
| Version | Summary | Created by | Modification | Content Size | Created at | Operation |
|---|---|---|---|---|---|---|
| 1 | Dr. Sita Rani | -- | 2850 | 2022-11-30 06:21:32 | | | |
| 2 | Amina Yu | + 2 word(s) | 2852 | 2022-11-30 06:49:59 | | | | |
| 3 | Amina Yu | Meta information modification | 2852 | 2022-12-01 01:39:53 | | |
Video Upload Options
A mobile agent is a software application that moves naturally among hosts in a uniform and non-uniform environment; it starts with one host and then moves onto the next in order to divide data between clients. The mobile paradigm is utilized in a wide assortment of medical care applications such as the medical information of a patient, the recovery of clinical information, the incorporation of information pertaining to their wellbeing, dynamic help, telemedicine, obtaining clinical data, patient administration, and so on. The accompanying security issues have grown in tandem with the complexity and improvements in mobile agent technologies. As mobile agents work in an insecure environment, their security is a top priority when communicating and exchanging data and information. Data integrity, data confidentiality and authentication, on-repudiation, denial of service, and access control, are all key security concerns with mobile agent migration.
1. Introduction
-
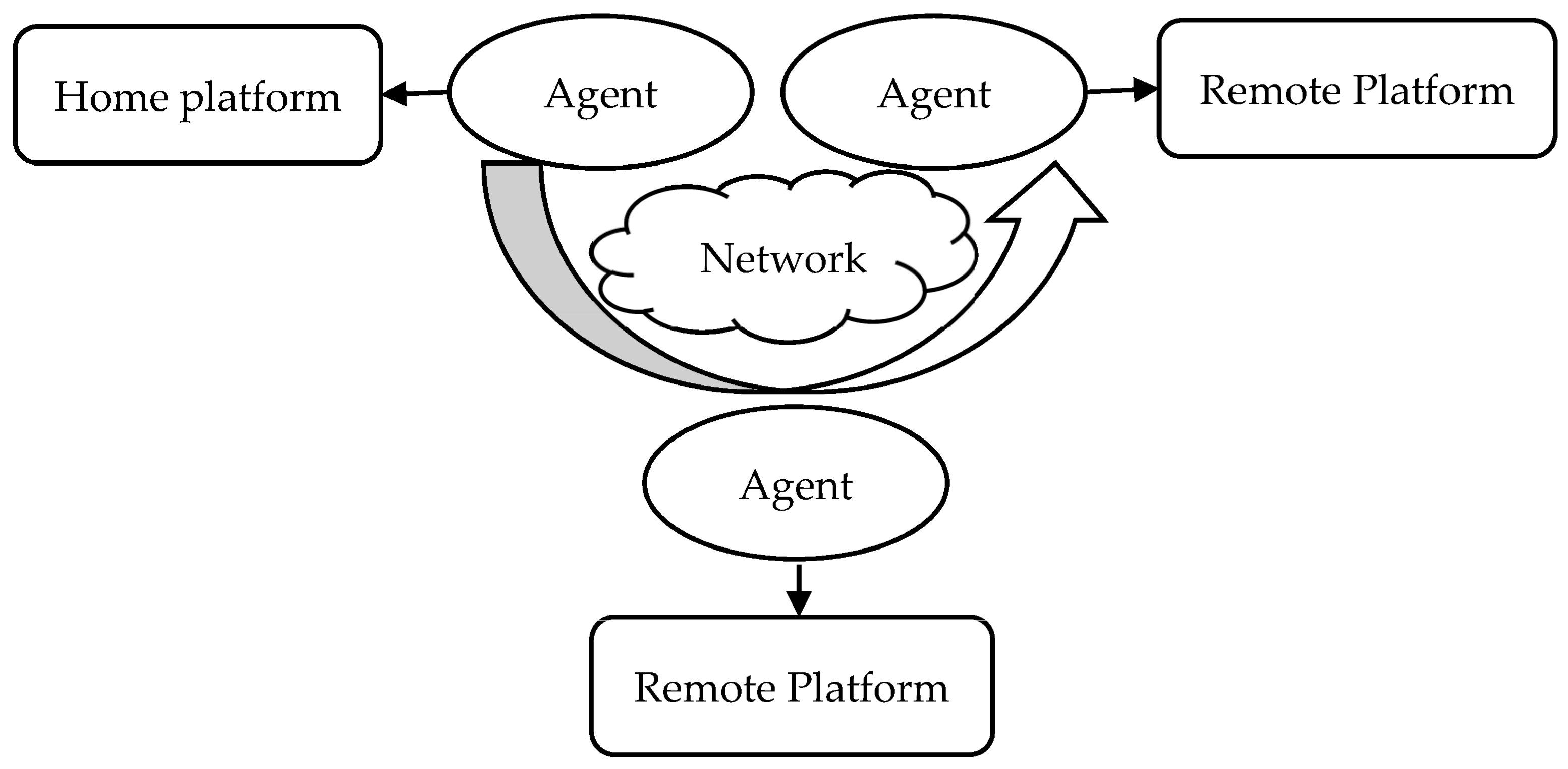
Mobility: Mobile agents can freeze an operation on one platform and continue with the operation on another (i.e., inside a different region. This is often referred to as agent migration) [5].
