Your browser does not fully support modern features. Please upgrade for a smoother experience.

Submitted Successfully!
Thank you for your contribution! You can also upload a video entry or images related to this topic.
For video creation, please contact our Academic Video Service.
| Version | Summary | Created by | Modification | Content Size | Created at | Operation |
|---|---|---|---|---|---|---|
| 1 | Imad Mahgoub | -- | 7788 | 2024-01-18 02:19:10 | | | |
| 2 | Camila Xu | Meta information modification | 7788 | 2024-01-18 02:36:08 | | |
Video Upload Options
We provide professional Academic Video Service to translate complex research into visually appealing presentations. Would you like to try it?
Cite
If you have any further questions, please contact Encyclopedia Editorial Office.
Alalwany, E.; Mahgoub, I. Security and Trust Management in the IoV. Encyclopedia. Available online: https://encyclopedia.pub/entry/53998 (accessed on 11 June 2026).
Alalwany E, Mahgoub I. Security and Trust Management in the IoV. Encyclopedia. Available at: https://encyclopedia.pub/entry/53998. Accessed June 11, 2026.
Alalwany, Easa, Imad Mahgoub. "Security and Trust Management in the IoV" Encyclopedia, https://encyclopedia.pub/entry/53998 (accessed June 11, 2026).
Alalwany, E., & Mahgoub, I. (2024, January 18). Security and Trust Management in the IoV. In Encyclopedia. https://encyclopedia.pub/entry/53998
Alalwany, Easa and Imad Mahgoub. "Security and Trust Management in the IoV." Encyclopedia. Web. 18 January, 2024.
Copy Citation
The Internet of Vehicles (IoV) is a technology that is connected to the public internet and is a subnetwork of the Internet of Things (IoT) in which vehicles with sensors are connected to a mobile and wireless network. Numerous vehicles, users, things, and networks allow nodes to communicate information with their surroundings via various communication channels. IoV aims to enhance the comfort of driving, improve energy management, secure data transmission, and prevent road accidents.
Internet of Vehicles
Internet of Things
machine learning
security
trust
1. Introduction
Today, with recent innovations in technology, the ability of different devices we use in our daily lives to connect to the internet, communicate, and exchange messages has rapidly increased. A large number of devices of different categories currently extend the internet to almost every part of the world. These devices provide different services via communication with other devices. The devices, whether a smartphone, vehicle, or vending machine, are capable of connecting to the internet and sharing data. The Internet of Things (IoT) provides various services to users in the whole network system. The IoT is also expected to increase automation levels. The IoT increases the efficiency of smart health, smart cities, and smart transportation when it is integrated with these services. The objective of this smart environment is to save money, time, lives, and energy [1][2][3].
The IoT has been implemented in the transportation industry by specialists through the development of wireless and mobile communication technologies. As a result, wireless networks have been steadily deployed on vehicles and roadways, allowing vehicles to share information with each other and with infrastructure. To make these vehicles more intelligent and secure, they are being equipped with external and internal sensors. External sensors are attached outside of the vehicle and include cameras and parking sensors, while internal sensors include automotive sensors such as brake sensors, fuel sensors, and tire pressure sensors. Vehicles equipped with sensors that communicate through a mobile and wireless network are considered part of the IoT and are referred to as the Internet of Vehicles (IoV). IoV integrates two technologies, vehicular ad hoc networks (VANETs) and the IoT, to take steps toward intelligent transportation [4][5][6][7][8]. The IoT mobilizes IoV to produce a revolution in the field. IoV is an open, integrated network system with significant controllability, manageability, and credibility that has evolved from the IoT. Numerous vehicles, users, things, and networks allow nodes to communicate information with their surroundings via various communication channels. IoV is considered one of the most significant IoT applications in the area of automobiles [9][10][11][12][13][14]. Driving safety is the main goal of many applications of IoV environments. IoV has its own set of challenges, particularly in terms of security and trust, since it has to provide highly important security functions. As with other technologies, IoV has many security vulnerabilities. Hackers could control vehicles if vulnerabilities in IoV are exposed, which could lead to traffic accidents. The security of IoVs is a critical issue for the safety of drivers and anyone using the roadways. The need for data security will increase as the number of vehicles connected to the public Internet increases.
2. Background
2.1. Trust Management in IoV
Trust is described as the probability that an individual will anticipate the behavior of another peer based on the behavior of the peer and the individual’s well-being. This definition comes from the field of psychology [15]. It is worth noting that trust is significantly influenced by the subject’s viewpoint. As a result, trust indicates the trustor’s confidence that the trustee will act in his or her best interests [16]. According to sociological research, reciprocity and cooperation among persons in social interactions are believed to build trust among individuals [17]. In the computer science field, trust is defined as a trustor’s conviction in the reliability of the target node, with the goal of achieving a trust objective under particular conditions [18]. Trust can also be viewed as an assessment made by an evaluator, which is influenced by past experiences with a particular entity and the perspectives of other trustworthy sources [19]. Trust management strategies are commonly employed to secure many network environments. To comprehend trust management approaches, it is also important to understand the basic definition of the trust concept. There is a distinction between trust and trustworthiness, which is a trait that describes reliability. Trust and reputation can be used interchangeably and at times can cause confusion. The reputation of a specific node in the network environment is defined as the opinion of that node that has been built based on recommendations of other network nodes that are either direct or indirect neighbors of the node in question. Trust concepts demonstrate the relationship existing between a trustor and trustee and that the trustor believes the trustee will fulfill its obligations. The success of trust relationships result in security and optimistic feelings, while their failure result in mistrust and insecurities. In the computer science community, the trust concept has been proven to be ideal for the protection of networks [20][21][22].
2.1.1. Trust Properties
Consideration of the concept that trust is a relationship between two entities, the trustor and trustee in this case, leads to the emergence of these attributes. In this instance, the trustee becomes the trustworthy entity. The trust properties are shown in Table 1.
Table 1. Trust properties.
| Trust Properties | Description |
|---|---|
| Direct | This attribute calculates trust value based on trustor–trustee relationships. |
| Indirect | Trust value is calculated from the suggestions and opinions of the trustor’s various neighbors. |
| Subjective | Trust value is calculated from the personal views of the trustor. |
| Objective | The parameters of the observed trustee entity are what determine the value of trust, which is derived from those parameters. |
| Local | The value of trust is exclusively accessible to the trustor and trustee and cannot be accessed by other users in the network. |
| Global | Each entity that is part of the network has its own trust value that is known by every other entity. |
| Asymmetric | This is when one entity gives trust to a second entity but the second entity does not give trust to the first entity. |
| History-dependent | Trust value is given depending on the previous behaviors of the entity under observation. |
| Context-dependent | The importance of trust depends on the surrounding circumstances. |
| Composite | Trust value is based upon various parameters. |
| Dynamic | If the initial trust value was generated with certain parameters and those values later change, the trust value will also change. |
2.1.2. Components of Trust
Direct trust: Because of the interactions between the trustor and the target vehicle, this component displays a trustor’s direct observations of a target vehicle [23]. Knowledge, in the context of some studies, can mean any information the trustor learns about the trustee [24]. This normally makes use of parameters that are dependent on the nodes and services involved. Although direct trust is more important than indirect trust, when evaluating a vehicle, a combination of the two should be considered [25]. The indirect trust component is used to display the opinions of the trustor’s neighbors about the trustee, who is the target node. Indirect trust usually considers the node’s previous encounters and experiences. In some circumstances, researchers employ both experience and reputation to explain the indirect observation. All previous experiences with a target node are included in reputation, which contributes to the formation of a global opinion about the node under observation. Experience, on the other hand, is frequently based on the interaction between the trustor and the trustee, and it strongly relies on the trustor’s confidence in the trustee’s competence to complete a task [18].
2.1.3. Attributes of Trust
Various trust attributes have to be considered when computing the components of trust mentioned earlier.
-
Similarity: This refers to the degree to which two vehicles are similar in terms of content and services. Euclidean distance is often used to describe the similarity of messages or vehicles in the literature. The direction of travel of the two nodes, which is usually the location based on trajectory similarity, is known as Euclidean distance [26].
-
Timeliness: The attribute of timeliness relates to how recently the two vehicles have interacted with each other. It is usually determined by adding the current time to the time when the interaction happened. Maintaining the timeliness of data and the trust score contributes to higher levels of trust; however, old data reveal an outmoded trust value, which can lead to negative consequences [27].
-
Duration of Interaction: This refers to the length of interaction among the two nodes. Longer interactions allow the entity to learn more about the other entity’s conduct and capabilities, and as a result, long interactions have been seen to lead to better interactions among entities, which leads to higher trust levels [28].
-
Familiarity: This attribute exhibits the level of acquaintance the two vehicles have with one another. This feature was derived from social networks, and it is worth noting that increased familiarity leads to increased trust in interpersonal relationships. Higher familiarity with the trustee is frequently a reflection of the evaluator’s past understanding and knowledge of the trustee [29].
-
Packet Delivery Ratio: This can be described as the degree of connection between the trustor and the trustee. The only criterion required to calculate direct trust toward a trustee is the packet delivery ratio. In the literature, this is typically referred to as the packet transmission rate between nodes. Furthermore, it is a main goal in the development of trust models and a key criterion for detecting harmful activity [30].
