3. Privacy-Based Blockchains
3.1. Secret Network
Secret Network is a blockchain based on Cosmos (https://cosmos.network/) and built with the Cosmos SDK (https://v1.cosmos.network/sdk), which aims to provide privacy, smart contracts, scalability, and interoperability. It employs proof-of-stake using Tendermint’s (https://docs.tendermint.com/master/introduction/what-is-tendermint.html) Byzantine fault-tolerant consensus algorithms and uses CosmWasm (https://cosmwasm.com/) for integration with Cosmos SDK and its ecosystem. The CosmWasm provides secure architecture, tools for developing and testing smart contracts, and Cosmos Inter-Blockchain Communication Protocol (IBC) (https://ibcprotocol.org/) integration. The IBC allows interoperability with other blockchain networks. The native token of the Secret Network is the SCRT, and its smart contracts are called secret contracts (https://docs.scrt.network/dev/secret-contracts.html).
The SNIP-20 (Secret Network Improvement Proposal) (https://github.com/SecretFoundation/SNIPs/blob/master/SNIP-20.md) specifies the interactions among tokens and contracts. It is based on Ethereum’s ERC-20 (https://ethereum.org/en/developers/docs/standards/tokens/erc-20/) and ERC-777 (https://ethereum.org/pt/developers/docs/standards/tokens/erc-777/) standards and is a superset of CosmWasm’s CW-20 (https://docs.cosmwasm.com/cw-plus/0.9.0/cw20/spec/). SecretSCRT (sSCRT) is the first implementation of the SNIP-20 specification and has the following guarantees: all balances and transaction arguments in a transfer are encrypted. Viewing keys can be created to allow third parties or other contracts to access private information (e.g., balance). The token wSCRT is a wrapped SCRT on Ethereum used to provide liquidity and can be redeemed for sSCRT/SCRT (1:1) using the Ethereum–Secret Network bridge (https://bridge.scrt.network/). The secret contracts are Rust-based smart contracts that compile to WebAssembly (wasm). Every six seconds, a block is created and appended to the network, with a limit of 22 transactions per second (however, the theoretical limit is 10,000 transactions per second with the current architecture and protocol) [48].
The network applies encryption protocols, key management, and confidential computing to achieve data privacy. Thus, trusted execution environments (TEEs) are required to protect data processing in all of the network’s validator nodes. Inputs, outputs, and states can be encrypted and securely processed inside a TEE. The consensus seed (256 bits) is the most critical part of the Secret Network encryption schema, being sealed and stored at \$HOME/.sgx\_secrets/consensus\_seed.sealed in the validator nodes. The protocol uses the consensus seed and HKDF-SHA256 (https://www.devglan.com/online-tools/hmac-sha256-online) to derive keys. The public keys are published to the Secret Network genesis.json. Curve25519 (https://cr.yp.to/ecdh.html) is used to generate asymmetric encryption keys, and ECDH (elliptic-curve Diffie–Hellman) is used to derive symmetric encryption keys. These symmetric keys are used to encrypt data with AES-128-SIV.
Secret NFTs, defined by the SNIP-721 (https://github.com/SecretFoundation/SNIPs/blob/master/SNIP-721.md) and based on ERC721 (https://eips.ethereum.org/EIPS/eip-721), allow the NFT owner to decide what data are public and what are private. These NFTs have a name, a value, and a privacy level. The privacy level can be public, protected, or private. For the public level, all the data are publicly available. For the protected level, only some property names are public. For the private level, only the owner can see the name and the value. When an NFT is sold, Stash (https://stashh.io/faq) charges a fee of 2.75% of the NFT price or 0.05 sSCRT, which is automatically deducted by the platform. A small SCRT amount is also required to pay operation fees to the Secret Network. The NFT is encrypted, uploaded to IPFS (https://ipfs.io/), and pinned via Pinata (https://www.pinata.cloud/). Its public preview is available at Azure. A creator can specify a royalty to be deducted automatically by the platform whenever a collector sells the NFT.
3.2. Oasis Network
The Oasis blockchain [49] is a smart contract platform that provides scalability and privacy. Its smart contracts can be efficiently verified and confidentially executed. Oasis was designed to be:
-
Flexible—easy to modify system parameters;
-
Extensible—easy to add new components like confidential computing techniques;
-
Scalable—throughput should increase with the number of nodes;
-
Secure—the system should enforce security policies and provide confidential computing;
-
Fault-isolated—the system should be fault-tolerant in terms of security and performance.
Oasis’ native token is called ROSE (although the native token of the testnet is TEST). The average time to generate a new block is 6 s.
The platform has a modular design containing two main layers: the consensus layer and the paratimes layer [50]. The name paratimes comes from parallel runtimes, which means multiple runtimes can run simultaneously in the network. A verifiable computing implementation (discrepancy detection) provides an optimized consensus execution that is more efficient than traditional BFT (Byzantine fault tolerance) techniques, improving the smart contracts’ scalability. The consensus layer is based on the Tendermint BFT consensus protocol, uses proof-of-stake as the block proposer protocol, and can be replaced by another consensus mechanism, i.e., allows easy changing of the consensus mechanism.