-
Individualism: Each mobile agent is guided by a program that is especially written to achieve at least one goal. The operations of mobile agents are entirely governed by this code, with no direct intervention from other groups.
-
Reactivity: Mobile agents respond to environmental changes in order to accomplish their objectives.
-
Proactivity: Mobile agents change their current circumstances and they take a few attempts to accomplish their objectives.
-
Sociability refers to a mobile agent’s ability to interact with other mobile agents. This is important because some agents are only made aware of their present situation via communication with other agents.
1.1. Protection of Mobile Agents
-
Assault from agents on platforms;
-
Agent-to-Agent Assaults;
-
Assault from platforms on agents;
-
Additional Assault to Agent Platform.
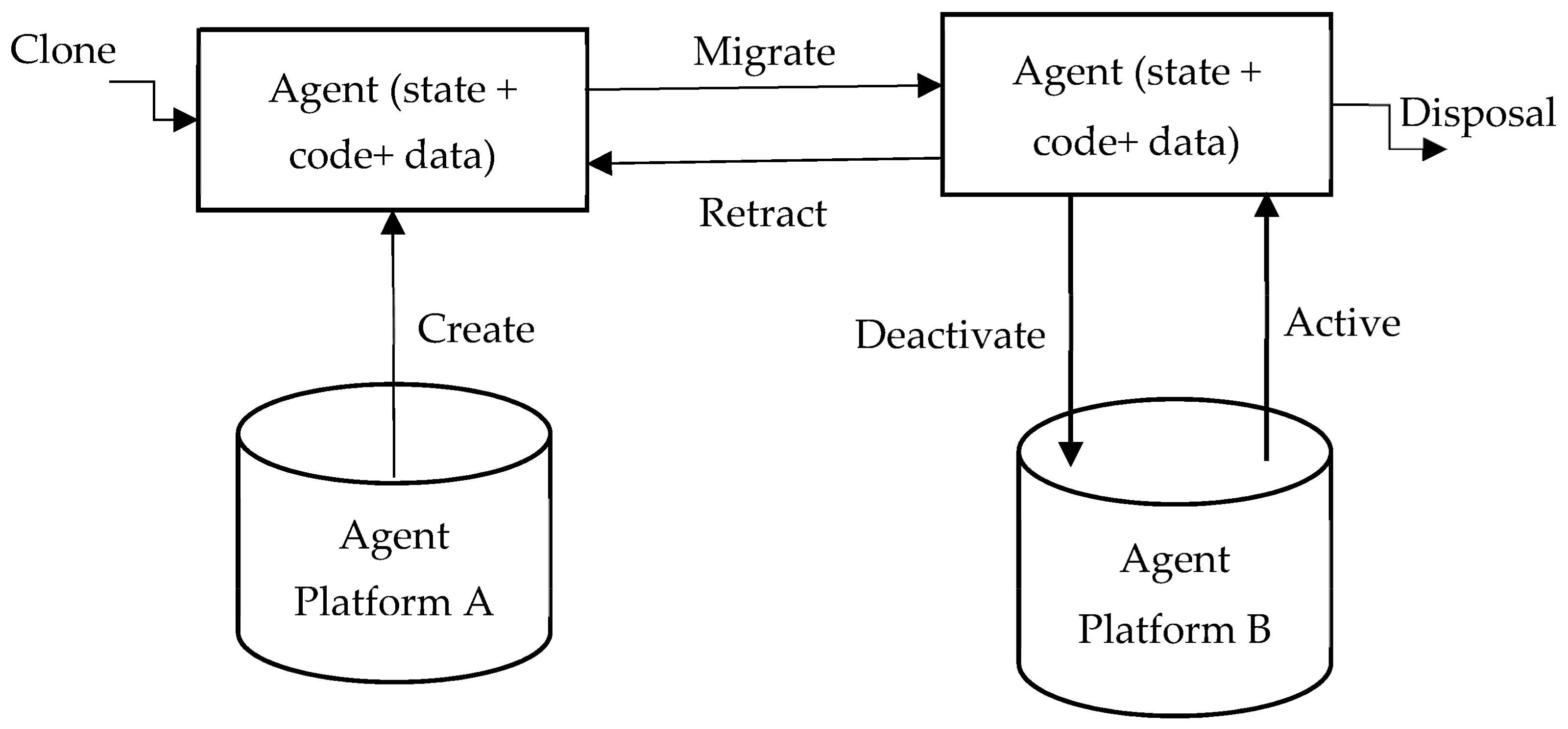
1.2. Mobile Agent Life-Cycle
-
Creation: A new mobile agent is made, and the conditions of the mobile agent are initiated.
-
