
| Version | Summary | Created by | Modification | Content Size | Created at | Operation |
|---|---|---|---|---|---|---|
| 1 | Abdullah M. Almuhaideb | -- | 5489 | 2022-08-11 20:43:03 | | | |
| 2 | Peter Tang | Meta information modification | 5489 | 2022-08-12 03:32:59 | | |
Video Upload Options
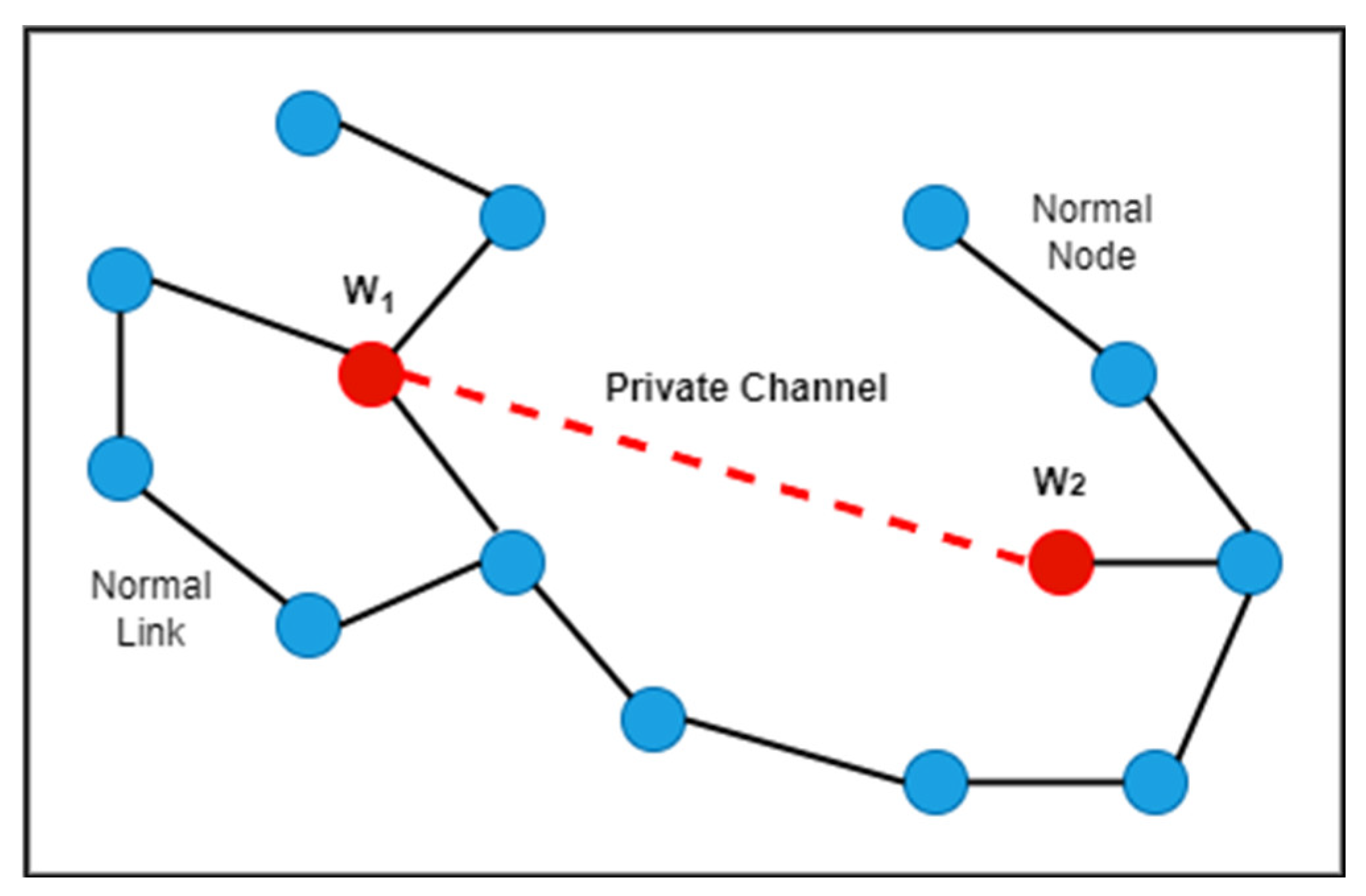
The popularity of wireless sensor networks for establishing different communication systems is increasing daily. A wireless network consists of sensors prone to various security threats. These sensor nodes make a wireless network vulnerable to denial-of-service attacks. One of them is a wormhole attack that uses a low latency link between two malicious sensor nodes and affects the routing paths of the entire network. This attack is brutal as it is resistant to many cryptographic schemes and hard to observe within the network.
