and Fu [47] proposed an image encryption procedure in which the key is composed of the three inputs to a 3D Lorenz system and utilizes the chaotic nature of said system to provide strong security.
- –
-
Logistic mapA logistic map is a relativity simplistic mathematical mapping function, which when influenced by particular control values, acts chaotically. An algorithm proposed by Sharma and Bhargava [48] utilizes a two-step interactive logistic map, where the next input is dependent on the previous two outputs, as a source of chaos. Similar work was performed by Li-Hong et al. [49], where they used a more standard logistic map and paired it with a hyper-chaos system to improve key generation effectiveness. Likewise, Mu and Lui [50] also found success utilizing the logistic map for key generation.
- –
-
Tent mapWu et al. [51] proposed an image encryption algorithm using the CTM, and the rectangular transform was later analyzed by Zhu et al. [52] and improved upon to better protect against plaintext attacks such as CPT and KPT. The Chaotic Tent Map (CTM) is a mapping function that, when configured with control values in a particular range, behaves chaotically.
- –
-
Lotka–VolterraA Lotka–Volterra chaotic system is a third-order differential equation in a similar family to other systems such as Lorenz, Rossler, Shua, and Chen. In a particular case study by Zahir et al. [53], an encryption procedure was proposed that utilizes the Lotka–Volterra chaotic system to aid in the creation of Substitution boxes (S-boxes) with strong confusion properties. The resulting S-boxes were found to satisfy the five criteria (bijective, non-linearity, strict avalanche, bit independence, input/output XOR distribution) required for acceptable use in cryptographic algorithms.
- –
-
Henon mapThe Henon map was first discovered in 1978 and can be described as a 2D mapping function with two control parameters, which, when chosen strategically, enable the map to behave chaotically. Tresor et al. [54] proposed an image encryption algorithm utilizing Henon maps for shuffling the pixels of the image and 4D Qi hyper-chaos to generate keys for encryption. Experimental analysis of the algorithm demonstrates strong cryptographic properties and resistance against common attacks.
- –
-
Logistic-sine systemA Logistic-Sine System (LSS) is a discrete combination of the logistic and sine maps, both of which exhibit chaotic behavior under particular initial conditions. Zeng and Chen [55] referred to such a combination of the two maps as a compound chaotic map and utilized it in a novel encryption algorithm using XOR and modulus operations.Zhao et al. [56] investigated the inefficiencies with single chaos systems and proposed a novel algorithm utilizing LSS and cascade chaos to improve upon said inefficiencies. Experimental analysis through simulation has proven the new algorithm to be highly resilientIn another study, Lu et al. [57] conducted cryptanalysis on an existing algorithm based on multiple S-boxes, but were able to break it using CPT attacks. A new algorithm was proposed to improve upon the old one and involved only a single S-box constructed utilizing LSS. Further cryptanalysis of the new algorithm showed improvement over the original and was also quite fast.Variants of LSS have also been employed in encryption algorithms, such as a 2D Logistic Modulated Sine Coupling Logistic (LSMCL) map proposed by Zhu et al. [58], a Logistic Sine Modulation Map (LSIMM) proposed by Zhang et al. [59], and a 2D Logistic Adjusted Sine Chaotic Map (LASCM) proposed by Balakrishnan and Mubarak [60]. In all cases, theoretical analysis and simulations determined the algorithms to be both secure and efficient.
- –
-
Baker mapThe baker map is a bijective permutation function that operates on an MxM matrix by randomizing its cells according to a secret key and is well respected in the image encryption community. Elshamy et al. [61] utilized the baker map in an image encryption algorithm to improve upon a classic technique known as Double Random Phase Encoding (DRPE). The proposed algorithm uses the map to pre-process the image before applying DRPE, and experimental analysis showed significant increases in security as opposed to using DRPE alone.Another algorithm utilizing the baker map was proposed by Tong et al. [62], where high-dimensional dynamical multiple chaos was paired with the baker map to achieve a larger avalanche effect. Experimental results again showed significant increases in security when
- –
-
Tinkerbell mapKrishna [63] proposed an encryption algorithm utilizing Tinkerbell maps, a pair of chaotic functions, to inject strong pseudo-random numbers in multiple points during the encryption and decryption process. Differential and correlational analysis of the algorithm showed the proposed method to be highly efficient.
