6. Risk Policies and Continuity Planning
Managing risks is tightly involved with policy analysis. In fact, the policy is attributed to a principle or a plan to lead decisions through obtaining intended outcomes, which are specifically applied to a broad range of subjects, including organizations, groups, governments, and individuals. Accordingly, the development and implementation of policies, aiming to guarantee continuous development, are accomplished through a similar structure as for the risk management structure, including:
-
The recognition of a problem;
-
Applying particular analysis;
-
Processing phase, including developing policy instrumentation, consulting, and coordination;
-
Decision-making;
-
Execution;
-
Final evaluation (assessing the effectiveness of the policy).
Each company or business is highly threatened by unpredicted business interruptions and associated challenges. Depending on the specific circumstances of any business, there are many particular events that might constitute a crisis. Unplanned events can bring about serious and catastrophic effects on a business, including damaging stocks, losing customers, and bankruptcy that also makes it impossible for the organizations to withstand them. These events are mainly specified by low probability, considerably large consequences, vagueness, and short response times. The crises that an organization may encounter can cover a wide range, including physical crisis, personnel crisis, information crisis, reputational crisis, criminal crisis, and economic crisis. Accordingly, it is critically important to set specific rules and policies to help to be completely immune against potential crises [
48,
49].
Digitalization also plays a crucial role in the continuity of an organization. The potential to treat and prevent risk, to be receptive to new ideas, and to adopt digitalization to improve efficiency and performance within the organization are all directly related to business continuity. Digital technologies allow the creation, quantification, and distribution of data required to implement new business processes to start organizing for effective implementation in a digitalized era. They can also be a very useful tool to help manage disaster risk at all stages, such as identifying and assessing, preventing, and preparing for recovery [
50,
51,
52].
Business continuity planning refers to the development and maintenance of specific frameworks, policies, and established standards not only to manage a business disruption but also to create resilience [
53]. It is simply understood that every business strategy is dependent on business sustainability, and each factor that violates this pre-established assumption would seriously contribute to impinging the business potential to hit its targets. Business continuity refers to the maintenance of unhindered availability and accessibility of all chief resources required for a business to act appropriately day in day out. A process of establishing a system of prevention and recovery from threatening interruptions is simply referred to as business continuity planning which its main objective is to provide the ability to preclude, prepare for, react against, and recover specific vulnerable sectors from an unplanned event. The associated business continuity plan is an outcome of the business continuity management process, which is referred to as a management process with specified steps to reach the main objectives of a continuity plan. Businesses that participate in continuity planning exhibit much more resilience, immunity, and stability against a series of emergencies, disasters, and associated unplanned events [
48,
54,
55].
Although used interchangeably and exhibiting common features, business continuity planning and business continuity policy are not exactly the same. In fact, along with addressing exclusive requirements for maintaining continuity, they serve different objectives within a company. The policy determines specific standards and benchmarks, while the role of a plan is to delineate how an organization reacts and behaves through an event, from its beginning to the end. It is clear that, the information required by the business continuity policy should be included in the business continuity plans [
48,
54,
55].
A continuity plan should be concise and straightforward. There are three main steps for creating and applying a business continuity plan in an organization:
-
Risk assessment and associated analysis;
-
Development and documentation of a business continuity plan;
-
Testing and implementing a business continuity plan.
The first step in applying continuity planning in an organization is to pursue risk assessment, to determine the essential business functions, and to identify the degree and the level of the exposure to threats. Throughout this step, the critical functions required for the operation of an organization and their associated impact after their loss are identified. A robust business impact analysis focused on functionality, services, and revenues is the foundation of a successful business continuity strategy [
56,
57]. Critical functions of a business are mainly referred to as the business outputs that, along with lacking scheduling plasticity, impose serious implications over many organization sectors if disrupted. In fact, not all operational sectors of an organization are required to be considered as critical functions because it is highly dependent on the duration of the emergency. Accordingly, the critical operative function of each sector with respect to covering time frames should be accurately considered. Their impact on the business should be determined during the process, along with specifying the correlated critical functions. Identified critical functions should be prioritized with respect to their associated impact, aiming to establish a priority over the recovery process. During the process, after identifying organization functions, the associated processes and operations of the business should be classified with respect to their priority, including critical, important, and non-critical, as is shown in
Table 1 [
58]. In accordance with the process, after identifying the associated critical functions, specific people should be allocated for each one to be in charge of them [
36,
37].
Table 1. Classifications to prioritize business processes in continuity planning [
58].
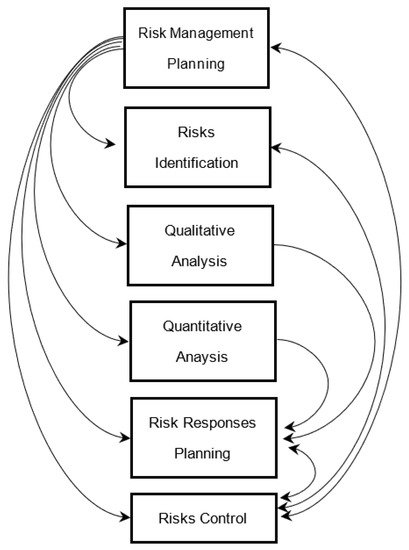
After specifying the critical functions of the business, a risk analysis should be accomplished over them. It is important to engage in risk assessment activities because the governed recovery plan is indeed highly dependent on the characteristics and the level of identified risk in each operation. The process of risk identification and analysis is quite similar to what has been mentioned in the risk management structure that is also tightly involved with the qualitative and quantitative analysis.
