The cyberspace depicts an increasing number of difficulties related to security, especially in healthcare. This is evident from how vulnerable critical infrastructures are to cyberattacks and are unprotected against cybercrime. Users, ideally, should maintain a good level of cyber hygiene, via regular software updates and the development of unique passwords, as an effective way to become resilient to cyberattacks. Cyber security breaches are a top priority, and most users are aware that their behaviours may put them at risk; however, they are not educated to follow best practices, such as protecting their passwords. Mass cyber education may serve as a means to offset poor cyber security behaviours; however, mandatory education becomes a questionable point if the content is not focused on human factors, using human-centric approaches and taking into account end users’ behaviours, which is currently the case. P The nature of the present papers report the best pr is largely exploratory, and the purpose is two-fold: To present and explore the cyber hygiene definition, context and habits of end users in order to strengthen our understanding of users. Our paper reports the best practices that should be used by healthcare organisations and healthcare professionals to maintain good cyber hygiene and how these can be applied via a healthcare use case scenario to increase awareness related to data privacy and cybersecurity. This is an issue of great importance and urgency considering the rapid increase of cyberattacks in healthcare organisations, mainly due to human errors. Further to that, based on human-centric approaches, theour long-term vision and future work involves facilitating the development of efficient practices and education associated with cybersecurity hygiene via a flexible, adaptable and practical framework.
- cyber hygiene
- cyberattacks
- healthcare
- human factors
1. Introduction
2. Cyber Hygiene in the Cyberspace
Cyber hygiene originates from the concept of personal hygiene in the public health domain. In an extensive report exploring cyber hygiene practices across various nations, the European Union Agency for Network and Information Security (ENISA) [6][22] introduced that “cyber hygiene should be viewed in the same manner as personal hygiene and, once properly integrated into an organisation will be simple daily routines, good behaviours and occasional check-ups to make sure the organisations online health is in optimum condition”. Research in social sciences on cyber security has been focused on the security behaviours and risk factors of the end–end users, while there is limited research on developing measurements of cyber hygiene. In particular, according to previous approaches that assume that the end users are aware of cyber safety behaviours, they, therefore, focus on measuring the frequency of enactment of these behaviours [7][23]. It is of high importance to understand the role of how end users are processing information and their interpretation within a cybersecurity framework in an organisation. For instance, researchers have empirically demonstrated that individuals who systematically process information are less likely to get victimised during a spear phishing attack [8][24]. Therefore, plenty of cybersecurity awareness programs aim to enhance the ability of the users to process better information. The lack of cyber hygiene leads to a number of cyber threats and cyberattacks. The recent WannaCry Ransomware cyberattack [9][25], which targeted, on a large scale, the Microsoft Windows operating system, had a severe impact on the systems. This occurred due to the organisations and individuals not having updated their software security versions as of the month of March, even though the more recent version had been released in 2014. This is why unlicensed Windows software and systems with outdated software versions became vulnerable and easy to exploit in this attack. The healthcare ecosystem was particularly affected by CT and MRI scanners being exploited in hospitals, among banking, business and corporate sectors worldwide. Around 300,000 computer systems in 150 countries were affected.3. Human Behaviours: The Weakest Link in Cyberattacks
A significant number of cyberattacks are directed towards the users through distorted means, such as malicious emails and masqueraded applications. Though cyberattacks are aiming to exploit either the technical vulnerabilities of networks and systems, or the errors due to human behaviour, it is the latter that remains as the weakest link in these cyberattacks [10][11][29,30]. Attackers most often employ methods exploiting weak cyber behaviours, defined as social engineering. Studies historically confirm that social engineering approaches account for the majority of total cyber security attacks. Bowen et al. [12][31] showed that 28% of the total attacks were due to social engineering, and in 2016, 97% of malware attacks targeted human behaviour. A more recent report estimated that 95% of cyberattacks were again attributed to human errors and risky behaviour [13][32]. Looking in the literature at the types of risky behaviours and human errors, one can identify the most common, including the use of infected memory disks, sharing of passwords, reusing the same passwords for different platforms, not updating software, unauthorised disclosure of personal information, accessing fake emails and installing software from unverified sources [14][15][16][17][18][33,34,35,36,37].4. Cyber Threats and Countermeasures in Healthcare 4.0
There are several attacks that occur daily within healthcare 4.0. However, as found in the literature, there are six main types of cyber threats that can be identified in the cyberspace, and are directly applied in healthcare 4.0, accompanied by appropriate countermeasures [4], which are presented in detail in Table 1.| Cyber Threat | Description |
|---|---|
| Attacks on Hosted Components | These types of attacks include destructive software injection to a targeted system, for example, cross-site scripting, SQL injection and related techniques, which threaten the access and/or authentication controls. This may occur in cloud-based control systems handling big volumes of sensitive data. Here, the countermeasures include mainly role-based approaches, creating awareness in order to protect towards impersonation at the cloud level and API authentication. |
| Social Engineering | It refers to the attacks performed on the “weakest link” in the security supply chain. This is achieved by psychologically manipulating individuals to perform malicious actions or share confidential information. Common techniques used for this manipulation are shoulder surfing, diversion theft, “dumpster diving”, impersonation of help desk calls, phishing and/or personal blackmailing |
| Component | Description | ||||
|---|---|---|---|---|---|
| User |
| ||||
