A UAS traffic management (UTM) system requires that each UAV be able to see and be seen; therefore, the communication channel becomes crucial. In the last five years, state-of-the-art research has focused on three types of communication: ADS-B, ADS-B-like communication, and Remote ID. ADS-B is the legacy system currently used in manned flights and has been mandatory since 2020. Similarly, the ADS-B-like system works similarly to ADS-B but uses different types of wireless communication technology such as 4G, XBee, and APRS (automatic packet reporting system). However, Remote ID is a new standard established, based on Bluetooth/Wi-Fi technology that fulfills the requirement for current UTM operations.
- UTM communication
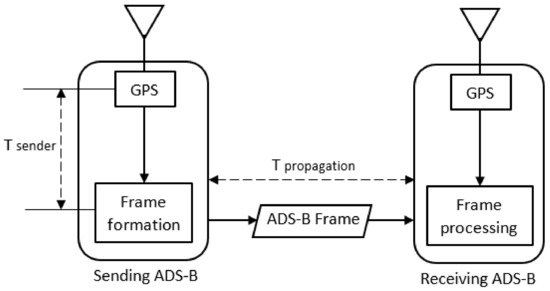
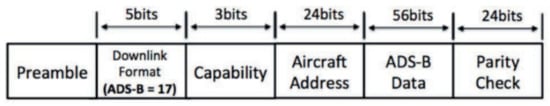
- ADS-B
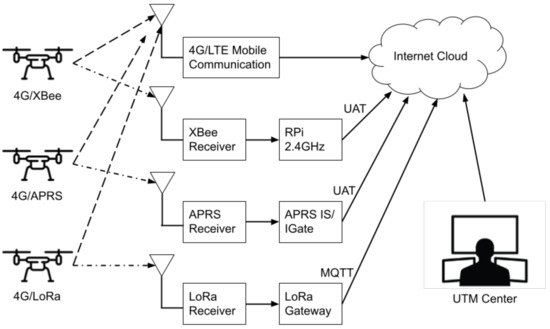
- ADS-B-like communication
- Remote ID
The communications in UTM can be categorized into ADS-B, Remote ID, and ADS-B-like systems. The information presented here consist of definition, data format, technology, and research application.
1. Definition
2. Data Format
- - UAS owner identification and its contact.
- - Properties of the vehicle including aircraft type, such as fixed-wing, quadcopter, etc.
- - Current flight plan, vehicle heading, speed, and future operations.
- - UTM status of the current flight plan, such as rogue, non-conforming, etc.
3. Technology
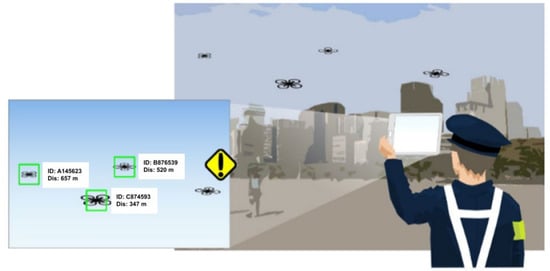
4. Research Applications
4.1. ADS-B Research
4.2. ADS-B-Like Research
4.3. Remote ID Research
This entry is adapted from the peer-reviewed paper 10.3390/drones6030057
References
- Carrio, A.; Lin, Y.; Saripalli, S.; Campoy, P. Obstacle Detection System for Small UAVs using ADS-B and Thermal Imaging. J. Intell. Robot. Syst. 2017, 88, 583–595.
- Kim, Y.; Jo, J.-Y.; Lee, S. ADS-B vulnerabilities and a security solution with a timestamp. IEEE Aerosp. Electron. Syst. Mag. 2017, 32, 52–61.
- Languell, Z.P.; Gu, Q. Securing ADS-B with Multi-Point Distance-Bounding for UAV Collision Avoidance. In Proceedings of the 2019 IEEE 16th International Conference on Mobile Ad Hoc and Sensor Systems (MASS), Monterey, CA, USA, 4–7 November 2019; pp. 145–153.
- Pan, Y.; Li, S.; Li, B.; Bhargav, B.; Ning, Z.; Han, Q.; Zhu, T. When UAVs coexist with manned airplanes: Large-scale aerial network management using ADS-B. Trans. Emerg. Telecommun. Technol. 2019, 30, e3714.
