Your browser does not fully support modern features. Please upgrade for a smoother experience.
Please note this is an old version of this entry, which may differ significantly from the current revision.
As the global supply chain grows more intricate and the prevalence of counterfeit components surges, it becomes paramount to verify the authenticity of electrical chips. The infiltration of counterfeit components, potentially finding their way into electronic equipment, raises concerns as workers contend with mounting client demands. Microelectronics are vital to the healthcare and defense industries, making them vulnerable to counterfeit products.
- counterfeit
- detection
- trust
- microelectronics
- security
1. Introduction
Cybersecurity plays a pivotal and indispensable role in today’s technological landscape. Yet, cybercriminal tactics continue to evolve, making their identification increasingly challenging. Phishing, IoT hacks, and ransomware have resulted in substantial losses in the tech industry. Thus, hardware security, which protects electronic gear throughout production, has grown in popularity. Hardware security, akin to other security domains, strives to shield hardware from threats that could compromise or obliterate it [1]. Ensuring ‘Assurance’ and ‘Trust’ in the context of securing hardware systems translates to the confidence that electronic equipment will perform as intended, free from the peril of compromised components [2].
As the global supply chain grows more intricate and the prevalence of counterfeit components surges, it becomes paramount to verify the authenticity of electrical chips. The infiltration of counterfeit components, potentially finding their way into electronic equipment, raises concerns as workers contend with mounting client demands [3]. National security, economic stability, and individual privacy hang in the balance when hardware systems lack adequate security. Reports from the Department of Defense reveal that over a million components in military aviation and combat missiles have been identified as counterfeit [4][5].