1. Introduction
|
Year |
Main Focus of Survey |
Major Contributions |
Enhancements in this research |
|---|---|---|---|
|
2020 |
Survey wormhole attack detection and prevention techniques in WSN |
Mohit et al. [12] reviewed schemes such as WGDD, RTT, Packet leaches, AOMDV, ANN, and high-power transmission. The advantages and disadvantages of these schemes are listed along with the author’s remarks about the schemes. However, a performance analysis based on quality assessment was not included. |
This research presents a detailed performance analysis, including critical analysis and results comparison, and identified the gaps in all existing schemes. |
|
2018 |
Detection and prevention analysis of wormhole attacks in wireless sensor networks |
Kumar et al. [13] presented a comparative analysis of several techniques, including reputation-based routing, Packet leashes, Beacon nodes, LITEWORP, and algorithms using active nodes. However, the study did not include the strengths and limitations of the existing schemes. |
This research presents a detailed critical analysis and comparative analysis of the schemes and identified gaps. |
|
2018 |
Review intrusion detection of wormhole attacks in IoT |
Goyal et al. [14] compared several existing techniques, including the use of the hound packet, distributed detection algorithm, modified AODV, node connectivity, Merkle tree, and AODV protocol for recognising and preventing wormhole attacks, including the constraints of all the schemes. However, strengths were not specified. |
This research presents a comprehensive comparative analysis of all existing schemes and detailed critical analysis. |
|
2019 |
Review techniques used against wormhole attacks on wireless sensor networks |
Farjamnia et al. [15] presented a review of the existing models (including AOVD with different sizes, ADT, T-AOVD, AOMDV, and DV-Hop with different sizes). The advantages and disadvantages of the models were specified. |
This research presents a detailed literature review along with a solution to identify gaps in the existing schemes. |
|
2020 |
Schemes to detect wormholes in WSNs |
Umashankar et al. [16] presented a detailed review of the literature on wormhole attack detection. However, the latest schemes were not included. The advantages and disadvantages of the existing schemes were not specified. |
This research presents all the latest schemes, including AI- and ML-based schemes, and a detailed critical analysis of all existing schemes. |
|
2019 |
Survey the detection and prevention of wormhole attacks in mobile ad hoc networks |
Anju et.al. [17] presented several existing schemes of wormhole recognition, including AODV, RTT, Neighbour Discovery, and Hop count. However, the strengths of the schemes were not specified, and the presented survey was not systematic. |
This research presents all existing schemes in detail and identifies a better technique. Moreover, challenges are specified for future research. |
|
2018 |
Survey approaches and measures in detecting wormhole attacks in WSNs |
Diksha et al. [18] presented a literature review on different location time, cluster-base, public key encapsulation, moving average indicator, hop count, and RTT-based approaches. However, it is not a systematic survey and not all the pros and cons of the schemes were elaborated in detail. |
This research presents a detailed literature review of existing techniques along with a comprehensive critical analysis. It also includes AI- and ML-based schemes. |
|
2018 |
Techniques and challenges in detecting wormhole attacks in WSNs |
