The issue of energy balancing in Wireless Sensor Networks is a pivotal one, crucial in their deployment. This problem can be subdivided in three areas: (i) energy conservation techniques, usually implying minimizing the cost of communication at the nodes since it is known that the radio is the biggest consumer of the available energy; (ii) energy-harvesting techniques, converting energy from not full-time available environmental sources and usually storing it; and (iii) energy transfer techniques, sharing energy resources from one node (either specialized or not) to another one.
- Wireless Sensor Networks
- energy harvesting
- energy-efficient data communication
- energy management
- energy prediction
Note: The following contents are extract from your paper. The entry will be online only after author check and submit it.
1. Introduction
- Energy conservation
-
techniques simply aim to extend the lifetime of the network by reducing the energy used while the WSN continues to operate as required [2]. Energy saving usually implies minimizing the cost of communication at the nodes since it is known that the radio is the biggest consumer of the available energy [3]. Different energy-saving schemes were recently surveyed in [4,5].
- Energy-harvesting
-
techniques seek to increase the energy available to the nodes. The energy can be obtained from the external environment such as solar, wind, vibrations, radio frequency, thermal, etc. These techniques convert energy from the environment into electrical energy for the nodes. In [6] it is presented a recent survey. A major constraint of these techniques is that energy sources are not always accessible and therefore it is necessary to store the harvested energy using rechargeable batteries or low-powered supercapacitors.
- Energy transfer
-
is another emerging technique applied to extend the lifetime of the network. The idea is that energy-rich nodes transfer energy to energy-deficient nodes. This transfer can be done wirelessly from a node specialized in energy harvesting or a node with enough energy resources to a node in need of energy in the same network. Engmann et al. [7] review several mechanisms for energy transfer such as inductive and magnetic coupling, or electromagnetic radiation.
2. Energy Conservation
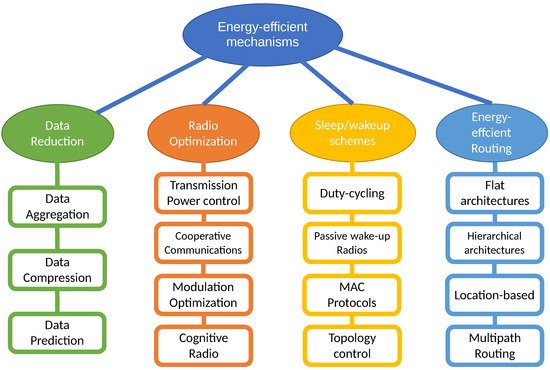
2.1. Radio Optimization
2.1.1. Modulation Optimization
2.1.2. Cooperative Communications
2.1.3. Transmission Power Control
2.1.4. Directional Antennas
2.1.5. Energy-Efficient Cognitive Radio
2.2. Data Reduction
2.2.1. Data Aggregation
2.2.2. Data Compression
- Distributed Data Compression
-
(also called in-network compression) is an asymmetric coding that uses the spatial correlation among the sensor nodes. In this case, the sensor nodes belonging to an area encode its data before sending it to the BS (or CH if clustering is used), where all the correlated flows are decoded jointly.Images and videos are usually compressed using a transform-based compression such as cosine transform or wavelets transform, where a sparse representation of the data is used to recover the original data at the decoding point with minimal loss. However, distributed transform coding (DTC) is difficult to implement in WSNs because they often need the knowledge of all measurements in the network at each node. Therefore, most articles in this field aim to modify DTC algorithms in order to make them suitable to WSNs.This problem can be avoided by means of distributed source coding (DSC) [66,67], based on the Slepian-Wolf theorem, since it does not require inter-communication among sensor nodes. The main problem of DSC is that it requires previous knowledge of the correlations in the data, and so its performance depends on specific assumptions.In contrast, compressive sensing (or compressed sensing) techniques, a relatively new idea in the field of WSNs, do not need any previous knowledge or assumption on data correlations. In compressed sensing (CS) [68] a small number of samples of a sparse signal contains enough information to successfully recover the original signal with almost no data loss. The great advantages in terms of limitations and data reduction (part of the redundant data is never acquired) make CS the most widely used technique presently in WSNs and IoT [69], even in the case of multimedia sensor networks [70].