During the first Iraq War in 1991, fighter planes were disabled by a secret activation code embedded in the hardware [6]. Experts believe that the presence of a wicked electrical circuit that was remotely programmable and triggerable played a part in aiding such a catastrophic catastrophe. The Semiconductor Industry Association (SIA) says that annual losses to manufacturers owing to counterfeits total USD 7.5 billion [7], amounting to around 11,000 job losses in the United States [8]. Other sources assert even higher losses, estimating annual sales losses of around USD 100 billion to counterfeiting [9][10].
To combat this menace, cutting-edge strategies for detecting and preventing counterfeits from infiltrating the market are of paramount importance [11]. Figure 1 illustrates the alarming increase in reported counterfeit components between 2021 and 2022, a period during which worldwide semiconductor sales remained relatively stable.
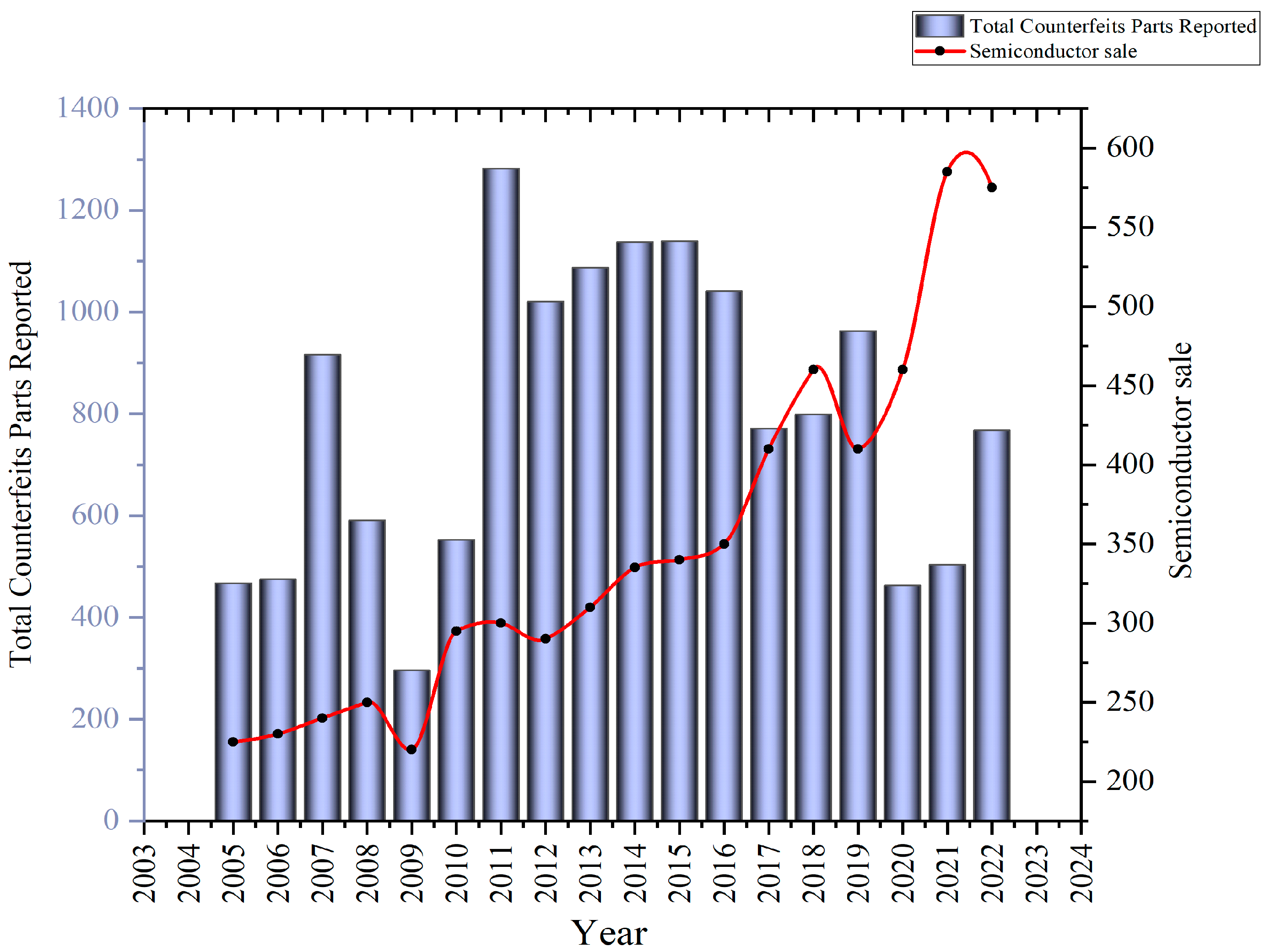
Figure 1. Reported counterfeits increased significantly between 2021 and 2022 [12].
2. Counterfeit Attack Modes
As depicted in Figure 2, counterfeit integrated circuits (ICs) are primarily susceptible to four categories of attack mechanisms: software, hardware, network, and information security.
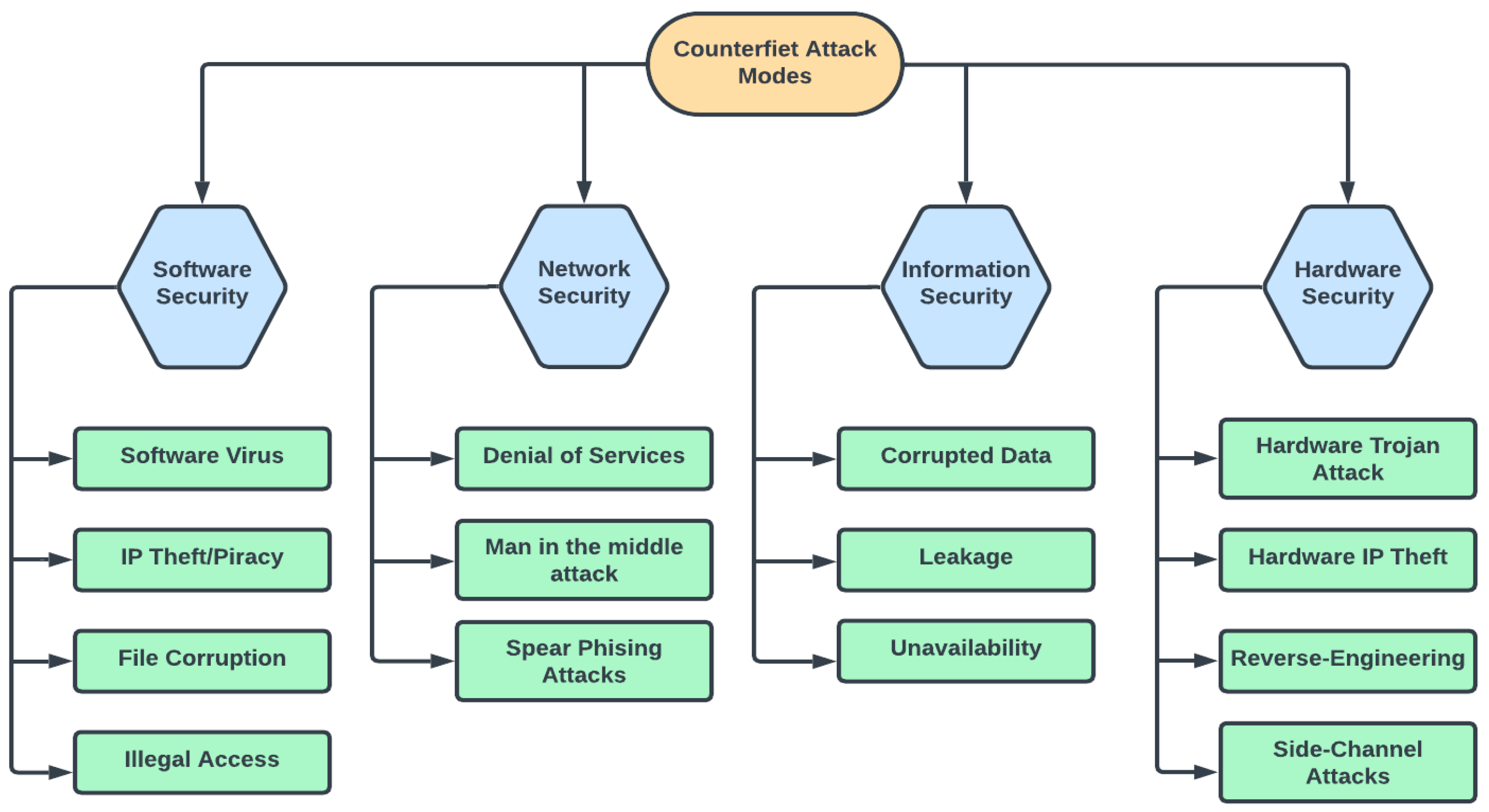
Figure 2. Chart showing counterfeit attack modes and the potential consequences of such attacks.
2.1. Software Security
As the significance of software security continues to escalate, the role of trusted microelectronics in fortifying software applications and ensuring their stability has gained paramount importance. Software security revolves around the safeguarding of software applications against vulnerabilities and attacks that could be exploited by counterfeit integrated circuits (ICs). Counterfeit ICs provide malicious actors with the means to inject malicious code, circumvent security protocols, or manipulate the functionality of software applications. They can also facilitate software-based side-channel attacks and privilege escalation, thereby granting unauthorized access to sensitive data or system resources.