Padmarpriya et al. [19] presented challenges in WSN concerning the limited bandwidth, time, power management, design constraints, and security. The schemes of wormhole recognition were presented on a category basis. However, there was neither a critical analysis of schemes nor a quality assessment of research articles. |
This research presents a comprehensive critical analysis of all existing schemes. Moreover, research gaps and challenges are identified. |
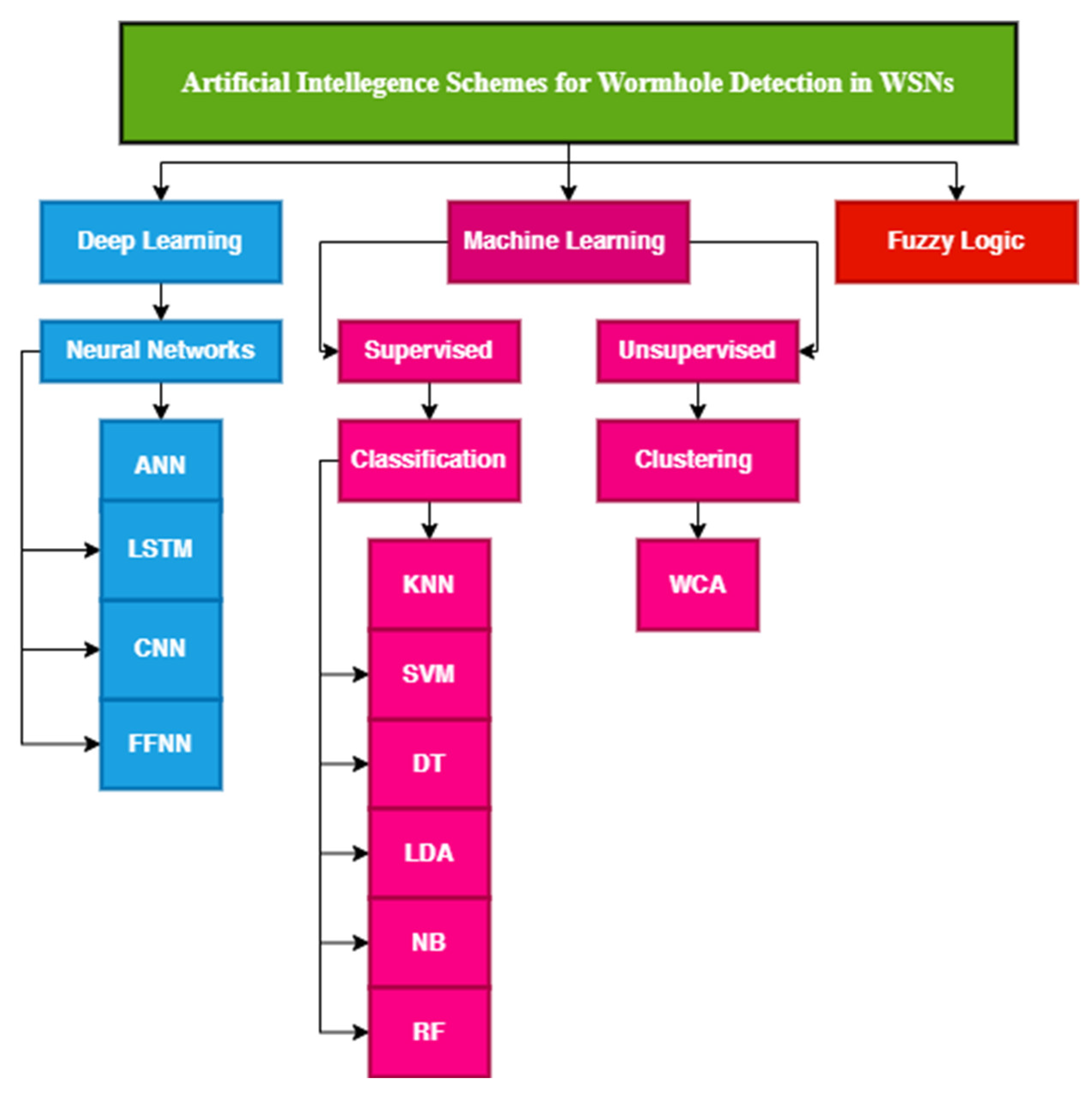
2. Artificial Immune Systems and Machine Learning-Based Systems
3. Neighbor Discovery-Based Systems
4. AODV Protocol-Based Systems
5. RTT-Based Systems
|
Ref. |
Scheme |
Methodology |
|
|---|---|---|---|
|
Neighbours discovery based |
[31] |
CREDND (creating a credible neighbour discovery) protocol |
This scheme uses a neighbour ration threshold to evaluate which nodes should be checked. After this, an external wormhole is recognized by hop count as external malicious nodes acting in hidden mode and using the out-of-band channel. In the last step, an internal wormhole is recognized by authentication packets as internal malicious nodes act as normal nodes and use packet encapsulation. |
|
[32] |
Trust-based scheme |
This lightweight trust-based scheme computes direct trust (DT) by considering the node properties and indirect trust (IT) and by considering the opinions of neighbour nodes. Every node keeps track of its neighbours and checks that they work according to the RPL network rules. The sum of DT and IT is calculated, and the decision is made based on TT (total trust). |
|
|
[33] |
Decentralized statistical scheme |
This scheme uses two parameters, i.e., the number of new neighbours and the number of old neighbours. The SWAN algorithm is used for detecting the number of neighbours. The decision rule is used with a sliding window to make the decision. |
|
|
[34] |
MLAMAN scheme |
This scheme works by changing tunnel lengths and the speed networks of the nodes. The malicious node is recognized by using hop-difference and AODV protocol. It detects intruders at the packet, neighbour, and membership levels. |
|
|
[35] |
MaxIS scheme |
The proposed method uses a greedy algorithm to search for intruders in maximum independent sets with forbidden sub-structures. |
|
|
[36] |
NIAPC scheme |
This scheme uses the AODV protocol and neighbourhood information to detect malicious nodes. It finds an alternate path for secure communication all over the network. |
|
|
[37] |
ESPMAW scheme |
This scheme uses the AODV routing protocol, neighbour, and connectivity information to find intruders in the system. |
|
|
[38] |
SDN-based scheme (SWANS) |
This scheme uses the information of neighbour similarity for the detection of wormholes in software-defined networks. |
|
|
AODV protocol-based schemes |
[39] |
Wormhole recognition using AODV |
The sender sends an RREQ (route request packet) to the receiver node in the AODV network. The sender calculates the average sequence numbers of all the receiver nodes. The receiver sends an RREP (route reply packet) to the sender, who compares the sequence number of the receiver with the already calculated average and decides whether the path is attacked. |
|
[40] |
Confirmation system using honeypot |
This method uses a honeypot for creating trees. The AODV and resilient ethernet protocol searches these trees for wormhole node detection. |
|
|
[41] |
AODV based scheme |
AODV, OSLR, and ZRP are used to detect malicious nodes in the wireless sensor network. |
|
|
[42] |
Lightweight scheme (AODV) |