The second step in applying continuity management is developing and documenting a continuity plan. After assessing the risk fields and their potential impact on the business under investigation, a continuity plan should be developed to determine the thresholds at which the business can accept the risks and specify the required actions against different levels of risk. At this level, there are three main actions that a business can perform according to the previous risk assessments, including:
-
Accepting the existing condition;
-
Diminishing the impact of a specific crisis/risk down to a satisfactory degree;
-
Diminishing or eradicating the potential effects.
Among the three mentioned options, activities associated with decreasing the likelihood or impact of a disaster are more often suggested since the exposure of the business is considerably diminished to a reasonably practicable level. Accepting the present condition is mostly reflected in the fast recovery ability. However, this may not be quite effective after completing the recovery; the business may not still recover its customers or other resources used to deal with. In addition, it is found to be extensively expensive to eradicate the associated potential effects.
Accordingly, concerning the obtained information from previous assessments, strategies for continuity of the business should be developed and documented to be further validated. To develop strategies that support business continuity, several main actions should be accomplished. As an important attempt during the process, the main communication channels that are essential for emergency conditions should be determined. This includes the particular locations and personnel required to be accessible, the means to communicate, and the time characteristics of communications during an emergency. This is an essential step in developing a plan for continuity management since communication plays a critical role in all essential operative sectors of an organization [
54,
55].
Once the communication channels and their correlated characteristics are thoroughly identified, essential resources required for the recovery process during the emergency should be specified. This includes the determination of the following requirements:
-
Minimum number of personnel required for critical operative sectors;
-
Minimal requirements for implementing critical functions regarding alternate manufacturing, warehousing, operating systems, etc.;
-
Means and resources of obtaining required materials;
-
The time frame through which each of these specified actions are required;
-
Recovery alternatives.
After identifying essential resources for the recovery process during emergencies, action over the disaster assessment should be carefully pursued. During this step, managers should identify the constituent components of disasters correlated with a particular operation, determine the means to quantitatively evaluate an emergency, and specify the main resources for obtaining information regarding the disasters under investigation. This assessment provides necessary information for decision-makers to engage in decisions. Decision-making for disasters should be included in the plan. During the process, it is important to envision the sequence of actions during and after the emergency. The decision-making process is reflected in many aspects of the business-critical functions, including the teams that are required before, during, and after the disaster, the correlated roles and responsibilities, and the time point through which these elements take action [
54].
After developing strategies in continuity management, it is important to provide these strategies as documents to be applicable in further steps in crisis management. However, this documentation process should be performed since poorly written plans can be strongly frustrating, hard to be employed, and outdated in a short period. Documentation should proceed to support the quick and straightforward perception and better success in its implementation. Accordingly, along with being brief and to the point, serious considerations should be taken into consideration, including:
-
Well-organized writing formats to contribute to the cohesiveness and conformity of the plan;
-
The specific assumption on which the strategies might be relied on should be written;
-
If the planner encounters difficulty in preparing the plan, it may pertain to the fact that he/she is trying to plan for areas that do not need to be planned.
The associated documented continuity plans are further required to be tested and validated. Efficient organizational contingency management is possible if the company consistently tests the involved person’s experience and knowledge of emergency response, as characterized in business continuity plans, to implement business continuity, identify and prioritize resources, thereby steadily developing the resources involved in the emergency response process and ensuring coordinated actions throughout crises, while taking technological developments and company specifics into account [
59,
60].
Accordingly, specific procedures should be considered to validate and test the previously documented continuity plan, including checklist tests, simulation tests, and parallel tests. Throughout the validation process, the compatibility of backup procedures is specified, the modification spots on the plan are determined, the potential of the organization to recover after a crisis is demonstrated, and a regular basis for the validation of the plan provides the opportunity to regularly update and correct inconsistencies that have been outlined. In fact, this step is highly functional as it establishes the guarantee that all important steps throughout the plan are included.
7. Risk Control and Fraud Detection
All businesses are threatened by fraud all over the world. During tough economic situations, small and medium-sized enterprises are more inclined toward developing ways to establish further innovation, development, and survival rather than risk management and associated activities. In addition, a highly linked world has resulted in advancements in communication and digital technology. Various forms of networks have evolved, including social media, e-commerce websites, blogs, industry trade networks, telecommunication networks, banking networks, and insurance networks, all of which generate an increasing amount of data. These networks provide a large amount of information that can be accessed anonymously, making them ideal platforms for spreading false information, mischief, and misdemeanors: fraudsters and attackers can hide their harmful actions within the mountains of data. As these networks continue to spread, fraudsters’ possibilities to manipulate them for their own gain have grown as well [
61,
62].