Notably, the Plundervolt attack, elucidated by [13], exploits the dynamic frequency and voltage scaling features of modern CPUs, specifically targeting Intel SGX enclave operations. By manipulating the processor’s voltage, attackers can induce known faults in the processor package, compromising security. This vulnerability can lead to the compromise of cryptographic keys and the introduction of memory-safety vulnerabilities. The repercussions, as outlined in [14], encompass unauthorized access to private data, system instability, software performance degradation, and reduced overall system security.
Furthermore, speculative execution, a form of software security attack that occurs when the CPU speculatively executes tasks it anticipates needing in the future without explicit instruction [15], introduces potential risks. This approach eliminates the need to await the completion of previous commands before executing new ones, thereby enhancing speed by reducing latency and increasing parallelism [16]. However, speculative execution can inadvertently execute potentially harmful programs, raising security concerns.
To enhance software security and instill trust, Physically Unclonable Functions (PUFs) have been proposed. PUFs are employed to generate unique and unpredictable cryptographic keys for authentication and encryption, constituting robust hardware-based security mechanisms. Notable PUF projects include the Arbiter PUF, which leverages differing data-line delays [17], the Ring Oscillator PUF, which relies on variations in the frequencies of two-ring oscillators [18], the SRAM PUF, exploiting idiosyncrasies in SRAM-cell startup behavior [19], and the Memristor PUF, capitalizing on the resistance-changing properties of memristive devices [20]. It is worth noting that PUFs have faced attacks, as elucidated in [21], where modeling attacks seek to emulate a PUF’s behavior through mathematical modeling. These attacks have been successfully executed with the aid of machine learning tools such as Support Vector Machines (SVMs) and neural networks.