- Local Data Compression
-
has not the limitations mentioned above and it is a universal and robust compression technique. Huffman coding, LZW (Lempel-Ziv-Welch) and RLE (Run-length encoding) are common compression techniques used in WSN for local data compression. Moreover, it can be used in conjunction with distributed data compression in WSNs to exploit both temporal and spatial data correlations.
2.2.3. Data Prediction
-
In the Single Prediction Schemes (SPSs), predictions are made in a single point in the network, either in the cluster head (CH), or in a sensor node when it is more expensive (in energy terms) to obtain a sample than to predict one. This scheme has been applied in conjunction with adaptive sampling [85], topology control [86] and clustering [87,88,89].
-
In Dual Prediction Schemes (DPSs), where clustering is used, the predictions are simultaneously made in CHs and nodes. The idea is that nodes and CH obtain the same prediction, but the node can check the precision of the prediction by comparing this with the real measure, and only send the measure to CH if the prediction is poor. In other case, CH uses the prediction.
2.3. Sleep/Wake-Up Schemes
2.3.1. Energy-Efficient MAC Protocols
2.3.2. Duty-Cycling
-
In ADP-MAC (Adaptive and Dynamic Polling-based MAC), Siddiqui et al. [95] propose modifying the polling interval distribution at the receivers dynamically, every TA
-
, based on the analysis of the coefficient of variation of the incoming traffic; and they resolve that the best results are achieved when the polling interval distribution is the same as that of interarrivals.
-
In AWR-PS-MAC (Adaptive wake-up interval to enhance Receiver-based Preamble Sampling MAC) [96], the transmitter reports on its particular traffic to the receiver—using piggybacking in DATA packets—and with such information the receiver adjust the next time to wake-up for this particular sender, which takes it from the corresponding ACK.
-
In ADMC-MAC (Adaptive MAC for Critical Missions) [97], a synchronous contention-based scheme, the authors design a protocol to adjust dynamically the duty-cycle of neighboring nodes, using a discrete set of values (40%, 20%, 10%), so adapting the cycle to traffic load: in a first stage, neighboring nodes determine which one will be the cluster head (each node broadcasts sync packets with the length of its transmission queue, the number of neighbors detected and its remaining energy, being such order what determines the priority in the election). Next, the selected node, using a single expression—determined after applying a regression technique to data obtained by a simulation study of S_MAC [98], its parent protocol—determines a duty-cycle-factor (a real number), which is then transformed—using some thresholds—in a duty-cycle value of a configured discrete set. Finally, this duty-cycle is broadcasted to the neighborhood and adopted as such.
-
In AP-MAC [99], to reduce the probability of collision among receiver awake intervals in a RI asynchronous scheme, the receiver add a random value to their precalculated next wake-up time before broadcasting it—via beacon frames—to the neighborhood, so transmitters can forecast the next potential rendezvous.
-
In [100], to minimize the latency in a multihop sink rooted tree topology, where data gathering is commanded by a request starting at then sink, Monica et al. [100] design a request-response protocol with extra wakeups generated dynamically to match the predicted arrival time of the response packet, as if the participating nodes were “hit” by (upward and downward) “waves”, and so sequentially awoken according to their depths.
-
In [101], the concept of duty-cycle is eliminated as a repetitive sequence of on-off periods, and is substituted by a slotted vision of time, where, self-adaptively, each node autonomously decides in every slot to sleep or wake-up. The authors claim that this way the trade off between energy-saving and packet delivery delay can be avoided. Unlike other prediction-based approaches where nodes must exchange information between each other, these enables nodes to approximate their neighbors’ situation without requesting information from them, thus saving the large amount of energy usually used for information exchange. In addition, to accomplish it, they propose an alternative approach based on game theory and a reinforcement learning technique (Q learning algorithm), where through trial-and-error interactions within the dynamic environment nodes are able to learn optimal actions.
