Your browser does not fully support modern features. Please upgrade for a smoother experience.
Please note this is an old version of this entry, which may differ significantly from the current revision.
Blockchain is the foundation of all cryptocurrencies, while machine learning (ML) is one of the most popular technologies with a wide range of possibilities. Blockchain may be improved and made more effective by using ML.
- blockchain
- security analysis
- machine learning
- algorithms
- applications
1. Introduction
Several fields in the real world have already begun to make use of and conduct extensive research into machine learning (ML) [1][2]. User-generated data in the tens of thousands per day may be utilized to train ML models, and those models can then be put to use solving a wide range of problems in business and society. Despite the progress of ML, data and model difficulties still exist. For instance, it is challenging to generalize ML models to reflect the future because current training methods require large amounts of data, which are often unavailable in practice [3] or limited due to the high cost of collection [4]. Concerns about data leakage and privacy [5] also exist. Filtering out “bad data” is a constant fight with malicious contributors or spammers, who can submit low-effort or illogical data and still receive rewards [6]. Additionally, it is difficult to generalize ML models to reflect the future due to outdated training [7], especially in subjects such as the Industrial Internet of Things (IIoT) [8], etc.
Most people agree that a blockchain is an efficient option that can guarantee security and reliability. However, as explained in [9], it may be vulnerable to attacks and security issues. Specifically, two significant attacks that undermined the network’s functioning recently occurred on Ethereum Classic [10], a permissionless (public) blockchain-based decentralized platform for smart contracts [11]. The blockchain is defined roughly by a global ledger that can efficiently and permanently record transactions via a timed chain of blocks, or blocks. Each block is added to the chain after being validated, based on a distributed consensus procedure, and contains information about the transactions. When enough nodes authenticate the block, which is subsequently regarded as reliable, the consensus is obtained. The whole procedure is recorded, and data may be gathered to describe the events taking place in the underlying ledger [12]. It is sensible to wonder whether such information may be used to monitor the process and provide early detection and analysis systems that can alert users to unusual events and potential attacks.
2. Security and Blockchain
There has been a significant surge in the number of reported security incidents involving the personal data of users. As a result, third parties may have access to the data and gather all personally identifiable information. This intermediary can be eliminated through the use of blockchain technology, which allows for direct transactions between two parties. The quantity of data in the environment has increased lately, and personal and sensitive information need not be safe in the hands of third parties as they are targeted for abuse and assault. Blockchain technology helps users who are not required to rely on a third party and acknowledges people as the owners of their data. However, it needs to have its regulations and norms, which is where the term “smart contract” comes in. Before initiating a transaction, the gateway keeper needs to draft a set of rules and a contract, which will facilitate peer-to-peer (P2P) interaction [13][14].
Many operations in cryptography are performed to provide various security services, including non-repudiation (ensuring authentication and integrity) [15], confidentiality (keeping information secret from communication parties), integrity, and authenticity. When asymmetrical cryptography is used, which has a set of public keys accessible to everyone and a set of private keys visible only to the owner, blockchain systems are naturally secure. These keys are used to ensure the integrity and ownership of a transaction [16][17]. The security of the blockchain system is linked to the integrity, confidentiality, and authorization of transactions. Unlike centrally kept data, which is more susceptible to security breaches, the decentralized structure of blockchain systems requires a P2P consensus mechanism, which reduces single points of failure for data [18]. There are many creative applications for blockchain, some of which are briefly discussed below. For example, Gai et al. [19] claim that integrating blockchain technology with an existing cloud solution could significantly improve the performance and security of cloud data centers. Recently, Wang et al. [20] implemented a secure and mutual authentication protocol to support the use of blockchain for identity verification issues in the smart grid. Similarly, before suggesting a blockchain-based authentication method for the smart grid, Wang et al. [21] highlighted a potential security threat to the infrastructure of the smart grid.
Despite the high level of security provided by blockchain systems, they are still vulnerable to various security and data integrity attacks [22]. PoW consensus-related attacks, such as 51% majority manipulation [23], consensus delay due to distributed denial of service [24][25], block ingestion, de-anonymization, blockchain forking, orphaned blocks, pollution log, and selfish mining [26], as well as attacks against double-spending [24] and liveness attacks [27] are some examples of these types of attacks. Based on the evidence, the majority of security issues arise from three primary areas: transactions, authentication, and network connectivity. Therefore, technologies that allow inappropriate connections and their integration with other technologies may pose several security risks [28]. Since the inception of blockchain technology, there have been five generations of technological advancements, and the range of applications has significantly expanded [29].
