Businesses are reliant on data to survive in the competitive market, and data is constantly in danger of loss or theft. Loss of valuable data leads to negative consequences for both individuals and organizations. Cybersecurity is the process of protecting sensitive data from damage or theft. To successfully achieve the objectives of implementing cybersecurity at different levels, a range of procedures and standards should be followed. Cybersecurity standards determine the requirements that an organization should follow to achieve cybersecurity objectives and facilitate against cybercrimes. Cybersecurity standards demonstrate whether an information system can meet security requirements through a range of best practices and procedures. A range of standards has been established by various organizations to be employed in information systems of different sizes and types. However, it is challenging for businesses to adopt the standard that is the most appropriate based on their cybersecurity demands. Reviewing the experiences of other businesses in the industry helps organizations to adopt the most relevant cybersecurity standards and frameworks. This study presents a narrative review of the most frequently used cybersecurity standards and frameworks based on existing papers in the cybersecurity field and applications of these cybersecurity standards and frameworks in various fields to help organizations select the cybersecurity standard or framework that best fits their cybersecurity requirements.
- cybersecurity framework
- cybersecurity standard
- information security framework
- information security standard
- cybersecurity requirements
- information security requirements
1. Introduction
2. Cybersecurity Standards and Frameworks
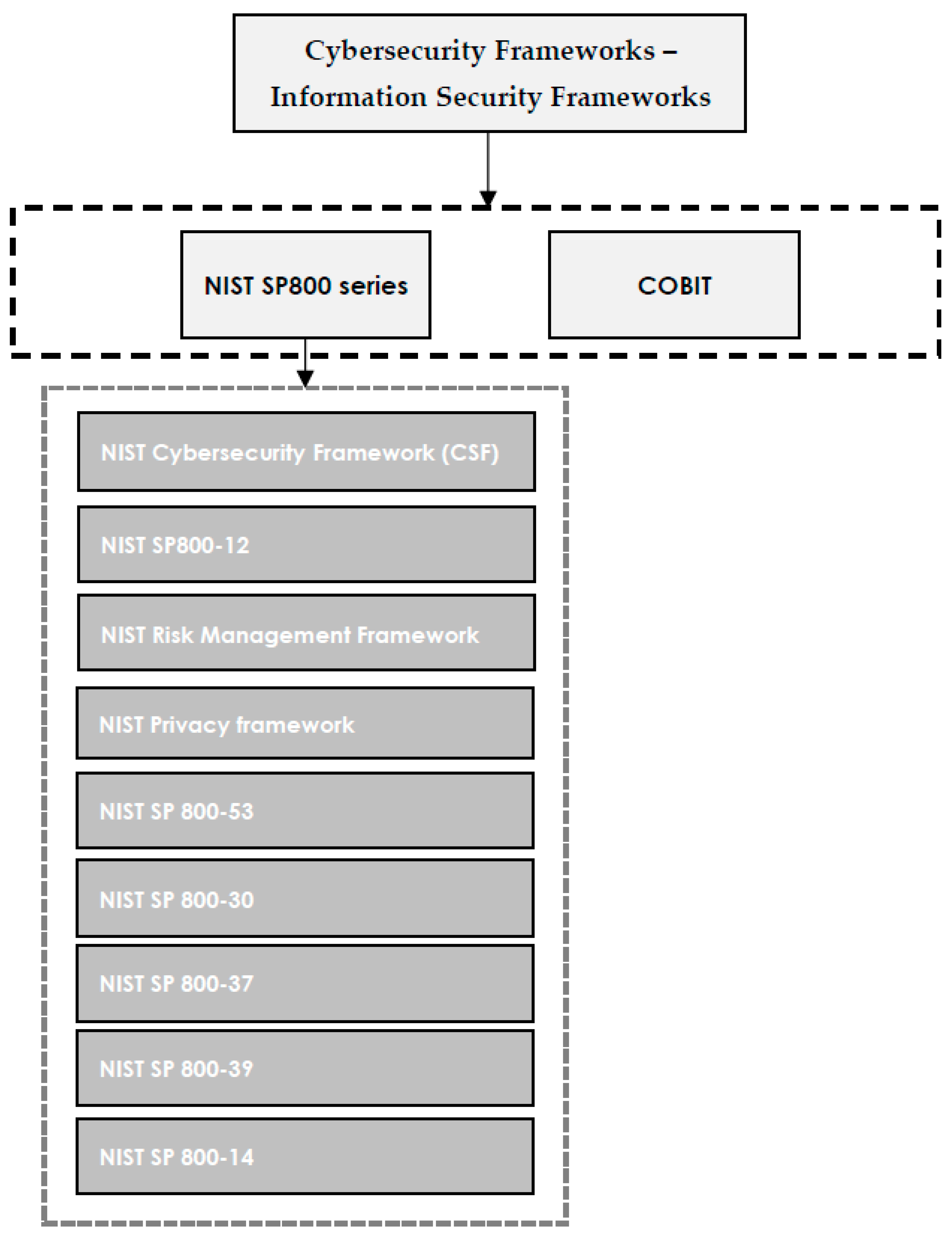
Cybersecurity standards are generally classified into two main categories, including information security standards and information security governance standards [15]. Information security standards and frameworks mainly concentrate on security concerns, such as the ISO 27000 series, ISF SOGP, NIST 800 series, SOX, and Risk IT. Selecting the most appropriate standard or framework is a serious decision that should be made based on the requirements of the organization to examine if it adequately suits the demands of the business. In some cases, employment of a single standard does not suffice to meet expectations of a business. Thus, managers need to examine whether they need to consider more than one standard [2]. Open standards and frameworks are easily available and optional to be employed. Thus, organizations