-
Frequency of Interactions: On a regular basis, the trustor and trustee communicate with one another., and this is measured by the frequency of their interactions. When two nodes communicate, they can learn each other’s communication and behavioral patterns to improve trust computations [28].
2.1.4. Trust Metrics
The proposed trust management approaches have been known to apply different metric methods to measure and evaluate trust value. These methods are:
-
Reputation-based metrics: This type of trust metric calculates trust value from the recommendations given by specific nodes in the network. These network nodes may have similar opinions about the node that has been propagated within the network. This metric method considers major opinions or global feedback regarding the node.
-
Knowledge-based metrics: This technique calculates trust value based on direct or previous experience that the node has or has gained from another specific node. These metrics help identify selfish nodes that may be part of a network.
-
Expectation-based metrics: These metric methods involve a node determining the trust of another node based on how it expects the node to act. Its expectations are based upon previous interactions with the node, received suggestions, or the initial prediction in the case of no prior communication.
-
Node-properties-based metrics: Trust calculations make use of the main parameters of proximity such as location and distance with the considered node.
-
Environmental-factors-based metrics: When measuring an IoV network, this metric takes into account environmental factors, including network density and topology.
2.1.5. Trust Computation
When trust has been established, it has to be managed throughout the duration of the target node interaction. Some commonly considered modules in trust computation are:
-
Trust Propagation: This module assists in establishing the trustworthiness of various communication system nodes based on previously established worthiness values while collaborating. It combines features from both a centralized approach, where trust is granted to entities through a single, trusted node or mechanism, and a decentralized system, where no one entity acts as a central point of control. The module’s main features are trust transitivity and trust fusion. Instead of determining each individual entity’s trust, resource computation costs in this module can be decreased by measuring trust value in a propagating network [31].
-
Trust Aggregation: Multiple network pathways can be used to disseminate different versions of a node’s trust value. When it receives diverse trust values for the node, this module aims to define a singular value based on the sum of data received. The Bayesian model, weighted sum approaches, and fuzzy logic are the most commonly used aggregation strategies. The primary principle for composing trust from the path of trust for various received values is trust aggregation.
-
Trust Update: This refers to the process of bringing trust values up to date, and it can be divided into three schemas:
- -
-
Event-driven Trust: this is where node trust is adjusted after an event or during the occurrence of a transaction.
- -
-
Time-driven trust: this is where the aggregation scheme is used to adjust the node trust value within a determined time period.
- -
-
Continuous trust update: this is mostly used to protect integrity and is used to regulate one single node task.
-
Trust Prediction: the purpose of this module is to predict trust connections between entities by utilizing selected criteria. This module predicts whether trust can develop between trusted nodes.
-
Trust Evaluation: This module often contains sections on experience, suggestions, and global knowledge. Requesting node neighbors provides experience, which is continually updated in the table of trust, from which it is communicated as a recommendation trust node. The assessed trust value is linked to the global knowledge component.
-
Trust Formation: This is the module where the trust formula is defined. To define how trust can be computed, it is necessary to establish the set of trust qualities and metrics considered by the trust formula. For the formation of the trust formula, the two trust categories of multitrust and single trust must be defined.
2.1.6. Trust Management Approaches
Entity-based approaches, data-based approaches, and integrated approaches are the three types of trust management approaches. The trust concept is related with network nodes in an entity-based approach. These methods are used to assess how trustworthy the nodes in a network are that send and receive data. Malicious nodes can subsequently be excluded from the network or isolated based on the evaluation of their trust ratings. Social trust interactions are inherited by certain existing entity-based techniques in the literature. These methods primarily consider measures that are based on a person’s reputation. As a result, the trust formula used to generate the trustee node’s trust value is mostly dependent on previous knowledge-related metrics as well as traded recommendations among various entities. Other studies look at comprehensive trust, considering not only reputation-based indicators but also the similarity aspect. In data-based systems, the concept of trust is closely associated with the integrity of the generated message, hence necessitating the assurance of data authenticity in these solutions. Utility refers to a specific helpful act or the worth of the created event compared to other actions in the same context, and it is an essential factor in determining data content worthiness. The proximity time, the type of incident that occurred, and the role of the vehicular node are some of the major trust elements considered in data utility assessments. Information-oriented methods and event-oriented methods are two types of data-driven approaches. Similarity is a term that describes how the contents of shared data are similar in terms of time and proximity criteria, and it is used to determine the value of data trust. Similarity aids in reducing the amount of data disseminated, ensuring that only meaningful information is broadcast. The primary principle of the combined trust management technique relies on entity and data-sharing trustworthiness. This module is more efficient when it comes to trust computation. The assessment of data trust value is aided by entity trustworthiness.
An example was provided to address the issue of injecting inaccurate information into safety-related events in VANETs, in which a similarity-based solution was proposed [32]. The calculation of a similarity rating is based on periodic beacons that contain position and speed information. An Echo procedure was also used to acquire a trust rating and to validate the reports by observing the vehicle’s normal and expected behavior in relation to the reported occurrence. In a VANET presented in [33], a multidimensional trust system was created for the agents. In order to require further feedback from trustworthy nodes, the system’s trust values must be maintained. When determining trustworthiness, authors take into account variables including experience, majority opinion, and priority criteria. These schemes classify nodes as having an authority role, an expert role, a seniority role, or an ordinary role. It is also worth noting that the experience factor is calculated as a result of the number of encounters. To deal with behavioral changes, the forgetting factor is introduced. Each node communicates its trustworthiness to other entities through trust messages sent to an authentic infrastructure, which later becomes a component of the reputation management center, where node trust is collected [34]. Authentic infrastructure filters trust communications based on statistical regularity, and each node then has access to updated trust data from the reputation center. Historical trust can be determined with the use of authentic center recommendations [35]. Platoon head vehicles are ranked using the reputation criteria. The system model includes servers that are used to assess the trust of vehicles, and reputation values are calculated using feedback from user vehicles. The use of iterative filtering eliminates any malicious user vehicle feedback. The server node then suggests a safe platoon leader vehicle.
2.2. Machine Learning
ML is a subfield of artificial intelligence that uses data and previous decisions to predict the future with high accuracy. ML comes in three forms: supervised, unsupervised, and reinforcement learning [36]. Highly accurate results can be ensured through the use of ML for trust evaluation in instances in which big data are processed. The high accuracy in trust evaluation when one uses big data is due to the adequate data sources big data provide [37]. Inaccurate evaluation results are common in instances in which scientists decide to use traditional trust evaluation methods in social networks as well as many other large-scale networking instances, as such instances have sophisticated data structures and generate and process vast volumes of data, thereby introducing enormous complexities. However, when it comes to handling and processing big data, using ML as the primary method provides enormous specific advantages. For trust evaluation, when dealing with big data, ML takes the lead compared with other methods in terms of the appropriateness dimension [38]. From an artificial intelligence perspective, massive convenience is evident in trust evaluation when ML is used. Artificial intelligence uses ML as its primary technology, with the simulation of human behaviors using computers being an example of a perfectly accomplished task using ML. A model for successor computations is obtained through the use of data or experiences that are already available. There is an almost perfect fit between this process and human thinking patterns. Since human beings’ subjective behavior items include trust patterns, the use of ML for trust evaluations is appropriate. ML artificial intelligence models and human behavior simulations using computers provide an almost perfect process for emulating human thinking patterns. The ML-based trust evaluation process is concise and instructive. There is usually a high degree of certainty in using ML-based trust evaluation to solve basic processes. Data processing, model selection, and final model determination are the three rough division steps of ML’s general process. The data processing step involves transforming available raw data into useful features or turning dirty raw data into meaningful features. It involves the use of, among many other methods, data cleansing, feature selection, and data fusion; these are methods that appropriately minimize high dimensions, missing values, noise, and values that are repeated. In the model selection step, the most appropriate trust evaluation model-building algorithm is selected from the many available ML algorithms. The final model selection step involves adjusting parameters and selecting the best performance achievement enabling parameters for the selected algorithm. The performance of the selected algorithm is usually significantly affected by the availed parameters’ configurations, as the algorithm has a set of parameters that should be set for its run to deliver expected results for the given input. Existing experience-based decision-making or human decision-making processes are what the ML-based trust evaluation process simulates. In addition to this process being easily understandable, implementing it is highly effective and easy. ML has a wide range of applications, including fraud detection in finance [39], personalized learning in education [40], disease diagnosis in healthcare [41], and climate modeling in environmental research [42]. ML helps solve challenges related to IoV, especially traffic flow prediction and optimization. The authors in [43] highlighted the importance of timely and reliable traffic flow information for ITS deployment. Traffic flow predictions are accurate using ML algorithms and historical and real-time traffic data. This predictive capability, which is difficult to acquire using traditional approaches, is useful for a variety of IoV applications, such as traffic congestion mitigation, fuel consumption reduction, and location-based services. In addition, the authors in [44] demonstrated how machine learning techniques can improve routing strategies in vehicular networks, including implementing a software-defined networking (SDN) architecture that incorporates a neural network (NN)-based mobility prediction. This approach guarantees uninterrupted connectivity and reduces latency [45], as well as using Q-learning-based hierarchical routing instead of traditional routing tables. This uses self-constructed adaptive Q-value tables that are based on local traffic flow. This approach enables them to achieve high delivery rates and balance network load [46]. These examples demonstrate how machine learning can effectively handle the many forms of communication and Quality of Service (QoS) needs in automotive networks, beyond the performance limitations of conventional networking systems. Moreover, the authors in [47] demonstrated the effectiveness of machine learning in predicting traffic flows, a typical time-series challenge. Because traffic flows are stochastic and nonlinear, conventional methods that rely on autoregressive moving averages frequently fail to account for these characteristics. Effectively enhancing the accuracy of predictions has been accomplished with the help of ML techniques such as kNN and support vector regression (SVR). A fundamental endeavor in intelligent transportation systems, behavior prediction is another area in which ML performs well. The authors in [48] showed that SVMs can predict lane changes. Overall, machine learning in the environment of IoV has shown its adaptability and efficacy in solving a wide range of challenges associated with predicting traffic patterns, optimizing routes, and forecasting behavior in vehicular networks.
