Information assurance (IA) is the practice of assuring information and managing risks related to the use, processing, storage, and transmission of information. Information assurance includes protection of the integrity, availability, authenticity, non-repudiation and confidentiality of user data. IA encompasses not only digital protections but also physical techniques. These protections apply to data in transit, both physical and electronic forms, as well as data at rest . IA is best thought of as a superset of information security (i.e. umbrella term), and as the business outcome of information risk management.
- information security
- information risk
- availability
1. Overview
Information assurance (IA) is the process of processing, storing, and transmitting and the right information to the right people at the right time.[1] IA relates to the business level and strategic risk management of information and related systems, rather than the creation and application of security controls. IA is used to benefit business through the use of information risk management, trust management, resilience, appropriate architecture, system safety, and security, which increases the utility of information to only their authorized users and reduces . Therefore, in addition to defending against malicious hackers and code (e.g., viruses), IA practitioners consider corporate governance issues such as privacy, regulatory and standards compliance, auditing, business continuity, and disaster recovery as they relate to information systems. Further, IA is an interdisciplinary field requiring expertise in business, accounting, user experience, fraud examination, forensic science, management science, systems engineering, security engineering, and criminology, in addition to computer science.
2. Evolution
With the growth of telecommunication networks also comes the dependency on networks, which makes communities increasing vulnerable to cyber attacks that could interrupt, degrade or destroy vital services.[2] Starting from the 1950's the role and use of information assurance has grown and evolved. In the beginning information assurance involved just the backing up of data.[3] However once the volume of information increased, the act of information assurance began to become automated, reducing the use of operator intervention, allowing for the creation of instant backups.[3] The last main development of information assurance is the implementation of distributed systems for the processing and storage of data through techniques like SANs and NAS as well as the use of cloud computing.[3][4][5] These three main developments of information fall in line with the three generations of information technologies, the first used to prevent intrusions, the 2nd to detect intrusion and the 3rd for survivability.[6][7] Information assurance is a collaborative effort of all sectors of life to allow a free and equal exchange of ideas.[8]
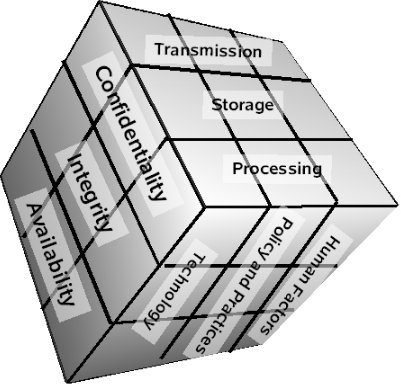
3. Pillars
Information assurance is built between five pillars: availability, integrity, authentication, confidentiality and nonrepudiation.[9] These pillars are taken into account to protect systems while still allowing them to efficiently provide services; However, these pillars do not act independently from one another, rather they interfere with the goal of the other pillars.[9] These pillars of information assurance have slowly changed to become referred to as the pillars of Cyber Security. As an administrator it is important to emphasize the pillars that you want in order to achieve your desired result for their information system, balancing the aspects of service, and privacy.