can use some parts or all of the guidelines, as required, or use them in combination, integrated with other standards, to complement and strengthen other requirements [16]. Performance standards can be a policy or law to be complied with by certain countries. They may also be required by the responsible organization, association, or regulatory body to be complied with by the implementing organization [17]. A country or company is authorized to reject rules or standards published by others, or to develop their own proprietary standards or local regulatory standards [18]. The effective implementation of cybersecurity standards as guidelines or techniques which include best practices to be used in business or industry is not possible without the employment of the relevant cybersecurity framework [19,20][19][20]. Cybersecurity standards explain and provide methods one by one, specify what is expected to be done to complete the process, and clarify methods to coincide with the standard, whereas a cybersecurity framework is a general guideline that covers many components or domains that can be adopted by businesses/companies/institutions, which does not specify the steps that are required to be taken [21]. Satisfactory cybersecurity protection can be achieved by adopting a cybersecurity framework that describes the scope, implementation, and evaluation processes, and also provides a general structure and methodology for protecting critical digital assets [22]. In fact, organizations can refer to cybersecurity frameworks to realize guidelines in the successful implementation of cybersecurity standards to be better equipped to identify, detect, and respond to cyberattacks [23]. Cybersecurity frameworks are flexible and can provide users with the freedom to choose some parts or the whole model, methods, or technical practices, offering general and adoptable guidelines, as well as offering suggestions to be applied within the organization [24]. Implementation costs can be reduced as a result of the flexibility of cybersecurity frameworks. This can be effective to protect the infrastructure against cyber threats and secure critical sectors in the nation and economy. Therefore, cybersecurity frameworks (CSFs) have been developed by academic institutions, international organizations, countries, and corporations to ensure cyber resilience [25]. Businesses that seek to successfully implement cyber security standards are dependent on cybersecurity frameworks to harmonize policy, business, and technological approaches that are effective to mitigate cybersecurity issues and address cyber risks [26]. Thus, to ensure the protection of data and the infrastructure in organizations, businesses, and governments, cybersecurity standards and frameworks are required [27]. The difference between a standard and a framework is summarized in Table 1.Standard | Framework | ||||