In this scheme, the sender nodes collect all reply packets along with their sequence numbers and compare them with the calculated average sequence number to detect intruders. |
|
|
RTT based |
[43] |
RTT-centred wormhole recognition |
The AODV protocol is used in the route discovery phase. The sender sends an RREQ and saves the TREQ. The receiver sends the RREP back to the sender. The RTT is calculated as the difference between the TREP and TREQ. The path is considered a wormhole attack if the RTT exceeds the threshold limit. |
|
[44] |
RTT centred scheme |
This scheme uses RTT in conjunction with propagation time. The sender sends an RREQ packet and receives an RREP packet. The sender then calculates the RTT and propagation time to decide whether the route is attacked or attacked-free. |
|
|
[45] |
EIRGP and RTT-based scheme |
This scheme uses the EIGRP protocol and round-trip time for the detection of intruders. |
|
|
[46] |
Trust-based scheme |
This scheme uses RTT and AODV protocols for detecting malicious nodes. |
|
|
High-power transmission based |
[47] |
Energy model by using AODV and hop count |
Hop count is used to computing the distance between sender and receiver. Every node consists of a routing table and the next-hop of all nodes. The AODV routing protocol and high-power transmission are used to build a wormhole path. The malicious nodes send data packets with high energy levels, resulting in nodes draining. The system shows the normal nodes in green and the negative nodes in red. |
|
[48] |
RPL-based scheme |
The RPL routing protocol is used with the RSSI value to detect malicious nodes in the network. |
|
|
Path selection |
[49] |
3PATw scheme |
This scheme applied 3PAT to recognize the blackhole in each communication in the network. Once it recognized the black hole, the modified transmission radius based (TRB) is applied to recognize the wormhole. |
|
[50] |
Spanning trees scheme |
This scheme selects a rode node for the spanning tree. The Breadth-First Search (BFS) algorithm is applied to detect wormhole nodes in the tree. |
|
|
[51] |
AD-PSO scheme |
First of all, K paths are selected. The sender sends a detection packet (DP) containing RTT and hops count information. The receiver generates a feedback packet (FP). The DP and FP are compared to find wormhole nodes. Once it detects the malicious node, PSO is used to find the optimal attacker-free path. |
|
|
Statistical method based |
[52] |
Encapsulation and fragmentation of message (EFM) scheme |
This scheme presents a data packet security process that encapsulates the message and adds extra four-bit information. The message is decapsulated at the receiver’s end. The technique divides the message into small pieces and sends all pieces through different parts to the destination. |
|
[53] |
Intrusion prevention system |
This scheme presents an intrusion prevention system (IPS) which detects malicious nodes and broadcasts their credentials all over the network so that no more nodes connect with those malicious nodes. |
|
|
[54] |
HCBS protocol-based scheme |
This scheme detects malicious nodes in clusters by using the heterogeneous cluster-based secure directing convention (HCBS) protocol. |
|
|
Hop count and Weight-based |
[55] |
LITS scheme |
This scheme uses a verification process of two replayable control messages and time synchronization to detect malicious nodes. |
|
[56] |
WDV-hop scheme |
This scheme first detects suspicious nodes by using hop count, calculates localization error for them, and drops the malicious nodes. |
|
|
[57] |
Delay per hour indication (DELPHI)-based scheme |