2.2.1. Supervised Learning
Supervised learning (SL) can be categorized into regression and classification. In the classification model, the output is categorical. The most common classification models include neural networks, Naïve Bayes, support vector machines, decision tree, and K-nearest neighbor. As for the regression model, the output is continuous. Logic regression methods are commonly used in secure vehicular networks [43][49][50].
2.2.2. Unsupervised Learning
Unsupervised learning (UL) is the opposite of supervised learning because there are no used labels for the dataset. Unsupervised learning can be categorized into clustering and dimensionality reduction applications The most common clustering models are k-means and the Hidden Markov Model, which are commonly used to secure vehicular networks [49][51].
2.2.3. Reinforcement Learning
Reinforcement learning (RL) algorithms fall into two categories: model-free RL algorithms and model-based RL algorithms. Model-free RL algorithms use policy optimization and value-based algorithms as the main approaches. The primary objective of these algorithms is to come up with a strategy that helps individuals gain the best results in the long term. In value-based algorithms, the temporal difference stands for the place where the agent studies the environment and learns the most accurate method for predicting a variable’s value over a certain period of time. The learned state values are then used to improve the state of the environment. The temporal difference performs refreshes depending on the information obtained from the current assessment. In Q-learning, the Q stands for quality. The agent uses a Q-table to choose the best action for each state. It also helps with increasing the rewards generated from all the ideal actions. The State–Action–Reward–State–Action (SARSA) algorithm learns Q values depending on the functions performed by the current system. Most importantly, the Deep Q-Network (DQN) algorithm creates a matrix that enables the working agent to locate the best action so as to maximize future rewards. It should be noted, however, that an increase in the number of states and actions leads to a more complex and time-consuming Q-table characterization [52]. The primary objective of RL is to identify the circumstances under which the output of the IoT system is most highly rewarded [53]. Below are some of the terms used in this process: Agent: the elements that perform the activities. Environment: the circumstances surrounding the agent. State: the present circumstances. Reward: the response of the environment. Value: the long-term reward.
2.3. Security Requirements
Security has become a critical issue in the IoT due to the large amount of data being transmitted, the different technologies used, and the development of cloud computing systems. IoT systems are particularly vulnerable when data are transmitted from a user interface to a cloud-based service, as attackers can use loopholes in transmission links to manipulate the data. Moreover, they can take charge of cameras, the brake system as well as the alert system. In such a case, the people inside the vehicle have no control over what the vehicle can do. This is what makes IoV a high-risk technology. Despite efforts to address the challenges presented by IoV, new and more sophisticated challenges keep popping up. The various security threats are a result of the frequent availability of large amounts of data in IoV. Among the many devices and nodes involved in IoV are data, access points, base stations, sink nodes, and backbone points, making data collection security crucial. To guarantee data security, IoV experts must ensure the data are authenticated and made confidential. Other requirements include integrity, authorization, and nonrepudiation [54].
Security requirements are measures for identifying how secure an IoV network is. While IoV is vulnerable to multiple threats, researchers have identified some of the most vulnerable areas and how they can be protected from network attacks [54][55][56][57]. Below are some of the security aspects that must be considered. Figure 1 illustrates the security requirements including authentication, confidentiality, availability, data integrity, nonrepudiation, access control, privacy, and real-time guarantees.
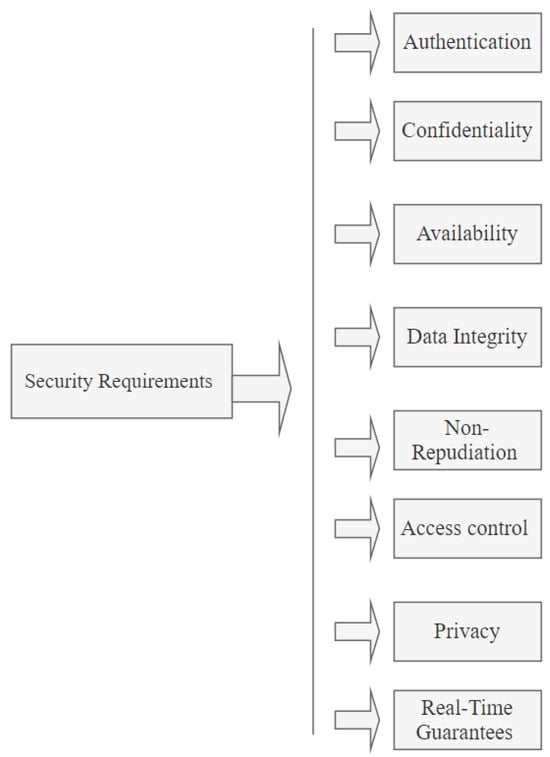
Figure 1. Security requirements in IoV.
2.3.1. Authentication
The system should not allow any form of imitation of a vehicle or vehicles trying to send information. The sensor that sends the data must be the vehicle it claims to be. The receiving sensor should also be able to differentiate between the true sender and a fake sender by scanning the ID of the sender. The chances of a masquerading node acting in the same way as a legitimate node are extremely high. As such, communication between nodes must be authenticated. Every sender must have a unique ID that can be verified through keys or passwords [58].
2.3.2. Confidentiality
Sensitive information passes through the communication channels in IoV networks. This information can have serious effects if it gets into the wrong hands. As such, an efficient system should ensure that sensitive information is secure and only the intended users can access it. Confidential information should be protected at all costs. Encryption has proven to be an effective solution in this endeavor.
2.3.3. Availability
The number of vehicle owners has increased in the past ten years. As such, there is a high likelihood of a high number of IoV users within a particular region at the same time. For this reason, network breakdowns cannot be ruled out, especially during peak hours when everyone is rushing to go home or to work. Hence, an effective system will be available at all times to all legitimate users. The entire IoT system is based on information dissemination. For this reason, information should be made available when needed; otherwise, if there are delays, it might be of no help. It is for this reason that group signature was developed to solve the availability issue.
2.3.4. Data Integrity
The information being delivered from one node to another should not be altered in any way. The content received should match what was sent. In communication that goes through various channels, malicious nodes can tamper with the message or send the wrong signals. Such tampering is dangerous because it might result in messages being interpreted differently. To ensure that the network’s integrity is intact, digital signatures can be used. The content of the message being passed from one node to the other may save a life or cause damage if modified [59].
2.3.5. Nonrepudiation
Nonrepudiation not only detects compromised nodes but also prevents the sender or receiver from denying the transmitted message. Coordination and cooperation among users of an IoT network within a particular range are crucial. For instance, information on an emergency or an accident should be communicated promptly to identify the person responsible. As such, if a user denies a sent message, the user can jeopardize the lives of other users.
2.3.6. Access Control
Access control is comparable to the police in that it ensures that every participating node performs its functions according to its roles and privileges. An efficient system must have an access control panel.
2.3.7. Privacy
A driver’s daily routine is one of the types of private information that should not be made public. No unauthorized access to the network should be allowed since it may put people’s lives at risk [60].
2.3.8. Real-Time Guarantees
Applications used in IoV are designed in such a way that they are time sensitive. For this reason, they have to disseminate information when needed and at the right time. The failure to deliver information in a timely manner can lead to accidents and unnecessary delays.
3. The Concept of IoV
3.1. The Internet of Vehicles
The unprecedented developments in computers and communication have escalated the implementation of IoV. The VANET is the previous version of IoV. IoV’s primary objective is to ensure safe driving. While IoV has been embraced by the vehicle manufacturing industry, the technology presents myriad challenges and opportunities that are yet to be explored [61].
Diverse network connections and varying road conditions are considered by intelligent vehicles that are controlled by sophisticated internal software. This software is responsible for managing and controlling vehicle systems. The software depends on information obtained from the interconnected devices and the internet. Most manufacturers decided to adopt IoV applications and start manufacturing their own cars when they discovered the process of converting vehicles from normal mobile nodes to intelligent vehicles. This discovery also brought stiff competition among renowned software-producing companies such as Apple, Google and Huawei [62].