Cloning: A specialist copy is made, and the present status of the first is duplicated in order to create cloning agents.
-
Dispatch: A mobile agent moves to another host.
-
Deactivation: The state of a mobile agent is saved in the repositories when it is in standby mode.
-
Activation: The state of a deactivated mobile agent is restored from the repositories and applied to the lifetime mobile agent.
-
Retraction: A mobile agent can converse with another agent and the stage.
-
Disposal: The life-cycle of a mobile agent ends.
-
Communication: Interactions between mobile agents and platforms.
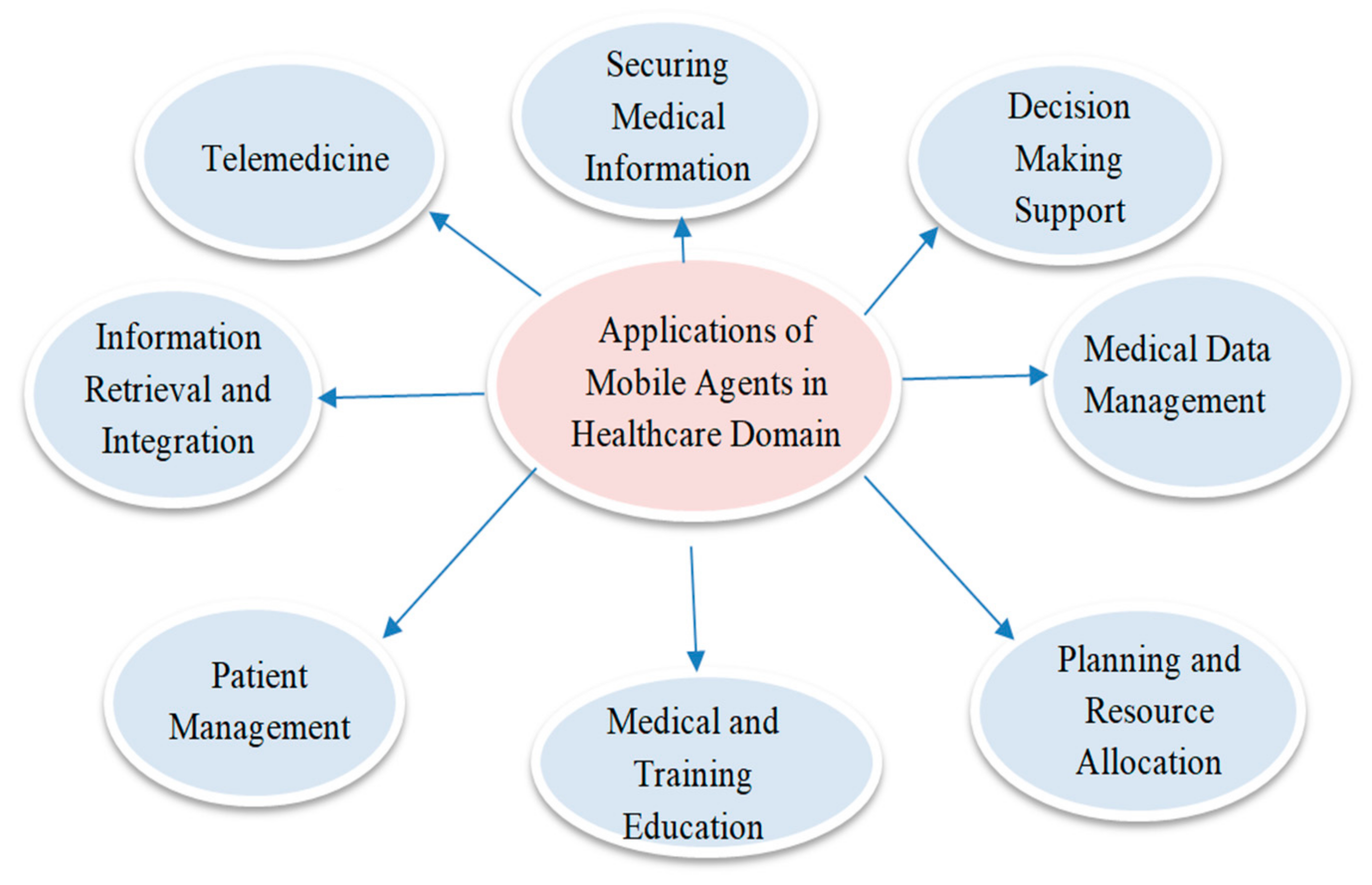
2. Utilization of Mobile Agents in the Medical Care Domain
-
Health Data Management: Acquiring, analyzing, and protecting medical information [13].
-
Information Retrieval: Retrieving medical information from heterogeneous databases.
-
Decision-Making Support: Assisting healthcare workers with procedures, including treatments and diagnostics.
-