Hence, along with requiring a great deal of hard work and research, they are highly endangered to fraud. Fraud commonly includes actions such as conspiracy, embezzlement, money laundering, and corruption, and it is mainly referred to as the untruthful and illegal actions committed by specific individuals or companies to provide a profitable, mostly financial outcome. Fraud occurs when an organization attempts to obtain something of value, in most cases money or property, in an illegal manner. Accordingly, fraud can originate from different sources, including staff members, suppliers, customers, and third parties having no direct connection with the associated business [
25,
26,
63].
No single reason can be considered as the associated driving force to fraud, and many elements that may contribute to the fraud happening include motivation and the required potentials of offenders, the technical and professional ability of the fraudster, final consequences of fraud discovery, etc. However, there is a generalized model to indicate the reasons for fraud that considers the main aspects of fraud is the fraud triangle which presents three main elements as the main driving forces contributing to fraud, including motivation, opportunity, and rationalization [
63,
64].
Briefly, motivation which is interchangeably known as pressure, refers to the inclination of an organization towards committing fraud. In simple terms, it typically relies on either greed or need. Incentives toward committing fraud may be reflected from the personal motivations, investors, or higher-positioned managers’ expectations or associated bonuses.
The opportunity is simply attributed to the conditions that enable fraud to occur. Based on numerous studies, it is indicated that employees are either completely honest or completely dishonest. However, most of the employees fall into a third category where they are mostly affected by opportunities. Among all three fraud elements, it is accounted as the only element that a company implements complete control over. The establishment of fraud opportunities mainly originate from inadequate accountant policies and weak internal controls. In other words, fraud opportunities are more likely to develop where weak internal controls, low security over properties, and imprecise policies exist [
63,
64].
Rationalization is the individual or organizational justification to commit fraud. The common rationalizations that fraudsters contribute to are justifications such as “the upper positioned managers doing as well” and “having no other solutions” [
64].
Many studies are being carried out in an attempt to estimate the exact scales and costs that fraud poses to a business. However, most of the frauds remain unrecognized, and even if recognized, they are rarely reported. Although gaining a full understanding of the concept and compiling associated reliable statistics is involved with high complexity, it has been majorly demonstrated that fraud, along with being prevalent within an organization, can bring about serious, costly problems (explaining examples of the scale) [
64]. Even if the optimistic prognosis of a long-term drop in fraud is correct, the trend is unlikely to be unstoppable or consistent. Informational and behavioral frictions, greater institutional skepticism, and economic inequality are all variables that might hinder the long-term drop in fraud [
65,
66,
67].
Aside from the vast scale of problems and costs that fraud can impose on a business, a great number of organizations all over the world still lack formal systems and processes aiming to detect, prevent and respond to fraud. In this regard, managers who professionally deal with the analysis of information and systems can play a chief role in the establishment and accomplishment of such systematized anti-fraud activities within an organization. There has been a great attempt toward employing integrated (or hybrid) multiple-criteria decision-making methods by modern decision-makers in acting against fraud and fraudsters [
68,
69]. Accordingly, financial organizations are increasingly relying on data-driven strategies to build fraud detection systems that can detect and prevent illegal transactions automatically [
70,
71,
72]. Generally, along with the development of anti-fraud actions, specific approaches should be developed to prevent fraud, detect, and respond appropriately [
64].
Considering the prevalence of fraud in numerous organizations and its associated destructive consequences, there is a compelling argument concerning the engagement of organizations in anti-fraud activities, which requires investing time and other resources. Generally, the anti-fraud strategies can be classified into four main actions as the following:
-
Prevention;
-
Detection;
-
Deterrence;
-
Response.
Each of these anti-fraud strategies are highly interconnected, and each one contributes to a particular role in eliminating fraud from an organization [
73].
7.1. Fraud Prevention
According to elements that contribute to fraud, it is clearly recognized that some effective ways should be performed to prevent fraud. These ways are mainly correlated with decreasing the associated incentives, mitigating the required opportunities, and restricting the ability of potential fraudsters to rationalize their fraud actions. Associated prevention methods mainly include the establishment of policies, controls, and practices, including training and fraud awareness to halt fraud from occurring. Here, we are discussing several main preventative efforts to mitigate the occurrence and cost of fraud within an organization [
63,
64].
One of the most critical factors contributing to anti-fraud activities is to create a well-organized ethical organization within a business [
74]. More dynamic and proactive managerial efforts, such as building an “ethical tone at the top” and establishing an efficient “ethics training”, are necessary to construct a whistleblowing policy in a firm, which in turn positively influences employees’ impressions of corporate anti-fraud tactics [
74,
75]. The attitudes within an organization can largely determine the extent to which the organization is likely to be at risk of fraud. Ethical standards have been revealed to be very beneficial in the long run and in very different aspects since many people, including customers, suppliers, the community, etc., realize that they can rely on a trustworthy organization with well-established ethical standards. The definition of well-organized ethical standards is not quite clear, and it can vary from organization to organization. However, in standardizing an ethical policy, it mostly attempted to establish straightforward short enough statements for better efficiency [
63].