The emergence of IoV technology made it more convenient to own and drive a vehicle. In addition to improving traffic monitoring, the technology aimed to enhance comfortable driving, improve energy management, secure data transmission, and prevent road accidents. While this was good news, the new technology came with many challenges and opportunities. Some of the issues that have still not been addressed are achieving large-scale coverage, exchanging data in a secure environment, managing diverse network connections, and dealing with vehicles with a dynamic topology [63].
3.2. Comparison of IoV and VANETs
IoV emerged as a result of the integration of the IoT and VANETs. As such, it is a more advanced version of VANETs. The primary reason for the development of IoV was to strengthen and enhance VANETs’ capabilities. While the two technologies share some similarities in terms of objectives, they also have differences that are worth discussing [64].
-
Goal: Both VANETs and IoV aim to enhance traffic safety and efficiency. However, while VANETs focus more on cost and pollutant emission efficiency, IoV focuses on commercial infotainment. Infotainment is one of the most crucial components of IoV because it helps passengers access services such as online video streaming and file downloading.
-
Network specification: IoV has a diverse network framework. The network is used for collaboration and entails communication types such as 4G, Wi-Fi, WAVE, and satellite [65].
-
Communication types: IoV has five types of communication, with each type relying on specific wireless communication technology. The five types of communication are vehicle to sensors (V2S), vehicle to road side units (V2R), possible vehicle to vehicle (V2V), vehicle to personal devices (V2P), and vehicle to the infrastructure of cellular networks (V2I) [66]. Figure 2 illustrates the types of communication used in IoV.
-
Processing competence: IoV is capable of handling large packets of global data. The system incorporates intelligent computing platforms such as fog computing, cloud computing, and edge computing, which enable it to process large amounts of data at a fast speed [67].
-
Compatibility: IoV is easy to use since all the devices used are compatible with the network, thus making it easier for information to be disseminated among the nodes in the most efficient way possible. As such, an interactive environment is created, making it possible to detect hazards early.
-
Network connectivity: Communication is a critical component of IoV networks; for this reason, IoV operates in an environment with the best communication. Moreover, it can easily switch to a stronger and more efficient network in case the current one fails.
-
Internet facilities: IoV environments enable vehicles to be connected to the internet at all times. The reliability of IoT networks depends on the speed of the internet and a high bandwidth.
-
Cloud computing: Massive quantities of data are processed on a daily basis in an IoV environment. As such, cloud computing is often regarded as the most effective approach for managing vast quantities of data. Cloud computing makes it easier for information to be collected, stored, and analyzed [68].
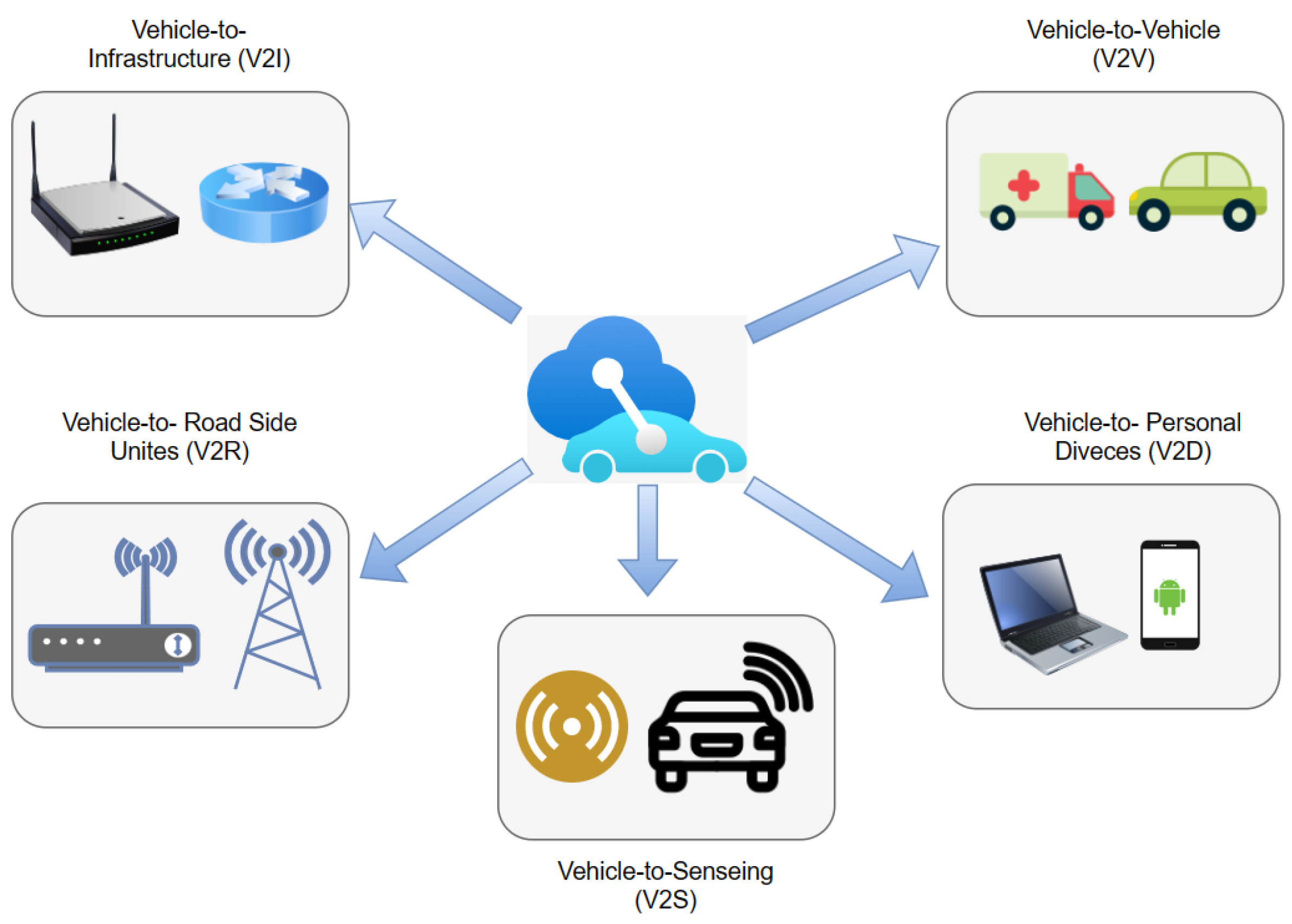
Figure 2. Types of communication used in IoV.
3.3. IoV Architecture
This subsection illustrates the suggestions of numerous researchers about various architectures for IoV. The researcher Liu Nanjie [69] suggested a “Client-Connection-Cloud” system as a three-layer architecture for IoV. The client layer collects data about driving patterns and intra-vehicle and inter-vehicular connections with surrounding vehicles by using all sensors present in the vehicle. The connection layer deals with communication among various units (vehicles, individuals, RSU, and the Internet) in an IoV system to offer vehicle-to-vehicle, vehicle-to-individuals, vehicle-to-RSU, and vehicle-to-Internet communication. In addition, the cloud layer offers services needed for executing tasks, which might not be satisfied by the restrained resources accessible within the vehicle such as mass storage, authentication, and actual-time communication.
Gandotra et al. [70] suggested a three-layer architecture for gadget interaction in which the first layer is utilized for the network region in which gadgets are connected to another device with the network control choosing either wireless or wired interaction. The next layer offers support for IP connectivity and roaming. The last layer backs up the chosen application (IoV and healthcare, among others). Other researchers in [66] proposed a seven-layer architecture: the first layer is the user communication layer, the second is the data acquisition layer, the third is the data filtering and preprocessing layer, the fourth is the business layer, the fifth is the communication layer, the sixth is the management and control layer, and the last layer is the security layer. A transparent connection among the network components is provided by this IoV architecture.
IoV structure can be broken down into four main categories: network, computing, sensing, and application, where the sensing layer collects important data about the vehicle’s surrounding environment. The data collected entail information such as the condition of the roads, object locations, and driving habits. The means of data collection is the Radio Frequency Identification Card. The network layer provides all the essential network types such as cellular networks (4G/LTE) and short-range communications (Wi-Fi, Bluetooth) between all the objects in the vehicle. This layer is also connected to the cloud. The computing layer processes, stores, and analyses data required for convenience, efficiency, safety, and risk evaluation. The last layer, the application layer, offers open and closed services. Open services include online video streaming, which is offered by internet service providers. In contrast, closed services are specific IoV applications [12][71][72]. Figure 3 shows the four main categories in IoV architecture.
