Blockchain being a leading technology in the 21st century is revolutionizing each sector of life. Services are being provided and upgraded using its salient features and fruitful characteristics. Businesses are being enhanced by using this technology. Countries are shifting towards digital currencies i.e., an initial application of blockchain application. It omits the need of central authority by its distributed ledger functionality. This distributed ledger is achieved by using a consensus mechanism in blockchain. A consensus algorithm plays a core role in the implementation of blockchain. Any application implementing blockchain uses consensus algorithms to achieve its desired task.
1. Introduction
The 21st century is all about revolutionizing technology. One of the leading technologies that have changed many aspects is blockchain. It impacted different businesses from the very first step. Blockchain provides decentralized, transparent, and secure systems. It is a distributed ledger technology that maintains a transaction ledger and secures it by using cryptography. The transactions are recorded in blocks and these blocks are connected to each other through hashes. Initially, it was used by Satoshi Nakamoto in 2008 for public transactions of bitcoins. Bitcoin
[1] digital currency was the first application of blockchain
[2][3].
Blockchain came as a solution to the longstanding user’s trust problem. With its emergence with the renowned cryptocurrency Bitcoin, it provided an architecture to allow the user to trust a decentralized system instead of trusting a third party. Operating a peer-to-peer network, it keeps records of the ledger of transactions. This helps to avoid any center party. The whole process is done through a consensus. A ledger is shared between multiple entities, allowing everyone to inspect it. No single user can control it. It is a distributed cryptographically secured database that keeps the record of every transaction from the very initial one.
2. Types of Blockchain
There are three main types of blockchain. These do not often confuse traditional databases or distributed ledger technology (DLT) with blockchains. These types of blockchain are:
-
Public/Permissionless Blockchains for example Bitcoin and Ethereum etc.
-
Private/Permissioned Blockchains for example Hyperledger and R3 Corda etc.
-
Hybrid Blockchains for example Dragonchain etc.
3. Applications of Blockchain
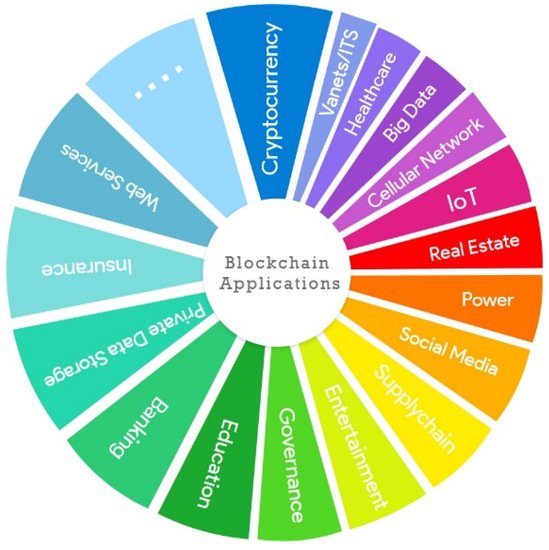
Blockchain has now being deployed in not only cryptocurrency but its underlying technology is used in various applications
[4]. We tried to discuss a few applications of blockchain which includes cryptocurrencies as well as other potential areas where blockchain has emerged.
Figure 1 shows different applications of blockchain.
Figure 1. Applications of blockchain.
4. Blockchain’s Architecture
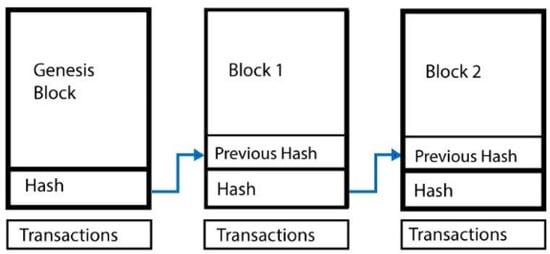
Figure 2 shows a general view of a blockchain. A block contains the transactions, the hash of the previous block, and a hash of the next block
[5]. This information is stored in a block using a cryptographic mechanism. A block in the chain can come from any miner. While creating the chain of blocks, the hash of the previous block is added to the current block. Thus a miner creates a new block by using the hash of the previous block, combines it with its own set of messages, and creates a new hash out of it. This way a new block is formed. This recently formed block now turns out to be the new end for the chain. By this mechanism, the chain grows as more blocks are added by the miners.