In some references, it is recommended to develop and promote ethical codes, which refer to particular policies concerning ethical conduct and implementation within an organization. However, such documented ethics codes are not sufficient to effectively prevent this. In fact, these ethical standards should be tightly entangled within the organizational culture. Accordingly, the commitment to ethical behaviors should be primarily reflected in the behavior of upper-positioned managers because within an organization the employees are more likely to imitate what they see from their superior managers. In addition, alongside the commitment of the senior managers, they must contribute to controlling the fraud risk and establish activities that may help to grow an anti-fraud culture [
63,
64].
Another important activity that an organization should perform to manage and prevent fraud risks is the regular assessment of fraud risks. This assessment is carried out in a similar manner discussed previously in the risk management section. Simply, the fraud risks should be clearly identified in all aspects, directly-related and indirectly related, and further assessed concerning their impact and probability.
Identifying and assessing fraud risks provide a wealth of information for further establishing the training to increase the awareness of individuals within an organization. The necessity to increase the awareness of an organization in terms of fraud is more obviously recognized since, after the occurrence of fraud, those who have been close to the fraud surprisingly declare a low consciousness concerning the fraud. Thus, as an imperative step through the risk management process, it is essential to increase the awareness of individuals within an organization through formal training, group meetings, posters, newsletters, bulletins, and associated platforms. Through this training, employees would be enlightened on what constitutes fraud, how to prevent and identify fraudulent behavior, how to respond if it has happened, and hence, the communication should be constantly established [
64,
76].
Just as employee awareness raises, it should be widely established in an organization as a major component of fraud risk management and an effective reporting mechanism. The importance of establishing an effective reporting system is simply understood since most of the employees are aware of specific misconducts in the organization, and a large set of them may remain silent. This silence in reporting such misconduct is majorly reflected in many conflicting emotions, including working group/family loyalties, fear of consequences, and suspicion rather than proof. Accordingly, the senior managers should provide a culture through which all employees play an important role in fraud-fighting [
76].
Another significant approach in developing a preventative culture within an organization is to provide a well-organized internal control system.
7.2. Detecting Fraud
It is of significant importance to invest time and resources to develop and establish approaches required for fraud prevention within an organization since it strongly supports the further sustainability and continuity of the business. In addition, the recovery of an organization after the occurrence of fraud is a highly inefficient and time-consuming process, and most organizations cannot fully recover the losses they have had. Nevertheless, the methodologies developed for preventing fraud are unable to ensure complete immunity to an organization. Accordingly, an organization should engage in other specific policies to ensure that the continuity of the system would be established after the fraud happened. This is mainly met through fraud detection. Fraud detection methodologies usually employ specific procedures that mostly rely on analytical approaches and reporting systems to specify and sum up the existence of inconsistencies and anomalies [
63,
64,
76].
Generally, fraud can be detected and revealed in several main ways. Since the risk management process plays a substantial role in fraud management, the internal audit functions should be strictly established to monitor risk management activities and fraud-susceptible factors. Moreover, the associated controls and mechanisms established within an organization largely contribute to fraud discovery. Aside from the fraud-related considerations, fraud can also be detected by accident or in terms of received information. However, concerning the fraud discovery, two sets of elements are considered to be highly helpful, including (i) warnings and fraud indicators and (ii) tools and methodologies [
63].
As mentioned, no systems are fully fraud-proof, and there is always a possibility of fraud occurrence. Accordingly, identifying fraud indicators can provide great potential in early diagnosis and discovery. There are two main classes of fraud indicators include alerts and warning signs.
Warning signs are known as the organizational indicators of fraud risk, which can be reflected in different areas of business risk, financial risk, environmental risk, information systems, and technology risks.
7.3. Fraud Deterrence
Although stated separately as a different anti-fraud strategy, deterrence is highly interrelated with the prevention concept. Fraud deterrent is a proactive, preventative strategy, whereas fraud detection is a reactive reaction to either a misuse of assets or falsification of financial results. Effective preventative measures act as powerful deterrents to individuals who would otherwise be inclined to perpetrate fraud [
77,
78].
Fraud detection serves as a deterrent to potential fraudsters by notifying them that the firm is actively counteracting fraud and that systems are in place to identify any illegal conduct that has happened. The fear of being caught will often prevent a potential criminal from attempting fraud. Additional detection controls should also be put in place to compensate for the fact that deterrent measures may be ineffective in some cases [
64,
77].
Three basic elements are essential in the prevention of fraud. To some extent, they all entail elements of a solid ethical culture: top management’s action-based commitment to ethical behavior, heightened skepticism and an inquiring attitude, and powerful communication from all those associated with the financial reporting process [
79].
7.4. Responding to Fraud
A formal approach to address and handle detected or suspected cases of fraud is to employ a plan called the fraud response plan. By using this plan, corporations can gather evidence to facilitate the response to fraud in a legal manner. Moreover, the corporate fraud response plan lowers the tendency to commit fraud which not only results in minimum loss and damage but also builds up market confidence and integrity of evidence for organizations [
63,
64,
80].
Generally, the fraud response plan is what creates legal, ethical, and moral standards for activities, and in the case of standard violation, the plan helps the organization to take any action against that person. All members of staff, and other stakeholders (customers, suppliers, and shareholders), must be aware of the fraud response plan, which contains the standards and the consequences of not respecting them. Although publicly exposing fraud has an adverse effect on the company’s public image, it is a warning to those tempted to misconduct. Thus, regulated financial services companies are now legally obliged to report financial crime [
64,
76].