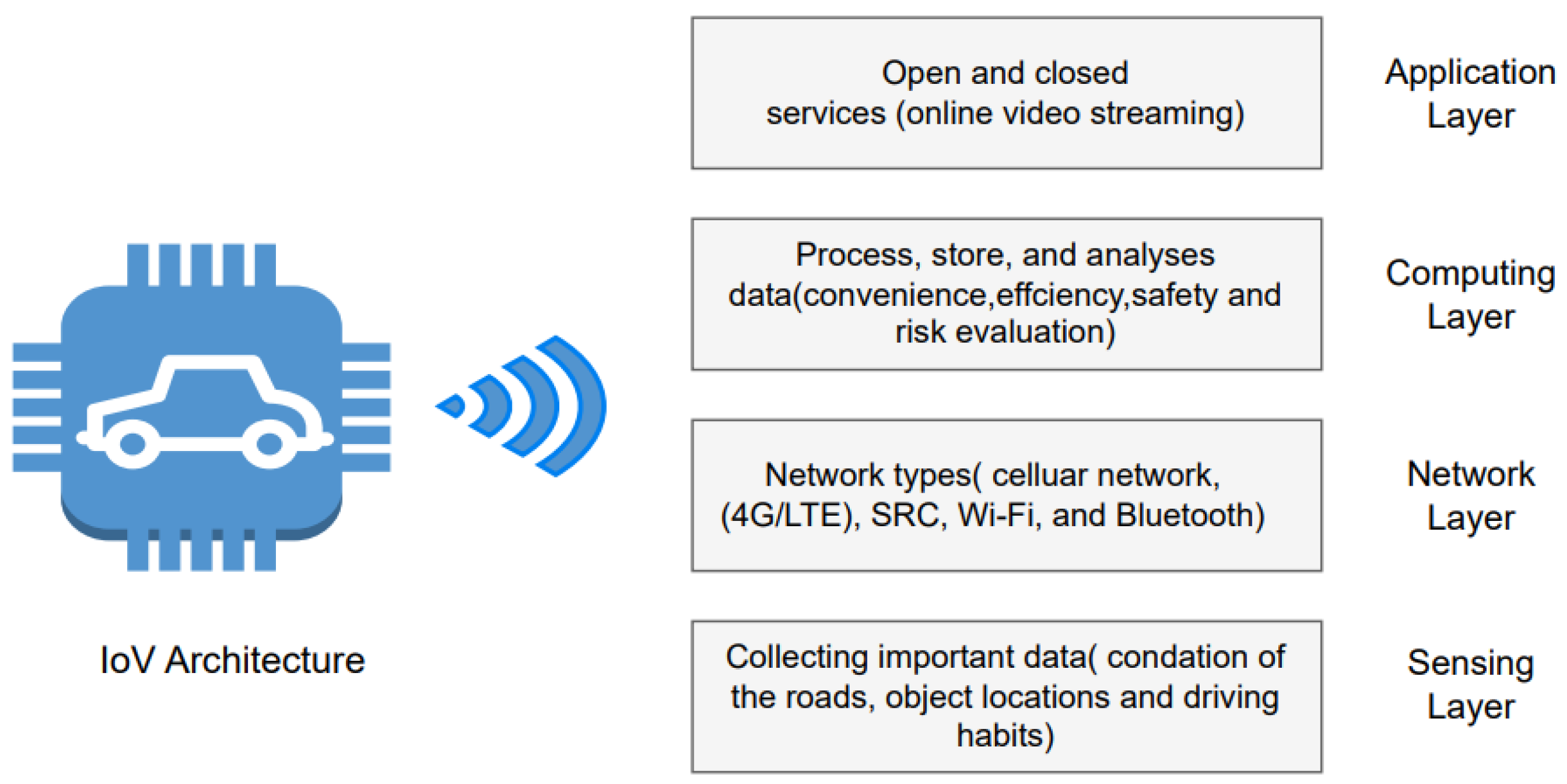
Figure 3. IoV architecture.
Different IoV architectures have been suggested by various researchers. Investigation of these architectures illustrates that some of these architectures do not consider security, while some have explained security as services. Since IoV has open network access, the security services provided on these architectures will not be sufficient for securing IoV, which will lead to different vulnerabilities that might affect the entire system. Accordingly, there is a requirement for effective security mechanisms to improve the security of any architecture.
3.4. Challenges Facing IoV
In recent years, various technologies have been integrated for the sole purpose of designing and deploying an IoV architecture. Some of these technologies are IEEE 802.11p, Microwave Access, Dedicated Short-Range Communication, Long-Term Evolution, and cloud computing [73]. While IoV is a promising field, it presents myriad challenges. Some of the bottlenecks IoV developers must grapple with include issues associated with data protection, liability, architecture, resource allocation, and diverse interconnected nodes [74][75][76].
The most common IoV network challenges are as follows:
-
Complex and diversified networks;
-
The security and reliability of services, incompatibility and accuracy of services, and limited storage capacity;
-
Data storage and management;
-
Scalability;
-
Internet provision;
-
Poor reception and weak signals that hinder the availability of satellite-based GPS systems;
-
Disruptive tolerant communication;
-
High mobility of dynamic topologies and vehicle nodes;
-
Localization issues;
-
Addressing and tracking network fragmentation.
3.5. Security Issues in IoV Communication
A middle ground exists between the smart vehicle and the cloud server. This middle ground is commonly referred to as the fog cloud-based IoV. This important component enhances the vehicle’s capabilities by enabling the vehicle to collect and process information locally and to make instant decisions during an accident rather than relying on a cloud server. For instance, several vehicles in the same vicinity can respond to a request from a vehicle within the same area instead of sending a request to the cloud, which may result in a delayed response. IoV highly depends on wireless communication for traffic flow management. For this reason, IoV is susceptible to various attacks such as data disclosure and session key leakage. To address these security issues, the following measures can be employed [61][77][78].
3.5.1. Regular Network Monitoring
Fog systems must be monitored on a regular basis to rid them of any suspicious activities. A fog network can be scanned using either static or dynamic techniques. Typically, a normal network scan involves an antivirus program and a firewall to identify threats and eliminate them to protect the network. Fog environments, however, require more security. Therefore, a new and more effective mechanism for network monitoring is required [79].
3.5.2. Encrypted Data/Communication
Electronic data produced when transmitting between fog and cloud should be protected by encryption. The two most widely used data encryption methods are the Advanced Encryption Standard (AES) algorithm and the Data Encryption Standard (DES) algorithm. The AES algorithm is more appropriate in a fog environment compared to the DES algorithm due to its suitability for sensitive data. Moreover, DES codes are easier to crack compared to AES codes [80].
3.5.3. Authentication and Key Management
During IoV deployment, authentication and key management should be employed between the different devices. Moreover, when authentication and key management are employed between fog servers and cloud servers, they enhance communication in an IoV environment [81].
3.5.4. Wireless Security Protocols
The transmission of sensitive information via mobile phones, wireless cameras, and Radio Frequency Identification (RFID) is common in an IoT environment. As such, for the information to be protected against hackers and other intruders, the wireless communication must be protected. For instance, an unauthorized user can take charge of the network by locking out authorized users, thereby preventing them from using the network. This can be carried out by downloading applications that are irrelevant to the network. Some of the most effective solutions against these kinds of attacks include the use of Wi-Fi-protected access such as WPA2 and WPA3 [82][83].
Now more than ever, IoT networks are vulnerable to cyberattacks. The most common type of attack against IoV involves manipulating and exploiting connections. In other cases, the attackers can gain access to the on-board unit (OBU) and manipulate the data there, affecting functions such as the locking system, emergency brakes, cameras, and wireless system. As such, an effective security mechanism should be capable of protecting the system’s data and nodes from external intrusion. The security of the IoV network is what determines the safety of the driver and passengers in a vehicle. The messages contained in IoV outline accident prevention procedures and methods on how to deal with malicious activity. As such, IoV networks must be protected at all costs due to their sensitivity. To maintain the integrity of the data being transmitted, they must not be altered or modified during transmission [84][85].
3.6. Security Threats and Attacks in IoV Environments
Attackers come in different forms. No matter how simple or sophisticated an attacker is, the attack will ultimately affect the integrity of the IoT network. Hence, to protect these networks, it is important to understand the existing threats. Attacks can be categorized into three types: active, passive, and malicious attacks. In active attacks, the attackers can either originate fake messages or alter the information of authentic messages. These attacks are more frequent and difficult to avoid but can easily be detected and are inexpensive to detect. Attackers usually carry out active attacks with the aim of modifying network operations. To prevent this kind of attack, physical security measures should be implemented [86]. The goal of passive attacks is to compromise the target node without changing the content of the transmitted messages. This type of attack is used by attackers to obtain dispersed data from the network. Since passive attacks do not disrupt network operations, they are difficult to detect, and since attackers do not participate in network communication, data encryption can be utilized to prevent such attacks [87]. With malicious attacks, rather than attackers benefiting from the attacks, they are instead initiated with the intent of harming participating nodes. These attacks are dangerous and can cause significant damage. Malicious attackers can even transmit false safety-critical information that puts drivers, passengers, and pedestrians in danger [56][88][89][90][91]. Below is a detailed explanation of some of the attacks to be expected in an IoV environment.
3.6.1. Wormhole Attack
This type of attack is also referred to as a tunnel attack. In this type of attack, the attacker displays the wrong information about its current location to the targeted victim. As a result, the victim node sends its messages through the fake node. Then, all the information received from the sender goes through the attacker node before flowing to the network. Such information is exposed.