- Ghubaish, A.; Salman, T.; Jain, R. Experiments with a LoRaWAN-Based Remote ID System for Locating Unmanned Aerial Vehicles (UAVs). Wirel. Commun. Mob. Comput. 2019, 2019, 1–11.
- Kubo, D.; Osedo, A.; Yasui, I. Low Altitude Situational Awareness Enhancement using Remote ID Broadcasted from small UAS. In AIAA AVIATION 2020 FORUM; American Institute of Aeronautics and Astronautics: Reston, VA, USA, 2020; Volume 1, pp. 6–13.
- Murrell, E.; Walker, Z.; King, E.; Namuduri, K. Remote ID and Vehicle-to-Vehicle Communications for Unmanned Aircraft System Traffic Management. Res. Adv. Technol. Digit. Libr. 2020, 12574, 194–202.
- Orrell, G.L.; Chen, A.; Reynolds, C.J. Small unmanned aircraft system (SUAS) automatic dependent surveillance-broadcast (ADS-B) like surveillance concept of operations: A path forward for small UAS surveillance. In Proceedings of the 2017 IEEE/AIAA 36th Digital Avionics Systems Conference (DASC), St. Petersburg, FL, USA, 17–21 September 2017; Volume 2017.
- Azari, M.M.; Geraci, G.; Garcia-Rodriguez, A.; Pollin, S. Cellular UAV-to-UAV Communications. In Proceedings of the 2019 IEEE 30th Annual International Symposium on Personal, Indoor and Mobile Radio Communications (PIMRC), Istanbul, Turkey, 8–11 September 2019; Volume 2019.
- Hosseini, N.; Jamal, H.; Haque, J.; Magesacher, T.; Matolak, D.W. UAV Command and Control, Navigation and Surveillance: A Review of Potential 5G and Satellite Systems. In Proceedings of the 2019 IEEE Aerospace Conference, Big Sky, MT, USA, 2–9 March 2019; Volume 2019, pp. 1–10.
- Minucci, F.; Vinogradov, E.; Pollin, S. Avoiding Collisions at Any (Low) Cost: ADS-B Like Position Broadcast for UAVs. IEEE Access 2020, 8, 121843–121857.
- An ADS-B Like Communication for UTM. In Proceedings of the 2019 Integrated Communications, Navigation and Surveillance Conference (ICNS), Herndon, VA, USA, 9–11 April 2019; Volume 2019, pp. 1–12.
- International Civil Aviation Organisation. ADS-B Implementation and Operations Guidance Document; International Civil Aviation Organisation: Montreal, QC, Canada, 2020; Volume 13.
- Ishihara, A.K.; Rios, J.; Venkatesan, P. Remote UAS ID for Rapid Assessment of Flight and Vehicle Information. In Proceedings of the AIAA Scitech 2019 Forum, San Diego, CA, USA, 7–11 January 2019.
- ASTM F3411-19; Standard Specification for Remote ID and Tracking; ASTM International: West Conshohocken, PA, USA, 2020.
- Lin, Y.-H.; Lin, C.E.; Chen, H.-C. ADS-B Like UTM Surveillance Using APRS Infrastructure. Aerospace 2020, 7, 100.
- Duffield, M.; McLain, T.W. A Well Clear Recommendation for Small UAS in High-Density, ADS-B-Enabled Airspace. In Proceedings of the AIAA Information Systems-AIAA , Grapevine, TX, USA, 9–13 January 2017.
- Sherman, T.; Elemy, T.; Retherford, M.; Cady, T.; Bhandari, S. Collision Avoidance System for Fixed-Wing UAVs using Ping-2020 ADS-B Transreceivers. In Proceedings of the AIAA Scitech 2019 Forum, San Diego, CA, USA, 7–11 January 2019; American Institute of Aeronautics and Astronautics (AIAA): Reston, VA, USA, 2019; pp. 1–9.
- Bhandari, S.; Curtis-Brown, N.; Guzman, I.; Sherman, T.; Tellez, J.; Gomez, E. UAV Collision Detection and Avoidance using ADS-B Sensor and Custom ADS-B Like Solution. In Proceedings of the AIAA Information Systems-AIAA , Grapevine, TX, USA, 9–13 January 2017; pp. 1–12.
- Tang, X.-M.; Chen, J.-D.; Li, T. Unmanned aerial vehicle trajectory data fusion based on an active and passive feedback system. Proc. Inst. Mech. Eng. Part G J. Aerosp. Eng. 2019, 234, 887–895.