Roles and responsibilities in an organization are contingent on the size, industry, culture, and other factors. Generally, managers and supervisors are responsible for detecting fraud and other irregularities in their area. The finance director is responsible for the organization’s response to fraud. Human resources usually handle any internal disciplinary procedures. Legal advisers (internal or external) are called as soon as a fraud is reported to advise on civil, internal, criminal responses, and the recovery of assets. If computers were used for fraud, IS and IT staff can provide technical advice on IT security, capability, and access. Public relations are in charge of preparing a brief for the press if that news of fraud becomes public. The police also investigate the matter. External consultants investigate skills from outside the organization. Insurers protect organizations against large fraud losses. Furthermore, where applicable, large organizations may have fraud officers, audit committees, and internal and external auditors [
63,
64,
80].
Several steps are generally being employed to respond to an identified fraud. First, after recording and evaluating all required details, the fraud officer should establish an investigation team accompanied by the advisers’ team. Throughout the associated investigation, objectives, time frame, and the required resources should be clearly specified. Accordingly, a formulated plan should be developed, and for each specific action, authorities should be assigned. The actions within the developed plan are majorly involved with the recovery of the stolen resources, funds, and properties coupled with the modification and adjustment of existing anti-fraud strategies to prevent further occurrence of similar fraud events [
64,
80].
8. Conclusions
With growing complexity in different businesses, information and data processing plays an important role in the effective operation of departments within an organization. Data processing is a substantially time-consuming effort since great and growing volumes of data exist in any organization. Accordingly, information systems in light of advances in computer-based systems have been developed to streamline the specific practices associated with data processing, specifically to collect, store, process, and analyze data, and also extract and disseminate information for particular purposes. Such information systems are largely contributing to the significant increase in the effectiveness of organizations through various means, especially in decision-making processes. However, aside from the wide range of advantages that information systems present to an organization, it has also brought a series of potential risks within an organization. Risks associated with the implementation and the development of information systems are highly involved in information development and data security. Hence, there is growing attention and investment in resources throughout the world aiming to standardize and develop specific frameworks through which the associated risks can be mitigated. These are recognized as risk management practices. Risk management provides a broad range of applications and disciplines which attempt to develop particular plans and frameworks to detect, prevent, mitigate, and respond to risks in highly organized structures. Throughout such structures, the risks are identified, organized, analyzed both qualitatively and quantitatively, and further responded to, which is coupled with developing particular policies to prevent the occurrence of similar risk events. Although there have been numerous literature studies in different fields of healthcare organizations, insurance, energy power, waste management, mining, etc., great efforts are still required to fill the gaps existing in the literature, specifically in the fields of psychological factors and social system issues causing information system risks.
References
- Nikoloski, K. The role of information technology in the business sector. Int. J. Sci. Res. (IJSR) 2014, 3, 303–309. [Google Scholar]
- Rochmah, T.N.; Fakhruzzaman, M.N.; Yustiawan, T. Hospital staff acceptance toward management information systems in Indonesia. Health Policy Technol. 2020, 9, 268–270. [Google Scholar] [CrossRef]
- Mutwiri, W. Amazon Business Information Systems. Data Acquisition and Management in Its Value Chain; GRIN Verlag: Munich/Ravensburg, Germany, 2020. [Google Scholar]
- Lucas, H.C., Jr. Performance and the use of an information system. Manag. Sci. 1975, 21, 908–919. [Google Scholar] [CrossRef]
- Abe, S.; Ozawa, M.; Kawata, Y. Science of Societal Safety: Living at Times of Risks and Disasters; Springer Nature: Berlin/Heidelberg, Germany, 2019. [Google Scholar]