Blockchain security issues need to be addressed because, despite its potential benefits, blockchain technology introduces new security concerns that need to be addressed. Blockchain networks are decentralized, transparent, and immutable, which makes them a desirable target for malicious actors attempting to exploit system vulnerabilities [30]. A total of 51% of attacks, smart contract vulnerabilities, consensus algorithm flaws, and privacy concerns are some of the most significant security obstacles in blockchain networks. These security issues can result in data intrusions, monetary loss, and reputational harm for individuals and organizations that utilize blockchain networks. Consequently, it is essential to resolve these challenges through research and innovation to improve the security of blockchain systems and facilitate the pervasive adoption of this technology.
3. Blockchain and the Importance of ML
Through the usage of Bitcoin, blockchain [31] was largely promoted in the banking industry. It has been incorporated into many other sectors recently, including pharmaceutical manufacturing, supply chain operations, the healthcare sector, and many other important areas. Although ML is known for its automation of problem-solving by applying statistical computer algorithms or models, blockchain is often used for preserving financial transactions/data by maintaining a decentralized digital ledger that keeps all data in a highly safe manner.
In addition to processing enormous amounts of business data and building an effective prediction system that makes decisions automatically, ML is well known for its ability to analyze patterns in a dataset and interpret patterns in business data to produce excellent visual graphs and interpolations that can be used to provide insights into top management. In the insurance sector, cutting-edge ML algorithms have recently been utilized to predict financial risks. Insurance firms may accurately estimate the risks involved with charging new insurance premiums thanks to ML, which runs its algorithms on massive amounts of financial information and discovers a certain hidden pattern. Blockchain establishes a distributed ledger with a secure transactional database that has precise timestamps and immutable and permanent data instances. The main reason blockchain is so well-known is that it uses digital signatures as a particular method of reaching an agreement on financial data entities. Large amounts of data are needed for ML to produce credible models. Gathering, organizing, and auditing data is a straightforward approach made possible by blockchain that may increase data accuracy [32].
Blockchain greatly enhances data protection by automating the prediction of which types of data need to be stored and processed in a chain for making instances as accessible as possible. Blockchain has incredible support for standards for securing a lot of data at different nodes and makes data available at any instance in an encrypted manner. Since they are decentralized, blockchains may have security flaws [33]. The most prevalent issue is that the consensus procedure may be disrupted as a result of an assault, allowing a few mining farms to control which blocks are put into the network. This specific risk exists in public blockchains. Private versions are immune to this assault since each node is uniquely recognized, and a suitable consensus process is in place.
In the field of security, combining blockchain with ML may result in new and reliable solutions (Figure 1). For example, blockchain may be used to establish an immutable record of transactions that cannot be changed, and ML algorithms can be taught to identify patterns of fraudulent conduct in financial transactions. Blockchain may also be used to securely store data about network activities, and ML algorithms can be used to identify and stop cyberattacks in real time. ML may be used to validate users’ identities based on biometric data, which can be utilized for identity verification. It is more difficult for hackers to obtain and use this data if it is securely stored in a decentralized way using blockchain. ML algorithms may be used to evaluate this data and find patterns of suspicious behavior or possible security breaches in supply chain security. Blockchain can be used to produce a safe and transparent record of every step in a supply chain. Lastly, ML can be used to analyze the behavior of these contracts and spot potential security flaws, helping to avoid the loss of money or other assets. Smart contracts are automatically executed based on predefined conditions and can be created using blockchain.
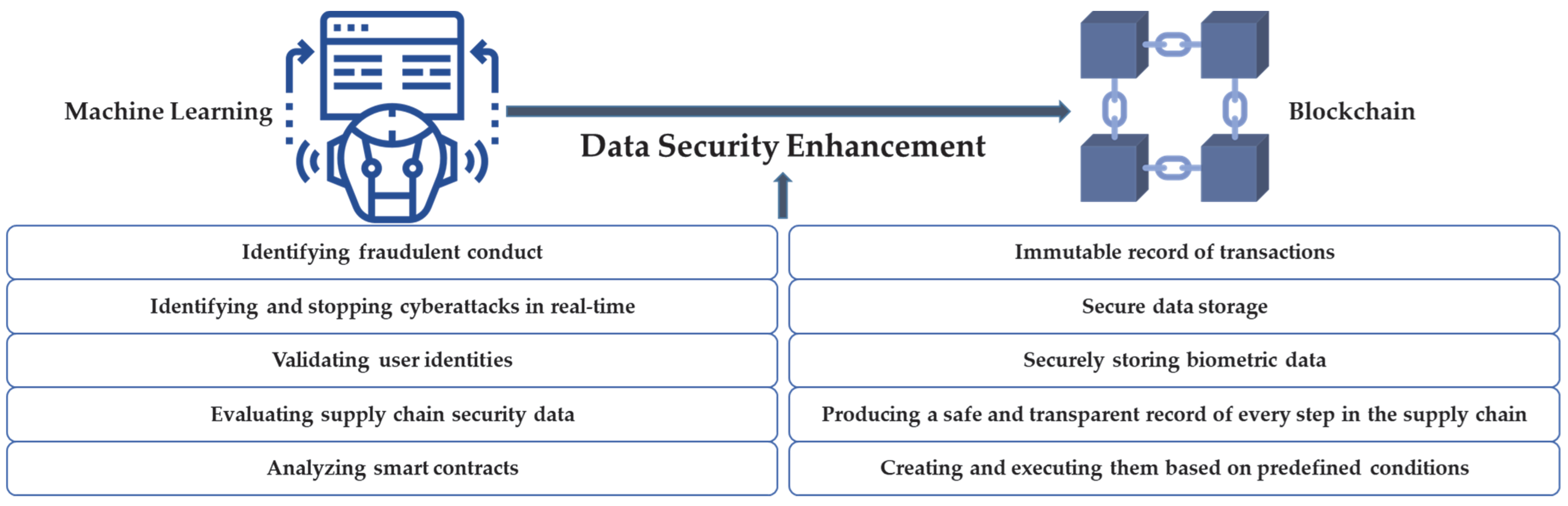
Figure 1. ML method to enhance data security of blockchain.