|---|---|---|---|---|---|
|
|
3. Cybersecurity Standards—Information Security Standards
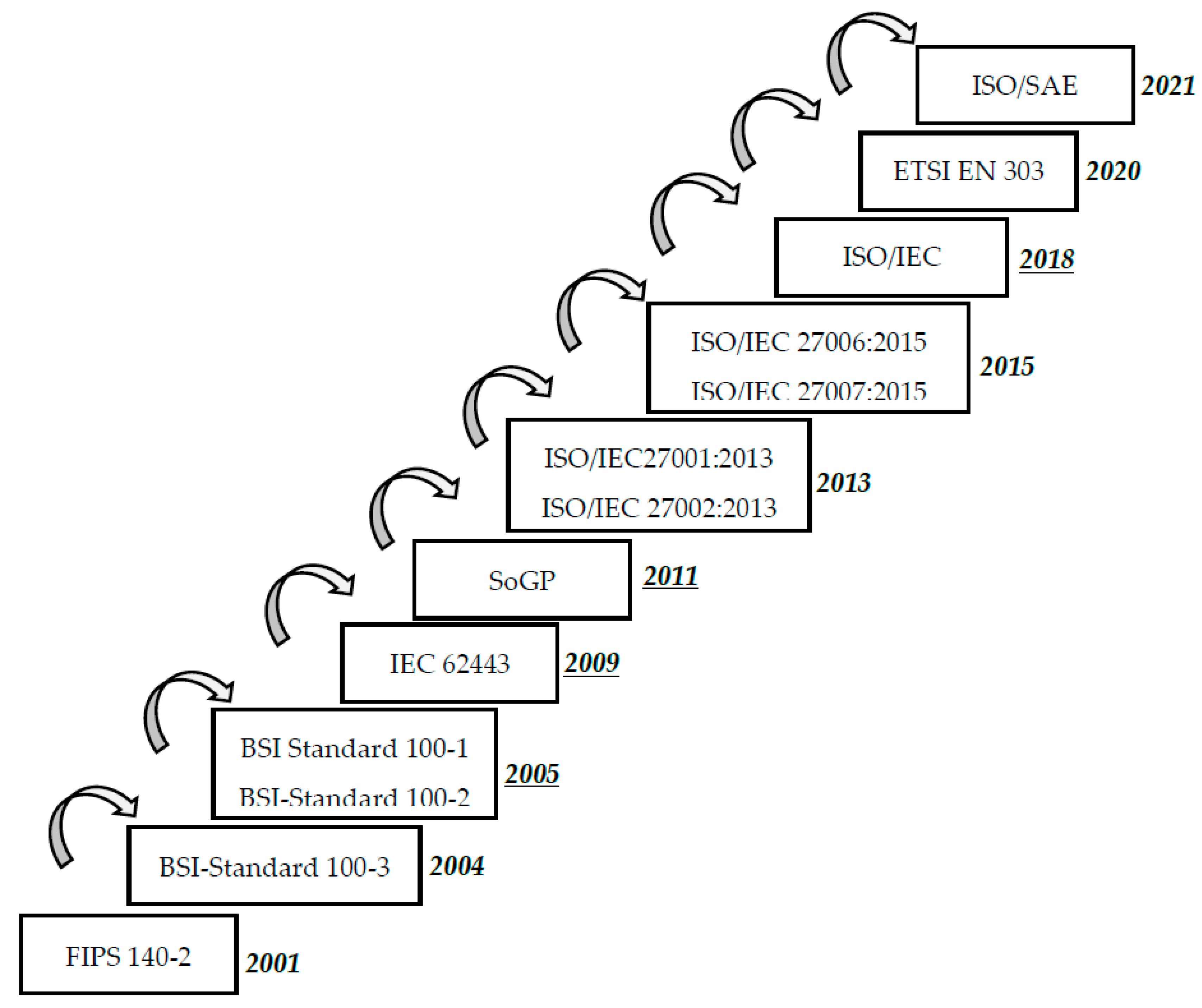
Cybersecurity standards, as key parts of IT governance, are consulted to ensure that an organization is following its policies and strategy in cybersecurity [3]. Therefore, by relying on cybersecurity standards, an organization can turn its cybersecurity policies into measurable actions. Cybersecurity standards clarify functional and assurance steps that should be taken to achieve the objectives of the organization in terms of cybersecurity. It may seem costly for a business to invest in the implementation of cybersecurity standards; however, the confidence and trust that it brings are more beneficial for the organization [28]. Written cybersecurity standard documents describe requirements to be respected by the organization and are easy to be controlled by stakeholders or relevant auditors. However, standards do not include how to achieve the standard requirements. The most popular and frequently used cybersecurity standards, are shown in Figure 1. In a general classification, the ISO 27000 series, BSI, and SoGP are provided. Additionally, some standards that are common in industry are presented in the Industry Related category.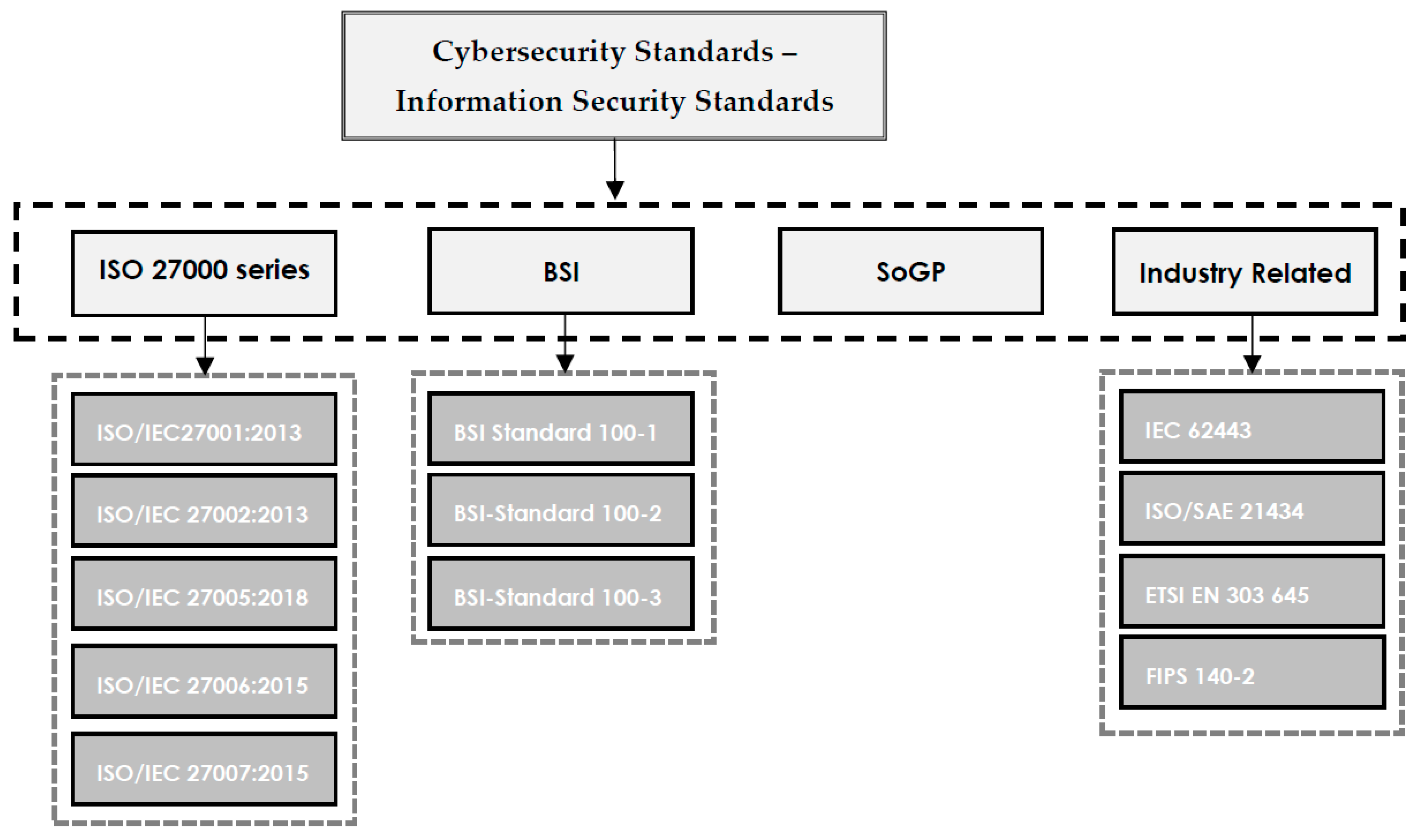
3.1. ISO/IEC 27000 Series
3.2. ISF Standard of Good Practice for Information Security
The standard of good practice (SoGP) was initially published in 1996 by the Information Security Forum (ISF), which is an international organization based in London, with staff in New York City. The Information Security Forum (ISF) is a non-profit and independent organization that concentrates on the development of best practices and benchmarking in the information security area [7]. Companies and individuals in manufacturing, financial services, transportation, chemical/pharmaceutical, retail, government, telecommunications, media, transportation, energy, and professional services from all over the world can join the ISF. The standard that includes best practices in cyber security is also revised every two years to cover the most recent best practices in information security. The standard is mainly designed to concentrate on six major aspects, including installing computers, application of critical business processes, managing security and networks, developing systems, and securing the environment for the end user [2].3.3. BSI IT-Grundschutz