This scheme uses DELPHI (delay per hop indication) approach with some broadcasting modification by computing threshold values to detect intruders. |
|
|
[58] |
RHE2WADI scheme using RSSI value |
This scheme uses received signal strength indicator (RSSI) values and hop count to detect malicious nodes in the IoT network. |
|
|
Authentication Key-based |
[59] |
EDAK scheme |
This scheme uses a dynamic matrix key process to store all the local information of the nodes so that legal nodes can be identified. It performs encryption and decryption along with two hash functions. |
|
[60] |
HKP-HD scheme |
This scheme uses key generation and its pre-distribution to reduce the chance of attacker nodes. |
|
|
[61] |
Elliptic curve cryptography scheme |
This scheme uses elliptic curve cryptography with the AODV protocol for wormhole attack-free networks. |
|
|
Mobile agent and Cloud-based |
[62] |
Visiting centre local-based scheme |
This scheme introduces a mobile agent in the network which is responsible for distinguishing malicious nodes from normal nodes. |
|
[63] |
Cross-layer verification scheme |
This scheme presents a cross-layer verification framework (CLVF) to find intruders in the system. |
6. High-Power Transmission-Based Systems
7. Path Selection-Based Systems
8. Statistical Method-Based Systems
9. Hop Count and Weight-Based Methods
10. Authentication Key-Based Systems
11. Mobile Agent and Cloud-Based Systems
References
- Adil, M.; Almaiah, M.A.; Omar Alsayed, A.; Almomani, O. An anonymous channel categorization scheme of edge nodes to detect jamming attacks in wireless sensor networks. Sensors 2020, 20, 2311.
- Elsayed, W.; Elhoseny, M.; Sabbeh, S.; Riad, A. Self-maintenance model for wireless sensor networks. Comput. Electr. Eng. 2018, 70, 799–812.
- Sah, D.K.; Amgoth, T. Renewable energy harvesting schemes in wireless sensor networks: A survey. Inf. Fusion 2020, 63, 223–247.
- Sampoornam, K.P.; Saranya, S.; Mohanapriya, G.K.; Devi, P.S.; Dhaarani, S. Analysis of LEACH Routing Protocol in Wireless Sensor Network with Wormhole Attack. In Proceedings of the 2021 Third International Conference on Intelligent Communication Technologies and Virtual Mobile Networks (ICICV), Tirunelveli, India, 4–6 February 2021; pp. 147–152.
- Shahraki, A.; Taherkordi, A.; Haugen, Ø.; Eliassen, F. Clustering objectives in wireless sensor networks: A survey and research direction analysis. Comput. Netw. 2020, 180, 107376.
- Numan, M.; Subhan, F.; Khan, W.Z.; Hakak, S.; Haider, S.; Reddy, G.T.; Alazab, M. A systematic review on clone node detection in static wireless sensor networks. IEEE Access 2020, 8, 65450–65461.
- Kandris, D.; Nakas, C.; Vomvas, D.; Koulouras, G. Applications of wireless sensor networks: An up-to-date survey. Appl. Syst. Innov. 2020, 3, 14.
- Ali, A.; Ming, Y.; Chakraborty, S.; Iram, S. A comprehensive survey on real-time applications of WSN. Future Internet 2017, 9, 77.
- Premkumar, M.; Sundararajan, T.V.P. DLDM: Deep learning-based defense mechanism for denial of service attacks in wireless sensor networks. Microprocess. Microsyst. 2020, 79, 103278.
- Liu, Y.; Ma, M.; Liu, X.; Xiong, N.N.; Liu, A.; Zhu, Y. Design and analysis of probing route to defense sinkhole attacks for Internet of Things security. IEEE Trans. Netw. Sci. Eng. 2018, 7, 356–372.
- Yousefpoor, M.S.; Yousefpoor, E.; Barati, H.; Barati, A.; Movaghar, A.; Hosseinzadeh, M. Secure data aggregation methods and countermeasures against various attacks in wireless sensor networks: A comprehensive review. J. Netw. Comput. Appl. 2021, 190, 103118.