3.6.2. Black Hole Attack
A black hole is formed when a vehicle drops packets or refuses to engage in communication. A black hole is akin to an empty space that no one knows exists. The attack starts with an attacker introducing itself as a legitimate node and as a shortcut to a particular destination. Then, the legitimate nodes abandon the route discovery process in favor of the shortcut. The fake node then intercepts the data packets and uses them to create confusion. Eventually, other attacks such as DoS attacks and man-in-the-middle attacks may ensue. In other words, one attack may open doors to other attacks [92].
3.6.3. Dissimulation of a GPS Attack
This refers to the act of intercepting and modifying GPS signals sent by a vehicle within a particular network. These signals are then sent to an unsuspecting receiver after being modified. As a result, the driver and passenger of the targeted vehicle make wrong decisions based on the modified message [57]. In a GPS attack, GPS signals are attacked and the exact location of the vehicle is manipulated. As such, when searching for a particular vehicle, a user may be directed to another location with a fake vehicle. A GPS spoofing attack is a common name for this kind of attack [54].
3.6.4. Denial-of-Service Attack
Every network has a bandwidth within which it operates. Hence, a denial-of-service (DoS) attack feeds a large amount of information to a particular communication channel legally. In this way, the attacker congests the channel and slows it down. While the network is down, the attacker can use the limited resources for illegal business [57]. When communication among legitimate vehicles is jammed, no form of communication can take place. This leads to confusion and panic because these vehicles depend on this communication to make informed decisions such as what routes to avoid [93]. Moreover, information relayed on the network can save lives by preventing accidents from happening. DoS attacks can be categorized into three types [94]:
-
Malicious—there is an objective behind the attack;
-
Disruptive—the attack has the potential to degrade the network;
-
Remote—the attack does not emanate from within the network.
3.6.5. Distributed Denial-of-Service
A distributed denial-of-service (DDoS) attack is a more advanced form of a DoS attack. Unlike a DoS attack, which focuses on specific targets, a DDoS attack is distributive. For this reason, it is more dangerous than a DoS attack. An attack is launched from multiple malicious vehicles to one particular node. The attack can also be launched at different times and locations with the ultimate goal of locking out legitimate users. The fact that the attack can be launched on both vehicles and infrastructure makes it a particularly dangerous type of attack.
3.6.6. Sybil Attack
In this type of attack, the targeted vehicle is made to believe there are vehicles on a particular route, even though the path is clear. As a result, the targeted vehicle takes another route. This attack is made possible by creating multiple fake IDs of a single node, thus indicating that there are multiple nodes in a particular location.
3.6.7. Man-in-the-Middle Attack (MITM)
In this case, the attacker acts as a middleman, but they impersonate both the sender and the receiver. As such, the attacker intercepts messages from both sides and sends wrong information to unsuspecting nodes. This type of attack can be either active or passive. This is one of the most dangerous types of attack because the attacker can cause massive damage, even with minimal information about the network. This type of attacker often targets roadside unit nodes because they are responsible for providing services by sending messages, updates, and resources to handle all communication requests.
3.6.8. Masquerading Attack
To masquerade is to pretend. As such, the attacker pretends to be someone else by hiding their true identity. Once that is achieved, the attacker can then act as a legitimate node with the sole intention of producing misleading messages or modifying the received messages. For instance, an attacker may receive a message indicating that the road is clear. In contrast, the attacker broadcasts that there is an accident ahead. As a result, road users may decide to take an alternative route or slow down. This type of attack disrupts traffic and may create a huge traffic jam [95].
3.6.9. Eavesdropping Attack
In this case, the attacker gains access to the network from the outside. Even though they are not an active participant in the network, the attacker is able to obtain private confidential information illegally and use it for personal gain.
3.6.10. Malware Attack
In this type of attack, malicious worms or viruses are transferred from one point to another through electronic files. The files can then infect the network instantly or gradually [96].
References
- Zantalis, F.; Koulouras, G.; Karabetsos, S.; Kandris, D. A review of machine learning and IoT in smart transportation. Future Internet 2019, 11, 94.
- Lee, I.; Lee, K. The Internet of Things (IoT): Applications, investments, and challenges for enterprises. Bus. Horizons 2015, 58, 431–440.
- Gubbi, J.; Buyya, R.; Marusic, S.; Palaniswami, M. Internet of Things (IoT): A vision, architectural elements, and future directions. Future Gener. Comput. Syst. 2013, 29, 1645–1660.
- Bhardwaj, I.; Khara, S. Research trends in architecture, security, services and applications of internet of vehicles (IOV). In Proceedings of the 2018 International Conference on Computing, Power and Communication Technologies (GUCON), Greater Noida, India, 28–29 September 2018; pp. 91–95.
- Gerla, M.; Lee, E.K.; Pau, G.; Lee, U. Internet of vehicles: From intelligent grid to autonomous cars and vehicular clouds. In Proceedings of the 2014 IEEE World Forum on Internet of Things (WF-IoT), Seoul, Republic of Korea, 6–8 March 2014; pp. 241–246.
- Karagiannis, G.; Altintas, O.; Ekici, E.; Heijenk, G.; Jarupan, B.; Lin, K.; Weil, T. Vehicular networking: A survey and tutorial on requirements, architectures, challenges, standards and solutions. IEEE Commun. Surv. Tutor. 2011, 13, 584–616.
- Ning, H.; Wang, Z. Future internet of things architecture: Like mankind neural system or social organization framework? IEEE Commun. Lett. 2011, 15, 461–463.
- Nitti, M.; Girau, R.; Floris, A.; Atzori, L. On adding the social dimension to the internet of vehicles: Friendship and middleware. In Proceedings of the 2014 IEEE International Black Sea Conference on Communications and Networking (BlackSeaCom), Odessa, Ukraine, 27–30 May 2014; pp. 134–138.
- Alam, K.M.; Saini, M.; El Saddik, A. Toward social internet of vehicles: Concept, architecture, and applications. IEEE Access 2015, 3, 343–357.
- Cheng, J.; Cheng, J.; Zhou, M.; Liu, F.; Gao, S.; Liu, C. Routing in internet of vehicles: A review. IEEE Trans. Intell. Transp. Syst. 2015, 16, 2339–2352.
- Datta, S.K.; Da Costa, R.P.F.; Härri, J.; Bonnet, C. Integrating connected vehicles in Internet of Things ecosystems: Challenges and solutions. In Proceedings of the 2016 IEEE 17th International Symposium on a World of Wireless, Mobile and Multimedia Networks (WoWMoM), Coimbra, Portugal, 21–24 June 2016; pp. 1–6.
- Yang, F.; Li, J.; Lei, T.; Wang, S. Architecture and key technologies for Internet of Vehicles: A survey. J. Commun. Inf. Networks 2017, 2, 1–17.
- Li, J.-L.; Liu, Z.-H.; Yang, F.-C. Internet of vehicles: The framework and key technology. J. Beijing Univ. Posts Telecommun. 2014, 37, 95.
- Yang, F.; Wang, S.; Li, J.; Liu, Z.; Sun, Q. An overview of internet of vehicles. China Commun. 2014, 11, 1–15.
- Ghafari, S.M.; Beheshti, A.; Joshi, A.; Paris, C.; Mahmood, A.; Yakhchi, S.; Orgun, M.A. A survey on trust prediction in online social networks. IEEE Access 2020, 8, 144292–144309.
- Jøsang, A.; Ismail, R.; Boyd, C. A survey of trust and reputation systems for online service provision. Decis. Support Syst. 2007, 43, 618–644.
- Håkansson, P.; Witmer, H. Social media and trust: A systematic literature review. J. Bus. Econ. 2015, 6, 517–524.
- Truong, N.B.; Um, T.W.; Zhou, B.; Lee, G.M. From personal experience to global reputation for trust evaluation in the social internet of things. In Proceedings of the GLOBECOM 2017—2017 IEEE Global Communications Conference, Singapore, 4–8 December 2017; pp. 1–7.
- Soleymani, S.A.; Abdullah, A.H.; Hassan, W.H.; Anisi, M.H.; Goudarzi, S.; Rezazadeh Baee, M.A.; Mandala, S. Trust management in vehicular ad hoc network: A systematic review. EURASIP J. Wirel. Commun. Netw. 2015, 2015, 146.
- Yu, Y.; Li, K.; Zhou, W.; Li, P. Trust mechanisms in wireless sensor networks: Attack analysis and countermeasures. J. Netw. Comput. Appl. 2012, 35, 867–880.
- Mohammadi, V.; Rahmani, A.M.; Darwesh, A.M.; Sahafi, A. Trust-based recommendation systems in Internet of Things: A systematic literature review. Hum. Centric Comput. Inf. Sci. 2019, 9, 1–61.
- Yan, Z.; Zhang, P.; Vasilakos, A.V. A security and trust framework for virtualized networks and software-defined networking. Secur. Commun. Netw. 2016, 9, 3059–3069.
- Wang, Y.-H. A trust management model for internet of vehicles. In Proceedings of the 2020 4th International Conference on Cryptography, Security and Privacy, Nanjing, China, 10–12 January 2020; pp. 136–140.
- Jayasinghe, U.; Otebolaku, A.; Um, T.W.; Lee, G.M. Data centric trust evaluation and prediction framework for IOT. In Proceedings of the 2017 ITU Kaleidoscope: Challenges for a Data-Driven Society (ITU K), Nanjing, China, 27–29 November 2017; pp. 1–7.