3.3. Phala
Phala Network (PHA) focuses on secure and private distributed computing [54]. The project started in 2018. Phala is a Web 3.0 computing cloud that supports data privacy while remaining trustless. It offers a service to access distributed computing TEE Secure Enclave through a blockchain [55]. Any participant wishing to purchase secure computer resources and services can do so by acquiring the Phala Network token (PHA) to access it through Polkadot (https://polkadot.network/). The users can access the same services through Polkadot’s Canary Network, Kusama (https://kusama.network/), using PHA or its specific token, K-PHA. The vision is to become the world’s largest P2P computing network, a decentralized cloud based on Web3.
Phala is a Polkadot parachain developed based on the Substrate framework (https://substrate.io/). Thus, it gains access to all of Polkadot’s features, but mainly the relay chain service that provides bridge services to other blockchains. Phala achieves scalability by implementing two software design patterns: event sourcing and CQRS (command query responsibility segregation) (https://www.eventstore.com/cqrs-pattern) [55]. Event sourcing is construed when the events causing state transitions are recorded in an appendonly log instead of storing the latest state of the data. The events receive timestamps and can be re-accessed to rebuild the state at any time. The second software pattern is the CQRS, which handles read/write operations separately. Such engineering decisions are based on the claim that these patterns make the system scale and avoid conflicts.
3.4. Integritee
Integritee is the new name for a parachain from a W3 foundation grant called Substratee, having the objective to provide a trusted off-chain compute framework for substrate blockchains (SubstraTEE GitHub) (https://github.com/integritee-network/substraTEE).
It is now under a company called Integritee AG (https://integritee.network/company), which is responsible for driving the development and community efforts for Integritee. The network launched its token TEER to cover payment and governance [56]. Until recently, it has operated its mainnet as an independent project. In February 2022, the community successfully secured a parachain slot in Kusama through a crowd loan process, where they provided rewards for those earlier investors. Their book (Integritee Book) [57] defined Integritee as a framework for parity substrate, allowing it to call a custom state transition function (STF) inside a TEE, namely an Intel SGX enclave, thereby providing confidentiality and integrity. The enclaves operate in an encrypted state that can be read and written to only by a set of provisioned and remote-attested enclaves.
The Integritee website states that the community aims to be the blockchain choice for a secure operating environment that will be scalable, decentralized, and trusted. The company behind Integritee declares that they can scale up to 1 M transactions per second (TPS) due to the decentralized choice of using Polkadot and Kusama infrastructure. The tokenomics of Integritee provide a cap on the token availability of 10 M TEER for the project [58].
3.5. Ternoa
Ternoa’s founder created this blockchain to share his memories with his children in the future. The NFTs work as the vehicle for data transmission and data handling. Ternoa provides the means to store data permanently in any format, with the user controlling access and availability [61]. CAPS is the token of the Ternoa blockchain used for payment and governance of transactions.
Ternoa allows secure data storage and transmission, providing an SDK to help develop and integrate applications [61]. It is based on the Substrate (https://substrate.io/) framework and the Polkadot blockchain, and it is designed to be a parachain of Polkadot. Thus, Ternoa enables the connection to other Polkadot-based blockchains. For decentralized storage, it uses other blockchains such as Storj (https://www.storj.io/), Sia (https://sia.tech/), or Arweave (https://www.arweave.org/). The Rust language is used to develop the smart contracts, and the NFTs are based on the ERC721 standard.
As Ternoa is a Polkadot-based blockchain, the community claims that it consumes approximately 0.001% of the Bitcoin blockchain’s energy consumption. This reduced consumption is possible because the Ternoa blockchain uses proof-of-stake (NPOS—nominated proof-of-stake) as the block proposer protocol instead of proof-of-work (PoW) [62]. The PoW consumption is estimated at 48.14 kWh per transaction, while the NPoS consumption is estimated in 0.8 GWh per year (800,000 kWh) [63].
3.6. NuCypher
NuCypher [69] is a data encryption and protection layer for Ethereum (and eventually other public networks) and decentralized applications (dApps) that do no rely on a central service provider. The protocol, which the team calls a decentralized key management system (KMS), allows developers to store, share, and manage private data on public blockchains. Developers receive this encryption service via a network of NuCypher nodes in exchange for a fee (paid for in ETH). Participants can only spin up a node by staking NuCypher’s token, NU, on the network as collateral.
NuCypher is a blockchain-based cryptographic infrastructure for privacy-preserving applications, dynamic control access, secrets management, and secure computation [69,70]. Additionally, NuCypher enables users to manage a range of computational secrets, such as identity and access management (IAM) tokens and database and secure shell (SSH) credentials to access servers remotely.
NuCypher uses a decentralized network to remove the dependency on central service providers, to create a proxy re-encryption for cryptographic access control, and to generate a token incentive mechanism to ensure reliability, availability, and correctness [71,72]. Because of proxy re-encryption, an unencrypted symmetric key that can decrypt private data is never exposed server-side. There is no single point of security failure. Even if compromised, hackers would only obtain re-encryption keys, as access to the file is still protected.
