Your browser does not fully support modern features. Please upgrade for a smoother experience.
Please note this is an old version of this entry, which may differ significantly from the current revision.
Subjects:
Robotics
Wireless Sensor Network (WSN) is one of the most effective methods for many real-time applications, due to its compactness, cost-effectiveness, and ease of deployment. The function of the WSN is to monitor the field of interest, collect the data, and transmit it to the base station (Access point) for post-processing analysis.
- wireless sensor networks
- ZigBee
- 6LoWPAN
1. WSN Overview
The primary advantage of the IoT is global awareness, intelligent processing, and the reliable transfer of information. The key is the realization of the information’s interactions between a human and a device or device-to-device. These devices consist of embedded systems, control and automation systems, WSNs, and others that share information in different environments for enabling the IoT [33]. Therefore, the data can be transferred over different networks without the need for human intervention. In the real environment of IoT applications, the smart city and home are the most popular fields. These applications mostly consist of three layers, which comprise; perception, the network, and the application [34]. Network and application layers are implemented in high-power devices that will keep data secure, while the perception layer is implemented in a low-power WSN. The WSN consists of multiple sensor nodes, which are communicating with each other by using different radio frequencies that are capable of performing various tasks of sensing, surveillance, measuring, and tracking [35]. These wireless nodes are resource-constrained devices that are characterized by their low processing power, narrow bandwidth, limited battery life, and restricted memory capacity [9]. The communication between WSN layers is depicted in Figure 1.
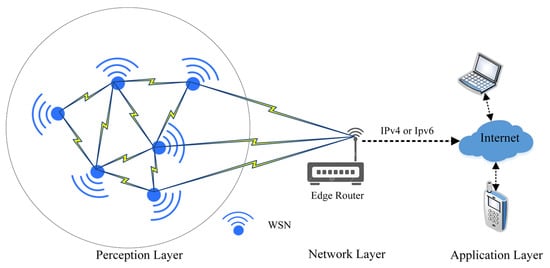
Figure 1. The communication among the WSN layers.
Based on Figure 1, wireless sensor networks are responsible for plotting the network topology and updating the routing table in the perception layer using different protocols to maintain the network infrastructure [6]. Then, the WSN starts collecting data from different locations and forwards it to the network layer (edge router). The WSN nodes are the basic building block of this layer and share some characteristics that distinguish them from other wireless networks [36]. Among these characteristics are the following:
-
Independent nodes without a central control
-
Stationary or mobile WSN nodes
-
The transmission range of WSN nodes is also limited
-
The WSN network topology is constantly changing
-
Multiple hop connections
-
Limited bandwidth
The WSN nodes, on the other hand, can generally operate in untrusted environments that are not regularly monitored. It is because of this vulnerability that valuable data can be easily leaked to uninvited parties, posing major security and privacy issues [37].
The ZigBee and 6LoWPAN are two common protocols that support management in WSNs in the perception layer [3]. Moreover, they can adapt to various other network media, such as low-power Wi-Fi [38], Bluetooth [39], and sub-1 GHz radio frequency [6]. In addition, ZigBee and 6LoWPAN were compared in [40], where 6LoWPAN provides IP capabilities for WPAN networks while ZigBee offers multiple nodes that operate at low power and cost. Moreover, ZigBee can be used in home area networks and for smart metering, as well as other devices that can be intelligently monitored from a distance using this technology. ZigBee has a reliable security system and uses strong encryption technology to secure its data. Furthermore, due to channel collision avoidance, its network technology is superior to other systems. 6LoWPAN, on the other hand, is suitable for low-power IP-based systems, such as sensors and controllers. The main features in the infrastructure of these technologies are summarized in Figure 2.
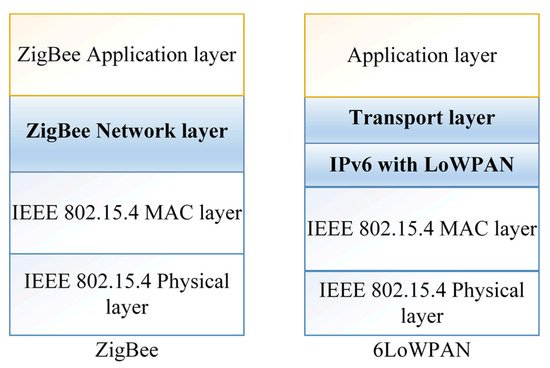
Figure 2. WSN co-management protocols.
However, in both protocols’ perception layers, WSN nodes are limited by computing power and energy [41]. Since the WSN is built to work in a variety of locations, it can be difficult to offer a charger in some of those locations. To circumvent this limitation, either the battery’s capacity should be raised or the security requirements should be dropped [42]. Nodes can also be charged using renewable energy, such as light, wind, and heat [43]. However, these solutions appear to be out of reach due to the size of the WSN and the requirement for additional hardware. On the other hand, decreasing security requirements allows for data breaches [44].