- Verma, M.K.; Dwivedi, R.K. A Survey on Wormhole Attack Detection and Prevention Techniques in Wireless Sensor Networks. In Proceedings of the 2020 International Conference on Electrical and Electronics Engineering (ICE3), Gorakhpur, India, 14–15 February 2020; pp. 326–331.
- Dwivedi, R.K.; Sharma, P.; Kumar, R. Detection and prevention analysis of wormhole attack in wireless sensor network. In Proceedings of the 2018 8th International Conference on Cloud Computing, Data Science & Engineering (Confluence), Noida, India, 11–12 January 2018; pp. 727–732.
- Goyal, M.; Dutta, M. Intrusion Detection of Wormhole Attack in IoT: A Review. In Proceedings of the 2018 International Conference on Circuits and Systems in Digital Enterprise Technology (ICCSDET), Kottayam, India, 21–22 December 2018; pp. 1–5.
- Farjamnia, G.; Gasimov, Y.; Kazimov, C. Review of the techniques against the wormhole attacks on wireless sensor networks. Wirel. Pers. Commun. 2019, 105, 1561–1584.
- Ghugar, U.; Pradhan, J. Survey of wormhole attack in wireless sensor networks. Comput. Sci. Inf. Technol. 2020, 2, 33–42.
- Kumar, S.S. Abridgement and Prevention of Wormhole Attack in Mobile Ad Hoc Networks using Coordinator Node. Ph.D. Thesis, Vels University, Chennai, India, 7 February 2020. Available online: http://hdl.handle.net/10603/274578 (accessed on 28 May 2022).
- Giri, D.; Borah, S.; Pradhan, R. Approaches and measures to detect wormhole attack in wireless sensor networks: A survey. In Advances in Communication 2018, Devices, and Networking; Springer: Singapore, 2018; pp. 855–864.
- Padmapriya, S.D.; Jeyalaksshmi, S.S.; Kamalakkannan, S. A Survey: Techniques and Challenges to Detect Wormhole Attack in Wireless Sensor Network. J. Appl. Sci. Comput. 2018, 5, 2120–2126.
- Jamali, S.; Fotohi, R. Defending against Wormhole Attack in MANET Using an Artificial Immune System. New Rev. Inf. Netw. 2016, 21, 79–100.
- Jhanjhi, N.Z.; Brohi, S.N.; Malik, N.A.; Humayun, M. Proposing a Hybrid RPL Protocol for Rank and Wormhole Attack Mitigation using Machine Learning. In Proceedings of the 2020 2nd International Conference on Computer and Information Sciences (ICCIS), Sakaka, Saudi Arabia, 13–15 October 2020; pp. 1–6.
- Singh, M.M.; Dutta, N.; Singh, T.R.; Nandi, U. A Technique to Detect Wormhole Attack in Wireless Sensor Network Using Artificial Neural Network. In Evolutionary Computing and Mobile Sustainable Networks; Springer: Singapore, 2021; pp. 297–307.
- Pawar, M.V.; Anuradha, J. Detection and prevention of black-hole and wormhole attacks in wireless sensor network using optimized LSTM. Int. J. Pervasive Comput. Commun. 2021, ahead of print.
- KP, K.S. Delta Ruled First Order Iterative Deep Neural Learning for Sybil and Wormhole Attacks Detection in Healthcare Wireless Sensor Network. Preprint 2021.
- Abdan, M.; Seno, S.A.H. Machine Learning Methods for Intrusive Detection of Wormhole Attack in Mobile Ad-Hoc Network (MANET). Wirel. Commun. Mob. Comput. 2021, 2021, 2375702.
- Ezhilarasi, M.; Gnanaprasanambikai, L.; Kousalya, A.; Shanmugapriya, M. A novel implementation of routing attack detection scheme by using fuzzy and feed-forward neural networks. Soft Comput. 2022, 1–12.
- Gulganwa, P.; Jain, S. EES-WCA: Energy-efficient and secure weighted clustering for WSN using machine learning approach. Int. J. Inf. Technol. 2022, 14, 135–144.
- Ali, S.; Nand, P.; Tiwari, S. Detection of Wormhole Attack in Vehicular Ad-hoc Network over Real Map using Machine Learning Approach with Preventive Scheme. J. Inf. Technol. Manag. 2022, 14, 159–179.