- Juntunen, M.; Lehenkari, M. A narrative literature review process for an academic business research thesis. Stud. High. Educ. 2021, 46, 330–342. [Google Scholar] [CrossRef]
- Zhu, T.; Haugen, S.; Liu, Y. Risk information in decision-making: Definitions, requirements and various functions. J. Loss Prev. Process Ind. 2021, 72, 104572. [Google Scholar] [CrossRef]
- Aven, T.; Zio, E. Foundational issues in risk assessment and risk management. Risk Anal. 2014, 34, 1164–1172. [Google Scholar] [CrossRef] [PubMed]
- Aven, T. Risk assessment and risk management: Review of recent advances on their foundation. Eur. J. Oper. Res. 2016, 253, 1–13. [Google Scholar] [CrossRef]
- Hansson, S.O.; Aven, T. Is risk analysis scientific? Risk Anal. 2014, 34, 1173–1183. [Google Scholar] [CrossRef] [PubMed]
- Aven, T.; Heide, B. Reliability and validity of risk analysis. Reliab. Eng. Syst. Saf. 2009, 94, 1862–1868. [Google Scholar] [CrossRef]
- Veres, O.; Ilchuk, P.; Kots, O.; Rishnyak, I.; Rishniak, H. Development of an Information System to Minimize the Risks of Personnel Management. In Conference on Computer Science and Information Technologies; Springer: Berlin/Heidelberg, Germany, 2020; pp. 939–958. [Google Scholar]
- Chinazirova, S.; Tlekhurai-Berzegova, L.; Buller, E.; Kadakoeva, G. Development of an information system for the assessment of industrial and environmental risks of the enterprise. Econ. Sci. 2020, 3, 45–49. [Google Scholar]
- Thompson, K.M.; Deisler, P.F., Jr.; Schwing, R.C. Interdisciplinary vision: The first 25 years of the Society for Risk Analysis (SRA), 1980–2005. Risk Anal. Int. J. 2005, 25, 1333–1386. [Google Scholar] [CrossRef]
- Lowrance, W.W.; Klerer, J. Of Acceptable risk: Science and the Determination of Safety. J. Electrochem. Soc. 1976, 123. [Google Scholar] [CrossRef]
- Kaplan, S.; Garrick, B.J. On the quantitative definition of risk. Risk Anal. 1981, 1, 11–27. [Google Scholar] [CrossRef]
- AMSC; SAFT. Department of Defense Standard Practice forSystem Safety; United States Department of Defense, The Pentagon: Arlington County, VA, USA, 2012. [Google Scholar]
- Aven, T.; Renn, O. On risk defined as an event where the outcome is uncertain. J. Risk Res. 2009, 12, 1–11. [Google Scholar] [CrossRef]
- Lemos, F. On the definition of risk. J. Risk Manag. Financ. Inst. 2020, 13, 266–278. [Google Scholar]
- Ward, S.; Chapman, C. Stakeholders and uncertainty management in projects. Constr. Manag. Econ. 2008, 26, 563–577. [Google Scholar] [CrossRef]
- Pritchard, C.L. Risk Management: Concepts and Guidance; Auerbach Publications: Boca Raton, FL, USA, 2014. [Google Scholar]
- Chen, J. Risk communication in cyberspace: A brief review of the information-processing and mental models approaches. Curr. Opin. Psychol. 2020, 36, 135–140. [Google Scholar] [CrossRef] [PubMed]
- Humayun, M.; Niazi, M.; Jhanjhi, N.; Alshayeb, M.; Mahmood, S. Cyber security threats and vulnerabilities: A systematic mapping study. Arab. J. Sci. Eng. 2020, 45, 3171–3189. [Google Scholar] [CrossRef]
- Finne, T. Information systems risk management: Key concepts and business processes. Comput. Secur. 2000, 19, 234–242. [Google Scholar] [CrossRef]
- Sherer, S.A.; Alter, S. Information systems risks and risk factors: Are they mostly about information systems? Commun. Assoc. Inf. Syst. 2004, 14, 2. [Google Scholar] [CrossRef]
- Goldstein, J.; Benaroch, M.; Chernobal, A. IS-Related Operational Risk: An Exploratory Analysis. In Proceedings of the AMCIS, Toronto, ON, Canada, 14–17 August 2008. [Google Scholar]
- Bank for International Settlements. Basel committee on banking supervision (BCBS). In International Convergence of Capital Measurement and Capital Standards: A Revisedframework; BCBS: Basel, Switzerland, 2006. [Google Scholar]
- Tefera, A.; Bekele, B. Periodontal disease status and associated risk factors in patients attending a tertiary hospital in northwest Ethiopia. Clin. Cosmet. Investig. Dent. 2020, 12, 485. [Google Scholar] [CrossRef]
- Westerman, R.; Kuhnt, A.-K. Metabolic Risk Factors and Fertility Disorders: A Narrative Review of the Female Perspective. Reprod. Biomed. Soc. Online 2022, 14, 66–74. [Google Scholar] [CrossRef]
- Samimi, A.; Samimi, M. Investigation of Risk Management in Food Industry. Int. J. Adv. Stud. Humanit. Soc. Sci. 2020, 9, 195–204. [Google Scholar]
- Stackpole, C.S. A User’s Manual to the PMBOK Guide; John Wiley & Sons: Hoboken, NJ, USA, 2013. [Google Scholar]
- Suroso, J.S.; Fakhrozi, M.A. Assessment of information system risk management with octave allegro at education institution. Procedia Comput. Sci. 2018, 135, 202–213. [Google Scholar] [CrossRef]