- Zhang, H.; Yan, Y.; Li, S.; Hu, Y.; Liu, H. UAV Behavior-Intention Estimation Method Based on 4-D Flight-Trajectory Prediction. Sustainability 2021, 13, 12528.
- Lum, C.W.; Rotta, H.; Patel, R.; Kuni, H.; Patana-Anake, T.; Longhurst, J.; Chen, K. UAS Operation and Navigation in GPS-Denied Environments Using Multilateration of Aviation Transponders. In Proceedings of the AIAA Scitech 2019 Forum, San Diego, CA, USA, 7–11 January 2019.
- Duffy, B.; Glaab, L. Variable-power ADS-B for UAS. In Proceedings of the 2019 IEEE/AIAA 38th Digital Avionics Systems Conference (DASC), San Diego, CA, USA, 8–12 September 2019; pp. 1–6.
- Palenska, M.; Brazdilova, S.L.; Casek, P.; Korenciak, L. Low-Power ADS-B for GA Operating in Low Altitude Airspace. In Proceedings of the 2020 AIAA/IEEE 39th Digital Avionics Systems Conference (DASC), San Antonio, TX, USA, 11–15 October 2020; pp. 1–10.
- Sallouha, H.; Chiumento, A.; Pollin, S. Aerial Vehicles Tracking Using Noncoherent Crowdsourced Wireless Networks. IEEE Trans. Veh. Technol. 2021, 70, 10780–10791.
- Sidibe, A.; Loubet, G.; Takacs, A.; Ferré, G.; Ghiotto, A. Miniature drone antenna design for the detection of airliners. Int. J. Microw. Wirel. Technol. 2021, 13, 21–27.
- Goossen, J.; Kim, J.; van der Hoeven, S. Development of a versatile ADS-B communications system. In Proceedings of the 2018 Texas Symposium on Wireless and Microwave Circuits and Systems (WMCS), Waco, TX, USA, 5–6 April 2018; pp. 1–4.
- Zhu, Y.; Shi, X.; Kang, K. UAV-Based Flight Inspection System. In Proceedings of the International Flight Inspection Symposium, Monterey, CA, USA, 16–20 April 2018; pp. 16–20.
- Alarcón, V.; García, M.; Alarcón, F.; Viguria, A.; Martínez, Á.; Janisch, D.; Acevedo, J.J.; Maza, I.; Ollero, A. Procedures for the Integration of Drones into the Airspace Based on U-Space Services. Aerospace 2020, 7, 128.
- Berdonosov, V.; Zivotova, A.; Naing, Z.H.; Zhuravlev, D.O. Speed Approach for UAV Collision Avoidance. J. Phys. Conf. Ser. 2018, 1015, 052002.
- Languell, Z.P.; Gu, Q. A Multi-Point Distance-Bounding Protocol for Securing Automatic Dependent Surveillance-Broadcast in Unmanned Aerial Vehicle Applications. J. Comput. Sci. Technol. 2020, 35, 825–842.
- Lee, Z.; Kumar, R.; Radmanesh, R.; Kumar, M.; Cohen, K. Application of fuzzy logic for developing sense and avoid techniques for uav flight operations in national airspace. In Dynamic Systems and Control Conference; American Society of Mechanical Engineers: New York, NY, USA, 2020; Volume 2.
- Radmanesh, M.; Kumar, M.; Sarim, M. Grey wolf optimization based sense and avoid algorithm in a Bayesian framework for multiple UAV path planning in an uncertain environment. Aerosp. Sci. Technol. 2018, 77, 168–179.
- Pierpaoli, P.; Rahmani, A. UAV collision avoidance exploitation for noncooperative trajectory modification. Aerosp. Sci. Technol. 2018, 73, 173–183.
- Berdonosov, V.; Zivotova, A.; Zhuravlev, D.; Naing, Z.H. Implementation of the Speed Approach for UAV Collision Avoidance in Dynamic Environment. In Proceedings of the 2018 International Multi-Conference on Industrial Engineering and Modern Technologies (FarEastCon), Vladivostok, Russia, 3–4 October 2018; pp. 1–6.
- Burke, P.J. Small Unmanned Aircraft Systems (SUAS) and Manned Traffic near John Wayne Airport (KSNA) Spot Check of the SUAS Facility Map: Towards a New Paradigm for Drone Safety Near Airports. Drones 2019, 3, 84.