The technology provides a decentralized key management system based on blockchain technology and claims it can be used in DDRM, decentralized digital rights management, for secret key transformation [72]. In NuCypher’s network, the content key is encrypted by the owner’s public key, and only the owner’s private key can decrypt it. With authorization from the owner, the encrypted key will be fragmented and re-encrypted by several proxy nodes. Nodes are unaware of each other and cannot collude with the receiver. After re-encryption, the receiver collects the re-encrypted fragments and decrypts them.
3.7. Lit Protocol
The Lit (lockable interactive token) Protocol is a decentralized access control protocol running on top of Ethereum and other Ethereum virtual machine (EVM) chains (full-list EVM chains) (https://github.com/LIT-Protocol/lit-js-sdk/blob/main/src/lib/constants.js#L14). Lit on-chain access control conditions allow for [73]:
-
Encrypting and locking static content among images, videos, and music behind an on-chain condition such as ownership of an NFT;
-
Decrypting static content that was locked behind an on-chain condition;
-
Authorizing network signatures that provide access to dynamic content (for example, a server or network resource) behind an on-chain condition;
-
Requesting a network-signed JWT (JSON web token authentication) that provisions access and authorization to dynamic content behind an on-chain condition.
With this functionality, the Lit protocol enables the creation of locked NFTs that only their owners can unlock [74]. It also allows access to a given server or network resource only to NFT owners. Rather than a simple JPEG, Lit NFTs can be HTML/JS/CSS webpages that can be interactive and dynamic.
The network acts as a decentralized access control list (ACL) that leverages on-chain data to grant users access to content, software, and other decentralized networks [75]. Lit supports many standard contracts and plans to support any RPC call soon. The Lit Protocol is in an alpha state (the “AlphaNet”), and the creators are running all the nodes.
For static content, the SDK encrypts the user’s content and uploads the conditions for decryption to each Lit Protocol node. When someone wants to access the content, the SDK requests a message signature from the user’s wallet that proves the user owns the NFT associated with the content to each Lit Protocol node. The Lit Protocol nodes will then send down the decryption shares, and the SDK will combine them and decrypt the content.
3.8. Summary
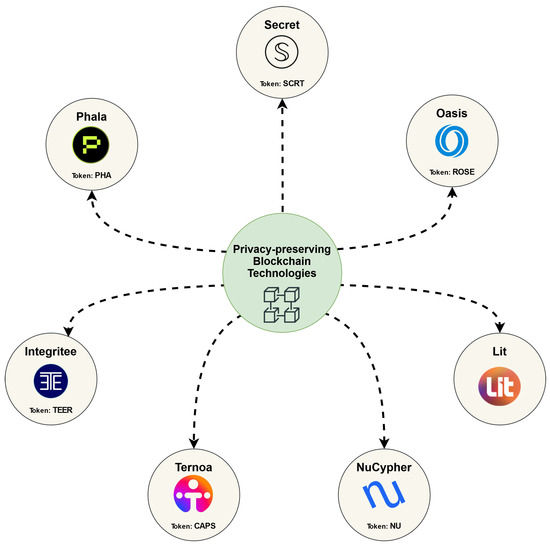
Figure 1 shows seven privacy-preserving blockchain technologies. Table 1 summarizes the properties of the discussed technologies, in terms of the blockchain basis, token name, TEE support, MPC, and ZKP.
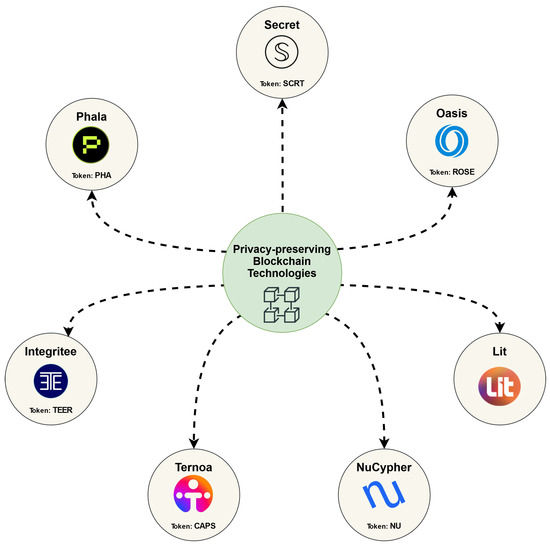
Figure 1. Privacy-preserving blockchains.
Table 1. Comparison among the privacy-preserving blockchain technologies.
| Technology | Blockchain Basis | Token Name | TEE | MPC | ZKP |
|---|---|---|---|---|---|
| Secret | Cosmos | SCRT | ✓ | ✗ | ✗ |
| Oasis | Ethereum | ROSE | ✓ | ✗ | ✗ |
| Phala | Polkadot | PHA | ✓ | ✗ | ✗ |
| Integritee | Polkadot | TEER | ✓ | ✗ | ✗ |
| Ternoa | Polkadot | CAPS | ✓ | ✗ | ✗ |
| NuCypher | Ethereum | NU | ✗ | ✗ | ✗ |
| Lit Protocol | Ethereum | - | ✗ | ✗ | ✗ |