BSI IT is published by a German governmental agency called Bundesamt für Sicherheit in der Informationstechnik, which is abbreviated as BSI. BSI is responsible for managing the security of computers and communication for the German government, focusing on security of computer applications, cryptography, internet security, security products, and security test laboratories [10]. BSI has provided recommendations for approaches, processes, methods, and procedures that are related to cyber security. It also covers key areas in information security that are required to be considered while setting approaches for companies and public authorities [34][31].3.4. Industry Related Standrads
Apart from the general classification of cybersecurity standards, a class of cybersecurity standards focusing on their application in business and technology, including IEC 62443, ISO/SAE 21434, and ETSI EN 303 645, is also provided here.4. Cybersecurity Frameworks—Information Security Frameworks
4.1. COBIT
4.2. The SP800 Standard Series
4.2.1. NIST Cybersecurity Framework (CSF)
4.2.1. NIST Cybersecurity Framework (CSF)
The “cybersecurity framework” was established by NIST after the executive order was signed by President Obama in 2014. Furthermore, the role of the NIST was updated by the Cybersecurity Enhancement Act of 2014 (CEA) aiming to cover the identification and development of cybersecurity risk frameworks for critical infrastructure operators and owners. Existing business operations and cybersecurity concerns are covered in this framework. Thus, it can be referred to as a foundation for a new a mechanism or cybersecurity program to improve an existing program, which can be adopted as the best practices by organizations or private sectors to secure their own critical organization [37].The “cybersecurity framework” was established by NIST after the executive order was signed by President Obama in 2014. Furthermore, the role of the NIST was updated by the Cybersecurity Enhancement Act of 2014 (CEA) aiming to cover the identification and development of cybersecurity risk frameworks for critical infrastructure operators and owners. Existing business operations and cybersecurity concerns are covered in this framework. Thus, it can be referred to as a foundation for a new a mechanism or cybersecurity program to improve an existing program, which can be adopted as the best practices by organizations or private sectors to secure their own critical organization [44].