3.1. Authentication
Authentication refers to the verification of the validity of a transmission, originator, or process within an information system.[10] Authentication provides the recipient confidence in the data senders validity as well as the validity of their message.[9] There exists many ways to bolster authentication, mainly breaking down into three main ways, personally identifiable information such as a person's name, address telephone number, access to a key token, or known information, like passwords.[11]
3.2. Integrity
Integrity refers to the protection of information from unauthorized alteration.[3] The goal of information integrity is to ensure data is accurate throughout its entire lifespan.[12][13] User authentication is a critical enabler for information integrity.[9] Information integrity is a function of the number of degrees-of-trust existing between the ends of an information exchange .[13] One way information integrity risk is mitigated is through the use of redundant chip and software designs.[14] A failure of authentication could pose a risk to information integrity as it would allow an unauthorized party to alter content. For example if a hospital has inadequate password policies, an unauthorized user could gain access to an information systems governing the delivery of medication to patients and risk altering the treatment course to the detriment of a particular patient.[13]
3.3. Availability
The pillar of availability refers to the preservation of data to be retrieved or modified from authorized individuals. Higher availability is preserved through an increase in storage system or channel reliability.[9] Breaches in information availability can result from power outages, hardware failures, DDOS, etc. The goal of high availability is to preserve access to information. Availability of information can be bolstered by the use of backup power, spare data channels, off site capabilities and continuous signal.[13]
3.4. Confidentiality
Confidentiality is in essence the opposite of Integrity. Confidentiality is a security measure which protects against who is able to access the data, which is done by shielding who has access to the information.[9] This is different from Integrity as integrity is shielding who can change the information. Confidentiality is often ensured with the use of cryptography and steganography of data.[3] Confidentiality can be seen within the classification and information superiority with international operations such as NATO[15] Information assurance confidentiality in the United States need to follow HIPAA and healthcare provider security policy information labeling and need-to-know regulations to ensure nondisclosure of information.[13]
3.5. Non-Repudiation
Nonrepudiation is the integrity of the data to be true to its origin, which prevents possible denial that an action occurred.[1][3] Increasing non-repudiation makes it more difficult to deny that the information comes from a certain source. In other words, it making it so that you can not dispute the source/ authenticity of data. Non-repudiation involves the reduction to data integrity while that data is in transit, usually through the use of a man-in-the-middle attack or phishing.[16]
3.6. Interactions of Pillars
As stated earlier the pillars do not interact independently of one another, with some pillars impeding on the functioning of other pillars or in the opposite case where they boost other pillars.[9] For example the increasing the availability of information works directly against the goals of three other pillars: integrity, authentication and confidentiality.[9]
4. Process
The information assurance process typically begins with the enumeration and classification of the information assets to be protected. Next, the IA practitioner will perform a risk assessment for those assets.[17] Vulnerabilities in the information assets are determined in order to enumerate the threats capable of exploiting the assets. The assessment then considers both the probability and impact of a threat exploiting a vulnerability in an asset, with impact usually measured in terms of cost to the asset's stakeholders.[18] The sum of the products of the threats' impact and the probability of their occurring is the total risk to the information asset.
With the risk assessment complete, the IA practitioner then develops a risk management plan. This plan proposes countermeasures that involve mitigating, eliminating, accepting, or transferring the risks, and considers prevention, detection, and response to threats. A framework published by a standards organization, such as NIST RMF, Risk IT, CobiT, PCI DSS or ISO/IEC 27002, may guide development. Countermeasures may include technical tools such as firewalls and anti-virus software, policies and procedures requiring such controls as regular backups and configuration hardening, employee training in security awareness, or organizing personnel into dedicated computer emergency response team (CERT) or computer security incident response team (CSIRT). The cost and benefit of each countermeasure is carefully considered. Thus, the IA practitioner does not seek to eliminate all risks, were that possible, but to manage them in the most cost-effective way.[19]
After the risk management plan is implemented, it is tested and evaluated, often by means of formal audits.[17] The IA process is an iterative one, in that the risk assessment and risk management plan are meant to be periodically revised and improved based on data gathered about their completeness and effectiveness.[2]
There do exist two meta-techniques with information assurance: audit and risk assessment.[17]
5. Business Risk Management
Business Risk Management breaks down into three main processes Risk Assessment, Risk Mitigation and Evaluation and assessment.[20] Information Assurance is one of the methodologies which organizations use to implement business risk management. Through the use of information assurance policies like the "BRICK" frame work.[1] Additionally, Business Risk Management also occurs to comply with federal and international laws regarding the release and security of information such as HIPAA[21] Information assurance can be aligned with corporates strategies through training and awareness, senior management involvement and support, and intra-organizational communication allowing for greater internal control and business risk management.[22] Many security executives in are firms are moving to a reliance on information assurance to protect intellectual property, protect against potential data leakage, and protect users against themselves.[18] While the use of information assurance is good ensuring certain pillars like, confidentiality, Non-repudiation etc. because of their conflicting nature an increase in security often comes at the expense of speed.[9][18] This being said, the use of information assurance in the business model improves reliable management decision making, customer trust, business continuity and good governance in both the public and private sector.[23]
6. Standards Organizations and Standards
There are a number of international and national bodies that issue standards on information assurance practices, policies, and procedures. In the UK, these include the Information Assurance Advisory Council and the Information Assurance Collaboration Group.[4]
The content is sourced from: https://handwiki.org/wiki/Information_assurance
References
- Sosin, Artur (2018-04-01). "HOW TO INCREASE THE INFORMATION ASSURANCE IN THE INFORMATION AGE" (in en). Journal of Defense Resources Management 9 (1): 45–57. ISSN 2068-9403. https://doaj.org/.