Figure 2. Blockchain architecture
[6].
Double-spending is the problem where the sender uses the same money at more than one place for gaining goods or services from multiple dealers. The use of centralized authority solves the double-spending problem, but another main issue arises which is the cost of maintaining and creating the centralized authority itself. Blockchain however prevents double-spending by grouping the transactions and timestamping them and then broadcasting them in the network to all the participant nodes. The transactions are mathematically related to previous ones and are timestamped, hence impossible to tamper with.
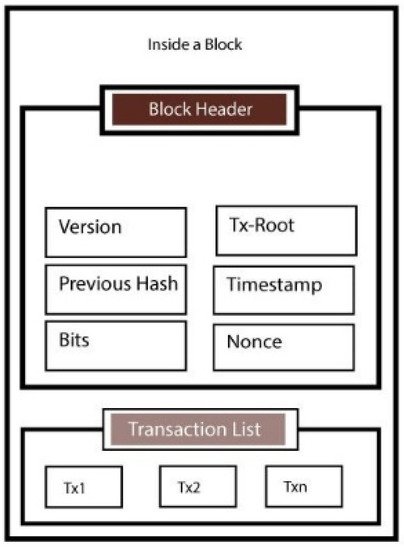
There are also some other fields in the block header which are shown in Figure 3. We explain each of them.
Figure 3. Structure of a block
[7].
5. Consensus Algorithms
We know that blockchain is a decentralized distributed network that provides security, immutability, transparency, and privacy. There is no concept of centralization to verify and validate the transactions, but still, transactions in the blockchain are considered to be completely verified and secured. This is the result of a core algorithm present in every blockchain network called a consensus protocol.
A consensus algorithm is a technique through which all the peers of the blockchain network reach a common agreement about the current state of the distributed ledger. Therefore, consensus algorithms provide trust and reliability among unknown peers in a distributed environment. A consensus mechanism ensures that every new block added to the blockchain is the only truth that is agreed upon by all the blockchain nodes
[8].
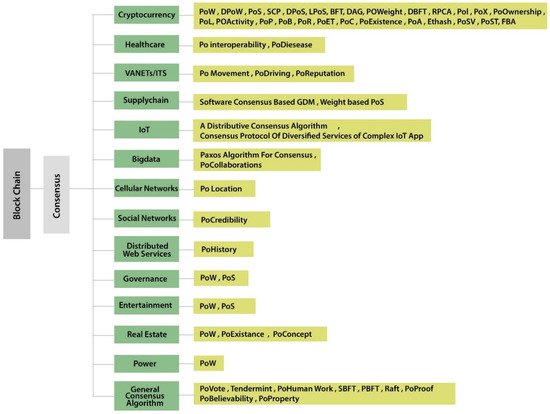
The blockchain consensus protocol comprises some specific aims that are coming to an agreement, cooperation, collaboration, mandatory participation of each node in the consensus process, and equal rights to every node. Hence, a consensus algorithm targets finding a common agreement that is a win for the whole network. The above-discussed applications are categorized and consensus algorithms based on these categories are further discussed below. Figure 4 shows a categorical diagram of the consensus and their distribution.
Figure 4. Categorization of the consensus algorithms.
6. Development Platforms
Table 5 describes some of the important features of the development environments.