The NIST cyber security framework (CSF) helps organizations to increase their cybersecurity measures and provides an integrated organizing structure for different approaches in cybersecurity through collecting best practices, standards, and recommendations. In other words, a framework providing a means of expressing cybersecurity requirements can be effective to point out gaps in the cybersecurity practices of an organization.The NIST cyber security framework (CSF) helps organizations to increase their cybersecurity measures and provides an integrated organizing structure for different approaches in cybersecurity through collecting best practices, standards, and recommendations. In other words, a framework providing a means of expressing cybersecurity requirements can be effective to point out gaps in the cybersecurity practices of an organization.
4.2.2. NIST Risk Management Framework (RMF)
Every organization is required to follow a process with seven steps, including preparing, categorizing, selecting, implementing, assessing, authorizing, and monitoring in order to manage its privacy and information security risks [7]. This process is designed to be a comprehensive and measurable process that is repeatable at different times. This framework can be also employed in IoT-based environments to address growing privacy and security challenges.
4.2.2. NIST Risk Management Framework (RMF)
4.2.3. NIST Privacy Framework
Every organization is required to follow a process with seven steps, including preparing, categorizing, selecting, implementing, assessing, authorizing, and monitoring in order to manage its privacy and information security risks [7]. This process is designed to be a comprehensive and measurable process that is repeatable at different times. This framework can be also employed in IoT-based environments to address growing privacy and security challenges.
The NIST privacy framework [38] concentrates on addressing the concerns of organizations to detect and respond to concerns related to privacy and establish innovative services and products while considering individual privacy [7]. This framework is based on five major functions including identifying, governing, controlling, communicating, and protecting. This framework can also help managers to address privacy concerns in IoT-based environments.4.2.3. NIST Privacy Framework
4.2.4. NIST SP800-12
The NIST privacy framework [45] concentrates on addressing the concerns of organizations to detect and respond to concerns related to privacy and establish innovative services and products while considering individual privacy [7]. This framework is based on five major functions including identifying, governing, controlling, communicating, and protecting. This framework can also help managers to address privacy concerns in IoT-based environments.
The core principles of cyber security are covered in detail in SP800-12 [10]. It was initially developed to be used in governmental and federal agencies; however, it can also be employed in other organizations focusing on computer security and controls [7]. The approach of the NIST is summarized in the SP800-12 series of standards clarifying the main elements, including the role of computer security in supporting the mission of the business, emphasizing the role of computer security in sound management, the importance of performing cost effective computer security, the importance of clearly defining accountability and responsibilities in computer security, emphasizing the role of system owners outside of the organization, emphasizing the employment of an integrated and comprehensive approach, the importance of assessing computer security on a regular basis, as well as the relationship between computer security and societal factors [7]. Thus, the handbook covers cost considerations, significant concepts, and the correlation between different security controls, eventually offering solutions to ensure that resources are secure [36].4.2.4. NIST SP800-12
4.2.5. NIST SP 800-53
The core principles of cyber security are covered in detail in SP800-12 [10]. It was initially developed to be used in governmental and federal agencies; however, it can also be employed in other organizations focusing on computer security and controls [7]. The approach of the NIST is summarized in the SP800-12 series of standards clarifying the main elements, including the role of computer security in supporting the mission of the business, emphasizing the role of computer security in sound management, the importance of performing cost effective computer security, the importance of clearly defining accountability and responsibilities in computer security, emphasizing the role of system owners outside of the organization, emphasizing the employment of an integrated and comprehensive approach, the importance of assessing computer security on a regular basis, as well as the relationship between computer security and societal factors [7]. Thus, the handbook covers cost considerations, significant concepts, and the correlation between different security controls, eventually offering solutions to ensure that resources are secure [43].
This standard mainly concentrates on privacy and controls in information systems and organizations aiming to secure assets, individuals, and operations in organizations from different cyber threats, including human error, hostile attacks, failures in structure, natural disasters, privacy risks, and threats from foreign intelligence entities [7].4.2.5. NIST SP 800-53
4.2.6. NIST SP 800-30
This standard mainly concentrates on privacy and controls in information systems and organizations aiming to secure assets, individuals, and operations in organizations from different cyber threats, including human error, hostile attacks, failures in structure, natural disasters, privacy risks, and threats from foreign intelligence entities [7].
This standard mainly concentrates on providing guidance for the development of information systems risk assessment. Risk assessment plans are conducted using NIST SP 800-30 based on the recommendations and principles of the NIST standard. This standard facilitates the understanding of cyber risks for decision makers in the organization [36]. When decision makers realize the risks and issues mentioned by a technician, they can make smart decisions based on the available resources and budget [7].4.2.6. NIST SP 800-30
4.2.7. NIST SP 800-37
This standard mainly concentrates on providing guidance for the development of information systems risk assessment. Risk assessment plans are conducted using NIST SP 800-30 based on the recommendations and principles of the NIST standard. This standard facilitates the understanding of cyber risks for decision makers in the organization [43]. When decision makers realize the risks and issues mentioned by a technician, they can make smart decisions based on the available resources and budget [7].
