The HIDA protocol we proposed is a secure and efficient identity verification protocol in cloud computing environments. The protocol uses federated chain technology to securely isolate entities in the trust domain, and combines zero-knowledge proof technology to further protect user data. Federated chain technology isolates interaction between different entities in their respective chains, achieving secure data isolation. Zero-knowledge proof technology can prove user identity information without revealing their true identity. Subsequent access management allows users to prove their identity with a brief credential, greatly improving access efficiency. We conducted formal semantic analysis and simulations, proving the protocol's high efficiency and reliability in practical applications. These research results provide new ideas and technical support for identity verification in cloud environments, providing valuable references for achieving more secure and efficient cloud computing application scenarios.
- cloud computing
- federated chains
- zero-knowledge proofs
In addition to the issues mentioned above, traditional identity management models also face challenges in terms of privacy protection. Centralized identity management systems often require users to disclose a significant amount of personal information to the central server, which may be vulnerable to hacking and data breaches. This can result in the disclosure of sensitive information, leading to financial and reputational damage.The HIDA identity authentication scheme proposed in this work addresses these challenges by leveraging blockchain technology and zero-knowledge proof (ZKP) techniques. Blockchain technology provides a decentralized and tamper-proof ledger that stores user identity information securely, without relying on a central server. This eliminates the single-point-of-failure issue and improves the overall security of the system.ZKP techniques, on the other hand, allow users to prove their identities without disclosing sensitive information. This enhances privacy protection and reduces the risk of data leakage. The use of consortium blockchain networks further enhances the security of the system by providing stricter access permissions and facilitating secure transactions between organizations and entities.We perform formal security analysis using BAN logic and simulation experiments to evaluate the performance of our scheme. The results demonstrate that HIDA provides better privacy protection, more efficient identity verification, and more reliable identity management than traditional schemes. Our work contributes to the development of secure and efficient identity management solutions in cloud computing environments, which are increasingly important in today's digital age.
One of the challenges faced by blockchain-based identity management is ensuring user privacy. While blockchain technology offers secure storage of identity information, it may still be possible to trace transactions back to specific individuals, compromising their privacy. Furthermore, man-in-the-middle attacks can also occur when attackers intercept communications between users and the blockchain network, allowing them to steal sensitive information.To address these challenges, various approaches have been proposed, including anonymous authentication, real-name authentication, and controllable anonymous authentication. Anonymous authentication allows users to authenticate themselves without revealing their identity, while real-name authentication requires users to provide verifiable identity information. Controllable anonymous authentication is a hybrid approach that allows users to choose the level of anonymity they desire.Notable projects in the field of blockchain-based identity management include OAuth, which is an industry-standard protocol for authorization, and UPort, which is a decentralized identity platform built on the Ethereum blockchain. ShoCard is another project that uses blockchain technology to verify identity information, and Sovrin is a self-sovereign identity platform that allows individuals to control their own identity information.While these projects offer promising solutions to the challenges of identity management in the blockchain era, each has its own strengths and weaknesses. Further research and development are needed to address the remaining challenges and improve the security, privacy, and usability of blockchain-based identity management systems.
There are two system models for identity authentication in the cloud: centralized authentication based on CA certificates and user credentials, and credential-based identity authentication based on service provider registration.
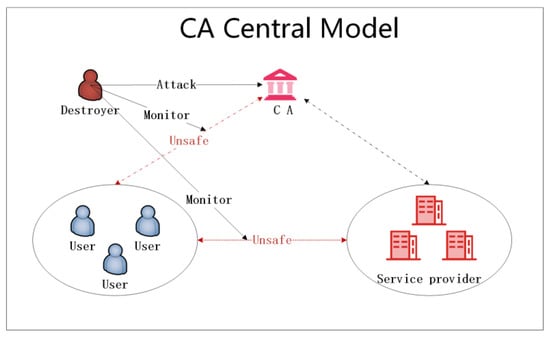
Figure 1. CA Centre based authentication model.
In the centralized authentication model (Figure 1), all system business flows through the authentication center for data filtering and storage. However, there are concerns regarding performance and security. The lightweight central service may not be able to support simultaneous multi-user access, and attackers can potentially paralyze the entire system through worm attacks or other methods. Additionally, if the CA is corrupted, all user data could be disclosed, leading to privacy leaks.