Telemedicine: Systems focused on remotely monitoring the situation with patients, thus allowing for a wide range of assessments.
-
Securing Medical Information: Approaches to working, bearing in mind the wellbeing and security of patient information.
Requirement of Security
-
Confidentiality: Security of information and data (state + data + code) [6] among platforms and agents.
-
Data integrity: Data and information [15] should not be interfered with by a third party.
-
Availability: Data and information requested by the platform or agents should be easily accessible.
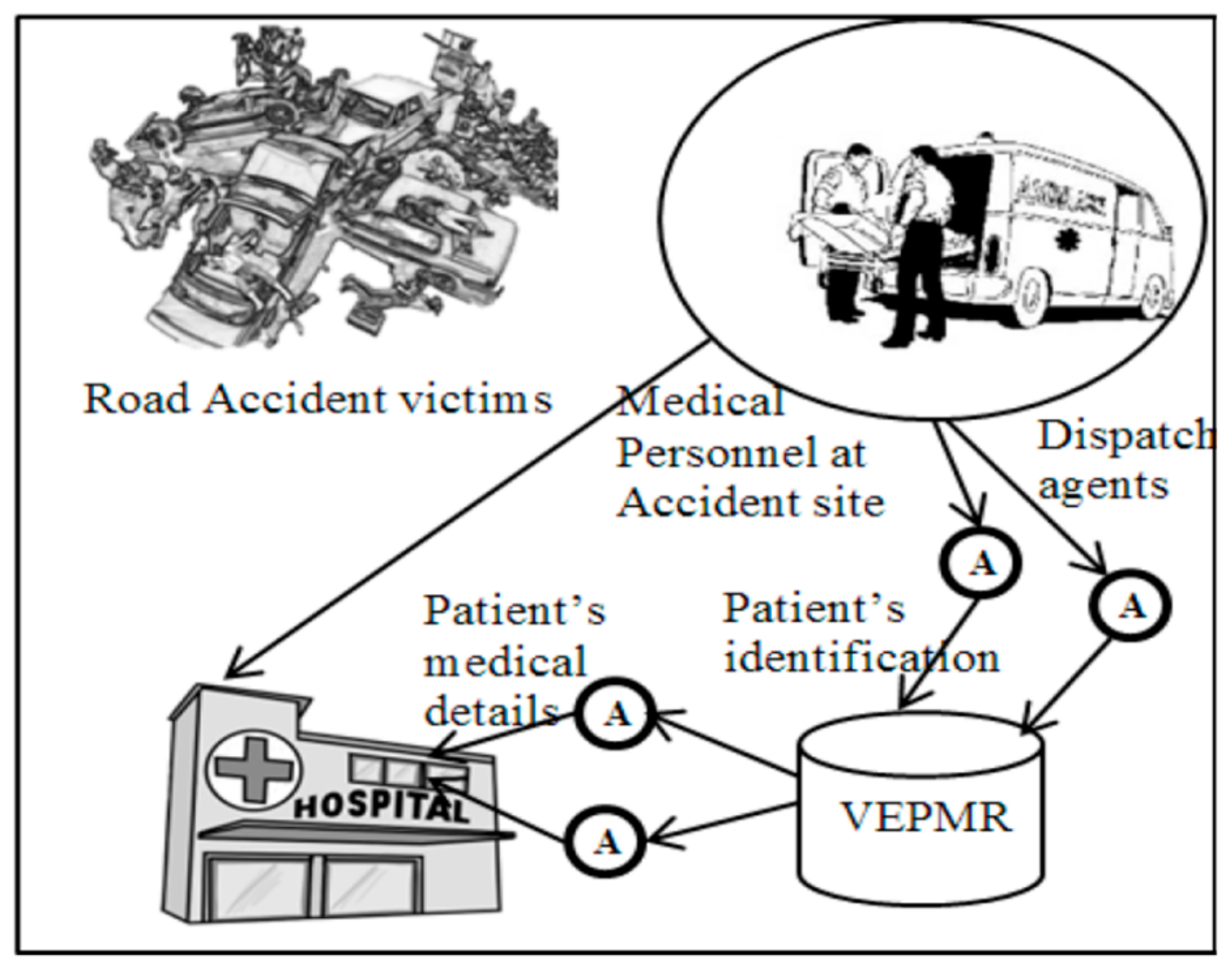
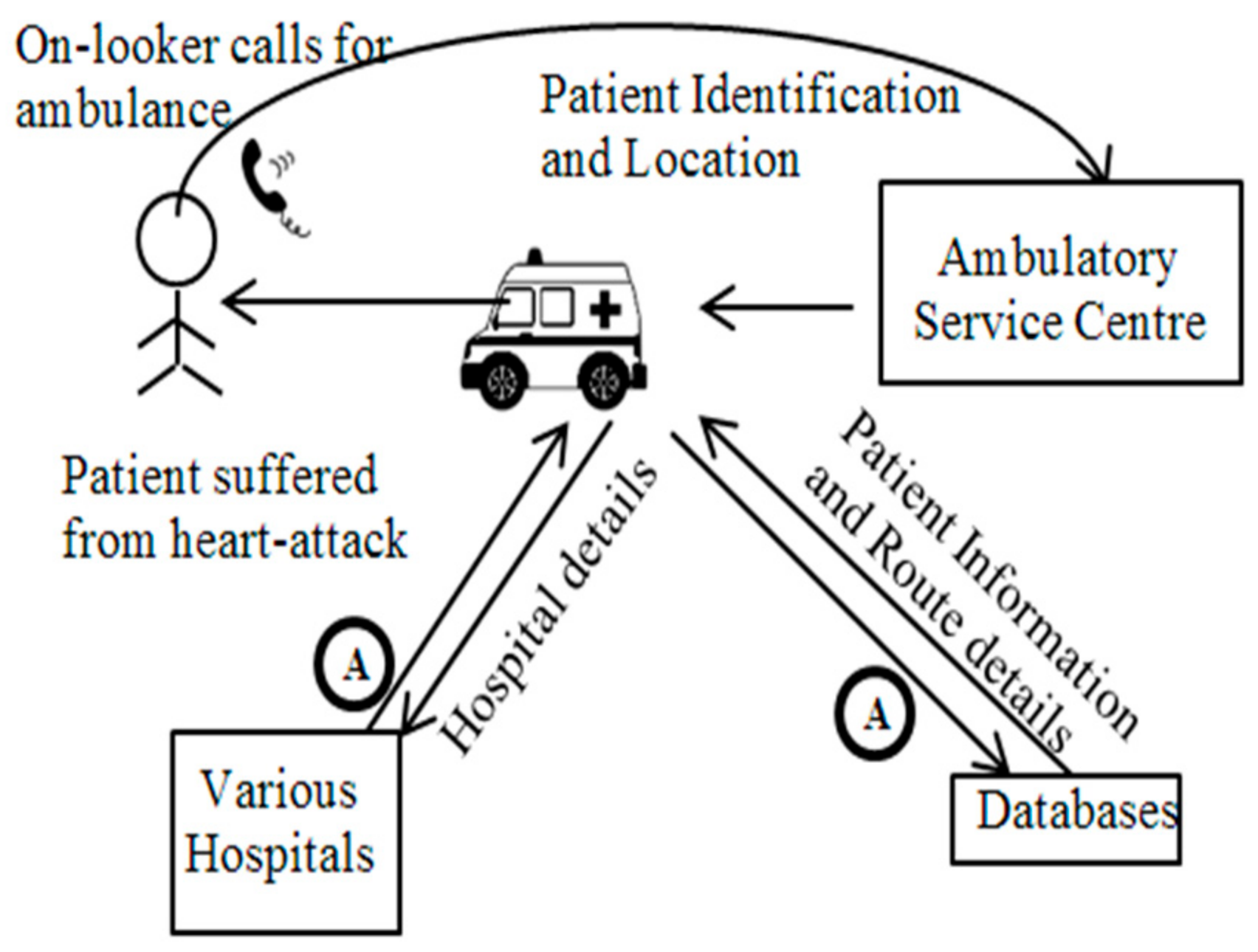
3. Verifiable, Secure Mobile Agent Migration in Healthcare Systems Using a Polynomial-Based Threshold Secret Sharing Scheme with a Blowfish Algorithm
-
A patient arrived at the hospital, and the medical faculty requested the patient’s vital clinical records via a VI (Visualized Interface).
-