- Mahmood, A.; Zhang, W.E.; Sheng, Q.Z.; Siddiqui, S.A.; Aljubairy, A. Trust management for software-defined heterogeneous vehicular ad hoc networks. In Security, Privacy and Trust in the IoT Environment; Springer: Cham, Switzerland, 2019; pp. 203–226.
- Mahmood, A.; Siddiqui, S.A.; Zhang, W.E.; Sheng, Q.Z. A Hybrid Trust Management Model for Secure and Resource Efficient Vehicular Ad hoc Networks. In Proceedings of the 2019 20th International Conference on Parallel and Distributed Computing, Applications and Technologies (PDCAT), Gold Coast, QLD, Australia, 5–7 December 2019; pp. 154–159.
- Huang, X.; Yu, R.; Kang, J.; Zhang, Y. Distributed reputation management for secure and efficient vehicular edge computing and networks. IEEE Access 2017, 5, 25408–25420.
- Jayasinghe, U.; Lee, G.M.; Um, T.W.; Shi, Q. Machine learning based trust computational model for IoT services. IEEE Trans. Sustain. Comput. 2018, 4, 39–52.
- Xia, H.; Xiao, F.; Zhang, S.s.; Hu, C.q.; Cheng, X.z. Trustworthiness inference framework in the social Internet of Things: A context-aware approach. In Proceedings of the IEEE INFOCOM 2019—IEEE Conference on Computer Communications, Paris, France, 29 April–2 May 2019; pp. 838–846.
- Lim, J.; Keum, D.; Ko, Y.B. A stepwise and hybrid trust evaluation scheme for tactical wireless sensor networks. Sensors 2020, 20, 1108.
- Suo, D.; Sarma, S.E. Real-time trust-building schemes for mitigating malicious behaviors in connected and automated vehicles. In Proceedings of the 2019 IEEE Intelligent Transportation Systems Conference (ITSC), Auckland, New Zealand, 27–30 October 2019; pp. 1142–1149.
- Al Falasi, H.; Mohamed, N. Similarity-based trust management system for detecting fake safety messages in vanets. In Proceedings of the Internet of Vehicles-Safe and Intelligent Mobility: Second International Conference, IOV 2015, Chengdu, China, 19–21 December 2015; Springer: Berlin/Heidelberg, Germany, 2015; pp. 273–284.
- Minhas, U.F.; Zhang, J.; Tran, T.; Cohen, R. Towards expanded trust management for agents in vehicular ad-hoc networks. Int. J. Comput. Intell. Theory Pract. 2010, 5, 3–15.
- Li, X.; Liu, J.; Li, X.; Sun, W. RGTE: A reputation-based global trust establishment in VANETs. In Proceedings of the 2013 5th International Conference on Intelligent Networking and Collaborative Systems, Xi’an, China, 9–11 September 2013; pp. 210–214.
- Hu, H.; Lu, R.; Zhang, Z.; Shao, J. REPLACE: A reliable trust-based platoon service recommendation scheme in VANET. IEEE Trans. Veh. Technol. 2016, 66, 1786–1797.
- Jordan, M.I.; Mitchell, T.M. Machine learning: Trends, perspectives, and prospects. Science 2015, 349, 255–260.
- Huang, Y.; Chen, M. Improve reputation evaluation of crowdsourcing participants using multidimensional index and machine learning techniques. IEEE Access 2019, 7, 118055–118067.
- Han, G.; He, Y.; Jiang, J.; Wang, N.; Guizani, M.; Ansere, J.A. A synergetic trust model based on SVM in underwater acoustic sensor networks. IEEE Trans. Veh. Technol. 2019, 68, 11239–11247.
- Cherif, A.; Badhib, A.; Ammar, H.; Alshehri, S.; Kalkatawi, M.; Imine, A. Credit card fraud detection in the era of disruptive technologies: A systematic review. J. King Saud Univ. Comput. Inf. Sci. 2023, 35, 145–174.
- Alsharif, B.; Altaher, A.S.; Altaher, A.; Ilyas, M.; Alalwany, E. Deep Learning Technology to Recognize American Sign Language Alphabet. Sensors 2023, 23, 7970.
- Karimzadeh, M.; Vakanski, A.; Xian, M.; Zhang, B. Post-Hoc Explainability of BI-RADS Descriptors in a Multi-Task Framework for Breast Cancer Detection and Segmentation. In Proceedings of the 2023 IEEE 33rd International Workshop on Machine Learning for Signal Processing (MLSP), Rome, Italy, 17–20 September 2023; pp. 1–6.
- Rolnick, D.; Donti, P.L.; Kaack, L.H.; Kochanski, K.; Lacoste, A.; Sankaran, K.; Ross, A.S.; Milojevic-Dupont, N.; Jaques, N.; Waldman-Brown, A.; et al. Tackling climate change with machine learning. ACM Comput. Surv. (CSUR) 2022, 55, 1–96.
- Ye, H.; Liang, L.; Li, G.Y.; Kim, J.; Lu, L.; Wu, M. Machine learning for vehicular networks: Recent advances and application examples. IEEE Veh. Technol. Mag. 2018, 13, 94–101.
- Tan, K.; Bremner, D.; Le Kernec, J.; Zhang, L.; Imran, M. Machine learning in vehicular networking: An overview. Digit. Commun. Netw. 2022, 8, 18–24.
- Tang, Y.; Cheng, N.; Wu, W.; Wang, M.; Dai, Y.; Shen, X. Delay-minimization routing for heterogeneous VANETs with machine learning based mobility prediction. IEEE Trans. Veh. Technol. 2019, 68, 3967–3979.
- Li, F.; Song, X.; Chen, H.; Li, X.; Wang, Y. Hierarchical routing for vehicular ad hoc networks via reinforcement learning. IEEE Trans. Veh. Technol. 2018, 68, 1852–1865.
- Yuan, T.; Da Rocha Neto, W.; Rothenberg, C.E.; Obraczka, K.; Barakat, C.; Turletti, T. Machine learning for next-generation intelligent transportation systems: A survey. Trans. Emerg. Telecommun. Technol. 2022, 33, e4427.
- Kim, I.H.; Bong, J.H.; Park, J.; Park, S. Prediction of driver’s intention of lane change by augmenting sensor information using machine learning techniques. Sensors 2017, 17, 1350.
- Caruana, R.; Niculescu-Mizil, A. An empirical comparison of supervised learning algorithms. In Proceedings of the 23rd International Conference on Machine Learning, Pittsburgh, PA, USA, 25–29 June 2006; pp. 161–168.
- Alotaibi, Y.; Ilyas, M. Ensemble-Learning Framework for Intrusion Detection to Enhance Internet of Things’ Devices Security. Sensors 2023, 23, 5568.
- Alloghani, M.; Al-Jumeily, D.; Mustafina, J.; Hussain, A.; Aljaaf, A.J. A systematic review on supervised and unsupervised machine learning algorithms for data science. In Supervised and Unsupervised Learning for Data Science; Springer: Cham, Switzerland, 2020; pp. 3–21.
- Akanksha, E.; Sharma, N.; Gulati, K. Review on reinforcement learning, research evolution and scope of application. In Proceedings of the 2021 5th International Conference on Computing Methodologies and Communication (ICCMC), Erode, India, 8–10 April 2021; pp. 1416–1423.
- Zhou, Z.; Oguz, O.S.; Leibold, M.; Buss, M. A general framework to increase safety of learning algorithms for dynamical systems based on region of attraction estimation. IEEE Trans. Robot. 2020, 36, 1472–1490.
- Talpur, A.; Gurusamy, M. Machine learning for security in vehicular networks: A comprehensive survey. IEEE Commun. Surv. Tutor. 2021, 24, 346–379.
- Sun, Y.; Wu, L.; Wu, S.; Li, S.; Zhang, T.; Zhang, L.; Xu, J.; Xiong, Y. Security and Privacy in the Internet of Vehicles. In Proceedings of the 2015 International Conference on Identification, Information, and Knowledge in the Internet of Things (IIKI), Beijing, China, 22–23 October 2015; pp. 116–121.
- Bagga, P.; Das, A.K.; Wazid, M.; Rodrigues, J.J.; Park, Y. Authentication protocols in internet of vehicles: Taxonomy, analysis, and challenges. IEEE Access 2020, 8, 54314–54344.
- Samad, A.; Alam, S.; Mohammed, S.; Bhukhari, M. Internet of vehicles (IoV) requirements, attacks and countermeasures. In Proceedings of the 12th INDIACom—5th International Conference on Computing for Sustainable Global Development, New Delhi, India, 14–16 March 2018; pp. 1–4.
- Daeinabi, A.; Rahbar, A.G. Detection of malicious vehicles (DMV) through monitoring in vehicular ad-hoc networks. Multimed. Tools Appl. 2013, 66, 325–338.
- Mokhtar, B.; Azab, M. Survey on security issues in vehicular ad hoc networks. Alex. Eng. J. 2015, 54, 1115–1126.