- Lakshmi Narayanan, K.; Santhana Krishnan, R.; Golden Julie, E.; Harold Robinson, Y.; Shanmuganathan, V. Machine learning-based detection and a novel EC-BRTT algorithm-based prevention of DoS attacks in wireless sensor networks. Wirel. Pers. Commun. 2021, 1–25.
- Gite, P.; Chouhan, K.; Krishna, K.M.; Nayak, C.K.; Soni, M.; Shrivastava, A. ML Based Intrusion Detection Scheme for various types of attacks in a WSN using C4. 5 and CART classifiers. Mater. Today Proc. 2021, in press.
- Luo, X.; Chen, Y.; Li, M.; Luo, Q.; Xue, K.; Liu, S.; Chen, L. CREDND: A novel secure neighbor discovery algorithm for wormhole attack. IEEE Access 2019, 7, 18194–18205.
- Mehta, R.; Parmar, M.M. Trust-based mechanism for Securing IoT Routing Protocol RPL against Wormhole & Grayhole Attacks. In Proceedings of the 2018 3rd International Conference for Convergence in Technology (I2CT), Pune, India, 6–8 April 2018; pp. 1–6.
- As’adi, H.; Keshavarz-Haddad, A.; Jamshidi, A. A New Statistical Method for Wormhole Attack Detection in MANETs. In Proceedings of the 2018 15th International ISC (Iranian Society of Cryptology) Conference on Information Security and Cryptology (ISCISC), Tehran, Iran, 28–29 August 2018; pp. 1–6.
- Vo, T.T.; Luong, N.T.; Hoang, D. MLAMAN: A novel multi-level authentication model and protocol for preventing wormhole attacks in mobile ad hoc networks. Wirel. Netw. 2019, 25, 4115–4132.
- Bai, S.; Liu, Y.; Li, Z.; Bai, X. Detecting wormhole attacks in 3D wireless ad hoc networks via 3D forbidden substructures. Comput. Netw. 2019, 150, 190–200.
- Patel, M.; Aggarwal, A.; Chaubey, N. Detection of Wormhole Attack in Static Wireless Sensor Networks. In Advances in Computer Communication and Computational Sciences; Springer: Singapore, 2019; Volume 760, pp. 463–471.
- Aliady, W.A.; Al-Ahmadi, S.A. Energy preserving secure measure against wormhole attack in wireless sensor networks. IEEE Access 2019, 7, 84132–84141.
- Alenezi, F.A.; Song, S.; Choi, B.Y. SWANS: SDN-based Wormhole Analysis using the Neighbor Similarity for a Mobile ad hoc network (MANET). In Proceedings of the 2021 IFIP/IEEE International Symposium on Integrated Network Management (IM), Bordeaux, France, 17–21 May 2021; pp. 653–657.
- Kaur, T.; Kumar, R. Mitigation of blackhole attacks and wormhole attacks in wireless sensor networks using aodv protocol. In Proceedings of the 2018 IEEE International Conference on Smart Energy Grid Engineering (SEGE), Oshawa, ON, Canada, 12–15 August 2018; pp. 288–292.
- Tiruvakadu, D.S.K.; Pallapa, V. Confirmation of wormhole attack in MANETs using honeypot. Comput. Secur. 2018, 76, 32–49.
- Govindasamy, J.; Punniakody, S. A comparative study of reactive, proactive, and hybrid routing protocol in wireless sensor networks under wormhole attack. J. Electr. Syst. Inf. Technol. 2018, 5, 735–744.
- Zardari, Z.A.; Memon, K.A.; Shah, R.A.; Dehraj, S.; Ahmed, I. A lightweight technique for detection and prevention of wormhole attacks in MANET. EAI Endorsed Trans. Scalable Inf. Syst. 2021, 8, e2.
- Kori, S.; Krishnamurthy, G.N.; Sidnal, N. RTT Centered Automatic and Dynamic Wormhole Attack Discovery in Sensor Network. In Proceedings of the 2018 International Conference on Electrical, Electronics, Communication, Computer, and Optimization Techniques (ICEECCOT), Msyuru, India, 14–15 December 2018; pp. 1684–1690.
- Roy, A.K.; Khan, A.K. RTT-based wormhole detection for wireless mesh networks. Int. J. Inf. Technol. 2020, 12, 1–8.
- Karthigadevi, K.; Balamurali, S.; Venkatesulu, M. Wormhole attack detection and prevention using EIGRP protocol based on round trip time. J. Cyber Secure. Mobil. 2018, 7, 215–228.