This standard mainly concentrates on providing guidelines to apply a risk management framework in information systems and organizations. This standard presents guidelines for organizations to implement and manage privacy and security risks regarding the best practices in information systems. The responsibility to manage privacy and security based on this standard belongs to the top management team [7].4.2.7. NIST SP 800-37
4.2.8. NIST SP 800-39
This standard mainly concentrates on providing guidelines to apply a risk management framework in information systems and organizations. This standard presents guidelines for organizations to implement and manage privacy and security risks regarding the best practices in information systems. The responsibility to manage privacy and security based on this standard belongs to the top management team [7].
This standard mainly concentrates on guiding organizations to develop a program that is integrated with the aim of managing information security risks regarding the organizational mission, operations, reputation, functions, individuals, image, and organizational assets [36]. This structured and flexible approach specifically concentrates on assessing and monitor risks and responding accordingly. Moreover, this guide towards risk is not intended to take the place of other risk-related measures in organizations [7].4.2.9. NIST SP 800-14
4.2.8. NIST SP 800-39
This standard mainly concentrates on guiding organizations to develop a program that is integrated with the aim of managing information security risks regarding the organizational mission, operations, reputation, functions, individuals, image, and organizational assets [43]. This structured and flexible approach specifically concentrates on assessing and monitor risks and responding accordingly. Moreover, this guide towards risk is not intended to take the place of other risk-related measures in organizations [7].
4.2.9. NIST SP 800-14
Commonly used security principles are described in NIST SP 800-14 to help users realize policies in cybersecurity. This standard equips organizations with requirements that they should follow to secure resources of information technology. Employment of NIST SP 800-14 ensures organizations of the readiness of their information technology security solutions in case of cyber threats [43][36].5. Discussion and Conclusion
Cybersecurity standards are significant for consideration in different organizations since they help businesses to identify best practices and methods for use to be equipped against cyber threats and the loss of valuable data [61,62]. These standards provide businesses with consistent metrics-based measures to ensure the effectiveness of methods and procedures that are employed to prevent and mitigate cyber threats [63].
As noted in this study, there are plenty of cyber security standards to be employed that are different in scope and features. In this study, an overview of the most frequently used cyber security standards based on existing papers in the cyber security field, their features and application areas, has been developed and a narrative literature review was conducted by extracting 17 relevant papers that were published from 2000 to 2022 regarding cyber security standards considering the aim of each research, its main findings, relevant industry, and employed standards. Based on the review of these 17 papers in this study, several key contributions in information security standards have been investigated.
Breda and Kiss [46] introduced MIL STD 285 and IEEE-299-2006 as two appropriate standards to implement in electromagnetic shielding emission security in manufacturing based on the design of protected areas by investigating the appropriate standard to provide protective measures. However, among 17 reviewed papers, these two standards were the main focus of just on one article.
Referring to the findings of Siponen and Willison [47] in comparing validation and application of cyber security standards, BS ISO/IEC17799: 2000, BS7799, SSE-CMM, and GASPP/GAISP are standards that are universal and general to be employed in organizations of different sizes and natures.
According to Humphreys [48], who analyzed ISO/IEC 27001 in terms of following the management PDCA cycle and controls in response to insider threats in organizations of different sizes and natures, training personnel regarding security, handling critical information, access controls, the separation of duties, regular back-ups, social engineering, and mobile devices are recognized as major controls in ISO/IEC 27001 to deal with insider threats. Additionally, another study [58] has demonstrated the effectiveness of ISO17799 in addressing insider threats.
Moreover, Hemphill and Longstreet [49] have focused on data breaches in the U.S. retail economy, considering PCI DSS that is the Payment Card Industry Data Security Standard. PCI DSS is a standard in cyber security that is employed in the finance and banking industry for credit cards, debit cards, and pre-paid cards that are issued by Discover, American Express, MasterCard and Visa, and JCB International, among others. This standard is not compulsory to be implemented in the U.S.; however, the combination of self-regulation and market forces in industries that use cards significantly motivates the response to cyber threats.
Security management guidelines and network security guidelines including ISO/IEC 17799, ISO/IEC 24743, ISO/IEC TR 13335-5, ISO/IEC 18028, and ISO/IEC TR 15947 are reviewed by Fumy [28], who concluded that the role of human awareness to combat cyber threats is the most significant issue to be considered.
Moreover, Srinivas [27] analyzes cyber-attacks, along with security requirements and measures, and discusses CIMF, which is the architecture of the cybersecurity incident management framework. Then, introduces the main purpose of CIMF that is to develop an integrated management mechanism to respond cyber threats and incidents.