- Sun, Y.; Wu, L.; Wu, S.; Li, S.; Zhang, T.; Zhang, L.; Xu, J.; Xiong, Y.; Cui, X. Attacks and countermeasures in the internet of vehicles. Ann. Telecommun. 2017, 72, 283–295.
- Fadhil, J.A.; Sarhan, Q.I. Internet of Vehicles (IoV): A survey of challenges and solutions. In Proceedings of the 2020 21st International Arab Conference on Information Technology (ACIT), Giza, Egypt, 28–30 November 2020; pp. 1–10.
- Cheng, X.; Zhang, R.; Yang, L. Wireless toward the era of intelligent vehicles. IEEE Internet Things J. 2018, 6, 188–202.
- Zhang, W.; Xi, X. The innovation and development of Internet of Vehicles. China Commun. 2016, 13, 122–127.
- Sharma, S.; Kaushik, B. A survey on internet of vehicles: Applications, security issues & solutions. Veh. Commun. 2019, 20, 100182.
- Zheng, K.; Zheng, Q.; Chatzimisios, P.; Xiang, W.; Zhou, Y. Heterogeneous vehicular networking: A survey on architecture, challenges, and solutions. IEEE Commun. Surv. Tutor. 2015, 17, 2377–2396.
- Contreras-Castillo, J.; Zeadally, S.; Guerrero Ibáñez, J.A. A seven-layered model architecture for Internet of Vehicles. J. Inf. Telecommun. 2017, 1, 4–22.
- Darwish, T.S.; Bakar, K.A. Fog based intelligent transportation big data analytics in the internet of vehicles environment: Motivations, architecture, challenges, and critical issues. IEEE Access 2018, 6, 15679–15701.
- Lopez, H.J.D.; Siller, M.; Huerta, I. Internet of vehicles: Cloud and fog computing approaches. In Proceedings of the 2017 IEEE International Conference on Service Operations and Logistics, and Informatics (SOLI), Bari, Italy, 18–20 September 2017; pp. 211–216.
- Liu, N. Internet of Vehicles: Your next connection. Huawei WinWin 2011, 11, 23–28.
- Gandotra, P.; Jha, R.K.; Jain, S. A survey on device-to-device (D2D) communication: Architecture and security issues. J. Netw. Comput. Appl. 2017, 78, 9–29.
- Liu, K.; Xu, X.; Chen, M.; Liu, B.; Wu, L.; Lee, V.C. A hierarchical architecture for the future internet of vehicles. IEEE Commun. Mag. 2019, 57, 41–47.
- Wu, W.; Yang, Z.; Li, K. Internet of Vehicles and applications. In Internet of Things; Elsevier: Amsterdam, The Netherlands, 2016; pp. 299–317.
- Wan, J.; Zhang, D.; Zhao, S.; Yang, L.T.; Lloret, J. Context-aware vehicular cyber-physical systems with cloud support: Architecture, challenges, and solutions. IEEE Commun. Mag. 2014, 52, 106–113.
- Mahmood, Z. Connected vehicles in the IoV: Concepts, technologies and architectures. In Connected Vehicles in the Internet of Things: Concepts, Technologies and Frameworks for the IoV; Springer: Berlin/Heidelberg, Germany, 2020; pp. 3–18.
- Peng, H. Connected and automated vehicles: The roles of dynamics and control. Mech. Eng. 2016, 138, S4.
- Qureshi, K.N.; Din, S.; Jeon, G.; Piccialli, F. Internet of vehicles: Key technologies, network model, solutions and challenges with future aspects. IEEE Trans. Intell. Transp. Syst. 2020, 22, 1777–1786.
- Thakur, A.; Malekian, R. Fog computing for detecting vehicular congestion, an internet of vehicles based approach: A review. IEEE Intell. Transp. Syst. Mag. 2019, 11, 8–16.
- Huang, C.; Lu, R.; Choo, K.K.R. Vehicular fog computing: Architecture, use case, and security and forensic challenges. IEEE Commun. Mag. 2017, 55, 105–111.
- Wazid, M.; Bagga, P.; Das, A.K.; Shetty, S.; Rodrigues, J.J.; Park, Y. AKM-IoV: Authenticated key management protocol in fog computing-based Internet of vehicles deployment. IEEE Internet Things J. 2019, 6, 8804–8817.
- Vishwanath, A.; Peruri, R.; He, J.S. Security in Fog Computing through Encryption; DigitalCommons@ Kennesaw State University: Kennesaw, GA, USA, 2016.
- Khan, S.; Parkinson, S.; Qin, Y. Fog computing security: A review of current applications and security solutions. J. Cloud Comput. 2017, 6, 1–22.
- Lin, C.C.; Deng, D.J.; Yao, C.C. Resource allocation in vehicular cloud computing systems with heterogeneous vehicles and roadside units. IEEE Internet Things J. 2017, 5, 3692–3700.
- Xu, W.; Shi, W.; Lyu, F.; Zhou, H.; Cheng, N.; Shen, X. Throughput analysis of vehicular internet access via roadside WiFi hotspot. IEEE Trans. Veh. Technol. 2019, 68, 3980–3991.
- Hasrouny, H.; Samhat, A.E.; Bassil, C.; Laouiti, A. VANet security challenges and solutions: A survey. Veh. Commun. 2017, 7, 7–20.
- Tanwar, S.; Vora, J.; Tyagi, S.; Kumar, N.; Obaidat, M.S. A systematic review on security issues in vehicular ad hoc network. Secur. Priv. 2018, 1, e39.
- Gür, G.; Bahtiyar, Ş.; Alagöz, F. Security analysis of computer networks: Key concepts and methodologies. In Modeling and Simulation of Computer Networks and Systems; Elsevier: Amsterdam, The Netherlands, 2015; pp. 861–898.
- Kim, S. Blockchain for a trust network among intelligent vehicles. In Advances in Computers; Elsevier: Amsterdam, The Netherlands, 2018; Volume 111, pp. 43–68.
- Shahid, M.A.; Jaekel, A.; Ezeife, C.; Al-Ajmi, Q.; Saini, I. Review of potential security attacks in VANET. In Proceedings of the 2018 Majan International Conference (MIC), Muscat, Oman, 19–20 March 2018; pp. 1–4.
- Tangade, S.S.; Manvi, S.S. A survey on attacks, security and trust management solutions in VANETs. In Proceedings of the 2013 Fourth International Conference on Computing, Communications and Networking Technologies (ICCCNT), Tiruchengode, India, 4–6 July 2013; pp. 1–6.
- Manvi, S.S.; Tangade, S. A survey on authentication schemes in VANETs for secured communication. Veh. Commun. 2017, 9, 19–30.
- Sharma, N.; Chauhan, N.; Chand, N. Security challenges in Internet of Vehicles (IoV) environment. In Proceedings of the 2018 First International Conference on Secure Cyber Computing and Communication (ICSCCC), Jalandhar, India, 15–17 December 2018; pp. 203–207.
- La, V.H.; Cavalli, A.R. Security attacks and solutions in vehicular ad hoc networks: A survey. Int. J. AdHoc Netw. Syst. (IJANS) 2014, 4, 1–20.
- Rawat, A.; Sharma, S.; Sushil, R. VANET: Security attacks and its possible solutions. J. Inf. Oper. Manag. 2012, 3, 301–304.
- Kim, Y.; Kim, I.; Shim, C.Y. A taxonomy for DOS attacks in VANET. In Proceedings of the 2014 14th International Symposium on Communications and Information Technologies (ISCIT), Incheon, Republic of Korea, 24–26 September 2014; pp. 26–27.
- Bariah, L.; Shehada, D.; Salahat, E.; Yeun, C.Y. Recent advances in VANET security: A survey. In Proceedings of the 2015 IEEE 82nd Vehicular Technology Conference (VTC2015-Fall), Boston, MA, USA, 6–9 September 2015; pp. 1–7.
- Gai, F.; Zhang, J.; Zhu, P.; Jiang, X. Ratee-based trust management system for internet of vehicles. In Proceedings of the Wireless Algorithms, Systems, and Applications: 12th International Conference, WASA 2017, Guilin, China, 19–21 June 2017; Springer: Berlin/Heidelberg, Germany, 2017; pp. 344–355.
More
Information
Subjects:
Others
Contributors
MDPI registered users' name will be linked to their SciProfiles pages. To register with us, please refer to https://encyclopedia.pub/register
:
View Times:
769
Revisions:
2 times
(View History)
Update Date:
18 Jan 2024
Notice
You are not a member of the advisory board for this topic. If you want to update advisory board member profile, please contact office@encyclopedia.pub.
OK
Confirm
Only members of the Encyclopedia advisory board for this topic are allowed to note entries. Would you like to become an advisory board member of the Encyclopedia?
Yes
No
${ textCharacter }/${ maxCharacter }
Submit
Cancel
Back
Comments
${ item }
|
More
No more~
There is no comment~
${ textCharacter }/${ maxCharacter }
Submit
Cancel
${ selectedItem.replyTextCharacter }/${ selectedItem.replyMaxCharacter }
Submit
Cancel
Confirm
Are you sure to Delete?
Yes
No