- Wallace, R.J.; Kiernan, K.W.; Haritos, T.; Robbins, J.; D’souza, G.V. Evaluating small UAS near midair collision risk using Aero Scope and ADS-B. Int. J. Aviat. Aeronaut. Aerosp. 2018, 5, 2.
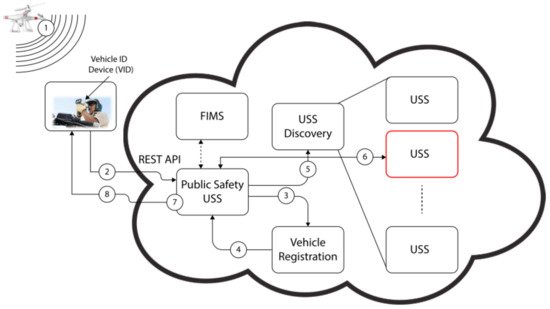
- Aweiss, A.; Homola, J.; Rios, J.; Jung, J.; Johnson, M.; Mercer, J.; Modi, H.; Torres, E.; Ishihara, A. Flight Demonstration of Unmanned Aircraft System (UAS) Traffic Management (UTM) at Technical Capability Level 3. In Proceedings of the 2019 IEEE/AIAA 38th Digital Avionics Systems Conference (DASC), San Diego, CA, USA, 8–12 September 2019; pp. 1–7.
- Mott, J.H.; Marshall, Z.A.; Vandehey, M.A.; May, M.; Bullock, D.M. Detection of Conflicts Between ADS-B-Equipped Aircraft and Unmanned Aerial Systems. Transp. Res. Rec. J. Transp. Res. Board 2020, 2674, 197–204.
- Jacob, J.; Mitchell, T.; Loffi, J.; Vance, M.; Wallace, R. Airborne visual detection of small unmanned aircraft systems with and without ADS-B. In Proceedings of the 2018 IEEE/ION Position, Location and Navigation Symposium (PLANS), Monterey, CA, USA, 23–26 April 2018; pp. 749–756.
- Meer, I.A.; Ozger, M.; Lundmark, M.; Sung, K.W.; Cavdar, C. Ground Based Sense and Avoid System for Air Traffic Management. In Proceedings of the 2019 IEEE 30th Annual International Symposium on Personal, Indoor and Mobile Radio Communications (PIMRC), Istanbul, Turkey, 8–11 September 2019; pp. 1–6.
- Arpaio, M.J.; Paolini, G.; Fuschini, F.; Costanzo, A.; Masotti, D. An All-in-One Dual Band Blade Antenna for ADS-B and 5G Communications in UAV Assisted Wireless Networks. Sensors 2021, 21, 5734.
- Siewert, S.; Sampigethaya, K.; Buchholz, J.; Rizor, S. Fail-Safe, Fail-Secure Experiments for Small UAS and UAM Traffic in Urban Airspace. In Proceedings of the 2019 IEEE/AIAA 38th Digital Avionics Systems Conference (DASC), San Diego, CA, USA, 8–12 September 2019; pp. 1–7.
- Svanstrom, F.; Englund, C.; Alonso-Fernandez, F. Real-Time Drone Detection and Tracking with Visible, Thermal and Acoustic Sensors. In Proceedings of the 2020 25th International Conference on Pattern Recognition (ICPR), Milan, Italy, 10–15 January 2020; pp. 7265–7272.
- Grzybowski, J.; Latos, K.; Czyba, R. Low-Cost Autonomous UAV-Based Solutions to Package Delivery Logistics. In Advanced, Contemporary Control; Springer: Berlin/Heidelberg, Germany, 2020; pp. 500–507.
- Shaikh, E.; Mohammad, N.; Muhammad, S. Model Checking Based Unmanned Aerial Vehicle (UAV) Security Analysis. In Proceedings of the 2020 International Conference on Communications, Signal Processing, and their Applications (ICCSPA), Sharjah, United Arab Emirates, 16–18 March 2021; pp. 1–6.
- Wang, J.; Song, D.; Liang, R.; Han, P. ADS-B and UAV Signal Monitoring System Design Based on Spectrum Sensing. In Proceedings of the 2019 IEEE 8th Joint International Information Technology and Artificial Intelligence Conference (ITAIC), Chongqing, China, 24–26 May 2019; pp. 422–426.
- Wu, Y.; Dai, H.-N.; Wang, H.; Choo, K.-K.R. Blockchain-Based Privacy Preservation for 5G-Enabled Drone Communications. IEEE Netw. 2021, 35, 50–56.