- Stoneburner, G.; Goguen, A.; Feringa, A. Risk management guide for information technology systems. Nist Spec. Publ. 2002, 800, 800–830. [Google Scholar]
- Boiko, A.; Shendryk, V.; Boiko, O. Information systems for supply chain management: Uncertainties, risks and cyber security. Procedia Comput. Sci. 2019, 149, 65–70. [Google Scholar] [CrossRef]
- Longerstaey, J.; Spencer, M. Riskmetricstm—Technical Document; Morgan Guaranty Trust Company of New York: New York, NY, USA, 1996; Volume 51, p. 54. [Google Scholar]
- Benjamin, C.W.; Chou, H.-Y.; Wu, M.B.; Chang, D.H. The Risks of Risk Management. In Proceedings of the 2006 IEEE International Conference on Management of Innovation and Technology, Singapore, 21–23 June 2006; pp. 708–712. [Google Scholar]
- Chalmers, J.; Armour, M. The Delphi Technique; Springer: Singapore, 2019. [Google Scholar] [CrossRef]
- Kaveh, A.; Rahami, H.; Shojaei, I. Swift analysis of linear and non-linear structures and applications using reanalysis. In Swift Analysis of Civil Engineering Structures Using Graph Theory Methods; Springer: Berlin/Heidelberg, Germany, 2020; pp. 201–245. [Google Scholar]
- Zhang, Y.; Guan, X. Selecting project risk preventive and protective strategies based on bow-tie analysis. J. Manag. Eng. 2018, 34, 04018009. [Google Scholar] [CrossRef]
- Brown, D.F.; Dunn, W.E. Application of a quantitative risk assessment method to emergency response planning. Comput. Oper. Res. 2007, 34, 1243–1265. [Google Scholar] [CrossRef]
- Kumar, L.; Jindal, A.; Velaga, N.R. Financial risk assessment and modelling of PPP based Indian highway infrastructure projects. Transp. Policy 2018, 62, 2–11. [Google Scholar] [CrossRef]
- Fang, C.; Marle, F.; Xie, M.; Zio, E. An integrated framework for risk response planning under resource constraints in large engineering projects. IEEE Trans. Eng. Manag. 2013, 60, 627–639. [Google Scholar] [CrossRef]
- Okta. What Is Identity Management and Access Control? Available online: https://www.okta.com/identity-101/what-is-identity-management-and-access-control/ (accessed on 10 November 2021).
- Bugge, C.; Williams, B.; Hagen, S.; Logan, J.; Glazener, C.; Pringle, S.; Sinclair, L. A process for Decision-making after Pilot and feasibility Trials (ADePT): Development following a feasibility study of a complex intervention for pelvic organ prolapse. Trials 2013, 14, 1–13. [Google Scholar] [CrossRef]
- Alsmadi, I.; Burdwell, R.; Aleroud, A.; Wahbeh, A.; Al-Qudah, M.; Al-Omari, A. Security and access controls: Lesson plans. In Practical Information Security; Springer: Berlin/Heidelberg, Germany, 2018; pp. 53–71. [Google Scholar]
- Beres, Y.; Baldwin, A.; Mont, M.C.; Shiu, S. On identity assurance in the presence of federated identity management systems. In Proceedings of the 2007 ACM workshop on Digital Identity Management, Fairfax, VA, USA, 2 November 2007; pp. 27–35. [Google Scholar]
- Yeluri, R.; Castro-Leon, E. Identity management and control for clouds. In Building the Infrastructure for Cloud Security; Springer: Berlin/Heidelberg, Germany, 2014; pp. 141–159. [Google Scholar]
- Blyth, M. Business Continuity Management: Building an Effective Incident Management Plan; John Wiley & Sons: Hoboken, NJ, USA, 2009. [Google Scholar]
- Jose, D.; Rosa, P.D.S.; Rosa, S. Crisis Management; Ateneo Graduate School of Business: Makati City, Philippines, 2020. [Google Scholar]
- Moşteanu, D.; Roxana, N. Management of disaster and business continuity in a digital world. Int. J. Manag. 2020, 11, 169–177. [Google Scholar]
- Moşteanu, N.R.; Faccia, A.; Cavaliere, L.P.L. Disaster Management, Digitalization and Financial Resources: Key factors to keep the organization ongoing. In Proceedings of the 2020 4th International Conference on Cloud and Big Data Computing, Liverpool, UK, 26–28 August 2020; pp. 118–122. [Google Scholar]
- Moşteanu, N.R. Challenges for Organizational Structure and design as a result of digitalization and cybersecurity. Bus. Manag. Rev. 2020, 11, 278–286. [Google Scholar] [CrossRef]
- Fezzey, T.; Batchelor, J.H.; Burch, G.F.; Reid, R. Cybersecurity Continuity Risks: Lessons Learned from the COVID-19 Pandemic; Kennesaw State University: Kennesaw, GA, USA, 2021. [Google Scholar]
- Lindström, J.; Samuelsson, S.; Hägerfors, A. Business continuity planning methodology. Disaster Prev. Manag. Int. J. 2010, 19, 243–255. [Google Scholar] [CrossRef]
- Syed, A.; Syed, A. Business Continuity Planning Methodology; Sentryx: Austerlitz, The Netherlands, 2004. [Google Scholar]
- Yang, C.-H.; Lee, K.-C. Developing a strategy map for forensic accounting with fraud risk management: An integrated balanced scorecard-based decision model. Eval. Program Plan. 2020, 80, 101780. [Google Scholar] [CrossRef]