A MAS (Mobile Agent Scheduler) [16] dispatched portable specialists to outside organizations and emergency clinics, in order to solicit and assemble data. When the portable specialist arrived at the outside organization, it finished the check assessment initiated by the MAS of the outside establishment, accumulated data from the outside foundation’s CIS (Clinical-information Index Storage), and it continued its journey to the organization.
-
After visiting all of the required institutions, the mobile agents returned to the organization at which they were assigned. The list items were saved in the CIS and displayed via the VI, which allowed the specialists to make better decisions.
References
- Tardo, J.; Valente, L. Mobile agent security and Telescript. In COMPCON’96. Technologies for the Information Superhighway Digest of Papers; IEEE: Piscataway, NJ, USA, 2002; pp. 58–63.
- Narad, M.S.K. Group Authentication Using Back-propagation Neural Network. Int. J. Adv. Res. Comput. Commun. Eng. 2017, 6, 272–278.
- Yao, M. A Security Architecture for Protecting Dynamic Components of Mobile Agents. Doctoral Dissertation, Queensland University of Technology, Brisbane City, QLD, Australia, 2004.
- Chen, T.-L.; Chung, Y.-F.; Lin, F.Y.S. Deployment of Secure Mobile Agents for Medical Information Systems. J. Med. Syst. 2011, 36, 2493–2503.
- Esparza, O.; Soriano, M.; Muñoz, J.L.; Forné, J. A protocol for detecting malicious hosts based on limiting the execution time of mobile agents. In Proceedings of the Eighth IEEE Symposium on Computers and Communications. ISCC 2003, Kemer-Antalya Turkey, 3 July 2003.
- Al-Jaljouli, R.; Abawajy, J.H. Secure Mobile Agent-based E-Negotiation for On-Line Trading. In Proceedings of the 2007 IEEE International Symposium on Signal Processing and Information Technology, Giza, Egypt, 15–18 December 2007; pp. 610–615.
- Jansen, W. Countermeasures for mobile agent security. Comput. Commun. 2000, 23, 1667–1676.
- Bagga, P.; Hans, R. Applications of Mobile Agents in Healthcare Domain: A Literature Survey. Int. J. Grid Distrib. Comput. 2015, 8, 55–72.
