
Video Upload Options
The visual fidelity of a virtual environment lacks the exceedingly complex layers from the physical world, but the continuous improvements of image rendering technology and computation powers have led to greater demands for virtual simulations. Our study employs Crime Prevention through Environmental Design (CPTED) as a risk control measure and utilizes two principles: Access Control and Natural Surveillance. We conducted an experiment with (n-sample: 100) graduate students. For the experiment, we utilized the Factor Analysis of Information Risk (FAIR) to quantitatively analyze the risk. Furthermore, we adopted the lme4 package for R to estimate the mixed effect of the 6,242,880 observations retrieved from Kaggle. Based on the two experiments, we were able to critically evaluate the contributions of CPTED through a multi-component analysis. Our study investigates how spatial syntax and territorial demarcation may translate in the cyberspace realm. We found that the corollaries of the mophology in the virtual environment effects the distribution of crime. The results of our study discusses how to determine the criminogenic designs and capacity in the cyberspace realm.
1. Data Collection
Experiment 1
This paper aims to measure the risk by applying the Risk Management model to the online game environments. Using AssaultCube, an open-source FPS game, we designed two maps for our experiment. The first map, Map1, is the default map provided by AssaultCube. Based on Map1 We changed the exposure rate and altered the environment to create a second map, Map2. To apply the CPTED method to the second map, Map2, we added fences to the environment. By applying contrasting settings to the two different maps, we aimed to observe if the components from Natural Surveillance and Access Control would change the user’s behavior. As mentioned in the aforementioned section, Natural Surveillance has been proven to reduce crime rates. We carried out an experiment with a total of 100 graduate students from the School of Information Security, Korea University, Republic of Korea. We used two laptops with the identical model, LG14Z95, specifications, and settings. The players participating in the game used the same firearm, MF-577. The goal of the experiment was to demonstrate the potential relationship between the natural surveillance and user’s behavior. The participants were given a brief description of the experiment, and a detailed explanation of the control setting was provided prior to the experiment. We conducted a questionnaire survey to analyze the participants response.
The questionnaire survey consisted of questions that pertained to the different maps. We assured the participants that there are no right or wrong answers to ensure that the participants honestly answered the questions. The respondents were asked to recall the situations from the first and second gameplay. We asked the participants to select the words or phrases that best associated with their experiences. The participants were asked to select more than one answer, and they were asked to fill out the answers for both Map1 and Map2. The FAIR model, a risk analysis model, was used in our study to compare the threat and risk between to the two different maps. The model is able to measure the risk by factoring in the probable frequency and probable magnitude of future loss. The FAIR model is dived into LEF and LM. Using the Risk Management Model we proposed a risk management procedure that consists of a five-step process. The first step is ‘determining the scope’ of the risk management. Then the risk analysis is the next step, which consists of ‘identification of the assets’, ‘asset value’, vulnerability evaluation’, ‘threat evaluation’. The ‘risk assessment’ assess and quantifies the risk. The CPTED is finally applied as a control measure.
In our study, we consider the two principles, natural surveillance and access control, from CPTED. Map1 had a low exposure setting in comparison to Map2. By adjusting the brightness within the settings, we were able to apply an aspect of natural surveillance to the Map2, as the brighter environment acted as a natural surveillance to the participants. The fences that were installed within Map2 served as the access control, as shown in Figure 3. As mentioned in the previous section, we conducted a survey after the experiment. The participants consisted of 100 students who received graduate degrees or a college degree. Over 28 percent of the respondents were female, and the 67.1 percent of the participants were in their 20’s and 32.9 percent were in their 30’s. The first question in the survey inquired about the number of bullets the users have used.