- Kori, S.; Krishnamurthy, G.N.; Sidnal, N. Distributed Wormhole Attack Mitigation Technique in WSNs. Int. J. Comput. Netw. Inf. Secure 2019, 11, 20–27.
- Gayathri, S.; Seetharaman, R.; Subramanian, L.H.; Premkumar, S.; Viswanathan, S.; Chandru, S. Wormhole Attack Detection using Energy Model in MANETs. In Proceedings of the 2019 2nd International Conference on Power and Embedded Drive Control (ICPEDC), Chennai, India, 21–23 August 2019; pp. 264–268.
- Deshmukh-Bhosale, S.; Sonavane, S.S. A real-time intrusion detection system for wormhole attack in the RPL-based Internet of Things. Procedia Manuf. 2019, 32, 840–847.
- Thanuja, R.; Ram, E.S.; Umamakeswari, A. A linear-time approach to detect wormhole tunnels in mobile Adhoc networks using 3PAT and transmission radius (3PAT w). In Proceedings of the 2018 2nd International Conference on Inventive Systems and Control (ICISC), Coimbatore, India, 19–20 January 2018; pp. 837–843.
- Harsányi, K.; Kiss, A.; Szirányi, T. Wormhole detection in wireless sensor networks using spanning trees. In Proceedings of the 2018 IEEE International Conference on Future IoT Technologies (Future IoT), Eger, Hungary, 18–19 January 2018; pp. 1–6.
- Tamilarasi, N.; Santhi, S.G. Detection of Wormhole Attack and Secure Path Selection in Wireless Sensor Network. Wirel. Pers. Commun. 2020, 114, 329–345.
- Scholar, M.T.; Yadav, B. Predication and Root Selection of Worm Hole Attack in WSN. Int. J. Sci. Res. Eng. Trends 2019, 5, 1937–1944.
- Scholar, M.T.; Kant, R.; Sen, A.D. Collaborative Decision for Wormhole Attack Prevention in WSN. Int. J. Sci. Res. Eng. Trends 2020, 6, 212.
- Chatla, A.B. Trust-Based Secure Network For Detection Of Attacks (Wormhole And Black Hole) Due To Malicious Nodes In Ad Hoc Wireless Sensor Network. Turk. J. Comput. Math. Educ. TURCOMAT 2021, 12, 2763–2769.
- Bhushan, B.; Sahoo, G. Detection and defense mechanisms against wormhole attacks in wireless sensor networks. In Proceedings of the 3rd International Conference on Advances in Computing, Communication & Automation (ICACCA) (Fall), Dehradun, India, 15–16 September 2017; pp. 1–5.
- Li, J.; Wang, D.; Wang, Y. Security DV-hop localization algorithm against wormhole attack in wireless sensor network. IET Wirel. Sens. Syst. 2018, 8, 68–75.
- Kaur, P.; Kaur, D. Performance Evaluation of the Proposed Wormhole Detection Scheme with Existing Schemes. Wirel. Pers. Commun. 2021, 119, 1–11.
- Bhosale, S.A.; Sonavane, S.S. Wormhole Attack Detection System for IoT Network: A Hybrid Approach. Wirel. Pers. Commun. 2021, 124, 1081–1108.
- Athmani, S.; Bilami, A.; Boubiche, D.E. EDAK: An Efficient Dynamic Authentication and Key Management Mechanism for heterogeneous WSNs. Futur. Gener. Comput. Syst. 2019, 92, 789–799.
- Ahlawat, P.; Dave, M. An attack resistant key predistribution scheme for wireless sensor networks. J. King Saud Univ. Comput. Inf. Sci. 2021, 33, 268–280.
- Shukla, M.; Joshi, B.K.; Singh, U. Mitigate Wormhole Attack and Blackhole Attack Using Elliptic Curve Cryptography in MANET. Wirel. Pers. Commun. 2021, 121, 1–24.
- Patel, M.A.; Patel, M.M. Wormhole Attack Detection in Wireless Sensor Network. In Proceedings of the International Conference on Inventive Research in Computing Applications, ICIRCA, Coimbatore, India, 11–12 July 2018; pp. 269–274.
- Jagadeesan, S.; Parthasarathy, V. Design and implement a cross-layer verification framework (CLVF) for detecting and preventing black hole and wormhole attack in wireless ad-hoc networks for cloud environment. Clust. Comput. 2019, 22, 299–310.