2. WSN Applications
WSNs are used in many application areas, such as the military [45], healthcare monitoring [46], industrial automation [47], and smart homes [48], among others [49]. More than 50 companies have attempted to standardize a protocol running over Layer 6LoWPAN called “Thread” (https://www.threadgroup.org/, accessed on 16 May 2022) that perfectly connects and controls smart home devices [50]. Most of these types of WSNs applications [51] are shown in Figure 3.
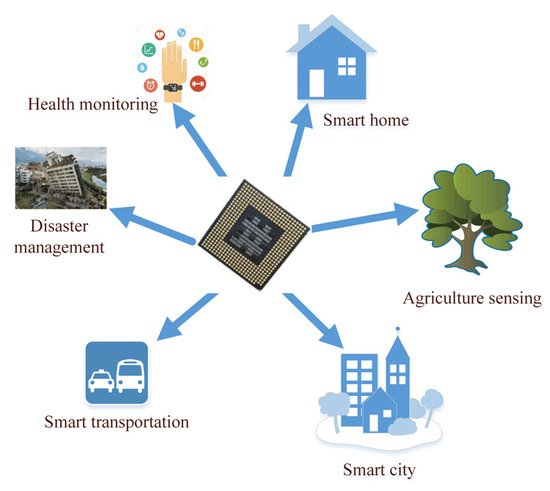
Figure 3. WSNs applications.
However, due to the nature of broadcasting and wireless network vulnerabilities, attackers can quickly inject, intercept, reroute and change overhead connections [52]. This can be risky, especially when networking is used for healthcare applications [9], military applications [53,54], or the detection of human targets [55]. Any security breach can lead to dire consequences. Therefore, WSNs can be of great interest in the civilian sector when used in healthcare. However, these networks containing sensitive data need adequate protection from all kinds of potential security threats and attacks [53]. In addition to the availability of this data, the continuity of its flow is also one of the parts that must be preserved.
3. Security in WSN
A great deal of research has addressed security concerns in WSN management protocols through the Triangle defined by Confidentiality, Integration, and Authentication (CIA). What is meant by this triangle are the three axes that must be achieved in any network for it to be called secure. Confidentiality is maintaining the privacy of important data transferred between WSN nodes. In general, before sending the packet from the sending node, important segments of the packet are encrypted, and then, at the node that received the packet, the segments are decrypted [11]. In the condition of integrity, the network must be prepared to ensure that attackers cannot alter the messages sent. Attackers can create interference beams to modify their poles. In addition, before forwarding, a malicious routing node can change important data in packets. The last condition of achieving the security triangle is availability. Availability is the availability of the WSN Services at any time required. In any case, attackers can activate attacks that reduce network performance or destroy the entire network. The most harmful risk to network availability is Denial of Service (DoS) [56]; It happens in situations where attackers, by sending wireless interference, disrupting network protocols, or exhausting WSN nodes in various ways, make the network unable to set up services. This type of attack will be discussed below.
A common protocol for the transport layer in 6LoWPAN is the User Datagram Protocol (UDP), which can be overlaid with the Datagram Transport Layer Security (DTLS) protocol to ensure data security [57]. Meanwhile, TLS is operated via the Transmission Control Protocol (TCP), and the AES-128 algorithm is used for link-layer authentication and encryption [2]. However, the TLS/DTLS implementation requires additional hardware encryption hardware to maintain the use of advanced encryption operations [58]. In addition, it is difficult to integrate Internet Protocol security (IPSec) commonly used at the network layer and Transport Layer Security (TLS) into the applications of those networks because these protocols have significant overhead costs and consume significant resources [59]. Likewise, these techniques cannot fully provide the Security Triangle (CIA), since the WSN devices use wireless communication within the range of public communication channels [60]. Therefore, there must be cooperation among a set of protocols so that these types of networks can work effectively in their environments and counteract any malicious attacks. In the domain of WSN security, malicious attacks are divided into groups [44,61], and each group has an impact on sensor nodes according to the level it belongs to. The distribution of these groups at the levels of the WSN model is shown in Figure 3.
Based on Figure 4, there are different malicious attacks in each different layer, while the DoS attack shares all layers. The DoS, Jamming, Exhaustion, and Collision disrupt network connectivity and availability. Whereas Sybil, Hole, Spoofing, Session hijacking, Eavesdropping, Man in the Middle, and Selective forwarding all threaten confidentiality and integrity [62]. In addition, these attacks that hit connectivity and availability are categorized as active while others can occur in both active and passive states.