- Cavalcante, R.C.; Bittencourt, I.I.; da Silva, A.P.; Silva, M.; Costa, E.; Santos, R. A survey of security in multi-agent systems. Expert Syst. Appl. 2012, 39, 4835–4846.
- Kumar, P.; Singhal, N.; Singh, S. Anonymous Scheme for Secure Mobile Agent Migration Using Mignotte’s Sequence and Back Propagation Artificial Neural Networks. Int. J. Comput. Inf. Syst. Ind. Manag. Appl. 2021, 13, 192–199.
- Santos-Pereira, C.; Augusto, A.B.; Cruz-Correia, R.; Correia, M.E. A secure RBAC mobile agent access control model for healthcare institutions. In Proceedings of the 26th IEEE International Symposium on Computer-Based Medical Systems, Porto, Portugal, 20–22 June 2013; pp. 349–354.
- Vieira-Marques, P.M.; Robles, S.; Cucurull, J.; Cruz-Correia, R.J.; Navarro, G.; Marti, R.; Navarro-Arribas, G. Secure Integration of Distributed Medical Data Using Mobile Agents. IEEE Intell. Syst. 2006, 21, 47–54.
- Fortino, G.; Trunfio, P. Internet of Things Based on Smart Objects; Springer: Berlin/Heidelberg, Germany, 2014.
- Kumar, P.; Vatsa, A.K. Novel Security Architecture and Mechanism for Identity based Information Retrieval System in MANET. Int. J. Mob. Adhoc Netw. 2011, 1, 397–404.
- van der Haak, M.; Wolff, A.; Brandner, R.; Drings, P.; Wannenmacher, M.; Wetter, T. Data security and protection in cross-institutional electronic patient records. Int. J. Med. Inform. 2003, 70, 117–130.
- Fong, C.-H.; Parr, G.; Morrow, P. Security Schemes for a Mobile Agent Based Network and System Management Framework. J. Netw. Syst. Manag. 2010, 19, 230–256.
- Burstein, F.; Zaslavsky, A.; Arora, N. Context-aware mobile agents for decision-making support in healthcare emergency applications. In International Workshop on Context Modeling and Decision Support: 05/07/2005-05/07/2005; CEUR Workshop Proceedings: Vienna, Austria, 2005; Volume 144.
- Orgun, B.; Vu, J. HL7 ontology and mobile agents for interoperability in heterogeneous medical information systems. Comput. Biol. Med. 2006, 36, 817–836.
- Chaouch, Z.; Tamali, M. A Mobile Agent-Based Technique for Medical Monitoring (Supports of Patients with Diabetes). Int. J. Comput. Model. Algorithms Med. 2014, 4, 17–32.
- Hsu, W.-S.; Pan, J.-I. Secure Mobile Agent for Telemedicine Based on P2P Networks. J. Med. Syst. 2013, 37, 9947.
- Pouyan, A.A.; Ekrami, S.; Taban, M. A Distributed E-health Model Using Mobile Agents. In Proceedings of the Seventh International Conference on Autonomic and Autonomous Systems, Venice/Mestre, Italy, 22–27 May 2011; pp. 7–12. Available online: http://www.thinkmind.org/index.php?view=article&articleid=icas_2011_1_20_20065 (accessed on 15 August 2021).
- Benachenhou, L.; Pierre, S. Protection of a mobile agent with a reference clone. Comput. Commun. 2006, 29, 268–278.
- Biswas, A.K.; Dasgupta, M. Two polynomials based (t, n) threshold secret sharing scheme with cheating detection. Cryptologia 2020, 44, 357–370.
- El-Yahyaoui, A.; EL Kettani, M.D.E.-C. A Verifiable Fully Homomorphic Encryption Scheme for Cloud Computing Security. Technologies 2019, 7, 21.
- Garcia-Perez, A.; Cegarra-Navarro, J.G.; Sallos, M.P.; Martinez-Caro, E.; Chinnaswamy, A. Resilience in healthcare systems: Cyber security and digital transformation. Technovation 2022.
- Patel, K. Performance analysis of AES, DES and Blowfish cryptographic algorithms on small and large data files. Int. J. Inf. Technol. 2019, 11, 813–819.
- Demster, B. Managing Information and Security in Healthcare; Bloomsbury Publishing: London, UK, 2013.