-
Liu et al. [102] present QTSAC (Quorum Time Slot Adaptive Condensing-based MAC protocol), derived from previous QMAC family protocols [103], for achieving delay minimization and energy efficiency in a synchronized sink driven and rooted topology. As a particular rendezvous scheme, QTSAC condenses the Quorum Time Slots (QTS) into the period in which nodes transmit data—at the beginning of the polling cycle for the furthest nodes, and towards the end for those closest to the sink—which increases the number of intersection slots, improving network performance (shorter delay to meet a node in the right next-hop-group), and uses more QTS in the area that is far from the sink (according to their less or null energy expenditure acting as a relay for others).
- 8.
-
Liu et al. [104] propose a QoS driven EE TDMA-based protocol that dynamically adjusts the transmission order and transmission duration of the nodes—frame slots reordering—and so their on/off scheduling, based on data priority, channel status (temporal fading of parts of the body) and application context (the individual’s activity, an emergency, etc.). To reduce the synchronization overhead their proposal uses guard time intervals (to deal with clock drifts), and clock tuning using data/ack exchange (piggybacking) with the personal server (onboard sink).
- 9.
-
In the same research field (WBAN), Rismanian Yazdi et al. [105] design ECTP-MAC (Energy Consumption Traffic Prioritization MAC) and modify the frame structure of IEEE 802.15.4 to include an extra phase for emergency data. They define three types of data (normal discontinuous, periodic continuous and emergency) and schedule transmissions in CP, CFP, and extra interval according to a priority value proportional to data type and inversely proportional to data length and frequency.
- 10.
-
In a more general context, in QPPD MAC (QoS MAC Protocol for Prioritized Data) [106], after broadcasting a beacon with QoS mode on (asynchronous contention-based RI protocol), the receiver uses a limited interval and listen for senders’ requests. The protocol implements a request-allocation scheme based on transmitter beacons and data priority tags: the highest priority transmitter beacon received at interval expiration, or, immediately, if received one tagged with the top level priority, determines which contender will obtain receiver assignment. From the point of view of EE/EH, the protocol adjusts the receiver duty cycle according to its current power level, working at 5% if remaining energy is below 10%, at full activity if battery state is above 90%, and with the value determined by a particular expression (continuous function) otherwise. The authors say the biggest advantage of their proposal over others (TDMA -based) is the energy savings due to the lack of synchronization.
- 11.
-
In EEQ-MAC (Energy-Efficient and QoS-aware MAC) [107], queue length and data priority are used to adapt the node’s duty cycle, increasing the length of its active period in the event of high traffic which provides less waiting time to support time-bounded delivery of priority packets. A Random Early Detection mechanism is also included to avoid starvation of low priority data.
2.3.3. Wake-Up Radios
-
In [112], FAWR (Fully Asynchronous Wake-up Radio-based MAC), a RI sink commanded scheme, is presented as a multihop WuR MAC able to overcome the short-range limitation (20 m) of this low power transceivers. Though sensor nodes are settled at one-hop distance from the BS (from the point of view of the main radio transmissions) they succeed to propagate WuR signals using a forwarding decision table built in an early topology discovery phase executed by the sink. This way, the covered area can be much larger. They also use sensor nodes’ state of charge information so that the BTS, knowledgeable about the application requirements, can properly poll deployed devices.
-
In RI-LD-WuR (RI Low Delay MAC), Singh and Sikdar [113] propose partitioning sensor nodes in k (almost) equal sized groups to reduce packet collisions in a broadcast-based RI WuR enabled WSN: the sink commands its cluster broadcasting a request in slot0—dynamic TDMA with contention—firing the data collection phase. N transmissions fit in each slot and only the sensor nodes of the respective group are able to contend for sending. They also contribute with a distributed algorithm for the initial composition of the groups.
-
In RI-CPT-WuR (RI Consecutive Packet Transmission MAC) [114], to cancel out the time wasted in collisions, the protocol enables transmitting multiple packets through a single competition.