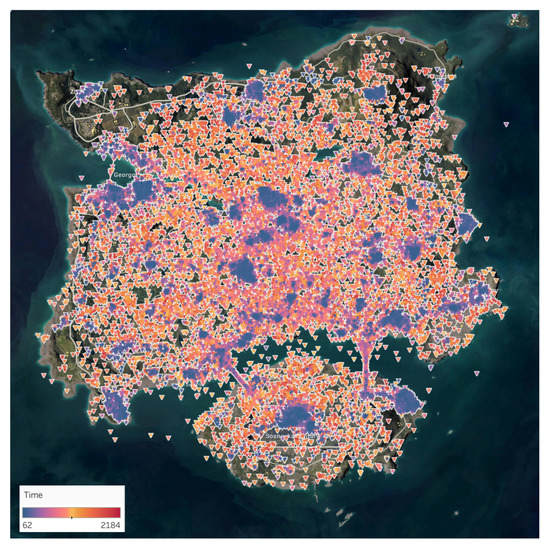
Figure 3. The figure is a visualization of the data clustered by observation for the data placed onto the two-dimensional map.
Experiment 2
The idiosyncratic nature of PUBG game implies that using PUBG for testing CPTED components requires a degree of reinterpretation and adapting real world assumptions to the first person shooter (FPS) game environment of PUBG. First of all, the element of deterrence operates differently in the FPS context as opposed to the real world. While in the real world deterrence in the personal security context occurs when the subject fears bodily harm, in the FPS context where all players are willingly committing (virtual) acts of violence, deterrence against violence does not exactly abound. Contrary to other FPS games, PUBG is a fitting environment to simulate deterrence, because the rules enforce significant penalties for each delay. So the players, at least in the initial phase of the game, prioritize self-preservation like in the real world. A game session in PUBG has a maximum duration of 40 min—every second counts and this constraint forces the players to act rationally. In addition, PUBG has a dynamic spatial constraint called “blue zone”, which shrinks the game space over time to ensure fast gameplay. Because of this, players first stock up with weapons and supplies, or “loot”, as much and as soon as possible before engaging other players in combat. Players, who can choose the initial location of gameplay, tend to start the game from locations where loot are known to be concentrated.
Naturally, this is a difficult balance to strike for a player since higher concentration of loot will attract more opponents, thereby increasing the chance of prematurely ending the game. Because of this particularity of PUBG, a typical player would avoid sites that increases exposure to opponents while maximizing the chance to collect supplies. But this behavior changes completely after the players have stocked up, as the goal is no longer about self-preservation but to eliminate as many opponents as possible. In sum, players shift from the initial risk averse phase to the risk seeking phase, and then the theory of deterrence no longer holds. While individual time marks for this “phase shift” may vary session to session and by individual preferences, in this study, we limit the initial phase to the first minute (or 60 s) into the game. Our study uses a very conservative approach given that it limits the usable sample size to a significant extent, as it represents only 1/24 of the session’s total duration. Yet, this is a time period in which there is little actualized threats and players prioritize threat avoidance over reward/risk seeking. Henceforth, it is during the first fleeting minute into the game when one can be confident that the players are acting on the perception of risks and threats rather than reacting to them. This is a period in which the components of CPTED in the FPS game setting can be tested rigorously.
2. Data Preprocessing
A set of data extracted from Pubg.op.gg was uploaded on the Kaggle Dataset, which holds data from more than 6 million players from PUBG which is available from “https://www.kaggle.com/skihikingkevin/pubg-match-deaths”. The data consisted of 6,242,880 observations from PUBG’s maps Erangel and Miramar. We focused only on the observations from Erangel, and as such we eliminated the observations from Miramar. We transposed the data obtained from the Kaggle Dataset into a format that we could analyze.
Moreover, we removed the outliers using distance-based, density-based method approach. We also eliminated data that had null values within the following metrics: (i) player id, (ii) x, y,coordinate value, (iii) maps. In order to further prepare the data for analysis, each observation is a revpairwise relationship between the “killer” and “victim”. Given that a player may eliminate multiple opponents, there are several observations in which the same player (“killer”) is matched with several others (“victim”). In addition, these observations are grouped under game sessions (“match_id”). The number of observations at the two sites are 19,117 and 81,137 for hospital and prison, respectively. After limiting the sample to observations in the first minute (60 s) of the gameplay, we are left with 12,225 observations, which are divided into 2,210 and 10,035 observations at hospital and prison locations, respectively. There is a total of 6623 unique individual players spread across 5271 sessions in the final sample.