To compare PCI DSS and ISO17799 [50], both standards were reviewed by Rowlingson and Winsborrow, who finally concluded that although both standards have a lot in common in terms of aim and objectives, they differ significantly in terms of scope. ISO17799 is a general standard that can be employed in a wide range of organizations; however, PCI is applicable for a limited range of information systems, and its implication costs depend on the maturity of the systems and the security processes and controls within a system.
In studies that have been developed regarding security in the micro grid industry [51], an overview of cyber security standards that may be found useful in this regard has been developed. However, in all these studies, it was concluded that there is no significant standard to guarantee the security of a smart grid, and a combination of standards [53], or the one that is the best match based on the case, should be employed [59].
Broderick [52] analyzed security standards and security regulations, and BS-7799, ISO-17799, ISO-27001, and COBIT were recognized as the most popular information security frameworks and standards that are oriented toward each other. Moreover, the ISO-17799:2005 standard does not include any guide to implement network isolation except for auditing network physical isolation. Additionally, Lai and Dai [56] suggested the provision of a technique viewpoint and a management viewpoint for network isolation purposes.
From the review, it was also concluded that despite the fact that ISO 27500 and ISO 31000 complete each other [54], they do not make explicit reference to each other. Thus, ISO 27500 is just a framework that does not specify any certain method or control.
To evaluate the performance of standards in mobile and wireless communication [55], a prototype implementation has been designed to compare CSI, ADOPT, CPC-OCSP, CRLs, and SCVP standards and relevant resulting parameters, concluding that OCSP-based schemes perform better in comparison to other standards in the ICT industry. Considering security breaches as the result of employing the Internet of Things in smart homes, one study on cybersecurity standards [60] has concentrated on ENISA and DCMS standards as applicable standards for smart homes.
The paper presented the various types of information security standards and their applications in different fields to ensure the security of data against cyber threats. Based on their nature, some standards are considered mandatory for organizations to follow in order to become certified; however, some standards, such as ISO17799, are applicable to all types of organizations, regardless of their size and type. Moreover, in some cases, the application of one standard may not fulfill all the demands of an organization, and it may be necessary to employ a combination of standards in order to ensure security against cyber threats and data loss.
References
- Vaidya, R. Cyber Security Breaches Survey 2019-GOV. UK; Department for Digital, Culture, Media and Sport: London, UK, 2019.
- Syafrizal, M.; Selamat, S.R.; Zakaria, N.A. Analysis of cybersecurity standard and framework components. Int. J. Commun. Netw. Inf. Secur. 2020, 12, 417–432.
- Baron, J.; Contreras, J.; Husovec, M.; Thumm, N. Making the Rules. The Governance of Standard Development Organizations and their Policies on Intellectual Property Rights; Publications Office of the European Union: Luxembourg, 2019.
- Taherdoost, H.; Sahibuddin, S.; Jalaliyoon, N. Smart Card Security; Technology and Adoption. Int. J. Secur. 2011, 5, 74–84.
- ISO. ISO/IEC Directives; ISO/IEC: Washington, DC, USA, 2009.
- Collier, Z.; DiMase, D.; Walters, S.; Tehranipoor, M.; Lambert, J. Cybersecurity Standards: Managing Risk and Creating Resilience. Computer 2014, 47, 70–76.
- Karie, N.M.; Sahri, N.M.; Yang, W.; Valli, C.; Kebande, V.R. A Review of Security Standards and Frameworks for IoT-Based Smart Environments. IEEE Access 2021, 9, 121975–121995.
- Knapp, K.J.; Maurer, C.; Plachkinova, M. Maintaining a cybersecurity curriculum: Professional certifications as valuable guidance. J. Inf. Syst. Educ. 2017, 28, 101–114.
- Purser, S. Standards for Cyber Security. In Best Practices in Computer Network Defense: Incident Detection and Response; Hathaway, M.E., Ed.; IOS Press: Washington, DC, USA, 2014; pp. 97–106.
- Tofan, D. Information Security Standards. J. Mob. Embed. Distrib. Syst. 2011, 3, 128–135.
- Maleh, Y.; Sahid, A.; Alazab, M.; Belaissaoui, M. IT Governance and Information Security: Guides, Standards, and Frameworks; CRC Press: Boca Raton, FL, USA, 2021.
- Taherdoost, H. Understanding of E-service Security Dimensions and its effect on Quality and Intention to Use. Inf. Comput. Secur. 2017, 25, 535–559.
- Kaur, J.; Ramkumar, K. The recent trends in cyber security: A review. J. King Saud Univ. Comput. Inf. Sci. 2021; in press.
- Dong, S.; Cao, J.; Fan, Z. A Review on Cybersecurity in Smart Local Energy Systems: Requirements, Challenges, and Standards. arXiv preprint 2021, arXiv:2108.08089.