Figure 2. Intra-domain-based business separated authentication model.
In the credential-based identity authentication model (Figure 2), users can undergo identity authentication in different security domains based on different service providers. While this model avoids the single point of failure problem brought on by over-centralization of the CA, it introduces its own set of security concerns. Not all domain users are completely trustworthy, and attackers can intercept and listen to communication between parties to obtain credential information. Additionally, attackers can launch attacks on specific business servers to block the normal operation of the system.
Our proposed identity authentication scheme combines blockchain technology and zero-knowledge proof, as shown in Figure 3. The model includes cloud users, cloud service organizations, cloud data centers, and blockchain networks.The separation of business and identity management allows CSP to focus on business processing, improving service efficiency and scalability. Additional CSP organizations can join the blockchain network by applying for a node in the CDC group.In the identity management and authentication model based on the Fabric network, CSP provides interfaces for users to register and log in with their identity information. Multiple nodes in the network share a ledger, and the administrator can monitor the state of the entire network. User identity credentials are stored in ciphertext in the block and transmitted in ciphertext form to prevent man-in-the-middle attacks.Overall, our proposed scheme addresses the limitations of traditional authentication models and offers a secure and efficient solution for identity authentication in the cloud.
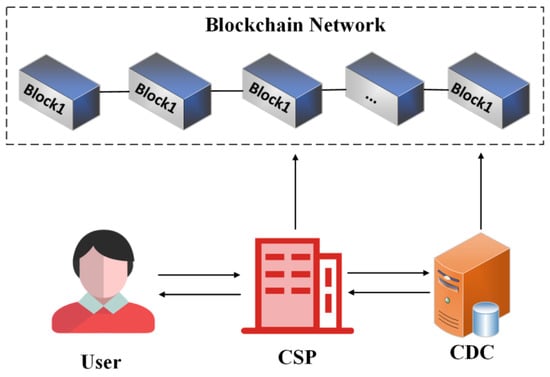
Figure 3. Secure and efficient identity authentication system model.
The system model in this article is based on a secure consortium chain using Fabric as a permission-granted blockchain, which ensures that only authorized entities can access and process sensitive data and business logic. The use of asymmetric encryption and symmetric encryption techniques, zero-knowledge proof technology, and blockchain technology further enhances the security of the system, making it difficult for unauthorized attackers to eavesdrop on the channel. The paper also provides a proof of security for the encryption method used, demonstrating its resistance to eavesdropping by adversaries. Overall, the analysis highlights the robust security measures in place to protect user data and prevent unauthorized access.
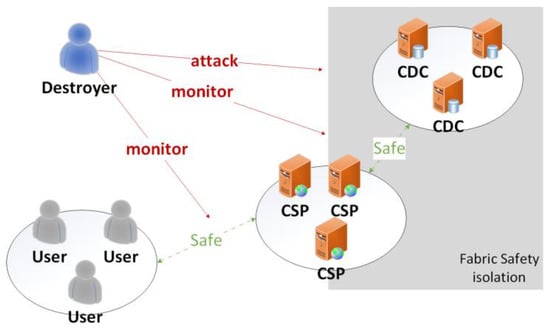
Figure 4. Safety model under HIDA.
The HIDA identity authentication scheme presented in this paper is based on the Hyperledger Fabric platform, which is a popular blockchain technology used in enterprise environments. By leveraging the distributed and decentralized nature of blockchain, the scheme addresses the challenges faced by traditional identity authentication in cloud computing environments, such as single points of failure and privacy security.The scheme incorporates important technologies such as user identity information registration, verification and access control, which are essential for secure authentication. Modern cryptography technologies such as zero-knowledge proof are also employed to enhance the security of the scheme. The scheme is verified through experimental simulations and performance tests, demonstrating its feasibility, efficiency and superiority. The results show that the HIDA scheme can provide strong support and guarantees for identity authentication in the field of cloud computing. The integration of blockchain technology with cloud computing is expected to bring better data security, higher efficiency, and lower costs. This study highlights the potential of such integration and provides a valuable reference for future research in this area. Further optimization and improvement of the HIDA scheme can be explored to enhance its performance and expand its scope of application.
This entry is adapted from the peer-reviewed paper 10.3390/electronics12092140