| [ | 19][20]. Social engineering is one of the major reasons why even security-aware and well-equipped companies fall victims to cyberattacks. Hackers identify the weakest link in the security supply chain in which they can insert the malicious software or the virus into the targeted system. Therefore, it is of great importance to identify and further secure the weakest link in the security chain. Some of the initial countermeasures, which can be adopted to prevent upcoming attacks, include block Wi-Fi connections to unsecured networks, block network connections related to malicious content, stop using non-secure web pages and websites and performing actions on them. Further approaches, which can be taken to reduce the high level of cyberattacks, include mitigating known threats in the systems and applications, regularly patching vulnerable systems and/or keeping the company’s devices up-to-date with the latest version. | It refers to the attacks performed on the “weakest link” in the security supply chain. This is achieved by psychologically manipulating individuals to perform malicious actions or share confidential information. Common techniques used for this manipulation are shoulder surfing, diversion theft, “dumpster diving”, impersonation of help desk calls, phishing and/or personal blackmailing [38,39]. Social engineering is one of the major reasons why even security-aware and well-equipped companies fall victims to cyberattacks. Hackers identify the weakest link in the security supply chain in which they can insert the malicious software or the virus into the targeted system. Therefore, it is of great importance to identify and further secure the weakest link in the security chain. Some of the initial countermeasures, which can be adopted to prevent upcoming attacks, include block Wi-Fi connections to unsecured networks, block network connections related to malicious content, stop using non-secure web pages and websites and performing actions on them. Further approaches, which can be taken to reduce the high level of cyberattacks, include mitigating known threats in the systems and applications, regularly patching vulnerable systems and/or keeping the company’s devices up-to-date with the latest version. | |||
| Usage |
| Physical Attack | Physical attacks are mostly carried out in fields involving several Internet of Things (IoT) applications since they are connected to a number of components and hardware devices. These are easily located by hackers since they cannot be monitored at a single location and are kept far away from each other [21][22]. The main countermeasures in such cases include trusted platform modules to enable storage of the data on separate platforms securely, file system encryption meaning proper algorithms and encryption decryption techniques shall be used so the data can be stored and secured properly, and lastly remote attestation meaning attesting a remote to each hardware device, which is located far in order to be controlled from faraway locations as well. | ||
| Usability | Physical attacks are mostly carried out in fields involving several Internet of Things (IoT) applications since they are connected to a number of components and hardware devices. These are easily located by hackers since they cannot be monitored at a single location and are kept far away from each other [42,43]. The main countermeasures in such cases include trusted platform modules to enable storage of the data on separate platforms securely, file system encryption meaning proper algorithms and encryption decryption techniques shall be used so the data can be stored and secured properly, and lastly remote attestation meaning attesting a remote to each hardware device, which is located far in order to be controlled from faraway locations as well. | ||||
|
Network Compromise | These attacks are known as ‘middle way attacks’ where the hackers use a number of techniques, for example, altering or blocking communications between hardware devices and their cloud-based controller session and/or hijacking to enter and disrupt a network. The countermeasures that can be offered here include performing regular updates on the software and use of proper file decryption and encryption techniques while sending and receiving sensitive data between the end-to-end users. | |||
| Hacked Device Software | In these attacks, the hacker accesses the software at the device level and then it carries out several fraudulent activities and techniques. Such activities and techniques target to take control of the data in the system and include elevation of privileges, denial of service, malware injection and/or false identification [23]. These types of attacks can be tackled by carrying out countermeasures, as for example, software isolation; “secured boot”, meaning that when any malicious activities are carried out in the system, after rebooting the system, it then does not turn on and all the available data in the system becomes resilient to the attacker; and/or software update, which maintains the software and its system updated with the latest version available on the market. | In these attacks, the hacker accesses the software at the device level and then it carries out several fraudulent activities and techniques. Such activities and techniques target to take control of the data in the system and include elevation of privileges, denial of service, malware injection and/or false identification [44]. These types of attacks can be tackled by carrying out countermeasures, as for example, software isolation; “secured boot”, meaning that when any malicious activities are carried out in the system, after rebooting the system, it then does not turn on and all the available data in the system becomes resilient to the attacker; and/or software update, which maintains the software and its system updated with the latest version available on the market. | ||
| Security Misconfiguration | This type of attack is being performed due to inattentiveness or carelessness. The moment when it has been observed to occur is when handling the security changes of the software, as the security changes become misconfigured and provide the attackers with the right opportunity to attack the devices and extract the available data from them. Hence, the most significant countermeasure is that the security changes ought to be carried out with extreme care and with proper decryption encryption techniques as well [21]. | This type of attack is being performed due to inattentiveness or carelessness. The moment when it has been observed to occur is when handling the security changes of the software, as the security changes become misconfigured and provide the attackers with the right opportunity to attack the devices and extract the available data from them. Hence, the most significant countermeasure is that the security changes ought to be carried out with extreme care and with proper decryption encryption techniques as well [42]. |
5. Towards a Human-Centric Approach to Security
Human behaviour is the weakest link in cybersecurity; it is the employees of any organisation that should be involved and engaged within cybersecurity awareness and the development of mitigation approaches.