- Arora, V. Comparing Different Information Security Standards: COBIT vs. ISO 27001; Carnegie Mellon University: Doha, Qatar, 2010.
- Krechmer, K. The Meaning of Open Standards. In Proceedings of the 38th Annual Hawaii International Conference on System Sciences, Big Island, HI, USA, 3–6 January 2005.
- Heckman, J.J.; Heinrich, C.; Smith, J. The Performance of Performance Standards. J. Hum. Resour. 2002, 37, 778–811.
- Bloor, M.; Sampson, H. Regulatory Enforcement of Labour Standards in An Outsourcing Globalized Industry: The Case of the Shipping Industry. Work Employ. Soc. 2009, 23, 711–726.
- Dedeke, A.; Masterson, K. Contrasting cybersecurity implementation frameworks (CIF) from three countries. Inf. Comput. Secur. 2019, 27, 373–392.
- Taherdoost, H.; Masrom, M. An Examination of Smart Card Technology Acceptance Using Adoption Model. In Proceedings of the 31st International Conference Information Technology Interfaces, Cavtat, Croatia, 22–25 June 2009; IEEE: Cavtat/Dubrovnik, Croatia, 2009; pp. 329–334.
- Seeburn, K. Basic Foundational Concepts Student Book: Using COBIT® 5; ISACA: Schaumburg, IL, USA, 2014.
- Antunes, M.; Maximiano, M.; Gomes, R.; Pinto, D. Information Security and Cybersecurity Management: A Case Study with SMEs in Portugal. J. Cybersecur. Priv. 2021, 1, 219–238.
- Ozkan, B.Y.; van Lingen, S.; Spruit, M. The Cybersecurity Focus Area Maturity (CYSFAM) Model. J. Cybersecur. Priv. 2021, 1, 119–139.
- Donaldson, S.; Siegel, S.; Williams, C.; Aslam, A. Enterprise Cybersecurity: How to Build a Successful Cyberdefense Program against Advanced Threats; Apress: Berkeley, CA, USA, 2015.
- Azmi, R.; Tibben, W.; Win, K. Review of cybersecurity frameworks: Context and shared concepts. J. Cyber Policy 2018, 3, 258–283.
- Shackelford, S.; Russell, S.; Haut, J. Bottoms up: A comparison of voluntary cybersecurity frameworks. UC Davis Bus. Law J. 2015, 16, 217.
- Srinivas, J.; Das, A.K.; Kumar, N. Government regulations in cyber security: Framework, standards and recommendations. Future Gener. Comput. Syst. 2019, 92, 178–188.
- Fumy, W. IT security standardisation. Netw. Secur. 2004, 2004, 6–11.
- Koza, E. Semantic Analysis of ISO/IEC 27000 Standard Series and NIST Cybersecurity Framework to Outline Differences and Consistencies in the Context of Operational and Strategic Information Security. Med. Eng. Themes 2022, 2, 26–39.
- Cordero, J.A.V. Les normes ISO/IEC com a mecanismes de responsabilitat proactiva en el Reglament General de Protecció de Dades. IDP Rev. Internet Derecho Y Política Rev. D’internet Dret I Política 2021, 33, 7.
- Schmitz, C.; Schmid, M.; Harborth, D.; Pape, S. Maturity level assessments of information security controls: An empirical analysis of practitioners assessment capabilities. Comput. Secur. 2021, 108, 102306.
- Institute, I.G. Aligning COBIT, ITIL and ISO for Business Benefit: Management Summary. A Management Briefing from ITGI and OGC. IT Gov. Inst. 2005, 1, 5–62.
- Amorim, A.C.; da Silva, M.M.; Pereira, R.; Gonçalves, M. Using agile methodologies for adopting COBIT. Inf. Syst. 2021, 101, 101496.
- Kozina, M. IT Risk Management in the enterprise using CobiT 5. In Proceedings of the Central European Conference on Information and Intelligent Systems, Varazdin, Croatia, 13–15 October 2021; Faculty of Organization and Informatics Varazdin: Varaždin, Croatia, 2021; pp. 249–256.
- Saarinen, M.-J.O. NIST SP 800-22 and GM/T 0005-2012 Tests: Clearly Obsolete, Possibly Harmful. Cryptol. Eprint Arch. 2022, 169, 1–8.
- Almuhammadi, S.; Alsaleh, M. Information security maturity model for NIST cyber security framework. Comput. Sci. Inf. Technol. 2017, 7, 51–62.
- NIST. Framework for Improving Critical Infrastructure Cybersecurity. In Cybersecurity Framework; National Institute of Standards and Technology: Gaithersburg, MD, USA, 2014; p. 41.
- NIST. NIST Privacy Framework: A Tool for Improving Privacy through Enterprise Risk Management; U.S. Departement of Commere National Institute of Standards and Technology: Gaithersburg, MD, USA, 2020; p. 43.