The adoption of blockchain technology in various industries has increased awareness of the significance of blockchain network security. By analyzing data, detecting patterns, and identifying potential security hazards in real time, ML has emerged as a potential method for enhancing the security of blockchain systems. By providing a secure, decentralized, and immutable digital ledger, blockchain can increase the veracity of data used by ML algorithms. However, blockchain networks are susceptible to security vulnerabilities, which necessitate the implementation of appropriate security measures and consensus procedures. The combination of blockchain and ML has the potential to revolutionize data security, but security needs to be maintained at all times.
This entry is adapted from the peer-reviewed paper 10.3390/info14050295
References
- Sarker, I.H. Machine learning: Algorithms, real-world applications and research directions. SN Comput. Sci. 2021, 2, 160.
- Taherdoost, H.; Madanchian, M. Artificial Intelligence and Knowledge Management: Impacts, Benefits, and Implementation. Computers 2023, 12, 72.
- De Breuck, P.-P.; Hautier, G.; Rignanese, G.-M. Materials property prediction for limited datasets enabled by feature selection and joint learning with MODNet. NPJ Comput. Mater. 2021, 7, 83.
- Vabalas, A.; Vabalas, A.; Gowen, E.; Poliakoff, E.; Casson, A.J. Machine learning algorithm validation with a limited sample size. PLoS ONE 2019, 14, e0224365.
- Liu, B.; Liu, B.; Ding, M.; Shaham, S.; Rahayu, W.; Farokhi, F.; Lin, Z. When machine learning meets privacy: A survey and outlook. ACM Comput. Surv. (CSUR) 2021, 54, 31.
- Daniel, F.; Daniel, F.; Kucherbaev, P.; Cappiello, C.; Benatallah, B.; Allahbakhsh, M. Quality control in crowdsourcing: A survey of quality attributes, assessment techniques, and assurance actions. ACM Comput. Surv. (CSUR) 2018, 51, 7.
- Jordaney, R.; Jordaney, R.; Sharad, K.; Dash, S.K.; Wang, Z. Transcend: Detecting concept drift in malware classification models. In Proceedings of the 26th USENIX Security Symposium (USENIX Security 17), Vancouver, BC, Canada, 16–18 August 2017.
- Sisinni, E.; Saifullah, A.; Han, S.; Jennehag, U.; Gidlund, M. Industrial internet of things: Challenges, opportunities, and directions. IEEE Trans. Ind. Inform. 2018, 14, 4724–4734.
- Ye, C.; Li, G.; Cai, H.; Gu, Y.; Fukuda, A. Analysis of security in blockchain: Case study in 51%-attack detecting. In Proceedings of the 2018 5th International Conference on Dependable Systems and Their Applications (DSA), Dalian, China, 22–23 September 2018.
- Atzei, N.; Bartoletti, M.; Cimoli, T. A survey of attacks on ethereum smart contracts (sok). In Proceedings of the Principles of Security and Trust: 6th International Conference, POST 2017, Held as Part of the European Joint Conferences on Theory and Practice of Software, ETAPS 2017, Uppsala, Sweden, 22–29 April 2017; Proceedings 6. Springer: Berlin/Heidelberg, Germany, 2017.
- Buterin, V. A next-generation smart contract and decentralized application platform. White Pap. 2014, 3, 2-1.
- Taherdoost, H. Smart Contracts in Blockchain Technology: A Critical Review. Information 2023, 14, 117.
- Stephen, R.; Alex, A. Alex, A. A review on blockchain security. In IOP Conference Series: Materials Science and Engineering; IOP Publishing: Bristol, UK, 2018.
- Hong, H.; Sun, Z. A secure peer to peer multiparty transaction scheme based on blockchain. Peer-to-Peer Netw. Appl. 2021, 14, 1106–1117.