- McConnell, M. (April 2002). "Information assurance in the twenty-first century" (in en). Computer 35 (4): supl16–supl19. doi:10.1109/MC.2002.1012425. ISSN 0018-9162. https://ieeexplore.ieee.org/document/1012425.
- Cummings, R. (December 2002). "The evolution of information assurance" (in en). Computer 35 (12): 65–72. doi:10.1109/MC.2002.1106181. ISSN 0018-9162. https://ieeexplore.ieee.org/document/1106181.
- Pringle, Nick; Burgess, Mikhaila (May 2014). "Information assurance in a distributed forensic cluster" (in en). Digital Investigation 11: S36–S44. doi:10.1016/j.diin.2014.03.005. https://dx.doi.org/10.1016%2Fj.diin.2014.03.005
- Chakraborty, Rajarshi; Ramireddy, Srilakshmi; Raghu, T.S.; Rao, H.Raghav (July 2010). "The Information Assurance Practices of Cloud Computing Vendors". IT Professional 12 (4): 29–37. doi:10.1109/mitp.2010.44. ISSN 1520-9202. http://dx.doi.org/10.1109/mitp.2010.44.
- Luenam, P.; Peng Liu (2003). "The design of an adaptive intrusion tolerant database system". Foundations of Intrusion Tolerant Systems, 2003 [Organically Assured and Survivable Information Systems] (IEEE): 14–21. doi:10.1109/fits.2003.1264925. ISBN 0-7695-2057-X. http://dx.doi.org/10.1109/fits.2003.1264925.
- Liu, Peng; Zang, Wanyu (2003). "Incentive-based modeling and inference of attacker intent, objectives, and strategies". Proceedings of the 10th ACM Conference on Computer and Communication Security - CCS '03 (New York, New York, USA: ACM Press): 179. doi:10.1145/948109.948135. ISBN 1-58113-738-9. http://dx.doi.org/10.1145/948109.948135.
- Stahl, Bernd Carsten (July 2004). "Responsibility for Information Assurance and Privacy: A Problem of Individual Ethics?" (in en). Journal of Organizational and End User Computing 16 (3): 59–77. doi:10.4018/joeuc.2004070104. ISSN 1546-2234. http://services.igi-global.com/resolvedoi/resolve.aspx?doi=10.4018/joeuc.2004070104.
- Wilson, Kelce S. (July 2013). "Conflicts Among the Pillars of Information Assurance". IT Professional 15 (4): 44–49. doi:10.1109/mitp.2012.24. ISSN 1520-9202. http://dx.doi.org/10.1109/mitp.2012.24.
- Sadiku, Matthew; Alam, Shumon; Musa, Sarhan (2017). "Information Assurance Benefits and Challenges: An Introduction". http://procon.bg/article/information-assurance-benefits-and-challenges-introduction.
- San Nicolas-Rocca, Tonia; Burkhard, Richard J (2019-06-17). "Information Security in Libraries". Information Technology and Libraries 38 (2): 58–71. doi:10.6017/ital.v38i2.10973. ISSN 2163-5226. https://dx.doi.org/10.6017%2Fital.v38i2.10973
- Boritz, J. Efrim (December 2005). "IS practitioners' views on core concepts of information integrity" (in en). International Journal of Accounting Information Systems 6 (4): 260–279. doi:10.1016/j.accinf.2005.07.001. https://linkinghub.elsevier.com/retrieve/pii/S1467089505000473.
- Schou, C.D.; Frost, J.; Maconachy, W.V. (January 2004). "Information assurance in biomedical informatics systems" (in en). IEEE Engineering in Medicine and Biology Magazine 23 (1): 110–118. doi:10.1109/MEMB.2004.1297181. ISSN 0739-5175. PMID 15154266. https://ieeexplore.ieee.org/document/1297181.