-
In addition, precisely to avoid collisions, refs. [114,115] present different strategies to face such issue in typical asynchronous TI WuR implementations: The proposal of Guntupalli et al. [114] uses an early backoff at time to send the WuR signal, arguing that in the case of success the transmitter will not need any additional backoff to use the main radio. Ghose et al. [115], on the contrary, advocate to incorporate to the WuC (wake-up channel) a more complete MAC protocol using CCA (CCA-WuR), CSMA (CSMA-WuR) or both adaptively (ADP-WuR). In the last, a threshold determines switching between CCA and CSMA modes if CCA fails such number of consecutive attempts.
-
Finally, in SNW-MAC (Star Network WuRx MAC) [116], an Energy Management (EM) scheme is incorporated which uses the node’s residual energy to optimize the energy usage in truly EH-WSN scenarios. The protocol assumes that the time is divided into time slots of equal duration T, and the EM is executed at the end of each slot to set the throughput of the node for the next interval. First, the Energy Budget Computation module evaluates the energy that the node can consume in the next time slot k to remain sustainable; and then Throughput Computation module calculates the wake-up interval TWI[k] according to the energy budget eB[k], so determining the frequency at which the node performs sensing and sends the so-obtained data.
2.3.4. Topology Control
2.4. Energy-Efficient Routing
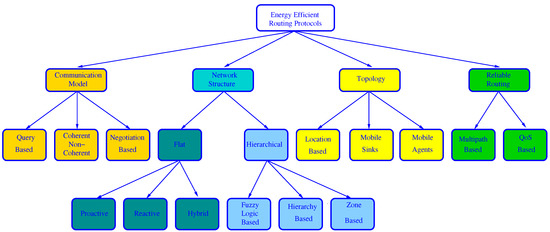
-
Query-based: When BS needs new data, it broadcasts a query message to ask for these data. Next, the node which owns the requested data sends them to the BS.
-
Coherent or non-coherent: In coherent protocols, a node applies some processing to the collected data. However, in non-coherent algorithms, the collected data are preprocessed at the source nodes and then sent to a special node, called aggregator (usually the CH), where they are further processed for data reduction.
-
Negotiation-based: before real data transmission, negotiation messages are exchanged between a source node and their destination to prevent redundant data. These protocols use a naming scheme to advertise data to destination.
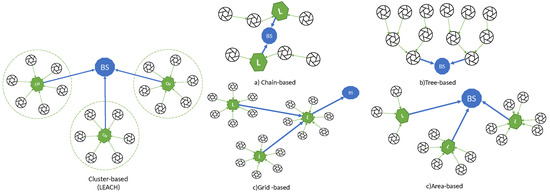
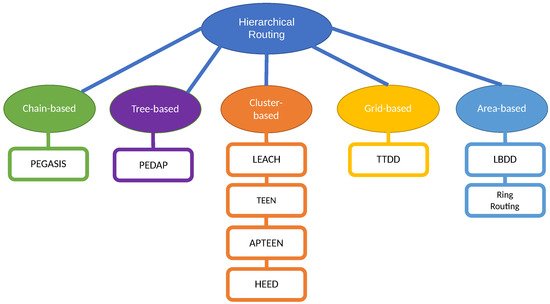
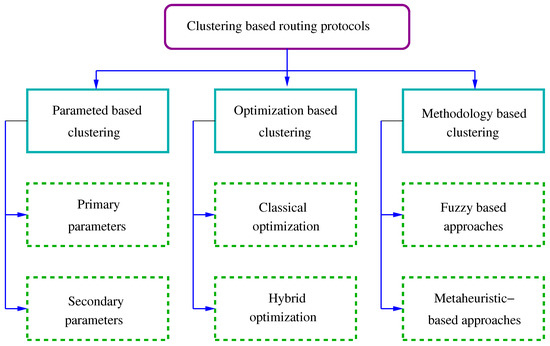
2.4.1. Hierarchical Routing Protocols
This entry is adapted from the peer-reviewed paper 10.3390/s21134281