- Anderson, R. Security Engineering: A Guide to Building Dependable Distributed Systems; John Wiley & Sons: Hoboken, NJ, USA, 2020.
- Xinyi, Y.; Yi, Z.; He, Y. Technical characteristics and model of blockchain. In Proceedings of the 2018 10th international Conference on Communication Software and Networks (ICCSN), Chengdu, China, 6–9 July 2018.
- Ferrag, M.A.; Derdour, M.; Mukherjee, M.; Derhab, A.; Maglaras, L. Blockchain technologies for the internet of things: Research issues and challenges. IEEE Internet Things J. 2018, 6, 2188–2204.
- Xie, J.; Tang, H.; Huang, T.; Yu, F.R.; Xie, R.; Liu, J.; Liu, Y. A survey of blockchain technology applied to smart cities: Research issues and challenges. IEEE Commun. Surv. Tutor. 2019, 21, 2794–2830.
- Gai, K.; Guo, J.; Zhu, L.; Yu, S. Blockchain meets cloud computing: A survey. IEEE Commun. Surv. Tutor. 2020, 22, 2009–2030.
- Wang, W.; Huang, H.; Zhang, L.; Su, C. Secure and efficient mutual authentication protocol for smart grid under blockchain. Peer-to-Peer Netw. Appl. 2021, 14, 2681–2693.
- Wang, W.; Huang, H.; Zhang, L.; Han, Z.; Qiu, C.; Su, C. BlockSLAP: Blockchain-based secure and lightweight authentication protocol for smart grid. In Proceedings of the 2020 IEEE 19th International Conference on Trust, Security and Privacy in Computing and Communications (TrustCom), Guangzhou, China, 29 December 2020–1 January 2021.
- Taherdoost, H. A critical review of blockchain acceptance models—Blockchain technology adoption frameworks and applications. Computers 2022, 11, 24.
- Kulkarni, N.; Pise, R.; Patil, S. A Deep Dive into Blockchain Consensus Algorithms, in Blockchain for Smart Systems; Chapman and Hall/CRC: Boca Raton, FL, USA, 2022; pp. 67–82.
- Sayadi, S.; Rejeb, S.B.; Choukair, Z. Blockchain challenges and security schemes: A survey. In Proceedings of the 2018 Seventh International Conference on Communications and Networking (ComNet), Hammamet, Tunisia, 1–3 November 2018.
- Göbel, J.; Keeler, H.P.; Krzesinski, A.E.; Taylor, P.G. Bitcoin blockchain dynamics: The selfish-mine strategy in the presence of propagation delay. Perform. Eval. 2016, 104, 23–41.
- Tosh, D.K.; Shetty, S.; Liang, X.; Kamhoua, C.A.; Kwiat, K.A.; Njilla, L. Security implications of blockchain cloud with analysis of block withholding attack. In Proceedings of the 2017 17th IEEE/ACM International Symposium on Cluster, Cloud and Grid Computing (CCGRID), Madrid, Spain, 14–17 May 2017.
- Kiayias, A.; Russell, A.; David, B.; Oliynykov, R. Ouroboros: A provably secure proof-of-stake blockchain protocol. In Proceedings of the Advances in Cryptology—CRYPTO 2017: 37th Annual International Cryptology Conference, Santa Barbara, CA, USA, 20–24 August 2017; Proceedings, Part I.. Springer: Berlin/Heidelberg, Germany, 2017.
- Bhutta, M.N.M.; Khwaja, A.A.; Nadeem, A.; Ahmad, H.F.; Khan, M.K.; Hanif, M.A.; Song, H.; Alshamari, M.; Cao, Y. A survey on blockchain technology: Evolution, architecture and security. IEEE Access 2021, 9, 61048–61073.
- Singh, S.; Hosen, A.S.; Yoon, B. Blockchain security attacks, challenges, and solutions for the future distributed IoT network. IEEE Access 2021, 9, 13938–13959.
- Taherdoost, H. Blockchain Technology and Artificial Intelligence Together: A Critical Review on Applications. Appl. Sci. 2022, 12, 12948.
- Mayo, M. Frameworks for approaching the machine learning process. KDnuggets, 19 October 2018.
- Balusamy, B.; Chilamkurti, N.; Beena, L.A.; Poongodi, T. Blockchain and Machine Learning for e-Healthcare Systems. The Institution of Engineering and Technology. 2021. Available online: https://www.amazon.ca/Blockchain-Machine-Learning-Healthcare-Systems/dp/1839531142 (accessed on 1 May 2023).
- Kumari, A.; Tanwar, S.; Tyagi, S.; Kumar, N. Verification and validation techniques for streaming big data analytics in internet of things environment. IET Netw. 2019, 8, 155–163.
This entry is offline, you can click here to edit this entry!