- Lahuta, P.; Kardoš, P.; Hudáková, M. Integrated Risk Management System in Transport. Transp. Res. Procedia 2021, 55, 1530–1537. [Google Scholar] [CrossRef]
- Jafar, E.; Taneja, U. Business continuity planning—A survey of hospitals in Delhi. J. Public Health 2017, 25, 699–709. [Google Scholar] [CrossRef]
- Civča, D.; Atstāja, D.; Koval, V. Business continuity plan testing methods in an international company. Restruct. Manag. Increase Compet. Trading Co. Latv. 2021, 5, 341. [Google Scholar]
- Sasaki, H.; Maruya, H.; Abe, Y.; Fujita, M.; Furukawa, H.; Fuda, M.; Kamei, T.; Yaegashi, N.; Tominaga, T.; Egawa, S. Scoping review of hospital business continuity plans to validate the improvement after the 2011 Great East Japan Earthquake and Tsunami. Tohoku J. Exp. Med. 2020, 251, 147–159. [Google Scholar] [CrossRef] [PubMed]
- Niemimaa, M.; Järveläinen, J.; Heikkilä, M.; Heikkilä, J. Business continuity of business models: Evaluating the resilience of business models for contingencies. Int. J. Inf. Manag. 2019, 49, 208–216. [Google Scholar] [CrossRef]
- Setiawan, A.; Wibowo, A.; Susilo, A.H. Risk analysis on the development of a business continuity plan. In Proceedings of the 2017 4th International Conference on Computer Applications and Information Processing Technology (CAIPT), Kuta Bali, Indonesia, 8–10 August 2017; pp. 1–4. [Google Scholar]
- Pourhabibi, T.; Ong, K.-L.; Kam, B.H.; Boo, Y.L. Fraud detection: A systematic literature review of graph-based anomaly detection approaches. Decis. Support Syst. 2020, 133, 113303. [Google Scholar] [CrossRef]
- Hooi, B.; Shin, K.; Song, H.A.; Beutel, A.; Shah, N.; Faloutsos, C. Graph-based fraud detection in the face of camouflage. ACM Trans. Knowl. Discov. Data (TKDD) 2017, 11, 1–26. [Google Scholar] [CrossRef]
- Karpoff, J.M. The future of financial fraud. J. Corp. Financ. 2021, 66, 101694. [Google Scholar] [CrossRef]
- Files, R.; Martin, G.S.; Rasmussen, S.J. Regulator-cited cooperation credit and firm value: Evidence from enforcement actions. Account. Rev. 2019, 94, 275–302. [Google Scholar] [CrossRef]
- Morgan, R.E. Financial Fraud in the United States, 2017; US Department of Justice, Office of Justice Programs, Bureau of Justice Statistics, NCJ: Washington, USA, 2021; Volume 255817. [Google Scholar]
- Samociuk, M.; Iyer, N.; Doody, H. A Short Guide to Fraud Risk: Fraud Resistance and Detection; Routledge: London, UK, 2017. [Google Scholar]
- Baldree, J. Fraud Risk Management: A Guide to Good Practice; CIMA Publisher Wokingham: Wokingham, UK, 2008. [Google Scholar]
- Baesens, B.; Höppner, S.; Verdonck, T. Data engineering for fraud detection. Decis. Support Syst. 2021, 113492. [Google Scholar] [CrossRef]
- Stojanović, B.; Božić, J.; Hofer-Schmitz, K.; Nahrgang, K.; Weber, A.; Badii, A.; Sundaram, M.; Jordan, E.; Runevic, J. Follow the trail: Machine learning for fraud detection in Fintech applications. Sensors 2021, 21, 1594. [Google Scholar] [CrossRef] [PubMed]
- Temuçin, T.S.; Erbaş, S.; Anıl, A. Using Big Data in Internal Fraud Detection. TIDE Acad. Res. 2021, 3, 55–82. [Google Scholar]
- Todorović, Z.; Tomaš, D.; Todorović, B. Anti-Fraud Strategy. Economics 2020, 8, 69–78. [Google Scholar] [CrossRef]
- Suh, J.B.; Shim, H.S. The effect of ethical corporate culture on anti-fraud strategies in South Korean financial companies: Mediation of whistleblowing and a sectoral comparison approach in depository institutions. Int. J. Law Crime Justice 2020, 60, 100361. [Google Scholar] [CrossRef]
- Dolan, S.; Hawkins, S.; Albrecht, C.; Richley, B. Raising the ethical bar: Ethical audits and positive culture transformation. The European Business Review. 11 January 2021. Available online: https://www.europeanbusinessreview.com/raising-the-ethical-bar-ethical-audits-and-positive-culture-transformation/ (accessed on 10 November 2021).
- Jackson, P.M. Debate: Fraud risk management in the public sector. Public Money Manag. 2013, 33, 6–8. [Google Scholar] [CrossRef]
- Eusebio, N. Anti-Fraud Strategy; Technical Note ACCID; Associació Catalana de Comptabilitat i Direcció: Vic, Spain, 2017. [Google Scholar]
- Sofia, I.P. The impact of internal control and good corporate governance on fraud prevention. In Proceedings of the International Seminar on Accounting Society, Kota Tangerang Selatan, Indonisea, 21 November 2020. [Google Scholar]
- Reporting, D.F. Three pillars of fraud deterrence and detection. Strateg. Financ. 2015, 96, 17–18. [Google Scholar]
- Araj, F.G. Responding to Fraud Risk; The Institute of Internal Auditors Research Foundation (IIARF): Lake Mary, FL, USA, 2015. [Google Scholar]