- –
-
Cubic mapA cubic map is a single-dimensional chaotic function that produces values on the interval [0, 1] and can be controlled by a single mapping parameter. Kavinmozhi et al. [64] proposed an encryption technique that employs a hybrid chaos source composed of the cubic and tent maps, as well as the Iterative Chaotic Map with Infinite Collapses (ICMICs). The resulting hybrid map is used with the XOR operation to achieve encryption, and an analysis of the algorithm showed that it is suitable for repeated use and is resilient against attacks.
- –
-
Gingerbreadman mapSavitri et al. [65] used the Gingerbreadman map, a 2D chaotic map, to generate encrypted keys for use with the well-known Cipher Block Chain (CBC) encryption algorithm. Using the map in this algorithm greatly improves CBC’s performance when applied to images, and a visual comparison demonstrated massive improvements.
- –
-
Tangent mapMoysis et al. [66] proposed a Random Number Generation (RNG) algorithm based on the usage of the mathematical hyperbolic tangent function. When the RNG algorithm was applied to image encryption, the resulting procedure demonstrated strong cryptography
- –
-
Multiple mapsMixing multiple mapping functions in image encryption algorithms can serve multiple purposes. For example, Bisht et al. [67] employed a verity of different maps to achieve tasks such as more chaotic permutation, diffusion, and RNG. A similar technique employing various maps in different stages of the encryption procedure was also proposed by Wang et al. [68].Fu et al. [69] proposed a novel keystream generation technique utilizing multiple chaotic maps that incorporates the plaintext itself into the stream. The algorithm was motivated by the need to defend against CPT and KPT attacks, and an analysis of the algorithm showed it is effective in achieving its goal.In terms of areas of application, stronger algorithms enforced by the use of multiple chaotic maps are important in numerous fields. For example, Choi et al. [70] proposed an algorithm using multiple maps for encrypting colored medical images, which can be seen as unique in their size and sensitivity. Experimental and statistical analysis of the resulting procedure showed it is secure for use with healthcare images.
-
Other mathematical sourcesIn addition to chaotic systems and maps, some researchers have used the following mathematical designs, which have not been originally defined for chaos creation:
- –
-
Space-filling curvesFractal geometry has several intriguing properties, such as self-similarity, composition by iterative methods, and a complex structure. Zhang et al. [71] utilized Hilbert curves and H-fractals, types of self-filling curves, in a novel image encryption algorithm. This algorithm alternates the use of both curves to efficiently scramble the pixels of the image.
- –
-
Memory cellular automataCellular Automata (CA) can best be described as a grid of cells with a finite set of states and a transition function that governs how cells change state over time. Whereas a standard CA only depends on the generation t-1, Memory Cellular Automata (MCA) depend on more parameters. When the MCA’s rules are defined by chaotic maps, the structure becomes a powerful tool for image encryption. Several algorithms using various-order MCAs have been proposed, for example a 4D MCA by Aslam et al. [72], a 2D MCA by Hibibipour et al. [73], and an indefinite CA by Hibibipour et al. [74].
- –
-
Transcendental numbersIn mathematics, a transcendental number has the characteristic that digits to the right of the decimal have no pattern [75]. Garcia et al. [75] proposed an image encryption algorithm that uses chaos and the transcendental number Pi, dubbed Chaotic Pi Ciphering (CPC). The algorithm uses Pi and a chaos source created using differential equations to generate cipher keys and substitution boxes.
Physical Sources
-
Optical ChaosOur physical world can provide many forms of chaos, with just one example being light. In studies by Xie et al. [76] and Lui et al. [77], they found success in producing a chaotic base for image encryption algorithms using lasers. Extensive security testing of both algorithms showed them to be highly secure and feasible for practical use.
-
Chaotic circuits
- –
-
Chua circuitSome physical electronic circuits such as the Chua circuit can produce chaotic behavior. AlMutairi et al. [80] utilized the circuit as a key generator in their proposed image encryption algorithm. By contrast, Lin et al. [81] proposed a similar encryption model, but instead utilized a variant of the classic Chua circuit with a PWL memristor. In both cases, analysis showed the algorithms to exhibit strong security properties.
- –
-
Memristive circuitsA memristor is a form of electrical component that is capable of exhibiting chaotic behavior. Liu et al. [82] proposed an image encryption algorithm that utilizes 4D memristive hyper-chaos to create chaos matrices. Security analysis showed strong security and cryptographic properties.Another image encryption algorithm was proposed by Sun et al. [83] using a memristive chaotic system. The presented system demonstrates a unique property known as multistability, which further improves the chaoticness of the system. Again, security analysis showed the algorithm to possess strong cryptographic properties.