2.2. Hardware Security
The embedding of Hardware Trojans, backdoors, and other malicious circuits within counterfeit integrated circuits (ICs) poses a significant threat, endangering the security, confidentiality, and availability of electronic systems [22]. This underscores the critical need for rigorous hardware security measures, including supply chain oversight, secure manufacturing processes, and state-of-the-art counterfeit detection technologies, to forestall unauthorized access [23], data breaches [24], or system malfunctions [25].
Hardware security presents multifaceted challenges, encompassing vulnerabilities to a range of attacks (e.g., side-channel or Trojan attacks) at various layers (e.g., chip or PCB), further complicating the landscape of hardware security. Concurrently, hardware trust concerns stem from interactions with untrustworthy third parties at any stage of a device’s production and distribution, spanning from IP or CAD tool providers to manufacturing facilities and warehouses.
Among common hardware security breaches, Reverse Engineering Attacks, which aim to pilfer a device’s intellectual property and design details for illicit purposes such as duplication or counterfeiting, are prominent [26]. These attacks can be executed through methods like deprocessing, optical imaging, and circuit extraction [27]. In contrast, fault injection attacks intentionally induce system malfunctions to gain access to or control over the targeted system [28], employing tools such as lasers, electromagnetic pulses, or temperature-dependent fault injections [29].
Side-channel attacks focus on unintentional data leakage from a device’s physical implementation, encompassing aspects like power consumption, electromagnetic radiation, or timing data [30]. Techniques such as differential power analysis, simple power analysis, and correlation power analysis are employed to infer device behaviors and potentially extract sensitive information, such as encryption keys, from power consumption patterns [31].
Furthermore, Hardware Trojans represent malevolent hardware additions introduced during product assembly, serving as latent security or functionality vulnerabilities that can be activated at a later stage [32].
2.3. Network Security
Network attacks often manifest in the deployment of counterfeit network interface controllers or routers, potentially leading to the theft of sensitive information, service disruptions, or the illicit takeover of networked devices via unauthorized remote access [33].
In safeguarding critical infrastructure, the Internet of Things (IoT), and cloud-based services, trusted microelectronics play a central role [34]. These components are instrumental in ensuring the privacy, integrity, and authenticity of stored data [18], commonly relying on cryptographic primitives and secure key storage.
One particular area of scrutiny is spear-phishing, an exceptionally targeted and sophisticated form of phishing attack that surpasses conventional phishing attempts in terms of complexity and personalization. This issue is explored extensively in a research paper authored by a single individual [35]. The paper underscores the urgency for enterprises to proactively counter the escalating threat of spear-phishing. To fortify themselves against sophisticated cyberattacks, businesses are advised to prioritize user education, implement robust security measures, and maintain a comprehensive and up-to-date incident response plan.
2.4. Information Security
In addition to bypassing security measures to gain unauthorized access to sensitive data, counterfeit cryptographic integrated circuits also have the potential to disrupt encryption or authentication methods. The advent of social media and cloud computing has necessitated a heavy investment by businesses in information security in order to safeguard data. The Federal Communications Commission offers tips to businesses for cybersecurity [36]. The CIA Triad, comprising of Confidentiality, Integrity, and Availability, serves as a fundamental framework within the field of information security. An all-encompassing information security strategy encompasses policies and security controls that effectively mitigate risks to these three essential components.
The CIA triad serves as a comprehensive framework for overseeing information security and is also valuable for effectively managing research products and data.
This entry is adapted from the peer-reviewed paper 10.3390/electronics12224618
References
- Bhunia, S.; Tehranipoor, M. Chapter 1—Introduction to Hardware Security. In Hardware Security; Bhunia, S., Tehranipoor, M., Eds.; Morgan Kaufmann: Burlington, MA, USA, 2019; pp. 1–20.
- Fazzari Booz, S.; Hamilton, A.; Narumi, R. New & Old Challenges for Trusted and Assured Microelectronics; Booz Allen Hamilton: Arlington, VA, USA, 2019.
- Shah, A. Europe, US Warn of Fake-Chip Danger to National Security, Critical Systems. The Register. 2022. Available online: https://www.theregister.com/2022/03/18/eu_us_counterfeit_chips/ (accessed on 13 April 2023).