Table 5. Comparison of blockchain technologies.
| Comparison Parameters |
Ethereum |
Cosmos |
Cardano |
EOS |
Bitcoin |
Hyperledger |
Corda |
| Token |
ETH |
ATOM |
ADA |
EOS |
Bitcoin |
n/a |
SDK |
| Public/Private |
Public |
Public/Private |
Public |
Public/Private |
Public |
Public/Private |
Private |
| Programming Languages |
Solidity |
Java, C++, Python, Go |
Haskell |
JavaScript, Python, Ruby |
Golang |
Java, Golang, Node |
Kotlin, Java |
| Consensus Algorithms |
Proof of Work (Currently used), Proof of Stake (In Future) |
Tendermint (Byzantine Fault-Tolerant, Proof of Stake) |
Proof of Stack |
Delegated Proof of Stack |
Proof of Work |
Practical Byzantine Fault Tolerance |
Pluggable Consensus |
| Transactions Per Second |
25 |
10,000 |
n/a |
Millions (theoretically) |
1/3 to 1/7 |
More than 1000 |
Between 15 and 1678 TPS |
| Transaction Size |
1 MB |
250 bytes |
n/a |
n/a |
1 MB |
Changeable (depending on framework) |
Maximum size in bytes |
| Open Source |
True |
True |
True |
True |
True |
True |
True |
| Pros |
Anyone can write smart contract and anyone can view that contract |
Works like a hub for blockchains, based on Tendermint |
Scalability, Sidechain which reduces the risk of hacks. |
Parallel processing, low latency, free usage (claimed not proven). |
Safe and secure, High token value. |
Don’t use cryptocurrency so it is ideal for business networks. |
Designed specifically for financial applications |
| Cons |
Scalability issue, 25 transactions per second is very slow |
Complex technology may have compatibility issues with the latest technologies and new blockchains |
Maintaining a side chain is complicated and it will require its own miners. |
Never actually free, not fully decentralized, the free transaction fee are imposed on everyone who has EOS. |
Very slow, not ideal for programming while there are other faster technologies. |
There are a lot of frameworks to choose from and they all have different requirements to implement and setup. |
Partially decentralized, not much suitable for IoT resource constrained networks |
7. Blockchain Challenges
Although blockchain has improved a lot of applications and has a fault-tolerant peer-to-peer network blockchain always comes up with its vulnerabilities. We discuss the possible attacks on a blockchain ledger.
7.1. Denial of Service (DoS) Attacks
The attacker crash a node by flooding a large amount of traffic in a denial of service (DoS)
[9]. It prevents authorized users from retrieving the service or resource. Similarly, a distributed denial of service (DDoS) is another type of attack where a node is flooded with malevolent requests. In DDoS multiple attackers attack a single node.
7.2. Sybil Attacks
Multiple identities attacking a larger portion of the network is called a Sybil attack. The invaders can launch numerous false nodes that seem to be honest to their peers. These false nodes take part in falsifying the network to authenticate illegal transactions and to modify valid transactions. They can use virtual machines, several devices, or internet protocol (IP) addresses as bogus nodes for the attack. The peer-to-peer (P2P) network assumes that every participating node contains only one identity. Thus, numerous forged nodes give attackers the ability to repudiate transmitted blocks and to outvote authentic nodes. When an attacker controls a large number of nodes in the network, it increases the chances of double-spending
[10].
7.3. Eclipse Attacks
In an eclipse attack
[11], specific nodes are isolated from the peer-to-peer network by the attacker. Similar to Sybil attacks, it does not attack the entire network. Once the target node is isolated, the attacker controls all outgoing connections of the node
[12]. From there on, the attacker can abuse the target network and dispatch distinctive sorts of attacks on blockchain mining power and agreement components. These attacks include double-spending, engineering block races, selfish mining, and splitting mining power.
7.4. Routing Attacks
In routing attacks
[13], a message is intercepted by the attacker in the blockchain network. The attack alters the message and sends it to its neighbors. Furthermore, this attack is divided into a partitioning attack and a delay attack. In a partitioning attack, the entire blockchain network is divided into two or more portions. In a delayed attack, the attacker captures the message and tampers with it. Then, it redirects the tampered message to another blockchain network portion.
Different consensus mechanisms are used by blockchain to develop trust among blockchain peers. However, there are some possible attacks on these consensus mechanisms.
7.5. The 51% Attacks
A miner, having 51% or more hashing power, can initiate a 51% attack in the blockchain network
[14]. The 51% attack, enables the attacker to stop the confirmation of a new block. Additionally, the attacker can reverse transactions already confirmed by the blockchain.