- –
-
Physically Unclonable Functions (PUFs)True Random Number Generators (TRNGs), although very important in cryptography, are impossible to achieve in software. To counter this fact, Muhammad et al. [84] proposed an encryption algorithm using a hardware device, a form of physically unclonable function, to generate true random numbers. Through extensive experiments and analysis, the TRNG was successful in passing all tests required for safe use in cryptographic algorithms.
2.1.3. Chaos Dimension
-
One-dimensionalWork with one-dimensional chaos includes that by Wang and Lui [85], where the novel 1D Sine Chaotic System (1DSCS) was proposed. This system exhibits a large parameter interval as compared to the standard sine map it was built upon.Elghandour et al. [86] proposed an image encryption algorithm utilizing the 1D tent map. A similar algorithm also using the tent map was proposed by Tiwari et al. [87]. Extensive testing proved both algorithms to be effective at resisting common cryptographic attacks. The former paper also elaborated on the low chaotic range for the tent map and suggested that future work use a variant with a larger range such as the tent-sine map.
-
Two-dimensionalAn image encryption algorithm based on two-dimensional chaos was proposed by Yang and Tong [88]. This algorithm uses the 2D logistic chaotic system and a novel block image encryption procedure. Experimental results demonstrated the algorithm to have strong randomness, low pixel correlations, and high key sensitivity.
-
Three-dimensionalMany image encryption algorithms utilize three-dimensional chaos. One such algorithm was proposed by Qian et al. [89], where they utilized the 3D logistic and cat maps. The novel usage of image reconstruction techniques also improved the effectiveness of the algorithm.In an algorithm proposed by Asl et al. [90], the 2D image was converted into three-dimensional space by creating three streams from the red, green, and blue channels of the image. The 3D modular chaotic map was used as the chaos source for encryption.
-
Four-dimensionalHuang et al. [93] proposed a novel four-dimensional chaos system based on concepts known as “shape synchronization” and “driver-response”. The complex mathematical underpinnings make the algorithm very difficult to break, and experimental tests in the application of image encryption showed promising results for its effectiveness.
-
Five-dimensionalZhu and Zhu [94] proposed a novel five-dimensional chaotic map composed of the 2D logistic map and 3D discrete Lorenz map. Experimental simulations of the system when applied to image encryption resulted in high scores in many common encryption strength tests.
-
Multiple dimensionalWork related to mixing maps of varying dimensions in image encryption has also been performed. For example, Qui and Yan [95] proposed an image encryption algorithm using both the 1D logistic map and 3D Lorenz system. Experimental results demonstrated that the algorithm has strong security.Parida et al. [96] proposed a novel image encryption and transmission procedure based on Elliptic Curve Cryptography (ECC). Encryption is achieved using 3D and 4D Arnold cat maps as chaos sources, and the Elliptic Curve Diffie–Hellman (EDCH) key exchange algorithm is utilized to establish a shared key between parties. Digital signatures allow the algorithm to authenticate the encrypted message before decryption, and experimental results showed the method to be effective.
2.2. State-of-the-Art in the Image Aspect
2.2.1. Two-Dimensional versus Three-Dimensional Image
2.2.2. Gray-Scale versus Color Image
2.2.3. Transforms
Wavelet
Zigzag Transform
Cosine Transform
Contourlet Transform
Linear Canonical Transform (LCT)
2.3. State-of-the-Art in the Encryption Aspect
2.3.1. Symmetric versus Asymmetric Cryptography
2.3.2. Block Cipher vs. Stream Cipher
-
BlowflishBora et al. [116] proposed a block cipher using the Blowfish algorithm and cross-chaos map. Cryptanalysis results showed strong security.
-
Ecliptic Curve Cryptography (ECC)Abbas et al. [117] proposed an Ecliptic-Curve (EC)-based algorithm that utilizes pixel-level parallelism for faster encryption speeds. A different proposal by Benssalah and Rhaskali et al. [118] uses ECC combined with the Hill cipher and Arnold cat map to achieve a strong encryption algorithm targeted at medical images.