- Yan, Aibin; Hu, Yuanjie; Cui, Jie; Chen, Zhili; Huang, Zhengfeng; Ni, Tianming; Girard, Patrick; Wen, Xiaoqing (2020-06-01). "Information Assurance Through Redundant Design: A Novel TNU Error-Resilient Latch for Harsh Radiation Environment". IEEE Transactions on Computers 69 (6): 789–799. doi:10.1109/tc.2020.2966200. ISSN 0018-9340. http://dx.doi.org/10.1109/tc.2020.2966200.
- Hanna, Michael; Granzow, David; Bolte, Bjorn; Alvarado, Andrew (2017). "NATO Intelligence and Information Sharing: Improving NATO Strategy for Stabilization and Reconstruction Operations". Connections: The Quarterly Journal 16 (4): 5–34. doi:10.11610/connections.16.4.01. ISSN 1812-1098. https://dx.doi.org/10.11610%2Fconnections.16.4.01
- Chen, Chin-Ling; Chiang, Mao-Lun; Hsieh, Hui-Ching; Liu, Ching-Cheng; Deng, Yong-Yuan (2020-05-08). "A Lightweight Mutual Authentication with Wearable Device in Location-Based Mobile Edge Computing". Wireless Personal Communications 113 (1): 575–598. doi:10.1007/s11277-020-07240-2. ISSN 0929-6212. http://dx.doi.org/10.1007/s11277-020-07240-2.
- Such, Jose M.; Gouglidis, Antonios; Knowles, William; Misra, Gaurav; Rashid, Awais (July 2016). "Information assurance techniques: Perceived cost effectiveness" (in en). Computers & Security 60: 117–133. doi:10.1016/j.cose.2016.03.009. https://linkinghub.elsevier.com/retrieve/pii/S0167404816300311.
- Johnson, M. E.; Goetz, E.; Pfleeger, S. L. (May 2009). "Security through Information Risk Management". IEEE Security Privacy 7 (3): 45–52. doi:10.1109/MSP.2009.77. ISSN 1558-4046. https://ieeexplore.ieee.org/document/5054909.
- Singh, R.; Salam, A.F. (May 2006). "Semantic information assurance for secure distributed knowledge management: a business process perspective". IEEE Transactions on Systems, Man, and Cybernetics - Part A: Systems and Humans 36 (3): 472–486. doi:10.1109/TSMCA.2006.871792. ISSN 1083-4427. https://ieeexplore.ieee.org/document/1632282.
- Knapp, Kenneth J., ed (2009). Cyber Security and Global Information Assurance. IGI Global. doi:10.4018/978-1-60566-326-5. ISBN 978-1-60566-326-5. http://dx.doi.org/10.4018/978-1-60566-326-5.
- Park, Insu; Sharman, Raj; Rao, H. Raghav (2015-02-02). "Disaster Experience and Hospital Information Systems: An Examination of Perceived Information Assurance, Risk, Resilience, and HIS Usefulness". MIS Quarterly 39 (2): 317–344. doi:10.25300/misq/2015/39.2.03. ISSN 0276-7783. http://dx.doi.org/10.25300/misq/2015/39.2.03.
- McFadzean, Elspeth; Ezingeard, Jean-Noël; Birchall, David (2011-04-08). "Information Assurance and Corporate Strategy: A Delphi Study of Choices, Challenges, and Developments for the Future" (in en). Information Systems Management 28 (2): 102–129. doi:10.1080/10580530.2011.562127. ISSN 1058-0530. http://www.tandfonline.com/doi/abs/10.1080/10580530.2011.562127.
- Ezingeard, Jean-Noël; McFadzean, Elspeth; Birchall, David (March 2005). "A Model of Information Assurance Benefits" (in en). Information Systems Management 22 (2): 20–29. doi:10.1201/1078/45099.22.2.20050301/87274.3. ISSN 1058-0530. http://www.tandfonline.com/doi/abs/10.1201/1078/45099.22.2.20050301/87274.3.