7.6. Double Spending
In double-spending, multiple transactions with the same cryptocurrency are performed by a user
[15][16]. This transaction is broadcast to each node in that network. This transaction needs to be confirmed by the nodes, this confirmation is time consumable
[15]. This time between two transactions’ initiation and confirmation can be a window for the attacker to quickly launch his/her attack
[17][18].
7.7. Alternative History Attacks
In an alternative history attack, a transaction is sent to the merchant by the attacker
[19][20]. In addition, a double-spending transaction is included by the attacker in an alternative blockchain fork
[21][22]. The merchant sends the product after n blocks confirmation. Therefore, the attacker tries to find more than n blocks. If the attacker succeeds, he gains his coins by releasing the fork.
7.8. Race Attacks
In the race attack, the attacker creates two transactions. The first transaction is sent to the merchant by the attacker
[23][24]. This product is sent by the merchant without confirmation. Meanwhile, the second transaction is broadcast by the attacker to invalidate the first transaction.
7.9. Finney Attack
In the Finney attack
[25], two similar transactions i.e., one crediting the target and the other crediting the attacker are used by the attacker
[26][27]. This attack mines a block that including the first transaction and delays publishing it. Meanwhile, the attacker mines the second transaction. When the attacker succeeds, he purchases goods with the first transaction. Then, he releases the pre-mined block which includes the first transaction. The attacker receives both goods and coins whereas the merchant finds their transaction invalid
[28][29].
8. Blockchain Research Issues
8.1. Blockchain-Based Research Issues in Healthcare
Blockchain has improved the medical and smartphone applications but there are still some security issues as blockchain comes with potential problems. Any industry including healthcare that needs to use blockchain and its devices should train themselves in these areas to improve it. Such education can improve patient-centered data
[30][31]. The blockchain experiments in this research need a patient to authorize himself before transferring a record and this could lead to threats. Key leakage and management is another issue that is not addressed. If a key is lost by a patient the data is difficult or impossible to be authenticated or recovered. A mechanism should be discovered for recovering data. Traditional blockchain cannot be enough in the case of a large amount of patient’s storage and sharing data so a double blockchain solution is presented by Lejun Zhang
[32].
8.2. Blockchain-Based Research Issues/Future Work in Intelligent Transportation System (ITS) and Internet of Things (IoT)
An ITS aims to improve road safety and traffic management
[33][34]. Vehicles share information regarding their position, speed, and direction, etc. with other vehicles
[35][36] as they carry sensing data via dedicated short-range communication
[37]. In ITS, nodes can communicate with each other via different blockchain apps at a large scale autonomously forming decentralized autonomous organizations (DAOs) or decentralized autonomous systems (DASs). Research is needed at the microscopic level of these autonomous agents. Concrete work is also needed in system modeling of self-adaptive, self-evolving, and self-organizing DAO and DASs. Moreover, mechanisms should be designed for crowd-sourcing incentives. There are more interesting issues in ITS such as credit evaluation of ITS assets and trust-based management which needs more effort of research. Further study needs to be undertaken in smart contract-based ITS and data security and privacy issues to prevent the easier 51% attack in ITS. Blockchain can be explored more to incorporate with IoT
[38] for improving security and privacy in various domains of smart application
[39]. G. Ali
[40] suggested a blockchain-based framework for access delegation in IoT which produces high throughput in the case of a large number of concurrent requests. Therefore, further investigation needs to be undertaken in such scenarios.
8.3. Blockhain Research Issues/Future Work in Real Estate
Private blockchain using smart contracts can be the best solution for recording transactions of real estate having high transaction fees
[41]. Using resource information by a customer can lead to a conclusion about the business work of other customers. So a hybrid blockchain that includes both private and public best features can be deployed to audit the access of data as it provides the most authoritative system for the participating nodes
[42].
9. Future Work
In the future, studies can explore more consensus algorithms as in IoT, machine learning, intelligent transportation systems, etc. Applications are not specific to those mentioned in this paper for example banking
[43] or related applications can be explored and added. Open blockchain-based research issues in academic subjects like software engineering, databases, and networks, etc must be considered.