Furthermore, as a result of the global COVID-19 pandemic, new working trends have been introduced, where employees working flexibly use their own devices or are using work devices outside the office, resulting in blurred lines between personal and business limits, exacerbating the risky behaviours. As a result, any measures to mitigate the cyber risks need to go beyond the software updating and hardware maintenance to a more human-centric approach. Human-centric cyber security is still a new domain, which is an intangible concept and is challenging to define and to be understood, not only by the lay end user, but also by specialists in cyberspace. The reason is that it sits at the intersection of human behaviour, computing and security systems. Grobler et al. (2021) [24][466. Best Practices and Education of Cybersecurity Hygiene for Healthcare Professionals
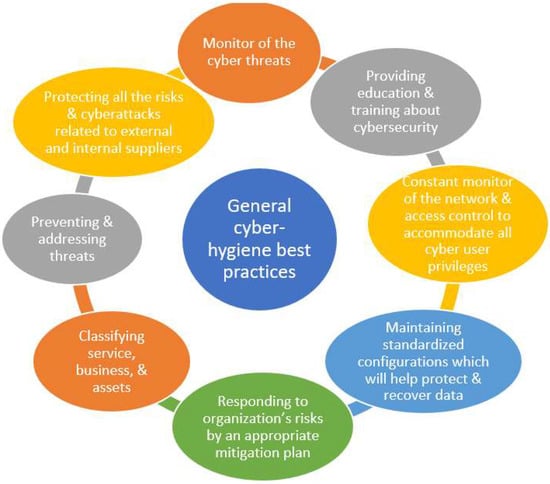
Cyber threats are rapidly increasing across various business sectors and the incidents in data privacy and cybersecurity breaches are also rising alongside them, particularly in the healthcare domain. In response to the rising threats and incidents, healthcare organisations adopt technical measures, such as the use of firewalls, antivirus and software/firmware patches, aiming to preserve and protect the business continuity of healthcare services. Regardless of such efforts, cybersecurity threats are rising, and the adopted measures have been proven insufficient to respond to cyberattacks. This is often because the important role that the personnel play in this supply chain, related to cyber defence, is not being considered. In practice, healthcare organisations are encouraged to adopt general data privacy and cybersecurity guidelines that have, as a focal point, the human factor. Nevertheless, there is limited research within the literature on collective practical cyber hygiene guidelines and best practices, which can help healthcare organisations to apply specific interventions, such as training programs and awareness activities, which at the same time are measurable to the healthcare professionals. With that being said, structured best practices that would assist the higher management to choose the optimal number of security controls that will be most efficient for healthcare organisations and professionals are yet not available and, at the same time, are highly desirable. Cybersecurity hygiene best practices and education are linked to individual differences aiming to improve cybersecurity. Even though Internet security guidelines for users are widely available, it is doubtful how many consumers understand and apply these reports and if the available security guidelines are written in a lay language for both tech laggards and tech savvy users [25][52]. One feasible solution in order to overcome the educational gap in cybersecurity would be to establish best practices and mandatory cyber hygiene education for users, including both non-cyber and cyber professionals [26][27][17,53]. Best practices and mass cyber education may contribute to discourage poor cybersecurity behaviours; however, to achieve the most optimal results, the content should shift its focus to human factors and use behaviours. It is evident that most available courses and/or training do not address explicitly human cognition and behaviours. The baseline cyber hygiene involves several basic steps that are required for cyber defence. The baseline practices are mostly rooted in frameworks, such as, for example, the NIST cybersecurity framework. It helps organisations, including the healthcare supply chain, to have a detailed and clear set of best practices to show and modify how cybersecurity is being performed and measured regularly [28][19]. While there are not standardised best practices for healthcare, a basic set of methods to maintain cyber hygiene in business has been presented in the literature [29][30][54,55]. All organisations and cyber users need to take responsibility for their browsing in both their personal and professional space. Individuals must take ownership of maintaining sufficient cyber hygiene and safeguarding, by using best practices, against cyberattacks [4]. Best practices, as collected from the literature, are presented in Figure 1.