- Zeljka, Z. Supply Chain Compromise: Adding Undetectable Hardware Trojans to Integrated Circuits. Help Net Security. 2018. Available online: https://www.helpnetsecurity.com/2018/12/10/hardware-trojans/ (accessed on 19 March 2022).
- Uppal, R. Threats to ICT Supply Chains including Counterfeit Electronic Components and Hardware Trojans Present Critical Risk to Military and Security Systems. International Defense Security & Technology Inc. 2020. Available online: https://idstch.com/threats/threats-to-ict-supply-chains-including-counterfeit-electronic-components-and-hardware-trojans-present-critical-risk-to-military-and-security-systems/ (accessed on 19 March 2022).
- Hambling, D. Pentagon’s “Kill Switch”: Urban Myth? Wired. 2008. Available online: https://www.wired.com/2008/05/kill-switch-urb/ (accessed on 27 March 2023).
- McKeefry, H. Counter the Counterfeiters. DigiKey. 2021. Available online: https://www.digikey.com/en/blog/counter-the-counterfeiters (accessed on 18 April 2022).
- Brett, D. Counterfeit Electronic Parts: A Multibillion-Dollar Black Market. Trenton Systems. 2020. Available online: https://www.trentonsystems.com/blog/counterfeit-electronic-parts (accessed on 19 March 2022).
- The Threat of Counterfeit Components to Electronic Supply Chains. Nanotech. Available online: https://www.nanosecurity.ca/counterfeit-electronic-components/ (accessed on 19 March 2022).
- IEEE Transactions on Components and Packaging Technologies Publication Information. IEEE Trans. Compon. Packag. Technol. 2007, 30, C2.
- Bastia, S. Next generation technologies to combat counterfeiting of electronic components. Compon. Packag. Technol. IEEE Trans. 2002, 25, 175–176.
- Akhoundov, D. 2022 Annual Report; ERAI, Inc.: Naples, FL, USA, 2022.
- Murdock, K.; Oswald, D.; Garcia, F.D.; Van Bulck, J.; Gruss, D.; Piessens, F. Plundervolt: Software-Based Fault Injection Attacks against Intel SGX. In Proceedings of the 2020 IEEE Symposium on Security and Privacy (SP), San Francisco, CA, USA, 18–21 May 2020; pp. 1466–1482.
- Tehranipoor, M.; Koushanfar, F. A Survey of Hardware Trojan Taxonomy and Detection. IEEE Des. Test Comput. 2010, 27, 10–25.
- Intel. Speculative Execution. 2018. Available online: https://www.intel.com/content/www/us/en/developer/articles/technical/software-security-guidance/technical-documentation/introduction-speculative-side-channel-methods.html (accessed on 16 March 2023).
- Dewan, M.C. Study of Speculative Execution and Branch Prediction. 2006. Available online: https://citeseerx.ist.psu.edu/viewdoc/download;jsessionid=EBE980ABF71E4B8C0055F14D3DDAC3F2?doi=10.1.1.119.2934&rep=rep1&type=pdf (accessed on 16 March 2023).
- Lee, J.W.; Lim, D.; Gassend, B.; Suh, G.E.; Van Dijk, M.; Devadas, S. A Technique to Build a Secret Key in Integrated Circuits for Identification and Authentication Applications. In Proceedings of the 2004 Symposium on VLSI Circuits, Honolulu, HI, USA, 17–19 June 2004; Digest of Technical Papers (IEEE Cat. No.04CH37525). IEEE: Piscataway, PJ, USA, 2004; pp. 176–179.
- Suh, G.E.; Devadas, S. Physical Unclonable Functions for Device Authentication and Secret Key Generation. In Proceedings of the 2007 44th ACM/IEEE Design Automation Conference, San Diego, CA, USA, 4–8 June 2007; pp. 9–14.
- Gassend, B.; Clarke, D.; Van Dijk, M.; Devadas, S. Silicon Physical Random Functions. In Proceedings of the 9th ACM Conference on Computer and Communications Security, Washington, DC, USA, 18–22 November 2002.