-
El-GamalEl-Gamal is a type of EC commonly utilized in cryptography. For example, Luo et al. [119] proposed a public-key-based image encryption algorithm utilizing the El-Gamal EC to address common issues with key management. In another proposal by Yousif et al. [118], El-Gamal was used to encrypt images that were first permutated using zigzag and spiral scanning.
-
RijindalDsouza and Sonawane [120] proposed a novel technique of using images as the key to encrypt/decrypt a directory in a file system. This technique employs both AES and Rijideal ciphers, and evaluation results demonstrated its effectiveness.
-
Rivest–Shamir–Adleman Cryptosystem (RSA)Nkapkop et al. [121] developed a novel asymmetric image encryption algorithm using RSA to solve the issue of key management. This algorithm uses the RSA key pairs to encrypt the initial values and parameters of the chaotic function so that the public key can encrypt images and only the private key can decrypt.
-
Data Encryption Standard (DES)Zhang et al. [122] proposed an image encryption algorithm utilizing the logistic chaos sequence for chaotic sequence generation and an improved DES algorithm for encryption. Simulation results demonstrated good security and speed, making it suitable for real-time use.
-
Novel block ciphersGupta et al. [123] proposed a novel block cipher using two keys where the image is split into four blocks; each is encrypted n times, and finally, the keys are inverted and the blocks further encrypted m more times. Evaluation through standard tests demonstrated strong cryptographic properties, making the algorithm usable for real-time connections.Rani and Kumar [124] proposed a novel stream cipher using a modified RC4 algorithm. The algorithm converts the image into three vectors for each color channel and uses the modified RC4 stream algorithm to encrypt them. Another algorithm utilizing the RC4 stream cipher was proposed by Ginting and Dillak [125]. This algorithm uses the logistic map to generate a keystream for encryption. The algorithm is lossless, which was verified by comparing the hash values of the image before encryption and the image after encrypting, then decrypting.
-
Hybrid ciphersA hybrid approach utilizing both block and stream ciphers was proposed by Goumidi and Hachouf [126]. This algorithm splits the image into two sub-images and encrypts one using the block cipher and the other using the stream ciphers. The encrypted sub-images are then merged back together to form the final image. The use of two different types of ciphers greatly increases the complexity of the algorithm, leading to stronger cryptographic properties.
2.3.3. Primitives
Scrambling
Bit Shuffling
Hashing
Permutation, Substitution, Confusion, and Diffusion
-
Permutation and diffusionPermutation is the process of rearranging elements in a structure, which, in the context of images, refers to scrambling the pixels. Abd-El-Hafiz et al. [134] performed an evaluation on three different permutation methods (discrete chaos, vectors, and Arnold cat map) and found that discrete performed the best.Diffusion is the process of ensuring there is no statistical significance to the resulting structure. In the context of images, this refers to scrambling the pixels of the image to eliminate the correlation between adjacent pixels. Ping et al. [135] proposed a novel digit-level permeation algorithm that additionally employs a high-speed diffusion algorithm. Evaluation results demonstrated high security and efficiency.Combining permutation with diffusion into the same stage of encryption aims to combat hackers who try to break each stage separately [136]. Liu et al. [137] proposed an algorithm to perform permutation and diffusion simultaneously. The algorithm additionally uses a Hopfield chaotic neural network to perform further diffusion, which gives the algorithm greater key sensitivity.
-
ConfusionConfusion in encryption refers to the level of dependency elements of the cipher-text have with the key. As seen with permutation, confusion is often integrated with diffusion for the same reasons. For example, Run-he et al. [138] proposed an image encryption algorithm that achieves an integration of confusion and diffusion by XORing the plain image with chaotically generated offset matrices.
-
SubstitutionSubstitution involves replacing an element with something else in a predictable and invertible manner. The substitution requirement is commonly implemented using S-boxes, which are matrices that define how each input maps to its substituted value.For image encryption, chaos-based S-boxes include those generated from the chaotic sine map [139] and the logistic map [140]. Wang and Zhang [141] also proposed an algorithm with multiple S-box substitutions, where the order of the boxes is determined by a random chaos sequence. Another algorithm proposed by Khan et al. [142] splits the image into four blocks and applies a different S-box to each block. These S-boxes each originate from a different encryption algorithm (AES, PQL, APL, and Shipjack). Another paper by Lidong et al. [143] proposes a dynamic encryption algorithm so that the cipher image is always different even if the same key and plain image are used.
One-Time Key
Secret Sharing
This entry is adapted from the peer-reviewed paper 10.3390/asi5030057