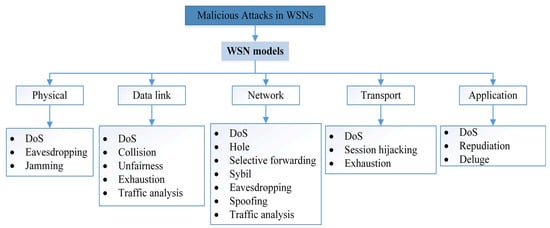
Figure 4. Malicious attacks classifications.
However, each of these layers has distinct tasks regarding reliability in data management and transmission between network nodes. The physical layer increase’s reliability by reducing the effect of path loss and shadowing. At the data link layer, the communication between WSN nodes must be interoperable through error recognition and multiplexing [21]. Moreover, the network layer will provide the best route for transmitting data to the edge router. However, in WSNs, each WSN node acts as a router, and the security related to this layer is responsible for securing this path from attacks. In addition, the transport layer is responsible for transmitting data to external networks, and the application layer is responsible for managing, collecting, and processing data to obtain trustworthy results [32].
Furthermore, authentication represents another important issue in the WSN security domain. For instance, the authentication method aims to protect the WSN network from being exploited by illegal WSN nodes. Moreover, different encryption and decryption methods are used in the security domain, while the limitations of WSNs lead to searching through various security technologies [63], in addition to these basic requirements in securing the security of wireless networks and who deals with them. There is also a need to track the actions of connected WSN devices to provide feedback on the events of a breach. Therefore, network security requires what is called non-repudiation, to prove actions for each WSN device [63]. Furthermore, unauthorized access to the network is faster in a WSN environment than in a wired connection, and physical entry is easy due to the hostile environment. If such user authentication is allowed, not only will the network efficiency be affected, but the data security may also be compromised. To avoid this, access control and parsing are essential, which can be provided by a variety of access control policies and encryption methods [59].
Attacks on WSNs
As shown in Figure 4, various types of malicious WSN attacks cause not only security issues but also other power and CPU issues. Therefore, these types of networks need to focus more on finding realistic and viable solutions than regular types of networks. In detail, we discuss the effect of each type of attack on WSNs.
-
Eavesdropping
Because of the security-related constraints of WSNs (e.g., hostile environment, dynamic nodes, and untrustworthy communication), eavesdropping is a process of acquiring information exchanged between nodes by hackers, which enhances the influence of radio fading and frequency transmission or scattering [64].
- 2.
-
Jamming
This type of attack is considered one of the most dangerous types for private wireless networks. Despite its risks, security measures are ignored against it, which can cause serious problems after the implementation of wireless networks. The foremost outcome of jamming is that it impedes user service or availability due to radio frequency interference [65].
- 3.
-
Collision
Since the sensors are located in different environments, this attack could be caused by malicious node replacement corruption. By presenting a brief noise packet, malicious nodes can cause collisions with surrounding broadcasts because they do not adhere to the Intermediate Access Control Protocol. Although this attack does not consume much energy from the attacker, it can lead to major network outages [66]. Moreover, due to the characteristics of wireless communication, it is difficult to determine the origin node.
- 4.
-
Unfairness
This type of attack prevents authorized users from accessing network resources and exploits contract connection period settings to bypass the submission deadline [67]. Repeated collision attacks or the random exploitation of the cooperative media access control layer priority methods are examples of this type of attack.
- 5.
-
Exhaustion
This type of attack recurs collision attacks until the total energy of the WSN nodes is exhausted [66]. In other words, resource depletion attacks deplete node energy by creating routing loops and path lengthening during packet transfers.
- 6.
-
Traffic monitoring
In WSNs, traffic analysis is a tool for deducing patterns of communication among nodes. The analysis uses data gathered by listening in on node-to-node communication [68]. This attack specifically targets nodes that store confidential data and have the position information of the access point or sink node. As a result, if the attack is successful, a variety of knowledge is disclosed. This has the potential to be deadly to the system.
- 7.
-
Hole attack
The black hole or sink attacks are network layer exploits that occur during message routing. Cluster heads are the target of this destructive bombardment. A hostile node can be chosen as the cluster head in this attack, and this node will now erase all transactional processes from its member nodes. It can potentially result in a sinkhole [69].
- 8.
-
Selective forwarding
It is hard to detect a selective redirection threat, particularly when hacked nodes deliberately discard packets. Hackers can use selective redirection to establish route discovery that attracts or deletes network activity. They can also increase or decrease the range of primary routers, send bogus signals, and ignore crucial messages [70].
- 9.