- Ranasinghe, C.; Engels, D.W.; Cole, P.H. Security and Privacy: Modest Proposals for Low-Cost RFID Systems. Available online: https://www.semanticscholar.org/paper/Security-and-Privacy%3A-Modest-Proposals-for-Low-Cost-Ranasinghe-Engels/4c755bb9751f148a769737addc3e0fb14de42341 (accessed on 27 September 2023).
- Rührmair, U.; Sehnke, F.; Sölter, J.; Dror, G.; Devadas, S.; Schmidhuber, J. Modeling Attacks on Physical Unclonable Functions. In Proceedings of the 17th ACM Conference on Computer and Communications Security, Chicago, IL, USA, 4–8 October 2010; Association for Computing Machinery: New York, NY, USA, 2010; pp. 237–249.
- Wang, X.; Tehranipoor, M. Novel Physical Unclonable Function with Process and Environmental Variations. In Proceedings of the 2010 Design, Automation & Test in Europe Conference & Exhibition (DATE 2010), Dresden, Germany, 8–12 March 2010; pp. 1065–1070.
- Monjur, M.M.R.; Heacock, J.; Calzadillas, J.; Mahmud, M.; Roth, J.; Mankodiya, K.; Sazonov, E.; Yu, Q. Hardware Security in Sensor and its Networks. Front. Sens. 2022, 3, 850056.
- Shivakumara, T.; Patil, R.M.; Muneshwara, M.S. Review Paper on Dynamic Mechanisms of Data Leakage Detection and Prevention. Int. J. Comput. Sci. Eng. 2019, 7, 349–358.
- Asadizanjani, N.; Rahman, M.T.; Tehranipoor, M. (Eds.) Package Security. In Physical Assurance: For Electronic Devices and Systems; Springer International Publishing: Cham, Switzerland, 2021; pp. 155–177.
- Sharief, S.; Chahal, P.; Alocilja, E. Application of DNA sequences in anti-counterfeiting: Current progress and challenges. Int. J. Pharm. 2021, 602, 120580.
- Torrance, R.; James, D. The State-of-the-Art in IC Reverse Engineering. In International Workshop on Cryptographic Hardware and Embedded Systems; Springer: Berlin/Heidelberg, Germany, 2009; pp. 363–381.
- Barenghi, A.; Breveglieri, L.; Koren, I.; Naccache, D. Fault Injection Attacks on Cryptographic Devices: Theory, Practice, and Countermeasures. Proc. IEEE 2012, 100, 3056–3076.
- Balasch, J.; Gierlichs, B.; Verbauwhede, I. An In-Depth and Black-Box Characterization of the Effects of Clock Glitches on 8-Bit MCUs. In Proceedings of the 2011 Workshop on Fault Diagnosis and Tolerance in Cryptography, Tokyo, Japan, 29 September 2011; IEEE Computer Society: Washington, DC, USA, 2011; pp. 105–114.
- Kocher, P.; Jaffe, J.; Jun, B.; Rohatgi, P. Introduction to differential power analysis. J. Cryptogr. Eng. 2011, 1, 5–27.
- Mangard, S.; Oswald, E.; Popp, T. Power Analysis Attacks: Revealing the Secrets of Smart Cards; Springer: New York, NY, USA, 2007.
- Brier, E.; Clavier, C.; Olivier, F. Correlation Power Analysis with a Leakage Model. In Cryptographic Hardware and Embedded Systems—CHES 2004; Joye, M., Quisquater, J.-J., Eds.; Springer: Berlin/Heidelberg, Germany, 2004; pp. 16–29.
- York, D. Chapter 3—Eavesdropping and Modification. In Seven Deadliest Unified Communications Attacks; York, D., Ed.; Syngress: Boston, MA, USA, 2010; pp. 41–69.
- Alves, T.; Das, R.; Werth, A.; Morris, T. Virtualization of SCADA Testbeds for Cybersecurity Research: A Modular Approach. Comput. Secur. 2018, 77, 531–546.
- Parmar, B. Protecting against spear-phishing. Comput. Fraud. Secur. 2012, 2012, 8–11.
- Cybersecurity for Small Businesses. Federal Communications Commission. Available online: https://www.fcc.gov/communications-business-opportunities/cybersecurity-small-businesses (accessed on 7 September 2023).
This entry is offline, you can click here to edit this entry!