- Bateman, A.J.; Burkholder, J.; Summers, T.; Richards, N.D. Incorporating RF Coverage Analysis in Mission Planning for Future Airspace Operations. In Proceedings of the AIAA Scitech 2019 Forum, San Diego, CA, USA, 7–11 January 2019.
- Kunze, S.; Weinberger, A. Concept for a Geo-Awareness-System for Civilian Unmanned Aerial Systems. In Proceedings of the 2021 31st International Conference Radioelektronika (RADIOELEKTRONIKA), Brno, Czech Republic, 19–21 April 2021; pp. 1–6.
- Yue, X.; Liu, Y.; Wang, J.; Song, H.; Cao, H. Software Defined Radio and Wireless Acoustic Networking for Amateur Drone Surveillance. IEEE Commun. Mag. 2018, 56, 90–97.
- Lin, C.E.; Shao, P.-C.; Lin, Y.-Y. System Operation of Regional UTM in Taiwan. Aerospace 2020, 7, 65.
- Baek, H.; Lim, J. Design of Future UAV-Relay Tactical Data Link for Reliable UAV Control and Situational Awareness. IEEE Commun. Mag. 2018, 56, 144–150.
- Minucci, F.; Vinogradov, E.; Sallouha, H.; Pollin, S. UAV Location Broadcasting with Wi-Fi SSID. In Proceedings of the 2019 Wireless Days (WD), Manchester, UK, 24–26 April 2019.
- Vinogradov, E.; Minucci, F.; Pollin, S. Wireless Communication for Safe UAVs: From Long-Range Deconfliction to Short-Range Collision Avoidance. IEEE Veh. Technol. Mag. 2020, 15, 88–95.
- Shao, P.-C. Risk Assessment for UAS Logistic Delivery under UAS Traffic Management Environment. Aerospace 2020, 7, 140.
- Abdel-Malek, M.A.; Akkaya, K.; Bhuyan, A.; Cebe, M.; Ibrahim, A.S. Enabling Second Factor Authentication for Drones in 5G using Network Slicing. In Proceedings of the 2020 IEEE Globecom Workshops (GC Wkshps), Taipei, Taiwan, 7–11 December 2020; pp. 1–6.
- Perez, E.; Winger, A.; Tran, A.; Garcia-Paredes, C.; Run, N.; Keti, N.; Bhandari, S.; Raheja, A. Autonomous Collision Avoidance System for a Multicopter using Stereoscopic Vision. In Proceedings of the 2018 International Conference on Unmanned Aircraft Systems (ICUAS), Dallas, TX, USA, 12–15 June 2018; Volume 91768, pp. 579–588.
- Kuroda, V.; Egorov, M.; Munn, S.; Evans, A. Unlicensed Technology Assessment for Uas Communications. In Proceedings of the 2020 Integrated Communications Navigation and Surveillance Conference (ICNS), Herndon, VA, USA, 8–10 September 2020; pp. 1–12.
- Alkadi, R.; Shoufan, A. Unmanned Aerial Vehicles Traffic Management Solution Using Crowd-sensing and Blockchain. IEEE Trans. Netw. Serv. Manag. 2021, 1–14.
- Alsoliman, A.; Bin Rabiah, A.; Levorato, M. Privacy-Preserving Authentication Framework for UAS Traffic Management Systems. In Proceedings of the 2020 4th Cyber Security in Networking Conference (CSNet), Lausanne, Switzerland, 21–23 October 2020.
- Shoufan, A.; Yeun, C.Y.; Taha, B. eSIM-Based Authentication Protocol for UAV Remote Identification. In Security and Privacy in the Internet of Things; Wiley: New York, NY, USA, 2021; pp. 91–122.
- Rios, J.L.; Aweiss, A.S.; Jung, J.; Homola, J.; Johnson, M.; Johnson, R. Flight Demonstration of Unmanned Aircraft System (UAS) Traffic Management (UTM) at Technical Capability Level. In Proceedings of the AIAA AVIATION 2020 Forum, Virtual, 15–19 June 2020.
- Tedeschi, P.; Sciancalepore, S.; Di Pietro, R. ARID: Anonymous Remote IDentification of Unmanned Aerial Vehicles. In Proceedings of the Annual Computer Security Applications Conference, Association for Computing Machinery (ACM). New York, NY, USA, 6–10 December 2021; pp. 207–218.