-
Sybil
The Sybil attack imitates the existence of a sensor node by creating several node IDs from a single current node. It also leads to system failure as a result of resource allocation issues and other issues. It has a huge effect on technologies, such as shared computing, structure management, and server protocols, which all offer load balance [31].
- 10.
-
Spoofing
This attack specifically affects routing data transferred between nodes, and it can result in routing loops, root path expansions and compression, network traceability to or from selected nodes, network segmentation, bogus error messages, and elevated end-to-end latency [63].
- 11.
-
Session hijacking
Another type of man-in-the-middle attack is a cookie side takeover, which gives the attacker full access to the application account. When you log in to an online account, such as Facebook or Twitter, the app sends you a ‘session cookie’, which is a piece of information that identifies the user to the server and gives them access to their account. The server will allow the user to use the app as long as their device keeps the session token.
- 12.
-
Repudiation
Repudiation attacks occur when an application or system fails to implement controls to correctly monitor and log users’ activities, allowing hostile tampering or forgery of additional steps to occur. This exploit can be used to alter the data authoring of harmful user operations to log incorrect data to log files. In a similar way to spoofing electronic mail, its use can be expanded to general data processing in the name of others. If this attack succeeds, the information contained in log files may be deemed inaccurate or deceptive [63].
- 13.
-
Deluge
Also known as a reprogramming assault, it is an attempt to reconfigure distributed nodes. If the assault is successful, the attacker will be able to seize control of a large portion of the network. The majority of the sensors were put in a hostile area and controlled remotely over a wireless network, which made this assault successful. It may be possible to prevent this through strong authentication.
- 14.
-
DoS
This type of attack was repeated in all layers of the WSN, which means that it applies to any layer. DoS attack seeks to shut down a system or network, making it unreachable to the intended audience. DoS attacks work by flooding the victim with traffic or providing information that causes the victim to fail. A DoS attack deprives real users (workers, members, or policyholders) of the services or assets they intended to use [57].
Therefore, these attacks can affect the security infrastructure of any organization as illustrated in Table 1. Moreover, Table 2 shows the security infrastructure of WSN networks, and the protection techniques for each baseline.
Table 1. Attacks in security policies.
| Security Infrastructure | Attacks |
|---|---|
| Confidentiality | Hole, Sybil, Spoofing, Session hijacking, Repudiation, Selective forwarding, Spoofing |
| Integrity | Eavesdropping, traffic analysis, Selective forwarding, Spoofing |
| Availability | DoS, Exhaustion, Jamming, Collision, Unfairness |
Table 2. WSNs protection techniques.
| Security Infrastructure | Attacks |
|---|---|
| Confidentiality | Encryption |
| Integrity | Digital signature, MAC |
| Availability | Traffic control, redundancy, Rerouting |
| Non-repudiation | Digital certificate |
In any case, malicious attack techniques change and evolve with the development of network protection software. Therefore, to be able to maintain the security of this type of wireless network, we must use the skills of self-development of sensors. The best option for their self-learning ability is to use machine learning techniques. Using these technologies, these devices can detect malicious cookies that are of a new type and not included in the current database list. The use of machine learning in WSN security is discussed in the next subsection.
4. Why Is Machine Learning Needed in WSN Security?
In malevolent circumstances, certain WSNs interact with security-sensitive information in an unsupervised manner. It is critical to use security measures for WSNs in such scenarios. Data confidentiality, data authentication, data integrity, and data freshness can all benefit from the security procedures. Traditional network security solutions, such as user authorization, are not suitable for these applications due to the WSNs’ limited resources and processing capabilities [71]. Therefore, for example, the authors in [72] designed an access gateway by using ML classification algorithms, such as Random Forest, k-NN, and Naive Bayes to assess IoT malware network activities. The k-Nearest Neighbor (k-NN) method showed the highest accuracy, according to the outcomes of performance assessment with those kinds of techniques. Moreover, the authors in [73] presented a privacy-preserving Support Vector Machine (SVM) training method for IoT data that requires only two transactions in one iteration and does not require the use of a reliable third party. When compared to conventional SVM, this technique greatly reduced computational complexity.
Therefore, ML technology provides a good model for reducing the cost of some areas of security. Anomaly detection, for example, provided excellent results against all types of malicious activity, and in the process of packet analysis [64,66,74], tracking and protection against DoS [20,21,67,75,76,77,78]. The processes of raising the availability of networks, error detection [23,24,25] and traffic congestion [17,18,19] are also based on the ML approach. In addition to the authentication operations of the physical layer, it can be a good solution [20,21,22]. Therefore, the application of ML techniques in WSNs aims to solve many of these problems and provide tremendous advantages in terms of flexibility and accuracy.
This entry is adapted from the peer-reviewed paper 10.3390/s22134730
This entry is offline, you can click here to edit this entry!
